The Underground Access Economy: Storm Infostealer and the Era of Passwordless Attacks

Executive Summary
In early 2026, Varonis Threat Labs identified Storm — a new infostealer circulating on underground cybercrime networks for under $1,000 per month. Storm is not simply another commodity stealer: it represents the next evolutionary step in how attackers compromise digital identities without ever needing a password or triggering MFA.
Varonis' panel analysis confirmed 1,715 victims across multiple countries, including Vietnam. A single Storm-infected browser can hand an operator authenticated access to an organization's entire SaaS estate, cloud environment, and internal tools — through valid, already-authenticated session cookies, without triggering any password-based detection.
Storm does not exist in a vacuum. It is a product of a mature access economy — an underground ecosystem where every link in the attack chain has been specialized, priced, and commoditized.
Highest priority action: Immediately review browser-based credential storage policy for privileged accounts, and enable alerting for impossible travel and fresh token anomalies in Entra ID / Google Workspace.
1. The Access Economy: When Attacks Become an Industry
"Attackers don't break in, they log in" is no longer just a warning — it is an accurate description of a functioning business model.
Underground marketplaces now operate with the full infrastructure of a legitimate market: reputation systems for sellers, escrow to guarantee transactions, role specialization, and tiered pricing by target value. One operator runs infostealers across thousands of machines. Another extracts and sorts credentials. A third sells curated access. A fourth deploys ransomware. Each party focuses on their specialty, and the entire chain operates with disturbing efficiency.
Four primary product categories are traded in this market:
1.1 Remote Access Credentials
VPN and RDP credentials are listed with full metadata: organization name, geographic region, industry, and VPN product in use. Pricing scales with target value. Varonis documented a confirmed seller offering seven Fortinet SSL VPN credentials targeting educational institutions — a lower-value market. Credentials for financial organizations or government agencies command significantly higher prices, sometimes with "exclusive access" guarantees — meaning the seller will not sell the same access to multiple buyers simultaneously.
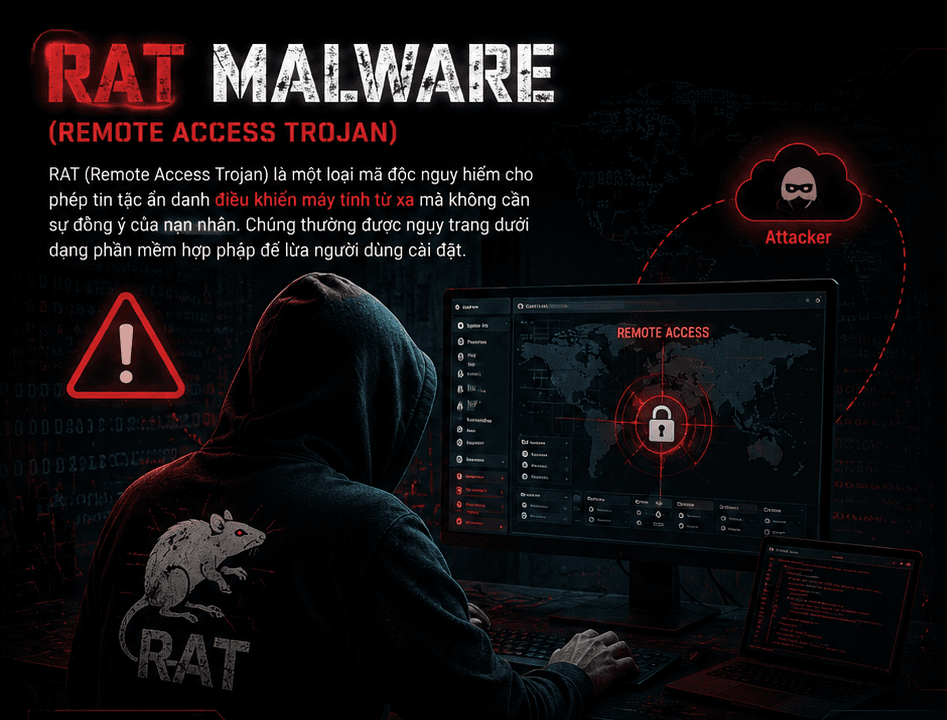
1.2 Infostealer Logs
This is the largest product category by volume. Infostealer families including Redline, Raccoon, Vidar, Lumma, and Risepro harvest browser-saved passwords, session cookies, autofill data, cryptocurrency wallet seeds, and authentication tokens — then distribute structured, searchable logs through subscription channels.
DAISY CLOUD is a representative example: a stealer log distribution service operating on subscription at $400 for seven days or $1,350 per month. Logs are indexed and searchable by credential type, country, and platform.
