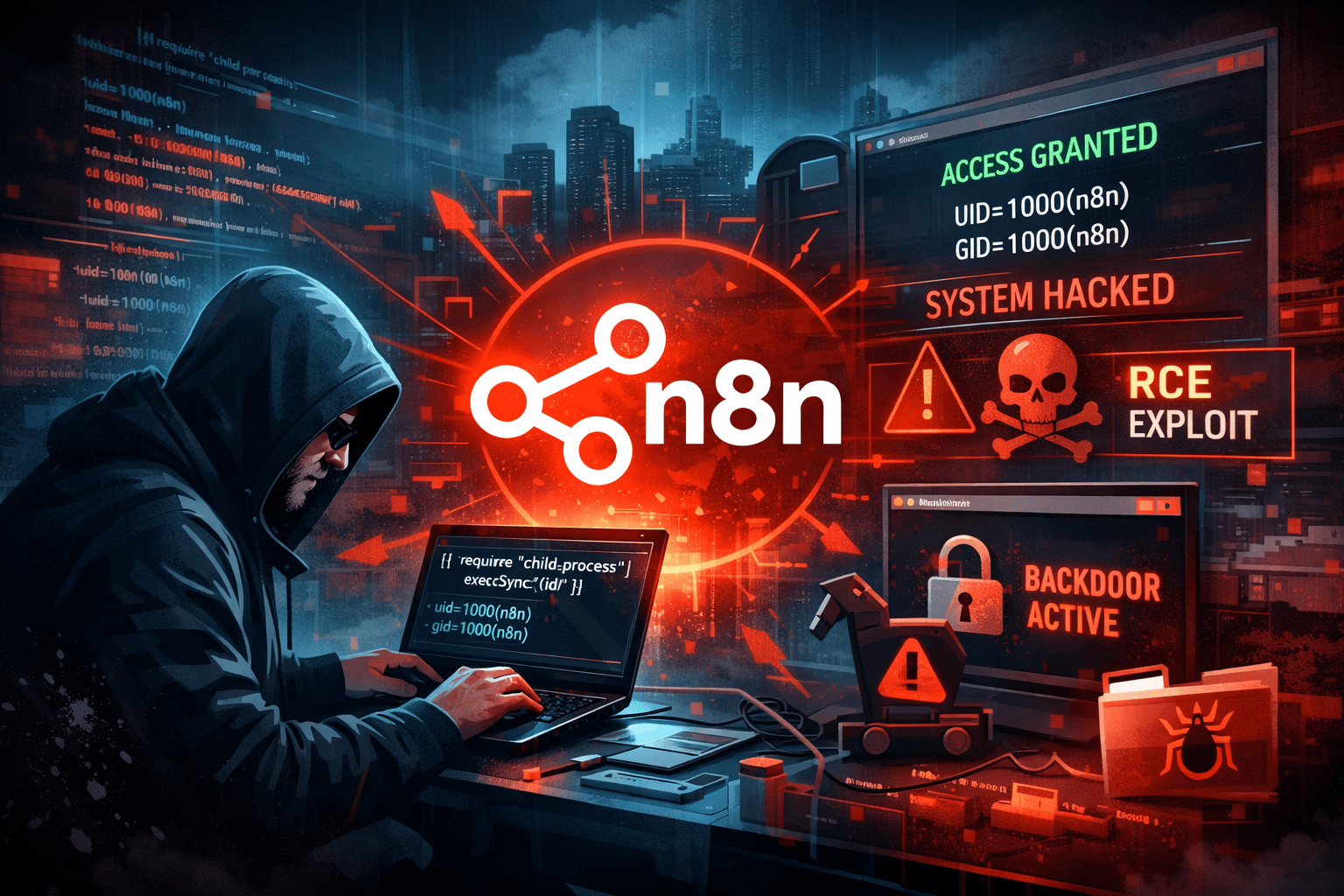
No login required, no clicks needed: n8n vulnerability allows hackers to take over the server in an instant
Overview The Pillar research team discovered an extremely critical vulnerability in n8n that allows: Remote Code Execution (RCE) No login required (unauthenticated) No user interaction needed (zero