FlowerStorm: A tool for phishing Microsoft365 accounts replacing Rockstar2FA
Just a SOC Analyst ^^
After Rockstar2FA - a tool previously used to steal Microsoft accounts - disappeared from the cybersecurity landscape, a new tool named FlowerStorm has developed remarkably with signs similar to the previous Rockstar2FA tool.
What is the Rockstar2FA tool?
Rockstar 2FA, a Phishing-as-a-Service (PhaaS) platform, supports Adversary-in-the-Middle (AiTM) attacks to steal Microsoft 365 credentials. This tool allows attackers to bypass multi-factor authentication (MFA) protection by intercepting valid session cookies. Victims are lured to a fake login page where their credentials are collected and forwarded to Microsoft to obtain the session cookie. This cookie is then used to directly access the target account, bypassing MFA.
According to Trustwave, Rockstar 2FA is an upgraded version of the DadSec and Phoenix phishing kits from 2023 and became popular in the cybercrime community from August 2024. Priced at $200 for two weeks or $180 to renew the API, this platform offers powerful features such as support for Microsoft 365, Hotmail, Godaddy, and SSO. It also has the ability to generate random source code to avoid detection, integrate Cloudflare Turnstile Captcha, and provide an admin interface with real-time tracking and backup features.
Since May 2024, Rockstar 2FA has set up over 5,000 phishing domains to support large-scale phishing campaigns. Phishing emails often use content such as document sharing notifications, IT alerts, password reset requests, or payroll notifications, combined with QR codes, link shortening services, and PDF files to bypass security filters.
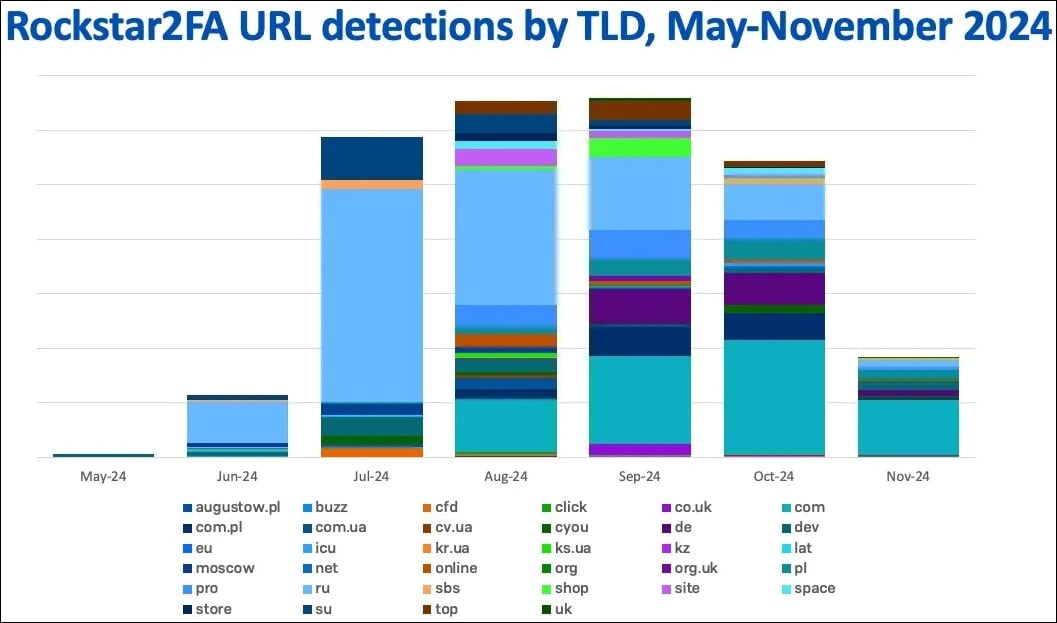
Figure 1. Number of TLDs related to Rockstar2FA
FlowerStorm, the replacement service for Rockstar2FA?
According to Sophos researchers, Rockstar2FA experienced a partial infrastructure failure on November 11, 2024, rendering many of the service's pages inaccessible. Sophos stated that this did not appear to be intentional but was due to a technical error. A few weeks later, FlowerStorm, a service with many similar functions, quickly gained attention.
Sophos identified several similarities between Rockstar2FA and FlowerStorm, suggesting they may have a common origin due to similarities in their operation:
Both tools use phishing websites that mimic legitimate login pages to collect credentials and MFA tokens. They also use backend servers hosted on domains like .ru and .com.
The HTML structure of these phishing pages is very similar, featuring random text generation in the comment section, Cloudflare Turnstile Captcha, and prompts like "Initializing browser security protocols." The difference is that Rockstar2FA uses an automotive theme on the phishing site, while FlowerStorm uses a plant theme, but they are essentially the same in design.
These tools also collect similar credentials, such as email, password, and session tracking tokens. They have tools to authenticate mail and MFA after stealing the victim's information.
