Is your Android still safe? Albiriox is proving otherwise…
Albiriox - A highly dangerous "Malware-as-a-Service" designed malware has been discovered on Android, aiming to steal your device.

Overview
At the end of 2025, the Cleafy Threat Intelligence team—a group dedicated to researching, analyzing, and monitoring cybersecurity threats targeting the global financial sector—recorded a campaign targeting Android users. This campaign aimed to spread the malware “Albiriox,” a new Android malware strain that is very difficult for antivirus software to detect.
Since early October 2025, Albiriox has been publicly released as a “Malware-as-a-Service” (MaaS), allowing attackers or even regular users to easily purchase and use it for about $650/month to attack any device they choose.
According to Cleafy's analysis, the attackers behind Albiriox are primarily Russian hackers, and their targets are clear: financial, banking, fintech applications, and cryptocurrency wallets.

Scope of Impact
According to Cleafy's analysis, Albiriox has targeted over 400 financial applications and crypto wallets (banking, fintech, payment apps, crypto exchanges, e-wallets...) globally, meaning any Android user using financial or crypto apps could be at risk.
As mentioned above, Albiriox is distributed as a "MaaS" (Malware-as-a-Service), allowing any criminal with enough money to rent it (~$650–720/month) to easily use it. This lowers the technical barrier, enabling the malware to spread widely through various "affiliates."
The distribution campaign uses social engineering (phishing SMS, shortened links, fake app store pages, even WhatsApp-based lures). This method can spread quickly, especially in countries or regions where users habitually install apps from unfamiliar links or pay little attention to security.

Initial Context
During the initial monitoring phase, Cleafy recorded one of the first distribution campaigns related to Albiriox RAT. Here, attackers used SMS messages with shortened links to lead users to:
Phishing websites,
Fake legitimate services,
Content presented in German,
Lure users into installing an "official app" outside of Google Play.
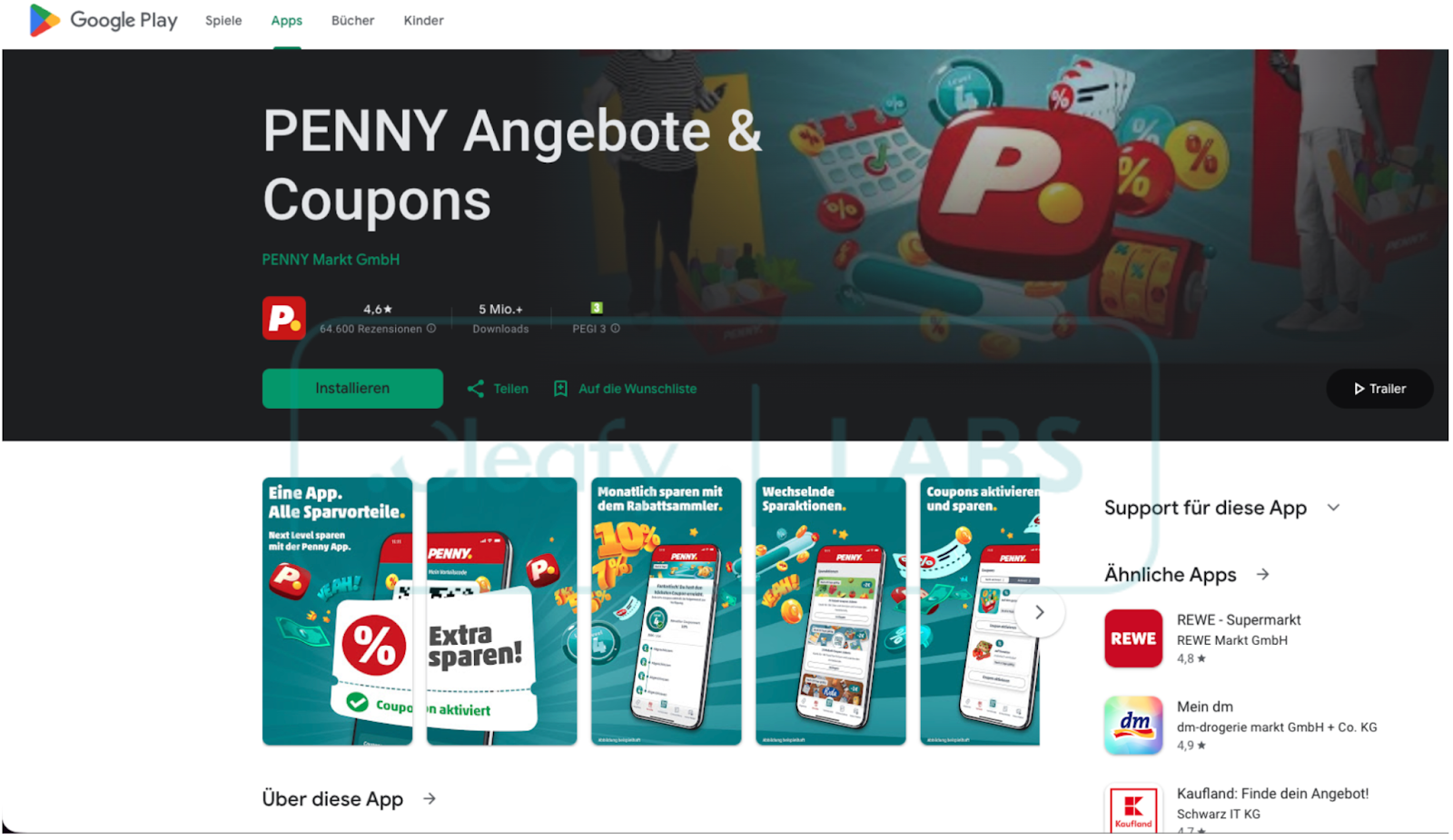
Attackers will remind you via SMS about an issue related to: delivery, account, or security verification. Then, the victim is led to an "official app approved by Google," and naturally, users will easily accept and install a malicious .apk file.