Session cookies are the highest-value product in this category. If an infostealer captures a valid cookie, an attacker can import it directly into a browser and inherit the fully authenticated session — no password needed, no MFA prompt triggered.
1.3 Breach Databases
Data from historical breaches is categorized by geography, sector, freshness, and field completeness (does the record include email + phone + password hash?). This data serves multiple purposes: credential stuffing, organizational reconnaissance, and building employee profiles for targeted spear-phishing.
One example documented in Varonis research: a dump from three Egyptian government ministries containing 24,000 HTML files and thousands of PDFs with citizen records.
1.4 Web Shells and Backdoors
Web shells bypass authentication entirely. These are backdoors planted on already-compromised servers that give buyers command execution capability over HTTP without any credentials. Once installed, a web shell persists independently of the original vulnerability — patching the vulnerability does not remove the shell.
One listing Varonis documented: root RCE and shell access to a government revenue management system (Linux, root-level permissions) — priced at $400, from a seller with a reputation score of 61 built over four months of operation.
2. Storm — A Next-Generation Infostealer
Storm is the clearest evidence of where infostealers are heading: from raw data dumping tools to automated identity takeover platforms.
2.1 Technical Context: Why Server-Side Decryption Matters
Traditional infostealers decrypted browser credentials on the victim's machine by loading SQLite libraries and directly accessing credential stores. EDR and endpoint security tools adapted to this — anomalous access to browser databases became one of the clearest signals of malicious activity on an endpoint.
In July 2024, Google deployed App-Bound Encryption in Chrome 127, binding encryption keys to the Chrome process itself and making local decryption significantly harder. This is where Storm and next-generation stealers pivoted: rather than decrypting on the endpoint, they exfiltrate the encrypted data blob to the attacker's server and decrypt it there.
The result: no suspicious SQLite access on the endpoint, no browser credential store access anomaly — the signals that EDR was trained to detect are simply absent.
2.2 Data Collected
Storm harvests everything an operator needs to restore a hijacked session remotely:
- Saved passwords and autofill data
- Session cookies (all browsers)
- Google account tokens and refresh tokens
- Browser-saved credit card data
- Browsing history
- Session data from Telegram, Signal, and Discord
- Cryptocurrency wallets via both browser extensions and desktop apps
- Documents from user directories
- System information and screenshots Storm handles both Chromium-based browsers (Chrome, Edge, Brave) and Gecko-based browsers (Firefox, Waterfox, Pale Moon) — entirely server-side. This distinguishes it from StealC V2, which still processes Firefox locally.
2.3 The Session Restore Feature: The Most Dangerous Capability
After decrypting the stolen data, Storm does not simply dump credentials into an operator panel for manual exploitation. It automates the next step:
- The operator supplies the victim's Google Refresh Token into the panel
- Combined with a SOCKS5 proxy geographically matched to the victim (same country/ISP)
- The panel silently restores the victim's authenticated session The result: the operator has a live, authenticated session originating from a geographically plausible IP address, triggering no password-based alerts. Every SaaS platform the victim was logged into — Microsoft 365, Google Workspace, Salesforce, internal tools — is now accessible to the attacker.
This technique is not new: Varonis' Cookie-Bite research demonstrated that stolen Azure Entra ID session cookies completely neutralize MFA. SessionShark showed phishing kits intercepting session tokens in real time. Storm is the productization of these known techniques — packaged into a subscription service with operator-friendly UX.
2.4 Confirmed Scope
Varonis found 1,715 entries in panel data, originating from Brazil, Ecuador, India, Indonesia, Vietnam, and the United States. While not all entries can be confirmed as genuine victims (test data may be included), the diversity of IP addresses, ISPs, and data sizes indicates active malicious campaigns are ongoing.
Stolen credentials cover a range of high-value platforms including Google, Facebook, Twitter/X, financial accounts, and corporate SaaS.
