AI-Powered Fake GitHub Repositories Are Fueling the Distribution of SmartLoader and LummaStealer

A new campaign has emerged that exploits fake GitHub repositories to distribute SmartLoader, which is subsequently used to deploy Lumma Stealer and other malicious payloads. This campaign capitalizes on GitHub's trusted reputation to avoid detection, employing AI-generated content to make the fake repositories appear credible.
The campaign exploits GitHub's trusted reputation to evade detection, using AI-generated content to make the fake repositories appear legitimate. The malicious ZIP files contain obfuscated Lua scripts that execute harmful payloads upon extraction.
If successful, the attack allows threat actors to steal sensitive information, including cryptocurrency wallets, two-factor authentication (2FA) extensions, login credentials, and other personally identifiable information (PII), potentially leading to identity theft and financial fraud.
Cybercriminals are evolving from using GitHub attachments to creating entire repositories, combining social engineering tactics with AI-assisted phishing.
Technical Details
Initial Lure
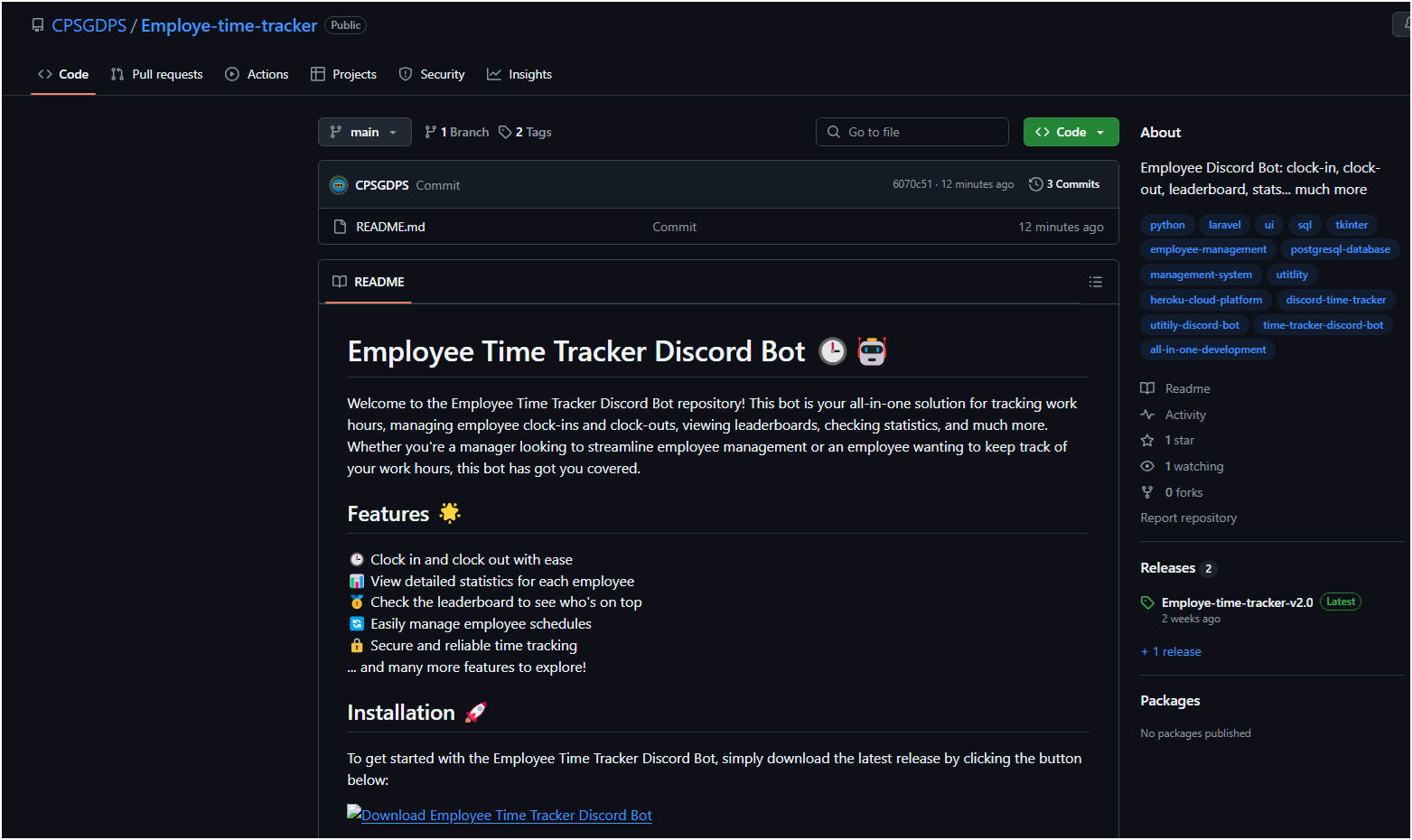
The malware campaign begins with a fake GitHub repository designed to appear legitimate, often mimicking popular tools or software. By exploiting GitHub's trusted reputation, attackers trick users into downloading malicious files. The malicious actors use AI to create convincing README files and documentation, making these repositories seem professional and authentic—thus increasing the likelihood that users will trust and install the harmful content.