As designed in the JavaScript code above, the attacker will collect information such as:
Victim's phone number
Country
Card type / Gas station
Timestamp
All the collected data will then be sent via POST method to a Telegram channel of the attack group as a C2 communication channel.

Technical Analysis
In this section, we will go through the details about Albiriox. Like many well-known Android banking Trojans, its core functions align with established patterns commonly seen in the mobile threat landscape, including “Overlay attacks” and “VNC-based remote control.” As with the initial attacks, the attacker uses a fake Penny app as bait for the Albiriox Payload. They use the JSONPacker technique, a form of code obfuscation and dynamic unpacking used to distribute the Payload.
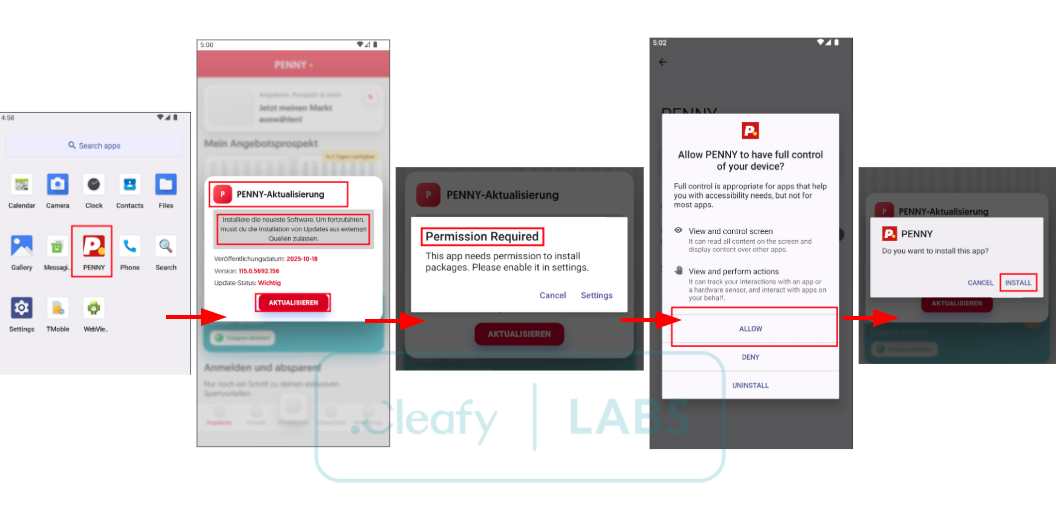
After installation and launch, it will immediately deploy attack techniques. Instead of functioning like a legitimate app, it displays a fraudulent system update interface designed to pressure the victim into granting the requested permissions. The attacker's main goal is to gain the critical permission “Install unknown apps,” which allows installations outside the store. This is extremely dangerous because the attacker can download the final Payload, Albiriox.
An initial malicious .apk file will be executed: com.nmz.nmz to store a list of popular cryptocurrency wallet apps, from which it will trigger the corresponding attack modules.


