ZeroDayRAT: The new generation mobile spyware platform explodes on Telegram and poses a global threat

Overview
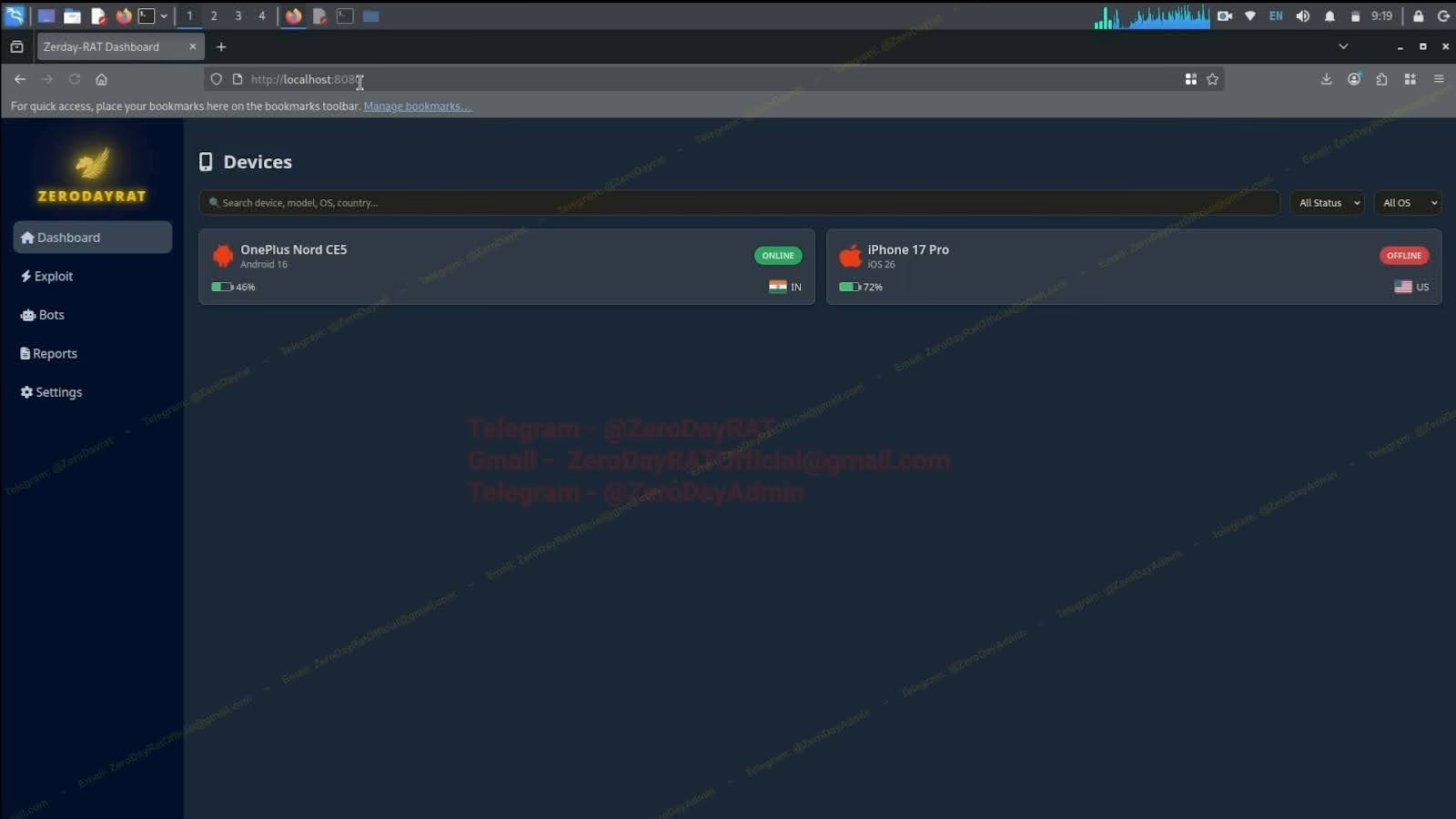
Recently, cybersecurity researchers have released details about ZeroDayRAT, a new generation mobile spyware platform being openly sold on Telegram. It has real-time spying capabilities, data theft, device control, and financial theft on both Android and iOS.
Worryingly, this platform is professionally built as a "commercial service," with dedicated sales, support, and update channels for buyers, bringing mobile espionage closer to a Spyware-as-a-Service model.
