CVE-2025-0927: serious memory overflow in Linux Kernel causes system collapse and remote code execution
Overview
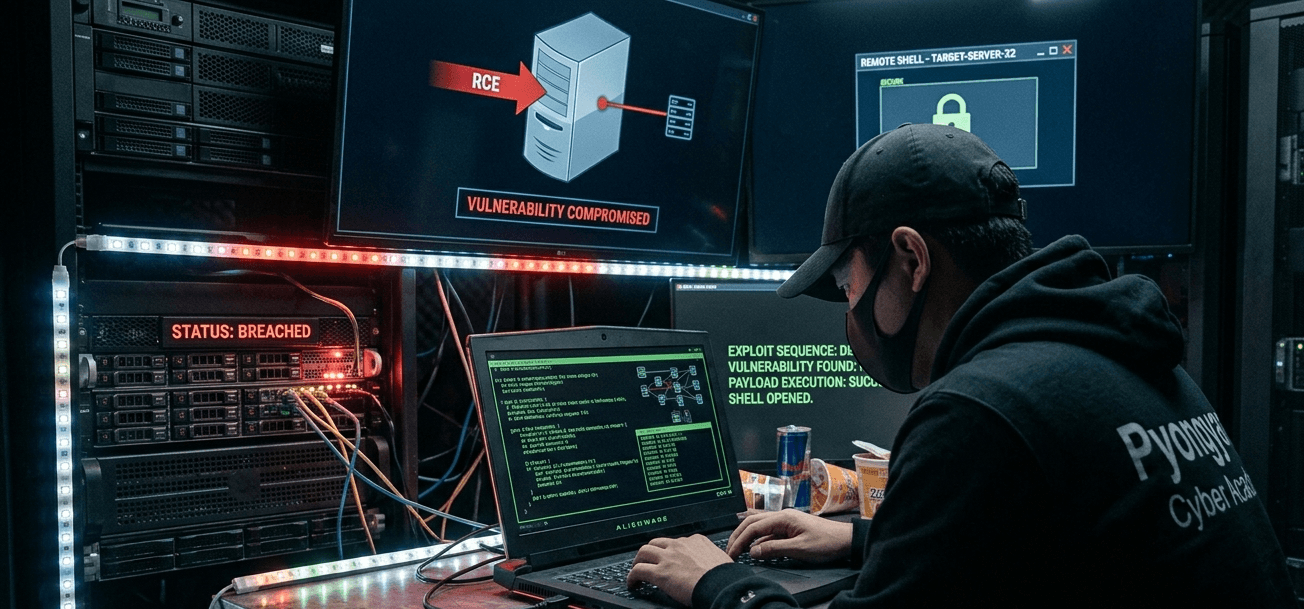
Recently, a serious vulnerability was discovered in the Linux Kernel, particularly affecting Ubuntu 22.04 users. The vulnerability, identified as CVE-2025-0927, is known for causing a heap overflow in the HFS+ file system driver of the Linux Kernel. This vulnerability allows an attacker to use a specially crafted file system image, which, when mounted, can lead to a denial of service (system crash) or even arbitrary code execution.
Details of the vulnerability
Vulnerability ID: CVE-2025-0927.
CVSS Score: 8.8/10 indicating a high severity level.
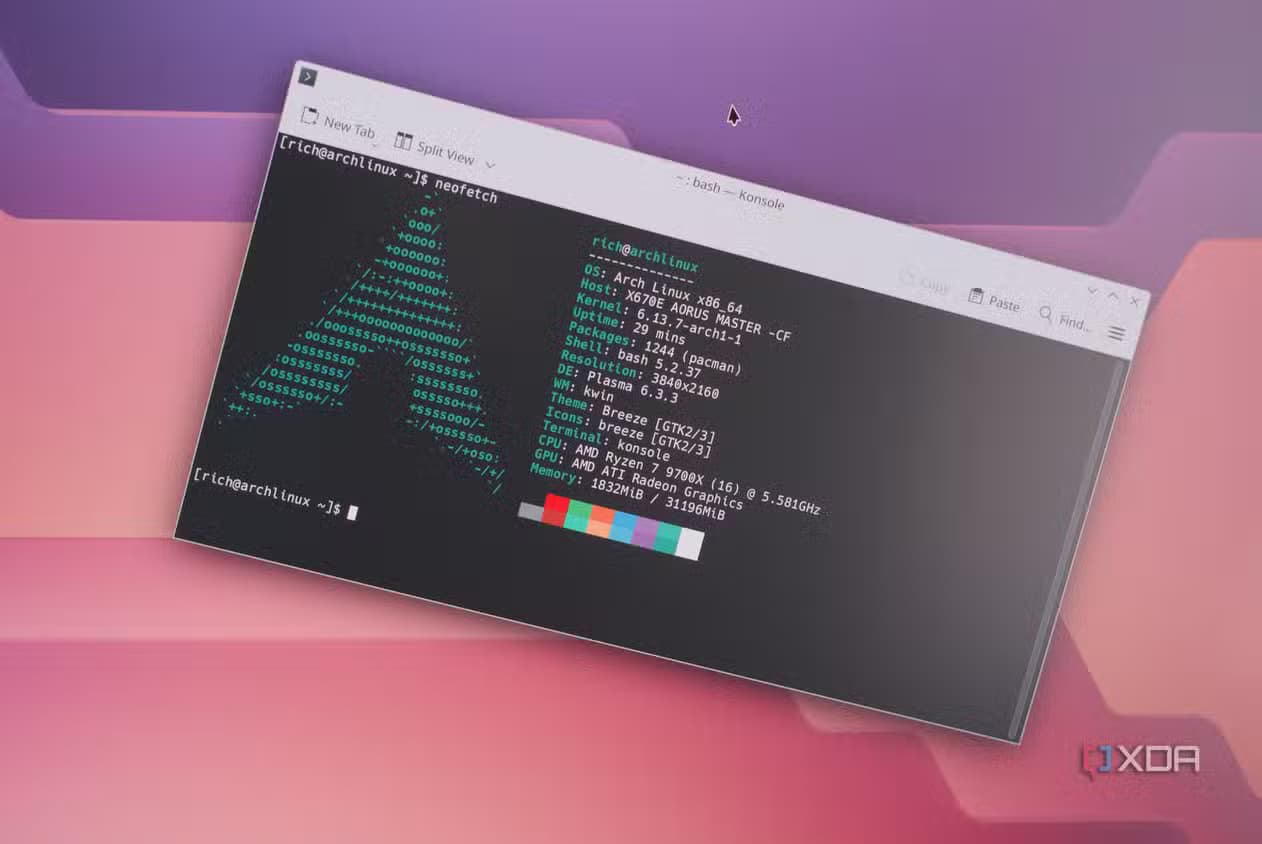
Affected Range: Linux Kernel versions from 2.6.12-rc2 to 6.12.0. Specifically, Ubuntu 22.04 with Linux Kernel 6.5.0-18-generic has been confirmed to be vulnerable.
Attack Mechanism: The vulnerability exists in the handling of B-tree nodes of the HFS+ file system. Specifically, the lack of key length checks in the
hfs_bnode_read_keyfunction leads to a heap overflow.Consequences:
System crash or hang.
Root access and execution of malicious code.
Data leakage or complete loss of control over the system.
Exploitation Method
Where is the vulnerability located?
The main vulnerability is in the data reading line where
key_lenis not checked for limits, especially whenkey_lencomes fromhfs_bnode_read_u16()—meaning it comes from the content of the HFS+ file image controlled by the attacker.Here, the attacker will create a fake HFS+ image with a valid format but containing specially designed extent records to exceed the legitimate buffer size.

