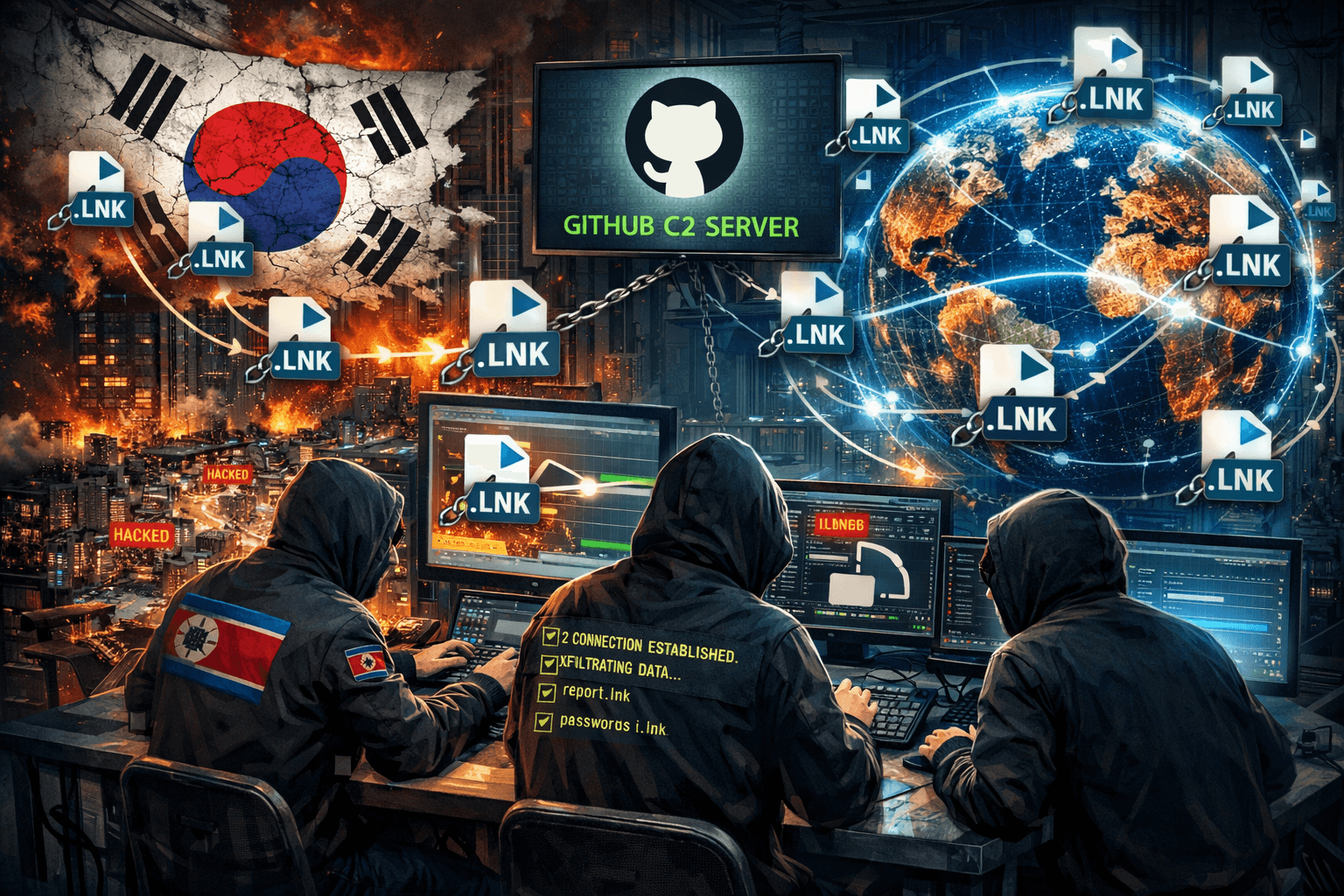
DPRK Attack Campaign: Abusing LNK Files and GitHub C2 Targeting South Korea
1. Executive Summary
In early April 2026, FortiGuard Labs disclosed an attack campaign linked to the Democratic People's Republic of Korea (DPRK), primarily targeting organizations in South Korea. This campaign is notable for abusing GitHub — a globally trusted platform — as Command and Control (C2) infrastructure, allowing malicious traffic to blend seamlessly with legitimate activity and bypass conventional security controls.