1. ZeroDayRAT – A complete mobile espionage toolkit
ZeroDayRAT supports:
Android 5 to 16
iOS up to version 26, including iPhone 17 Pro
No advanced technical skills required; buyers receive:
APK/iOS payload builder
Self-hosted control panel
Telegram channels for updates and support
Common distribution methods
Smishing (SMS containing malicious links)
Phishing email
Fake app stores
Links shared via WhatsApp, Telegram
Victims download a "legitimate" app, but in reality, it's a spyware version custom-built for each customer.
2. Data collection and user monitoring capabilities
After infiltration, ZeroDayRAT immediately sends data to the panel.
2.1. Device Overview
Here, the attacker sees all the device information:
Model, OS version, battery, country
SIM, carrier, numbers of both SIMs
App usage time
Activity timeline
Most recent SMS messages
These capabilities are enough to profile users: who they interact with, app usage habits, activity hours, and which banking services are used...
2.2. Real-time location tracking
ZeroDayRAT continuously collects GPS data, displaying:
Current location
Movement history
Google Maps embedded directly in the panel
The device is turned into a literal "tracking machine."
2.3. Collect notifications
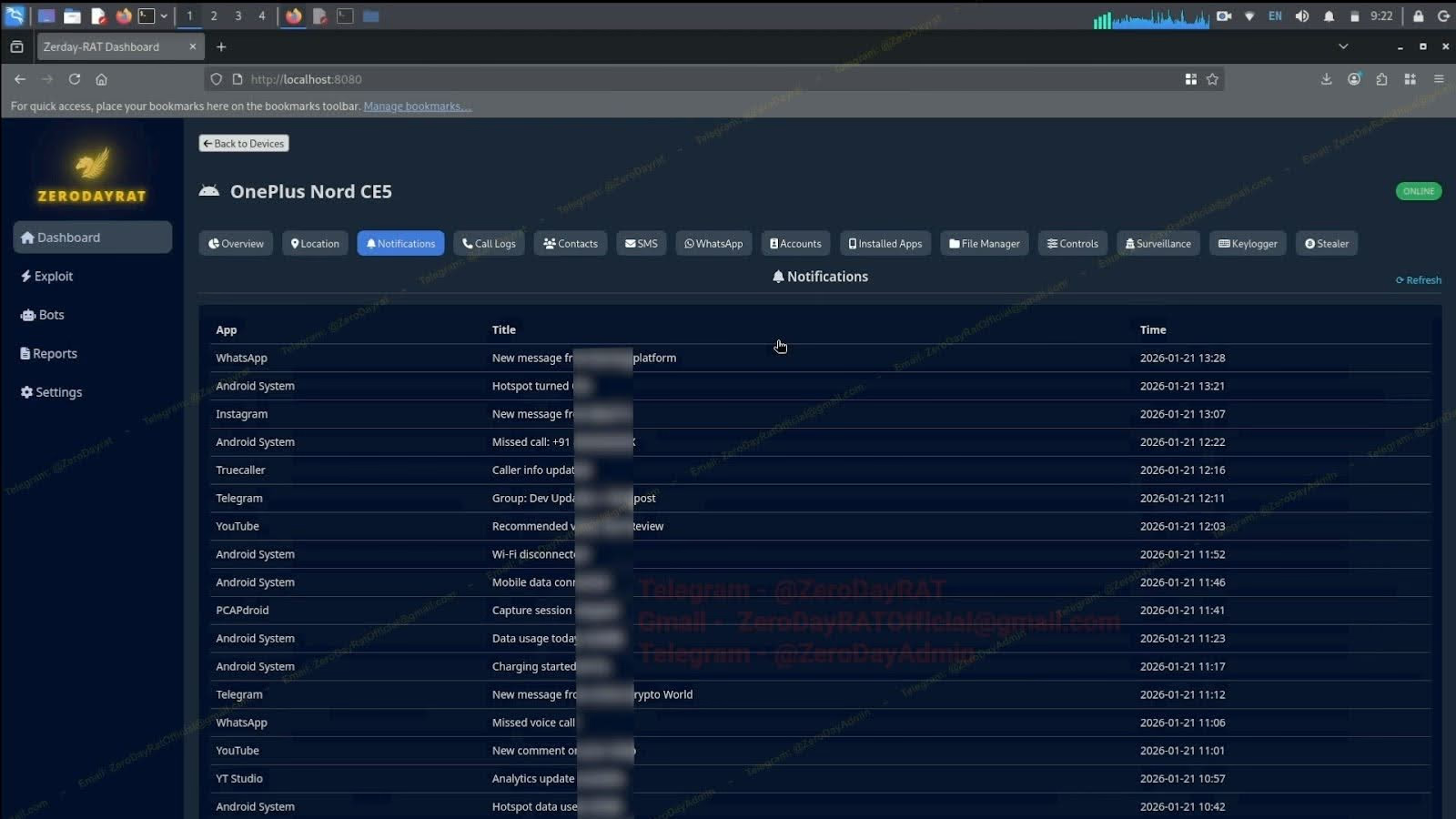
Spyware automatically records:
WhatsApp
Instagram
Telegram
YouTube
Missed call
Message from the bank
System event…
Without needing to open the app, the attacker can still read everything.