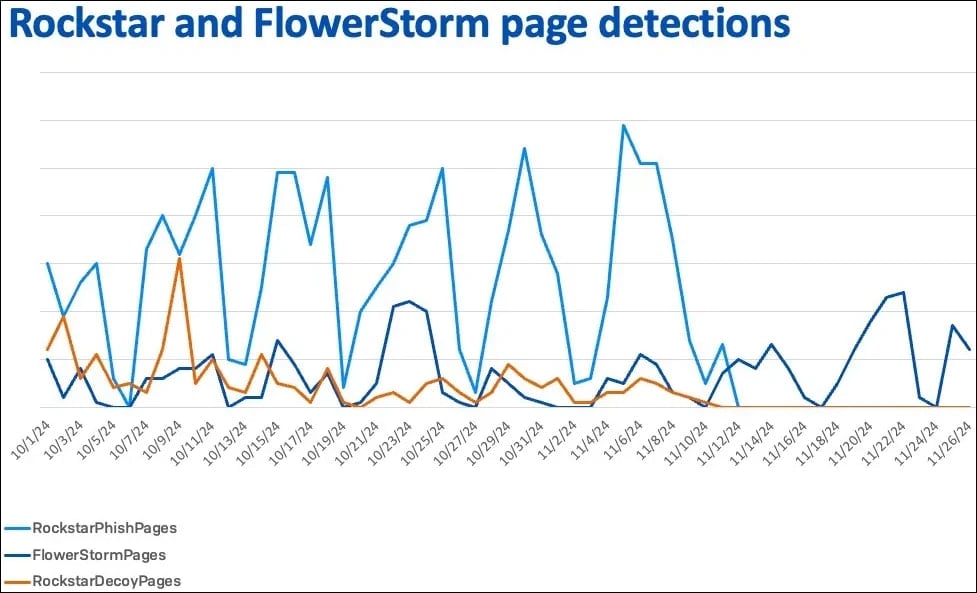
Figure 2. Similarity in the number of phishing websites of these two tools
Impact Level
Data from Sophos shows that about 63% of organizations and 84% of users targeted by FlowerStorm are based in the U.S.
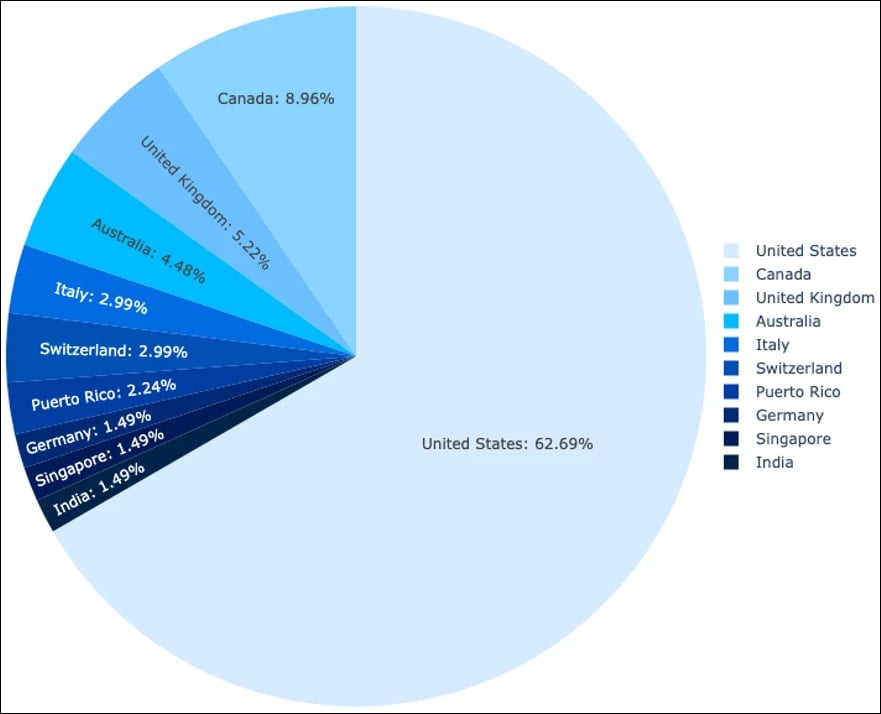
Figure 3. Target countries of FlowerStorm.
The data also shows that the service sector is the most targeted by this campaign (33%), followed by manufacturing (21%), retail (12%), and financial services (8%).
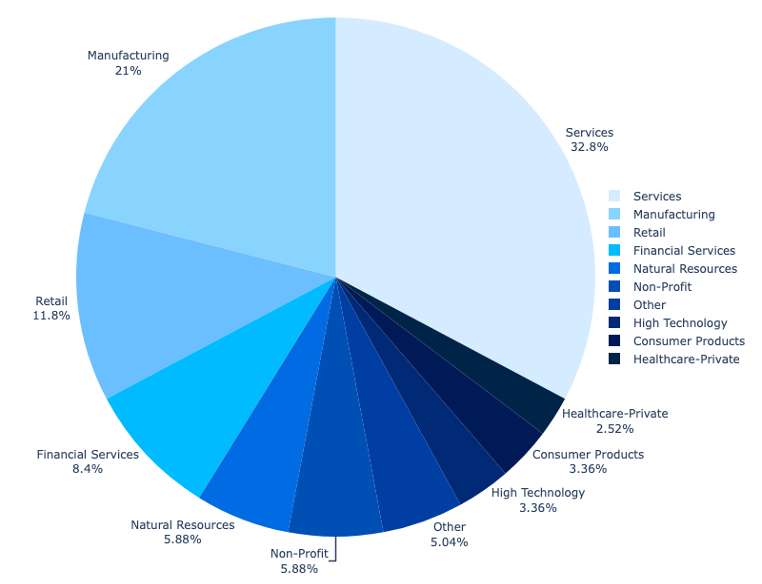
Figure 4. Sectors targeted by FlowerStorm.
Recommendations
FPT Threat Intelligence recommends organizations and individuals take several measures to prevent this campaign:
Use multi-factor authentication (MFA): To protect against phishing attacks, use MFA with FIDO2 tokens against AiTM.
Implement email filtering solutions: Enhance the deployment of email filtering solutions to block malicious emails and detect unusual activities.
Use DNS filtering: Use DNS filtering to block access to suspicious domains like .ru, .moscow, and .dev.