The initial vector is a Windows LNK (shortcut) file disguised as a legitimate PDF document, distributed via spearphishing emails targeting employees at South Korean companies. When a victim opens the file, a multi-stage attack chain is triggered: the LNK decodes and silently executes a PowerShell script that performs environment checks, establishes persistence via a Scheduled Task, and exfiltrates system information to GitHub using private repositories.
The campaign has been traced back to at least 2024, with earlier versions linked to the distribution of XenoRAT. The latest iterations remove identifying metadata, increase obfuscation, and expand the network of GitHub accounts used for C2. LNK file metadata — particularly the "Hangul Document" naming pattern — suggests ties to North Korean state-sponsored APT groups including Kimsuky, APT37, and Lazarus.
Risk to organizations running Windows with email-exposed users: HIGH. No zero-day vulnerability is required — a single click on an LNK file initiates the attack chain. GitHub is routinely whitelisted in enterprise environments, making exfiltration difficult to detect through conventional domain-based filtering.
2. Threat Information
2.1 Campaign Overview
| Attribute | Details |
|---|---|
| Campaign Name | DPRK LNK-GitHub C2 Campaign |
| Threat Actor | DPRK-affiliated (Kimsuky / APT37 / Lazarus — no definitive attribution) |
| Geographic Target | South Korea |
| Targeted Sectors | Finance, technology, investment, blockchain/AI (based on decoy PDF titles) |
| Activity Period | At least since 2024; escalating activity in early 2026 |
| Discovered By | FortiGuard Labs (Cara Lin) — published April 2, 2026 |
| Severity | HIGH |
| Primary Source | FortiGuard Labs |
2.2 Attribution
Metadata extracted from LNK files — specifically the "Hangul Document" pattern in the Name field — is consistent with techniques used by North Korean state-sponsored APT groups: Kimsuky, APT37, and Lazarus. The use of GitHub C2 to distribute XenoRAT and its MoonPeak variant was previously documented by ENKI and Trellix and attributed to Kimsuky. AhnLab has also reported a similar LNK-based infection chain from Kimsuky leading to a Python-based backdoor.
⚠️ Note: Attribution has not been definitively confirmed. FortiGuard Labs describes this as "DPRK-related" — it may involve multiple groups sharing TTPs or infrastructure.
2.3 Targeting Profile
Based on decoy PDF titles collected from attack samples, the threat actor is targeting companies in:
AI / Blockchain Technology:
TRAMS WINBOT AI Strategic Proposal.pdf.lnkInvestment / Funds:
상세 제안서 - 미래에셋 X AYC Fund.pdf.lnk(Mirae Asset × AYC Fund)Fintech / Web3:
(CONFIDENTIAL) AIN x Mine Korea 2026.pdf.lnkSecurity / IOTRUST:
CONFIDENTIAL IOTRUST OFFER.pdf.lnk
The strategic objective appears to be long-term surveillance and intelligence collection against South Korean organizations — not immediate destructive impact.
3. Technical Analysis
3.1 Initial Access Vector
Spearphishing emails carry obfuscated LNK files disguised as standard PDF documents. When the victim clicks the file, a decoy PDF is displayed to avoid suspicion while the malicious PowerShell script executes silently in the background.

Figure 1: LNK file containing an embedded PowerShell script — Source: FortiGuard Labs
3.2 Stage 1 — LNK File (Loader)
Evolution across versions:
Early versions (2024): Simple character concatenation used to conceal the GitHub C2 address and access token. Easily detectable — the script was clearly designed to execute a PowerShell command fetched from GitHub.
Intermediate versions: Basic character decoding functions added. Metadata still present: file name, size, modification date, and notably the "Name" field frequently reads "Hangul Document" — a reliable threat-hunting pivot.

Figure 2: Intermediate version LNK file — "Hangul Document" metadata still present — Source: FortiGuard Labs
Latest versions (2026): All identifying metadata has been removed. Only a decoding function p1 remains in the LNK arguments, accepting three parameters: location, length, and an XOR key. This function decodes both the decoy PDF and the PowerShell script for the next stage.

