CVE-2025-14847: The most severe memory leak vulnerability in MongoDB in years
A serious unauthenticated memory leak vulnerability in MongoDB Server has been identified, allowing attackers to extract sensitive information.
Overview
In recent years, MongoDB has often been considered a "secure by default" database management system if configured correctly. However, at the end of 2025, a serious vulnerability was discovered, challenging this assumption. MongoBleed (CVE-2025-14847) was discovered by chance and allows remote attackers to directly read data in the memory (heap) of MongoDB without any form of authentication, simply through specially crafted network packets.
The alarming aspect of MongoBleed is not the complexity of the exploit, but the nature of the leaked data. It's not logs or metadata, but what MongoDB is "thinking" at that moment: authentication information, BSON data not yet written to disk, session tokens, and other internal structures. This makes MongoBleed often compared to Heartbleed, one of the most shocking vulnerabilities in security history.
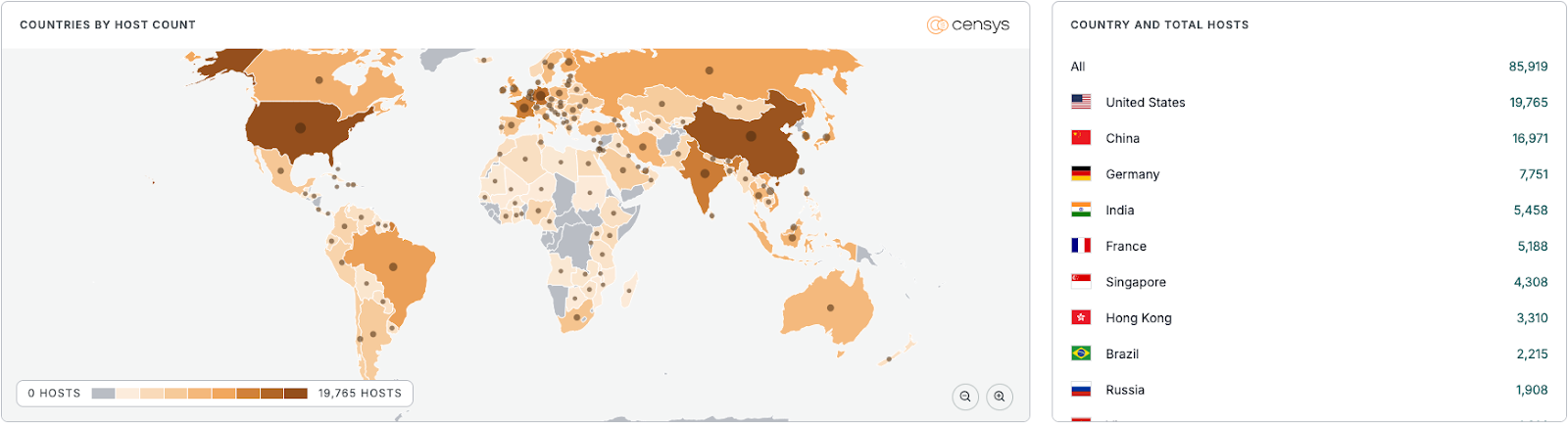
Immediately after the proof-of-concept was published, scanning and exploitation campaigns quickly appeared on the Internet, targeting tens of thousands of publicly exposed MongoDB instances. Let's explore how this vulnerability works, the level of risk if exploited, and how users can effectively protect themselves.
According to a report by Censys, more than 87,000 MongoDB instances have been affected by this vulnerability, with the majority located in the United States.
Introduction to MongoDB
MongoDB is a NoSQL document-oriented database management system designed to handle large volumes of data with high performance and flexible scalability. Instead of using the traditional table-row model like relational databases, MongoDB stores data as BSON documents (Binary JSON), allowing for the representation of complex, nested, and flexible data structures.
Architecturally, MongoDB is designed in a client-server model, where applications (clients) communicate directly with mongod through MongoDB's proprietary binary protocol (MongoDB Wire Protocol), by default on port 27017.

From a security perspective, MongoDB supports several defense mechanisms such as user authentication, role-based access control (RBAC), TLS connection encryption, data-at-rest encryption, and audit logs. However, in practice, many MongoDB systems are still exposed directly to the Internet, misconfigured, or slow to patch, making them attractive targets for attackers.
MongoDB uses the Wire Protocol to exchange messages between the client and server. A message typically includes:
Header (opcode, requestId, responseTo)
Payload (BSON documents, metadata)
Compression options
To optimize performance and reduce bandwidth, MongoDB supports Message Compression, with zlib being the most common. When compression is enabled, data received from the client will be:
Read into the network buffer
Decompressed in memory
Passed to the query processing layer
Cause of the Vulnerability
As mentioned above in the architecture section of MongoDB, there is a part that supports Message Compression, but this is also the security weakness leading to the CVE-2025-14847 vulnerability. This feature allows any client, even those not authenticated, to trigger decompression logic and memory allocation. This results in a consequence:
A portion of uninitialized heap memory is sent back to the client.
The data leak is not due to "reading the wrong file," but due to returning the wrong RAM.
CVE-2025-14847 exists not because MongoDB lacks security, but due to a wrong assumption at a very low level:
- "Data after decompression is always safe to use."
Vulnerability Description
Identifier: CVE-2025-14847
CVSS Score: 8.7
Severity Level: High
Description: Allows an unauthenticated attacker to extract sensitive data directly from the MongoDB server's memory remotely.
Affected Versions
8.2.x < 8.2.3
8.0.x < 8.0.17
7.0.x < 7.0.28
6.0.x < 6.0.27
5.0.x < 5.0.32
4.4.x < 4.4.30
Setting Up the Environment
To set up the environment, we can install it on both Windows and Ubuntu. In this example, we will set it up on Windows 10 with the following minimum requirements:
| Component | Recommended |
| OS | Windows 10 x64 |
| RAM | ≥ 4 GB |
| Disk | ≥ 5 GB free |
| System permissions | Administrator |
| Tool | PowerShell / CMD |
Visit MongoDB Community to download the installer: https://www.mongodb.com/try/download/community