The fake repositories stand out due to their README content format, which appears heavily AI-assisted, as evidenced by clear signs like excessive use of emojis, unnatural phrasing, linked logos, and structured content. The repository contains only a README file, and all hyperlinks redirect to malicious files strategically hidden in the release section, making them less noticeable to unsuspecting users.
The main goal of these repositories is to trick users into unintentionally downloading ZIP files containing the SmartLoader payload. Once extracted, the ZIP file contains four components:
lua51.dll: LUAJIT runtime interpreter
luajit.exe: Lua loader executable file
userdata.txt: a malicious Lua script
Launcher.bat: a batch file used to execute luajit.exe with "userdata.txt" passed as an argument
While the executable files and DLL are not harmful, the batch file is specifically designed to launch luajit.exe, which in turn executes the Lua script hidden in userdata.txt. This script acts as the actual malicious payload, responsible for compromising the victim's system.
From SmartLoader to Lumma Stealer

During normal execution, the loader delivers the LummaStealer malware as the final payload. It retrieves a file from GitHub, saves it as search.exe, and then executes LummaStealer. This executable removes necessary files and runs an AutoIt script encoded within Excel files.
SmartLoader can inflate files when loading the payload, increasing the file size to about 1GB.
After retrieving and executing the downloaded files, it initiates a series of commands to create and execute additional files, setting the stage for the LummaStealer payload. It performs malicious actions such as creating harmful files in the %TEMP% directory, appending to a batch script, and executing it.
textcmd /c copy /bc..\Entertaining.xls + ..\Divide.xls + ..\Providence.xls + ..\Shakespeare.xls + ..\Adolescent.xls + ..\Divided.xls + ..\Unnecessary.xls + ..\Karma.xls
It will also execute several commands to explore security software using findstr, such as:
textfindstr /I "opssvc wrsa"
findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth"
From the batch script, it will create another file named “Research.com” in the %TEMP% directory, which is a misnamed AutoIT interpreter. Finally, it will debug the browser with this command before reaching its C&C server:
text"C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory="Default" --remote-debugging-port=9222
Finally, LummaStealer reaches its C&C server at pasteflawwed[.]world. This communication channel is used to filter logs and other sensitive information collected from the infected system.
Cybercriminals can use malware distributed via GitHub to carry out highly destructive attacks, especially when combined with advanced threats like Lumma Stealer, which can gather information from web browsers, compromise cryptocurrency wallets and 2FA extensions, and steal sensitive data such as login credentials, financial information, and other PII. This can leave victims vulnerable to identity theft, financial fraud, and unauthorized access to critical accounts, leading to severe financial and personal consequences. Furthermore, the attackers can further exploit this stolen data by selling it to other cybercriminals for profit, increasing the risk to the victims.
Risk Mitigation
To protect against threats like SmartLoader and similar malware campaigns, individuals and organizations should consider the following best practices:
Only download software from official sources: Avoid third-party websites, torrents, and repositories offering free or cracked software.
Verify the authenticity of repositories: Check for legitimate contributors, repository history, and signs of AI-generated or suspicious documentation.
Enable security features: Use endpoint security solutions that can detect and block malicious downloads.
Analyze files before execution: Use sandboxing tools to scan unknown files before running them.
Implement network security controls: Block known malicious GitHub repositories and restrict file downloads from unverified sources.
Monitor for unusual activity: Use security information and event management tools to detect unauthorized script executions and unusual outbound connections.
Educate employees about social engineering risks: Conduct security awareness training to prevent employees from falling for fake repositories.
Enforce application control policies: Implement measures to prevent the execution of unauthorized applications and scripts.
Conclusion
The ongoing campaign utilizing fake GitHub repositories to distribute SmartLoader and Lumma Stealer underscores the evolving strategies of cybercriminals. By leveraging GitHub's trusted reputation, attackers employ social engineering techniques and AI-generated content to entice victims into downloading malicious files. The transition from traditional GitHub attachments to complete repositories illustrates their adaptability in evading detection and sustaining operational resilience.
As cyber threats continue to advance, it is crucial for organizations and individual users to remain vigilant against these deceptive tactics. This campaign highlights the importance of verifying software sources, particularly when engaging with open-source platforms.