Figure 3: Latest LNK version — payload encoded, metadata removed — Source: FortiGuard Labs
3.3 Stage 2 — PowerShell Script (Core Malware)
The PowerShell script decoded from the LNK performs four primary tasks:
a) Anti-Analysis / Sandbox Evasion
The script scans the running process list to detect VMs, debuggers, and forensic tools. The list includes over 40 processes:
vmxnet, vmusrvc, vmsrvc, vmtoolsd, vmwaretray, vboxservice, vboxtray,
idaq, idaq64, autoruns, dumpcap, de4dot, hookexplorer, ilspy, lordpe,
dnspy, petools, autorunsc, resourcehacker, filemon, regmon,
procexp, procexp64, tcpview, tcpview64, Procmon, Procmon64,
vmmap, vmmap64, portmon, processlasso, Wireshark, Fiddler,
ida, ida64, ImmunityDebugger, WinDump, x64dbg, x32dbg, OllyDbg, ProcessHacker
If any process in the list is detected → the script terminates immediately.

Figure 4: PowerShell script scanning for sandbox/debugger processes — Source: FortiGuard Labs
b) Payload Deployment
Once a clean environment is confirmed, the script:
Reconstructs and Base64-decodes a series of encoded strings
Saves the plaintext payload to a randomly named folder within
%Temp%Drops a VBScript file

Figure 5: VBScript dropped into %Temp% — Source: FortiGuard Labs
c) Persistence via Scheduled Task
$action = New-ScheduledTaskAction -Execute 'wscript.exe' `
-Argument ('"' + $vbsFilePath + '"')
$trigger = New-ScheduledTaskTrigger -Once -At (Get-Date).AddMinutes(5) `
-RepetitionInterval (New-TimeSpan -Minutes 30)
$settings = New-ScheduledTaskSettingsSet -Hidden
Register-ScheduledTask `
-TaskName "Technical Paper for Creata Chain Task S-1-12-12-3-1231241245BVSKLERh-SD234GHSI56" `
-Action \(action -Trigger \)trigger -Settings $settings
The task runs wscript.exe against the VBScript every 30 minutes, with a task name crafted to resemble a legitimate technical document reference.
d) Initial Exfiltration — System Information
The script collects:
OS version and build number
Last boot time
List of currently running processes
Data is saved in the format: <timestamp>-<IP_address>-BEGIN.log, then uploaded to GitHub:
hxxps://api[.]github[.]com/repos/motoralis/singled/contents/kcca/technik
Using a hardcoded access token: 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

Figure 6: Script exfiltrating system information to GitHub via API — Source: FortiGuard Labs
3.4 C2 Infrastructure
The threat actor operates a strategically managed network of GitHub accounts:
| GitHub Account | Role | Status |
|---|---|---|
motoralis |
Primary operational hub — repo singled |
Actively used since 2025 |
God0808RAMA |
Secondary C2 | Active |
Pigresy80 |
Secondary C2 | Active |
entire73 |
Dormant / Backup | Largely inactive for months |
pandora0009 |
Secondary C2 | Active |
brandonleeodd93-blip |
Newly activated — redundancy | Activated weeks ago |
Infrastructure strategy:
Private repositories → payloads and exfiltrated logs hidden from public view
Traffic flows over HTTPS to github.com → blends with normal developer activity
GitHub is commonly whitelisted in enterprise environments → exfiltration goes unblocked

Figure 7: GitHub account motoralis — primary C2 hub with activity surge coinciding with LNK phishing waves — Source: FortiGuard Labs
3.5 Stage 3 — PowerShell Script (Live C2 Channel)
The Stage 3 script maintains a persistent C2 connection:
hxxps://raw[.]githubusercontent[.]com/motoralis/singled/main/kcca/paper[.]jim
Executed periodically via the Scheduled Task established earlier, this enables the attacker to:
Deliver additional modules or instructions
Execute remote commands
Monitor the victim over an extended period

Figure 8: Stage 3 PowerShell script maintaining C2 channel via raw.githubusercontent.com — Source: FortiGuard Labs
Keep-alive script: Collects network configuration and uploads logs periodically:
hxxps://api[.]github[.]com/repos/motoralis/singled/contents/jjyun/network/<Date>_<Time>-<IP_Address>-Real.log

Figure 9: Keep-alive script logging network config in Date_Time-IP-Real.log format — Source: FortiGuard Labs
3.6 Kill Chain / Attack Flow