3. Kill Chain
[Infection Vector]
Phishing email / Malicious download / Compromised third-party tool
│
▼
[Collection — Endpoint]
Storm harvests: passwords, cookies, tokens, wallets, documents
→ No local decryption, no direct SQLite access
→ Packages data as encrypted blob
│
▼
[Exfiltration → C2 Server]
Encrypted blob shipped to attacker-controlled server
│
▼
[Server-Side Decryption]
Attacker server decrypts all browser data
→ Credentials and session cookies dumped to operator panel
│
▼
[Session Restore — Automation]
Google Refresh Token + SOCKS5 proxy (geo-matched to victim)
→ Panel silently restores authenticated session
│
▼
[Impact]
Authenticated access to SaaS, cloud, internal tools
→ No password alert triggered, no MFA required
4. MITRE ATT&CK Mapping
| Tactic | Technique ID | Technique Name | Notes |
|---|---|---|---|
| Initial Access | T1566 | Phishing | Primary delivery vector |
| Initial Access | T1078 | Valid Accounts | Using purchased VPN/RDP credentials from market |
| Credential Access | T1555.003 | Credentials from Web Browsers | Core Storm capability |
| Credential Access | T1539 | Steal Web Session Cookie | Priority target |
| Credential Access | T1528 | Steal Application Access Token | Google Refresh Token |
| Defense Evasion | T1027 | Obfuscated Files or Information | Encrypted blob avoids local detection |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | Encrypted blob shipped to attacker server |
| Persistence | T1505.003 | Web Shell | Applies to web shell access brokers |
| Initial Access | T1190 | Exploit Public-Facing Application | Vector for web shell installation |
| Lateral Movement | T1550.004 | Web Session Cookie | Using cookie to pivot across services |
5. Detection & Threat Hunting
5.1 Endpoint Signals (Microsoft Defender for Endpoint)
With server-side decryption, local signals are weaker than previous-generation stealers — but they do not disappear entirely:
// Detect anomalous child processes spawned by browsers — potential Storm loader activity
DeviceProcessEvents
| where InitiatingProcessFileName in~ ("chrome.exe", "msedge.exe", "firefox.exe")
| where FileName !in~ ("chrome.exe", "msedge.exe", "firefox.exe", "crashpad_handler.exe")
| where ProcessCommandLine !contains "extension"
| project Timestamp, DeviceName, InitiatingProcessFileName, FileName, ProcessCommandLine
| order by Timestamp desc
// Monitor anomalous access to browser credential stores
DeviceFileEvents
| where FolderPath has_any (
@"\AppData\Local\Google\Chrome\User Data\Default\Login Data",
@"\AppData\Local\Microsoft\Edge\User Data\Default\Login Data",
@"\AppData\Roaming\Mozilla\Firefox\Profiles"
)
| where InitiatingProcessFileName !in~ ("chrome.exe", "msedge.exe", "firefox.exe", "MicrosoftEdgeUpdate.exe")
| project Timestamp, DeviceName, InitiatingProcessFileName, FolderPath, ActionType
5.2 Identity Signals (Microsoft Entra ID)
Session hijacking leaves clear traces at the identity layer — this is where detection is most effective:
// Impossible travel following successful sign-in — indicates session restore with proxy
SigninLogs
| where ResultType == 0
| summarize
Locations = make_set(Location),
IPAddresses = make_set(IPAddress),
Count = count()
by UserPrincipalName, bin(TimeGenerated, 1h)
| where array_length(Locations) > 1
| project TimeGenerated, UserPrincipalName, Locations, IPAddresses, Count
// Refresh token use from unknown IP — Google Refresh Token abuse pattern
AADNonInteractiveUserSignInLogs
| where AuthenticationProtocol == "refreshToken"
| where NetworkLocationDetails !contains "trustedNamedLocation"
| join kind=leftouter (
SigninLogs
| where TimeGenerated > ago(30d)
| summarize KnownIPs = make_set(IPAddress) by UserPrincipalName
) on UserPrincipalName
| where IPAddress !in (KnownIPs)
| project TimeGenerated, UserPrincipalName, IPAddress, AppDisplayName, Location
5.3 Network Signals
- Monitor outbound connections from endpoints to non-whitelisted IPs/domains, particularly following user login activity
- SOCKS5 proxy traffic combined with anomalous browser activity — consistent with session restore operations
- Large encrypted outbound transfers from workstations (encrypted blob exfiltration)
5.4 Required Log Sources
| Source | Purpose |
|---|---|
| MDE — Process Creation | Detect Storm loader / child process anomaly |
| MDE — File Events | Monitor browser credential store access |
| Entra ID Sign-in Logs | Session hijack detection, impossible travel |
| Entra ID Non-Interactive Logs | Refresh token abuse detection |
| Network Proxy Logs | Exfiltration and SOCKS5 detection |
| Microsoft Sentinel — UEBA | Behavioral baseline for user sessions |
6. IOC & Artifacts
# Related Infostealer Ecosystem
Redline Stealer
Raccoon Stealer
Vidar
Lumma Stealer
Risepro
# Distribution Services
DAISY CLOUD (stealer log subscription service)
→ Pricing: \(400 / 7 days | \)1,350 / month
# Storm Binary Hashes
[NEEDS VERIFICATION: Varonis has not released specific Storm binary hashes in open sources]
# Storm C2 Infrastructure
[NEEDS VERIFICATION: C2 domains/IPs not published in public reporting at time of writing]
# Session Restore Technique Indicator
Google Refresh Token abuse + geographically matched SOCKS5 proxy
→ Detect via: AADNonInteractiveUserSignInLogs with refreshToken auth from unknown IP
7. Analysis
Storm is not a zero-day and does not rely on fundamentally new techniques. Every core capability — server-side decryption, session cookie theft, refresh token abuse — has been previously documented. What Storm does is productize the entire workflow into a subscription service with an operator interface simple enough that technical depth is no longer required.