2.4. Collect all login accounts
The Accounts tab lists all accounts on the device:
Google, Facebook, Instagram, Amazon, Spotify, Telegram, Paytm, PhonePe, Flipkart…
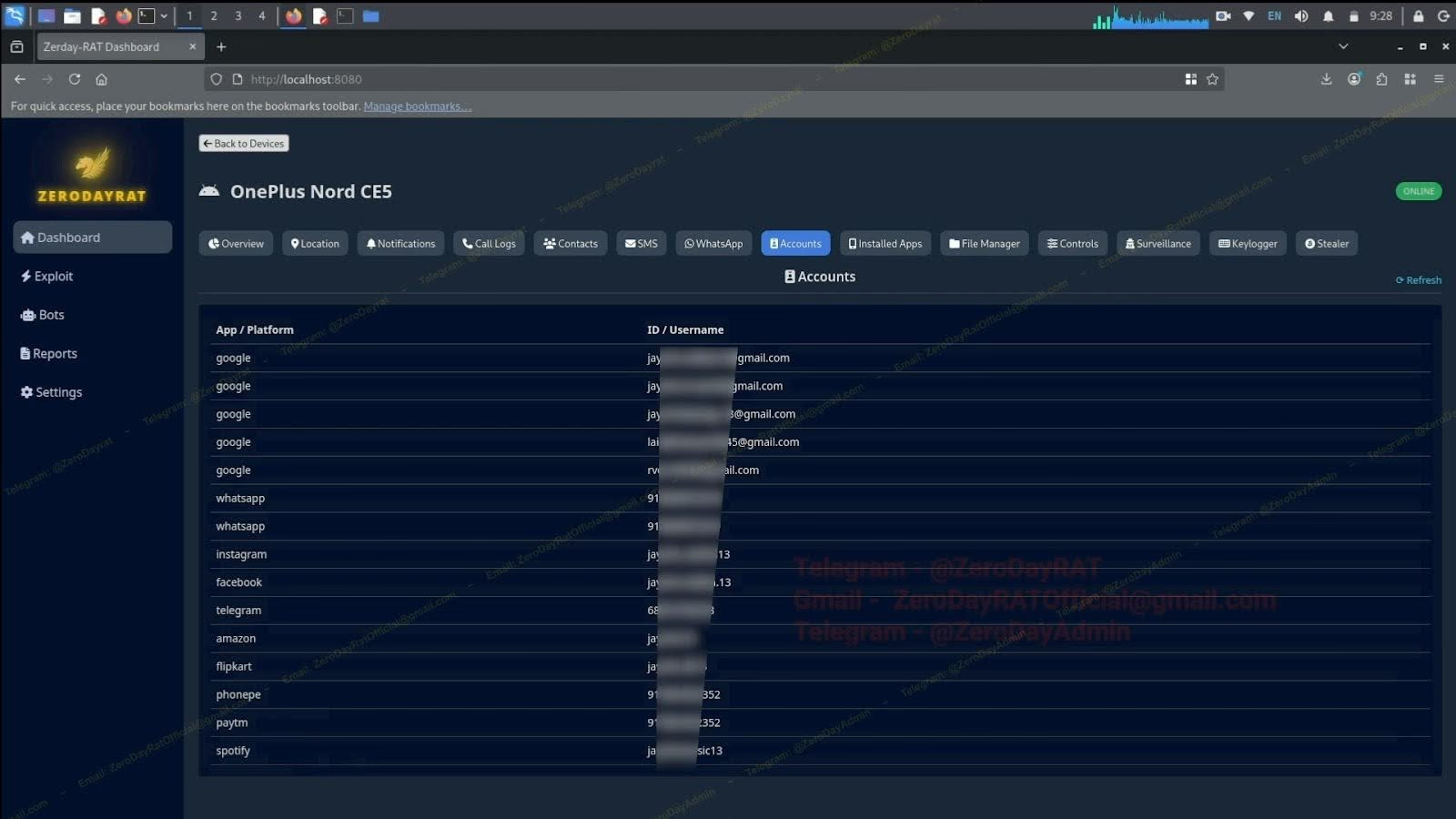
The attacker has enough data to:
Account takeover
Targeted phishing
Financial hijacking
2.5. Read, send, and block OTP codes
ZeroDayRAT:
Read all SMS
Find and collect OTP
Allow sending SMS from the victim's SIM
→ SMS-based 2FA is completely disabled.