| Step | Phase | Detailed Action | MITRE ID |
|---|---|---|---|
| 1 | Initial Access | Spearphishing email sent with LNK attachment disguised as PDF | T1566.001 |
| 2 | Execution | Victim clicks → LNK silently executes PowerShell, displays decoy PDF | T1204.002, T1059.001 |
| 3 | Defense Evasion | LNK decodes payload using XOR function p1(location, length, xorKey) |
T1027 |
| 4 | Defense Evasion | PowerShell scans process list, terminates if sandbox/debugger detected | T1497.001 |
| 5 | Execution | PowerShell Base64-decodes VBScript, drops to %Temp%\<random>\ |
T1059.005, T1140 |
| 6 | Persistence | Scheduled Task created to run VBScript every 30 minutes | T1053.005 |
| 7 | Discovery | Collects OS version, last boot time, running process list | T1082, T1057 |
| 8 | Exfiltration | Uploads BEGIN.log to GitHub API (motoralis/singled/kcca/technik) |
T1567.001 |
| 9 | C2 | Fetches instructions from raw.githubusercontent.com/motoralis/singled/main/kcca/paper.jim |
T1102.002 |
| 10 | Collection | Keep-alive script periodically collects network configuration | T1016 |
| 11 | Exfiltration | Periodically uploads Real.log to GitHub in Date_Time-IP-Real.log format |
T1567.001 |

Figure 10: Complete attack chain — from phishing LNK to persistent GitHub C2 — Source: FortiGuard Labs
4. TTPs — MITRE ATT&CK
| Tactic | Technique ID | Technique Name | Campaign Context |
|---|---|---|---|
| Initial Access | T1566.001 | Spearphishing Attachment | LNK file attached to phishing email, disguised as a legitimate PDF |
| Execution | T1204.002 | User Execution: Malicious File | Victim manually opens the LNK file |
| Execution | T1059.001 | PowerShell | PowerShell script runs silently as soon as LNK is opened |
| Execution | T1059.005 | VBScript | VBScript dropped and executed by wscript.exe |
| Defense Evasion | T1027 | Obfuscated Files or Information | XOR encoding in LNK arguments; Base64 encoding for VBScript payload |
| Defense Evasion | T1140 | Deobfuscate/Decode Files or Information | Function p1 XOR-decodes payload directly within the LNK |
| Defense Evasion | T1497.001 | Virtualization/Sandbox Evasion: System Checks | Scans 40+ analysis processes, terminates if detected |
| Defense Evasion | T1218.005 | System Binary Proxy Execution: wscript | Uses wscript.exe to execute VBScript — avoids dropping PE files |
| Persistence | T1053.005 | Scheduled Task/Job: Scheduled Task | "Technical Paper for Creata Chain Task..." runs every 30 minutes |
| Discovery | T1082 | System Information Discovery | Collects OS version, build number, last boot time |
| Discovery | T1057 | Process Discovery | Enumerates running processes, writes to BEGIN.log |
| Discovery | T1016 | System Network Configuration Discovery | Keep-alive script collects network configuration |
| Collection | T1074.001 | Data Staged: Local Data Staging | Log files staged in %Temp% prior to exfiltration |
| Command & Control | T1102.002 | Web Service: Bidirectional Communication | GitHub API used for both receiving instructions and exfiltration |
| Exfiltration | T1567.001 | Exfiltration Over Web Service: GitHub | BEGIN.log and Real.log uploaded to private GitHub repository |
5. Severity Assessment
Level: HIGH
| Criterion | Assessment | Notes |
|---|---|---|
| Impact Scope | High | Targets multiple sectors in South Korea; potential for regional expansion |
| Sophistication | High | LolBins, XOR encoding, sandbox evasion, GitHub C2, private repositories |
| Detectability | Difficult | Traffic hidden within HTTPS to github.com — routinely whitelisted |
| Actual Impact | Medium–High | System information exfiltration; potential escalation to long-term espionage |
| Exploitation Requirements | Low | Only requires a user click — no zero-day vulnerability needed |
| Persistence Level | High | Scheduled Task every 30 minutes, keep-alive mechanism, multiple backup GitHub accounts |
6. Analysis & Forecast
This section reflects analyst assessments based on collected data combined with current threat landscape context. Inferential assessments are explicitly labeled.