Next, a piece of code performs the initial handshake between the victim's device and the command and control (C2) server.
The goal is to register the device, send unique identification information, device characteristics, and bot version so the server can:
Track the device
Categorize by model, version, brand
Activate the corresponding payload or command
Bind control rights to a unique HWID

After gathering information and connecting to the C2 server, Albiriox continues to deploy a series of techniques that allow it to take control, manipulate, and commit fraudulent actions—almost undetectably. Specifically, it will perform Remote Access / RAT + VNC-streaming. Here, Albiriox includes a VNC module, allowing the attacker to view the victim's device screen in real-time, manipulate the UI, click, swipe, enter text, and open or close apps.

Furthermore, Albiriox uses what is called AC-VNC, which means the malware will use Android's Accessibility service to stream "node-level UI data," not just pixel images. This helps bypass screenshot prevention measures that many banking/crypto apps often use.
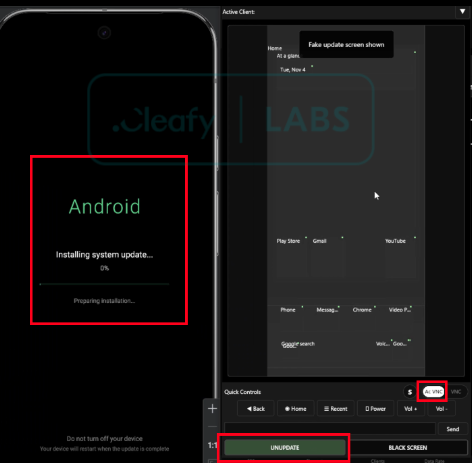

And of course, the consequences of this malware are extremely serious. Users can lose money or crypto without knowing, as the screen can be covered and actions happen invisibly. Additionally, common security measures (2-FA, trusted devices, IP checks, behavior checks, etc.) can be bypassed because the transaction appears to be made from the victim's own device.
Conclusion
The emergence of Albiriox marks a concerning shift in the ecosystem of financial attack malware on Android. It no longer stops at stealing information or collecting sensitive data; Albiriox clearly shows a new trend: taking control of the device to commit fraud directly on the victim's device (On-Device Fraud). With the ability to combine Accessibility abuse, AC-VNC streaming, and a powerful UI interaction command set, Albiriox allows attackers to operate like a "legitimate user," making traditional fraud prevention systems less effective.
The commercialization of Albiriox as Malware-as-a-Service increases its danger, as any threat actor can easily access this tool to launch attack campaigns targeting banks, cryptocurrency wallets, and financial apps worldwide. This shows the blurring line between "skilled" and "unskilled" cybercriminals, while the potential damage level is unprecedentedly high.
In this context, financial institutions and fintech companies need to proactively upgrade their defense methods—from real-time device monitoring and detecting unusual Accessibility interference to behavior and context-based fraud prevention mechanisms. At the same time, users must be more vigilant against increasingly sophisticated phishing techniques, especially when installing apps from unofficial sources.
Recommendations
Awareness of SMS Scams
Check Dangerous Permissions in Android
Be immediately suspicious if an app requests the following permissions:
Accessibility
Draw over other apps
Screen capture (MediaProjection)
Device admin
Install unknown apps
Special Warning for Crypto Users
Do not store seed phrases/mnemonics on your phone
Use a hardware wallet
Enable alerts when apps access the clipboard
IOC
File Hash
b6bae028ce6b0eff784de1c5e766ee33
61b59eb41c0ae7fc94f800812860b22a
f09b82182a5935a27566cdb570ce668f
f5b501e3d766f3024eb532893acc8c6c
C2 Server
- 194.32.79.94
Domain
google-app-download[.]download
google-get[.]download
google-aplication[.]download
play.google-get[.]store
google-app-get[.]com
google-get-app[.]com
google-app-install[.]com