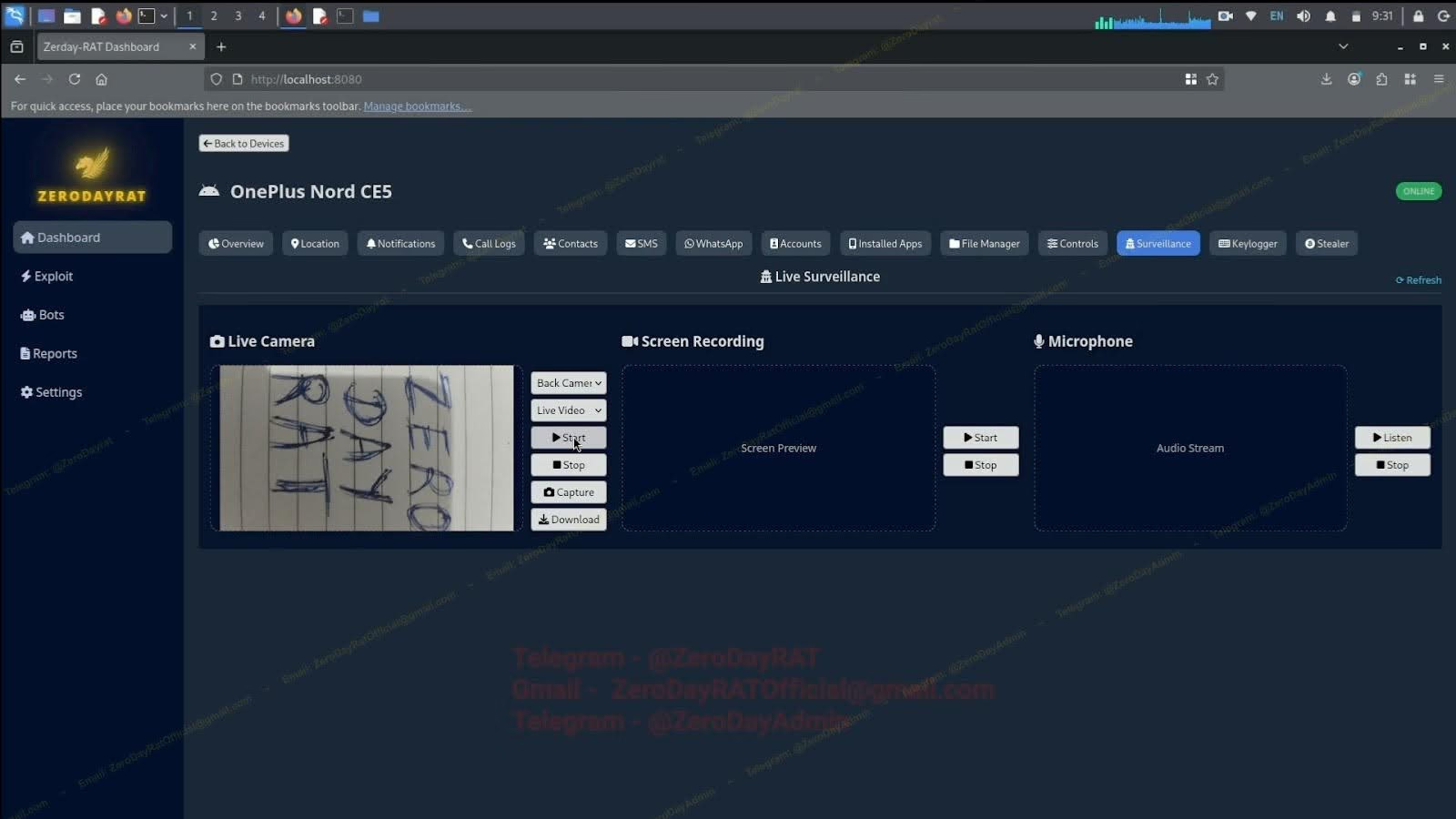
3. Direct spying: Camera – Mic – Screen recording
ZeroDayRAT provides real-time device control capabilities:
Stream front/rear camera
Screen recording
Record microphone audio
View live screen preview
Keylogger with millisecond timestamps
The attacker can watch, listen, and monitor every action of the victim in real time.