6.1 Campaign Assessment
This campaign reflects a deliberate shift by DPRK-linked APT groups away from deploying complex custom malware toward a "minimum footprint" model — prioritizing native Windows tools (PowerShell, VBScript, Scheduled Tasks) and trusted cloud services (GitHub). This evolution is consistent with trends observed from Kimsuky and Lazarus over the past 18 months.
The use of GitHub is not opportunistic — it represents a calculated architectural decision: GitHub holds a valid TLS certificate, maintains stable IP ranges, and is almost never blocked in corporate environments. Private repositories ensure that payloads and stolen data remain hidden from public view. This C2 model is particularly difficult to address: blocking GitHub entirely would disrupt legitimate organizational operations.
The "keep-alive with network logs" pattern suggests the objective is not immediate destructive action but sustained persistent access for long-term intelligence collection — consistent with the profile of Kimsuky, known for espionage campaigns focused on South Korea.
6.2 Likely Next Targets (Analyst Assessment)
Based on decoy PDF titles collected (AI strategic proposals, investment funds, blockchain):
High probability: Technology startups, venture capital firms, and fintech organizations in South Korea will remain priority targets — aligned with DPRK's need for economic intelligence gathering.
Medium probability: The campaign may expand to Japan and Taiwan — adjacent technology/investment markets with similar target profiles.
Watch for: If GitHub is widely blocked or detected, the threat actor may pivot to GitLab, Bitbucket, or Azure DevOps as alternative C2 platforms — a pattern observed in similar campaigns.
6.3 Risk to Organizations Outside South Korea
The current campaign is clearly focused on South Korea. However:
Indirect risk exists for organizations with partners, subsidiaries, or joint ventures in South Korea — phishing emails may propagate along supply chains.
Organizations in technology, blockchain, and international investment sectors should remain alert — DPRK APT groups have a history of expanding targeting once TTPs are proven effective in a region.
Any organization that whitelists GitHub in its egress policy carries latent risk if a similar campaign targets it directly.
6.4 Broader Threat Landscape Implications
This campaign is part of a larger trend: APT groups increasingly leveraging legitimate cloud services (GitHub, OneDrive, Google Drive, Dropbox, Notion) as C2 to bypass defenses based on domain reputation and TLS inspection. This poses a fundamental challenge to traditional perimeter-based defense models.
The "LolBins + trusted cloud C2" methodology carries a significantly lower detection rate than custom malware and is being adopted by multiple APT groups — not exclusively DPRK-linked actors.
7. Recommendations & Defensive Measures
7.1 Immediate Actions (0–24h)
Threat Hunting — search for current indicators of compromise:
// KQL — Find abnormal Scheduled Tasks containing wscript.exe and VBS in Temp
DeviceProcessEvents
| where ProcessCommandLine has_all ("wscript.exe", "Temp")
| where InitiatingProcessFileName in~ ("svchost.exe", "taskeng.exe", "taskhostw.exe")
| project Timestamp, DeviceName, ProcessCommandLine, InitiatingProcessCommandLine
| order by Timestamp desc
// KQL — Find PowerShell calling GitHub API (exfiltration pattern)
DeviceNetworkEvents
| where RemoteUrl has "api.github.com/repos"
| where InitiatingProcessFileName =~ "powershell.exe"
| project Timestamp, DeviceName, RemoteUrl, InitiatingProcessCommandLine
| order by Timestamp desc
// KQL — Find LNK file execution spawning obfuscated PowerShell
DeviceProcessEvents
| where InitiatingProcessFileName =~ "explorer.exe"
| where FileName =~ "powershell.exe"
| where ProcessCommandLine has_any ("-enc", "-EncodedCommand", "XOR", "FromBase64String")
| project Timestamp, DeviceName, ProcessCommandLine, InitiatingProcessCommandLine
Check Scheduled Tasks:
# Find abnormal Scheduled Tasks containing wscript.exe
Get-ScheduledTask | Where-Object {
$_.Actions.Execute -like "*wscript*" -or
$_.Actions.Arguments -like "*Temp*"
} | Select-Object TaskName, TaskPath, @{n='Execute';e={$_.Actions.Execute}} | Format-List
Block/Report C2-linked GitHub Accounts:
Contact GitHub Security to report and request suspension of: motoralis, God0808RAMA, Pigresy80, entire73, pandora0009, brandonleeodd93-blip
Revoke the compromised GitHub token:
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
→ This token has been publicly disclosed. Verify whether it appears in your environment.