- In the Linux Kernel, there is a function
hfs_brec_keylen()used to determine key length, which includes limit checks. However, attackers can exploit this function to copy large data, causing a heap overflow.

Create a fake HFS+ image
- Attackers will use the HFS+ file system creation tool (from the
hfsprogspackage)
- Attackers will use the HFS+ file system creation tool (from the


Mount image on the target machine
After creating a malicious HFS+ image, the attacker will use the following command to mount it on the victim's machine:
sudo mount -t hfsplus exploit.img /mnt/hfsOr exploit the automount system (by attaching it to a USB or introducing it into the CI environment)
Trigger error
- When the Kernel reads a node leading to an unusually large
key_len, the hacker will copy it into the heap, causing an overflow.
- When the Kernel reads a node leading to an unusually large

If the memory layout is predictable, the attacker can:
Overwrite pointers, functions, and execute kernel code
Cause a denial of service (DoS) through a crash
Detailed Impact
When mounting an HFS+ image with malicious data, the kernel can crash (panic), causing the system to freeze.
If the attacker controls the heap layout (through heap spraying or environment normalization), it can lead to code execution in the kernel.
If a container is granted permission to mount a loop or HFS+ image, the attacker can escape the container.
A CI system running tests with a
.imgimage can experience a complete crash or be exploited with malicious kernel code.On Linux desktops like Ubuntu, Fedora, etc., users only need to double-click on a malicious HFS+
.imgto trigger the exploit.
Recommendation
Update the Kernel as soon as possible
sudo apt update
sudo apt upgrade
sudo reboot
Disable HFS+ file system support if not needed
Temporarily (until reboot)
- sudo modprobe -r hfsplus
Permanently (do not load the module at boot)
Add the following line to
/etc/modprobe.d/blacklist.conf:blacklist hfsplus
Block mounting of HFS+ file systems by unprivileged users
Disable auto-mounting of HFS+ devices on desktop or server systems.
Do not grant
mountpermissions to users outside of root or admin groups.
Check the system for suspicious HFS+ images
Monitor and log security
Conclusion
CVE-2025-0927 is a critical vulnerability because it affects the kernel layer, is easy to exploit, and exists in a feature that is rarely monitored—the HFS+ file system. On Ubuntu, both Desktop and Server versions have default polkit rules that allow users with a local session to create loop devices and mount various block file systems. This bypasses the CAP_SYS_ADMIN restriction, allowing regular users to exploit the vulnerability.