4. Financial theft: Banking and Crypto
The ability to commit financial theft becomes the focus of ZeroDayRAT.
4.1. Crypto Stealer
Spyware scans wallets:
MetaMask
Trust Wallet
Binance
Coinbase
It automatically replaces the wallet address in the clipboard to transfer funds to the hacker's wallet.
4.2. Bank Stealer
Attack apps like:
Google Pay
Apple Pay
PayPal
PhonePe
Banking app
Techniques used:
Overlay attack
Collect login information
Block OTP
Remote device control
→ Allow withdrawals, transfers, and bank account takeovers.
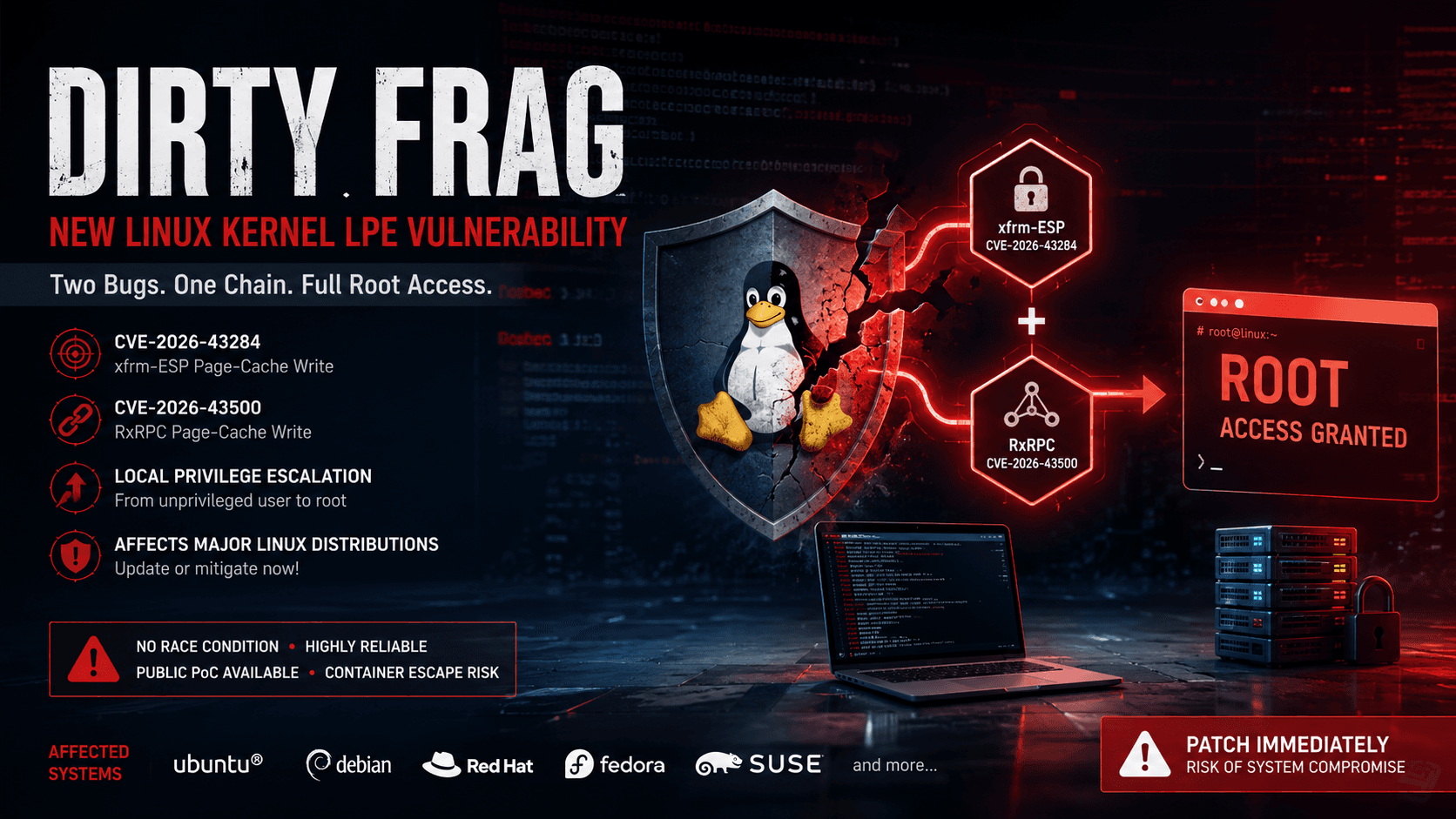
5. ZeroDayRAT in the context of the global wave of mobile malware
The emergence of ZeroDayRAT coincides with a series of other complex malware campaigns, indicating that the mobile environment is being exploited by cybercriminals more than ever. Some notable recent campaigns include:
Exploiting Hugging Face to distribute malicious APKs (RAT TrustBastion) is an app dropper that downloads additional malware from Hugging Face, then requests Accessibility permissions to:
Spyware
Steal login information
Device control
Arsink RAT uses Google Apps Script + Firebase: Distributed via Telegram, Discord, MediaFire, focusing on: Egypt, Indonesia, Iraq, Yemen, Turkey.
Anatsa (TeaBot) hidden in a document reader app on Google Play: Over 50,000 downloads before being removed.
deVixor: banking trojan + ransomware targeting Iranian users, capable of:
Lock device
Demand ransom
Collect data
Use Google Firebase + Telegram bot
ShadowRemit cross-border money transfer scam: Masquerades as a money transfer app on Google Play to bypass legitimate financial systems.
Campaign in India targets government services: Distributed via WhatsApp → takes control of devices and installs miners.
Triada uses fake Chrome update pages: Abuses legitimate ad accounts for malicious redirects.
GhostChat / GhostPairing – Spyware targeting dating victims in Pakistan, in addition to stealing data, the operators also attack:
ClickFix (DLL)
Take over WhatsApp without needing a QR code
Phantom – Click fraud trojan using TensorFlow.js: Automatically clicks ads with ML in a hidden WebView.