7.2 Detection Rules
Sigma Rule — LNK File Spawning Encoded PowerShell:
title: LNK File Spawning Obfuscated PowerShell
id: a1b2c3d4-e5f6-7890-abcd-ef1234567890
status: experimental
description: Detects LNK file spawning PowerShell with encoded/obfuscated command — pattern of DPRK LNK campaigns
references:
- https://www.fortinet.com/blog/threat-research/dprk-related-campaigns-with-lnk-and-github-c2
author: SOC Analyst Team
date: 2026-04-10
tags:
- attack.initial_access
- attack.t1566.001
- attack.execution
- attack.t1059.001
- attack.defense_evasion
- attack.t1027
logsource:
category: process_creation
product: windows
detection:
selection:
ParentImage|endswith: '\explorer.exe'
Image|endswith: '\powershell.exe'
CommandLine|contains:
- '-enc '
- '-EncodedCommand'
- 'FromBase64String'
- 'XOR'
lnk_parent:
ParentCommandLine|contains: '.lnk'
condition: selection and lnk_parent
falsepositives:
- Legitimate admin scripts executed from shortcut files
level: high
Sigma Rule — Suspicious Scheduled Task with VBScript in Temp:
title: Suspicious Scheduled Task VBScript Temp Execution
id: b2c3d4e5-f6a7-8901-bcde-f12345678901
status: experimental
description: Detects Scheduled Task running wscript.exe with VBScript in %Temp% — persistence mechanism of DPRK campaign
references:
- https://www.fortinet.com/blog/threat-research/dprk-related-campaigns-with-lnk-and-github-c2
author: SOC Analyst Team
date: 2026-04-10
tags:
- attack.persistence
- attack.t1053.005
- attack.execution
- attack.t1059.005
logsource:
category: process_creation
product: windows
detection:
selection:
ParentImage|endswith:
- '\svchost.exe'
- '\taskeng.exe'
- '\taskhostw.exe'
Image|endswith: '\wscript.exe'
CommandLine|contains:
- '\Temp\'
- '\AppData\Local\Temp\'
condition: selection
falsepositives:
- Legitimate software using wscript in temp (rare)
level: high
Sigma Rule — GitHub API Exfiltration via PowerShell:
title: PowerShell Exfiltration to GitHub API
id: c3d4e5f6-a7b8-9012-cdef-123456789012
status: experimental
description: Detects PowerShell sending data to GitHub API — exfiltration pattern of DPRK campaign
references:
- https://www.fortinet.com/blog/threat-research/dprk-related-campaigns-with-lnk-and-github-c2
author: SOC Analyst Team
date: 2026-04-10
tags:
- attack.exfiltration
- attack.t1567.001
- attack.command_and_control
- attack.t1102.002
logsource:
category: network_connection
product: windows
detection:
selection:
Image|endswith: '\powershell.exe'
DestinationHostname|contains:
- 'api.github.com'
- 'raw.githubusercontent.com'
DestinationPort: 443
filter_legitimate:
CommandLine|contains:
- 'chocolatey'
- 'winget'
- 'scoop'
condition: selection and not filter_legitimate
falsepositives:
- Legitimate DevOps automation via PowerShell
level: medium
7.3 Long-Term Prevention
Email & File:
Configure email gateways to block or quarantine
.lnkfiles attached to emails from external sendersEnable Content Disarm and Reconstruction (CDR) where available to strip active code from files before delivery
Conduct security awareness training on LNK files disguised as PDFs — this remains a highly effective phishing technique
PowerShell & Scripting:
Enable PowerShell Script Block Logging and Module Logging across all endpoints
Enforce Constrained Language Mode for PowerShell on non-administrative workstations
Monitor
wscript.exeandcscript.exeexecution — especially when the parent process issvchost.exe
GitHub & Cloud C2:
Do not block GitHub entirely (operational disruption risk) — instead:
Monitor and alert when PowerShell or script processes call
api.github.comorraw.githubusercontent.comImplement User and Entity Behavior Analytics (UEBA) to detect anomalous GitHub API calls
Enforce SSL/TLS inspection for GitHub traffic where policy permits
Scheduled Tasks:
Monitor creation of new Scheduled Tasks, particularly those invoking
wscript.exewith paths in%Temp%Restrict Scheduled Task creation rights for non-administrative users where not operationally required
7.4 References
FortiGuard Labs — DPRK-Related Campaigns with LNK and GitHub C2 (April 2, 2026)
Security Affairs — Phishing LNK files and GitHub C2 power new DPRK cyber attacks (April 6, 2026)
The Hacker News — DPRK-Linked Hackers Use GitHub as C2 (April 9, 2026)
CSO Online — North Korean hackers abuse LNKs and GitHub repos
8. Indicators of Compromise (IOCs)
Note: URLs and domains are defanged (brackets around
.) to prevent accidental activation. Revoke the listed token if found in your environment.