This is more concerning than any novel technique: the barrier to entry for identity-based attacks continues to fall.
The presence of Vietnam in Storm's panel data is a specific signal, not a general warning. Multiple financial institutions and government agencies in Vietnam currently use browser-based SSO and OAuth for internal systems — this is a direct attack surface. An employee with an active browser session into a core banking web portal, or into a Microsoft 365 tenant, is a high-value target for a Storm operator.
The broader trend is clear: infostealers are rapidly shifting from noisy local theft (increasingly caught by EDR) toward server-side stealth with higher automation. In the next two years, session hijacking will become the primary initial access vector for account takeover, displacing traditional credential stuffing that MFA has largely throttled.
A critical operational point for SOC teams: an infostealer incident is an identity incident. Remediating the malware on the endpoint and closing the ticket is insufficient. The full response must include reviewing all SaaS OAuth grants, mailbox rules, and SSO integrations — immediately after confirming infection. Any session active at the time of compromise should be considered stolen until proven otherwise.
8. Recommendations
Immediate (0-24h)
- Audit browser credential storage policy: Stop saving passwords for high-value accounts (admin portals, banking systems, cloud consoles) in browsers. Enforce a dedicated password manager with administrative controls.
- Enable Entra ID UEBA alerting: Configure alerts for impossible travel, refresh token use from unknown locations, and sign-ins originating from anonymous proxies or SOCKS endpoints.
- Revoke active sessions: For admin and privileged accounts, revoke all active session tokens and require re-authentication.
Short-term (1-7 days)
- Deploy phishing-resistant MFA: FIDO2/passkeys for high-privilege accounts. Note: TOTP and SMS-based MFA do not protect against session hijacking post-authentication.
- Threat hunt: Search for anomalous browser child processes and file access to browser credential stores initiated by non-browser processes.
- Audit OAuth grants and SSO: Revoke grants for third-party applications no longer in use. Identify OAuth applications recently authorized outside of normal approval workflows.
- Monitor SOCKS5 traffic: Outbound SOCKS5 from workstations not on an established whitelist is a high-confidence indicator.
Long-term
- Build an "Infostealer = Identity Incident" playbook: Steps must include session revocation, OAuth grant audit, mailbox rule review, SSO integration check, and HR notification regarding potential data exposure scope.
- Session lifetime enforcement: Enforce short-lived session tokens across SaaS platforms. Negotiate configurable session timeout with vendors where this is not default.
- Continuous authentication evaluation: Assess solutions that enforce re-authentication when location shift or device fingerprint change is detected within an active session.
- Underground monitoring: Subscribe to threat intelligence feeds covering stealer log marketplaces to detect early when organizational credentials appear in underground channels.
9. References
- Varonis Threat Labs, Daniel Kelley — A Quiet "Storm": Infostealer Hijacks Sessions, Decrypts Server-Side (April 2026): https://www.varonis.com/blog/storm-infostealer
- Varonis Threat Labs, Daniel Kelley — How Cybercriminals Buy Access: Logins, Cookies, and Backdoors (February 2026): https://www.varonis.com/blog/how-hackers-buy-access
- Varonis Threat Labs — Cookie-Bite: Stolen Azure Entra ID Session Cookies and MFA Bypass: https://www.varonis.com/blog/cookie-bite
- BleepingComputer — The silent "Storm": New infostealer hijacks sessions, decrypts server-side (April 2026): https://www.bleepingcomputer.com/news/security/the-silent-storm-new-infostealer-hijacks-sessions-decrypts-server-side/
- Infosecurity Magazine — New 'Storm' Infostealer Remotely Decrypts Stolen Credentials (April 2026): https://www.infosecurity-magazine.com/news/storm-infostealer-remotely/
- MITRE ATT&CK — T1539: Steal Web Session Cookie: https://attack.mitre.org/techniques/T1539/
- MITRE ATT&CK — T1555.003: Credentials from Web Browsers: https://attack.mitre.org/techniques/T1555/003/