NFCShare – NFC card attack: Poses as Deutsche Bank → steals NFC card data.
6. NFC malware explosion – the most dangerous trend today
According to Group-IB, 2024–2025 will see an explosion of NFC relay malware (Ghost Tap).
Three major groups:
TX-NFC (25.000+ subscriber Telegram)
X-NFC (5.000+)
NFU Pay (600+)
Reported damage:
355,000 USD in fraudulent transactions
Mobile wallet hijacked
Mule uses "virtual" cards to withdraw money globally
Attack method:
Trick victims into installing an NFC APK
Ask them to tap their card on the phone
Card data is relayed in real-time to the mule's device
The mule conducts transactions as if they have the actual card
7. Threat level
ZeroDayRAT marks a significant shift from:
"Advanced spyware for nations" → to "Anyone can buy powerful spyware like a nation on Telegram."
Impact:
For individuals
Complete loss of privacy
Monitored 24/7
Risk of identity theft, account loss
Bank and crypto theft
For businesses
Internal information leak
Loss of enterprise application accounts
System intrusion via BYOD
Supply chain attack from compromised accounts
8. Recommendations
For individuals
Do not install apps via links sent through SMS/WhatsApp/Telegram
Disable side-loading of apps
Prioritize using app-based 2FA (Authenticator), avoid SMS
Check for unusual app permissions (Accessibility, Notification, Device Admin)
Install a reliable mobile antivirus/EDR
For businesses
Apply Mobile Threat Defense (MTD) / Mobile EDR
Block side-loading on enterprise devices
Monitor unusual traffic from BYOD devices
Alert when dangerous permissions are detected: Accessibility, Notification Listener
Implement Mobile Zero Trust security policies
Conclusion
ZeroDayRAT is just a part of the increasingly grim picture of mobile security. With spyware powerful enough to control entire devices from the browser, openly sold on Telegram, individuals and businesses are forced to raise their level of vigilance to a new degree.
The mobile ecosystem—central to modern life—is becoming the new "hotspot" for cybercrime.
Reference
Breaking Down ZeroDayRAT - New Spyware Targeting Android and iOS
New ZeroDayRAT Mobile Spyware Enables Real-Time Surveillance and Data Theft