8.1 Domain / URL — C2 Endpoints
| URL | Description | Source |
|---|---|---|
hxxps://api[.]github[.]com/repos/motoralis/singled/contents/kcca/technik |
Upload initial system log (BEGIN.log) | FortiGuard Labs |
hxxps://raw[.]githubusercontent[.]com/motoralis/singled/main/kcca/paper[.]jim |
Fetch C2 instructions / additional modules | FortiGuard Labs |
hxxps://api[.]github[.]com/repos/motoralis/singled/contents/jjyun/network/<Date>_<Time>-<IP_Address>-Real.log |
Upload network keep-alive logs | FortiGuard Labs |
hxxps://api[.]github[.]com/repos/motoralis |
Primary C2 repository root | FortiGuard Labs |
8.2 GitHub Accounts — C2 Infrastructure
| Account | Role | Notes |
|---|---|---|
motoralis |
Primary C2 hub | Active since 2025 |
God0808RAMA |
Secondary | Active |
Pigresy80 |
Secondary | Active |
entire73 |
Dormant backup | Largely inactive |
pandora0009 |
Secondary | Active |
brandonleeodd93-blip |
Newly activated | Redundancy |
8.3 Credentials — C2 Access Token
| Type | Value | Notes |
|---|---|---|
| GitHub Personal Access Token | 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 |
Hardcoded in PowerShell script. Publicly disclosed — revoke if present in environment |
8.4 File Hashes — LNK Files (SHA-256)
| SHA-256 | Filename | Notes |
|---|---|---|
af0309aa38d067373c54b2a7774a32f68ab72cb2dbf5aed74ac784b079830184 |
TRAMS WINBOT AI Strategic Proposal.pdf.lnk |
AI/Tech lure |
9c3f2bd300ad2ef8584cc48adc47aab61bf85fc653d923e106c73fc6ec3ea1dc |
전략적 파트너십 상세 제안서.pdf.lnk |
Partnership Proposal lure |
f20fde3a9381c22034f7ecd4fef2396a85c05bfd54f7db3ad6bcd00c9e09d421 |
상세 제안서 - 미래에셋 X AYC Fund.pdf.lnk |
Investment Fund lure |
484a16d779d67c7339125ceac10b9abf1aa47f561f40058789bfe2acda548282 |
CONFIDENTIAL IOTRUST OFFER.pdf.lnk |
Security Offer lure |
c0866bb72c7a12a0288f434e16ba14eeaa35d3c4cff4a86046c553c15679c0b5 |
(CONFIDENTIAL) AIN x Mine Korea 2026.pdf.lnk |
Web3/Blockchain lure |
8.5 File System Artifacts
| Path | Description |
|---|---|
%Temp%\<random_folder>\ |
VBScript and payload drop directory |
%Temp%\<timestamp>-<IP>-BEGIN.log |
Initial system info exfiltration log |
Scheduled Task: Technical Paper for Creata Chain Task S-1-12-12-3-* |
Persistence mechanism — runs wscript.exe every 30 minutes |
8.6 Malware Detection Signature
| Vendor | Signature Name |
|---|---|
| FortiGuard Antivirus | LNK/Agent.ALN!tr |