Configuring MongoDB as a Service
C:\Program Files\MongoDB\Server\8.2\data\: Default Data PathC:\Program Files\MongoDB\Server\8.2\log\: Log Directory

Connecting to MongoDB

Vulnerability Analysis and Demo

As previously mentioned in the vulnerability cause and MongoDB's operation mechanism, the attacker will exploit the protocol handling layer of MongoDB, allowing an unauthenticated client to send syntactically valid requests that are specially crafted to:
Trigger unreleased memory allocation.
Gradually increase the RAM usage of the mongod process.
Lead to memory exhaustion and denial of service.
In the first stage, the attacker will perform a network scan to find which host has port 27017 open - this can also be considered a prerequisite for proceeding with the subsequent stages.
After identifying the open port, the attacker continues to establish initial connections by having MongoDB accept connections at the network layer and send some protocol-compliant requests:
Correct MongoDB Wire Protocol structure.
No schema violations at the parser level.
With such valid requests, MongoDB receives and processes them as "normal" requests. During request processing, MongoDB will:
Allocate buffer/object in the heap memory.
Use it to process intermediate data.
After processing the requests, MongoDB will reach a stage called the Memory Accumulation Phase. Here, MongoDB no longer processes queries at the application logic level but moves to internal memory handling (heap management). It will allocate temporary memory to process valid network messages. Due to a logic error during processing, some memory is not reclaimed, leading to each processing cycle leaving behind a "residue" of memory—this is known as a memory leak.

Not only does this vulnerability stop here, but if exploited, it also impacts the system.
Short-term impact
RAM usage continuously increases
Latency increases
MongoDB responds slowly
Long-term impact
OOM Killer (Linux)
Service crash (Windows)
Replica set:
Primary goes down
Trigger election
Causes cluster instability
In a production environment, this is an infrastructure-level DoS, not just an application error.
Conclusion
The MongoBleed (CVE-2025-14847) exploitation campaign reveals a concerning reality: even popular, mature, and widely deployed database management systems like MongoDB can become serious vulnerabilities when there are errors in the core memory processing layer. Unlike traditional vulnerabilities that rely on authentication or authorization, MongoBleed allows attackers to deplete server memory without authentication, leading to denial of service, system disruption, and potential leakage of sensitive data.
The danger of this vulnerability lies in its ability to directly exploit the protocol and internal memory management mechanisms, completely bypassing typical security layers like user accounts, passwords, or role-based access control. In real-world environments, where many MongoDB instances are still exposed to the Internet or operate with default configurations, MongoBleed can become an effective attack tool for both sabotage scenarios (DoS) and reconnaissance and preparation for deeper intrusions.
Ultimately, MongoBleed is not just a single vulnerability, but also reflects a trend of attacks increasingly focusing on foundational infrastructure components. For security teams, understanding the internal workings of the system—from protocols and memory to actual deployment—is key to early detection, effective response, and prevention of similar attack campaigns in the future.
Recommendations
Patch and Upgrade (Highest Priority)
Upgrade MongoDB to the version that addresses CVE-2025-14847 as per MongoDB's official recommendations.
Do Not Expose MongoDB Directly to the Internet
Absolutely do not expose port 27017 to the public Internet.
Allow MongoDB access only through:
Internal network (LAN/VPC)
VPN
Bastion host
Use a firewall or security group to restrict source IPs that are allowed to connect.
Monitor memory resources and unusual behavior
Set up alerts when:
Memory usage increases unexpectedly
MongoDB process continuously uses RAM without decreasing
Track metrics:
Resident Memory
WiredTiger cache usage
Unusual number of connections and requests
In a SOC environment, build a normal behavior baseline to detect early signs similar to MongoBleed.
Limit resources to reduce attack impact
Apply resource limits:
Limit RAM for MongoDB (especially in containers or VMs)
Limit the number of concurrent connections
In cloud or container environments:
Use cgroups / container memory limits
Avoid letting MongoDB consume all system RAM during an attack
Mapping MongoBleed using MITRE ATT&CK & D3FEND
Phase 1 – Reconnaissance (Target Discovery)
T1046 – Network Service Discovery
- Attackers scan the network to find MongoDB with port 27017 open
Phase 2 – Initial Access (Service Interaction)
T1190 – Exploit Public-Facing Application
MongoDB is considered a public-facing service
MongoDB protocol is exploited before authentication
Phase 3 – Execution (Abuse of Server-Side Processing)
T1059 (Conceptual) – Command Execution (logic-level, not OS command)
T1106 – Native API Abuse (concept applied)
Phase 4 – Impact (Primary Objective)
T1499.003 – Endpoint Denial of Service: Resource Exhaustion
- Exhaust RAM through memory leak