HOT: A Technology Corporation in Vietnam Hit by Ransomware Attack

Just a SOC Analyst ^^
According to the latest cybersecurity news gathered by FPT Threat Intelligence, CMC Corporation — a technology corporation in Vietnam — has fallen victim to a ransomware attack carried out by the crypto24 group. This data breach, discovered on 2025-04-12 08:52:39, raises alarms about the increasing danger of targeted cyberattacks (APT) aimed at critical organizations in Vietnam.

Figure 1. Ransomware incident report summary (via HookPhish)
Information about the Crypto24 Group
Currently, there is very little information and technical analysis about this malware and APT group. Below are some notable details gathered by FPT Threat Intelligence:
Type of Malware
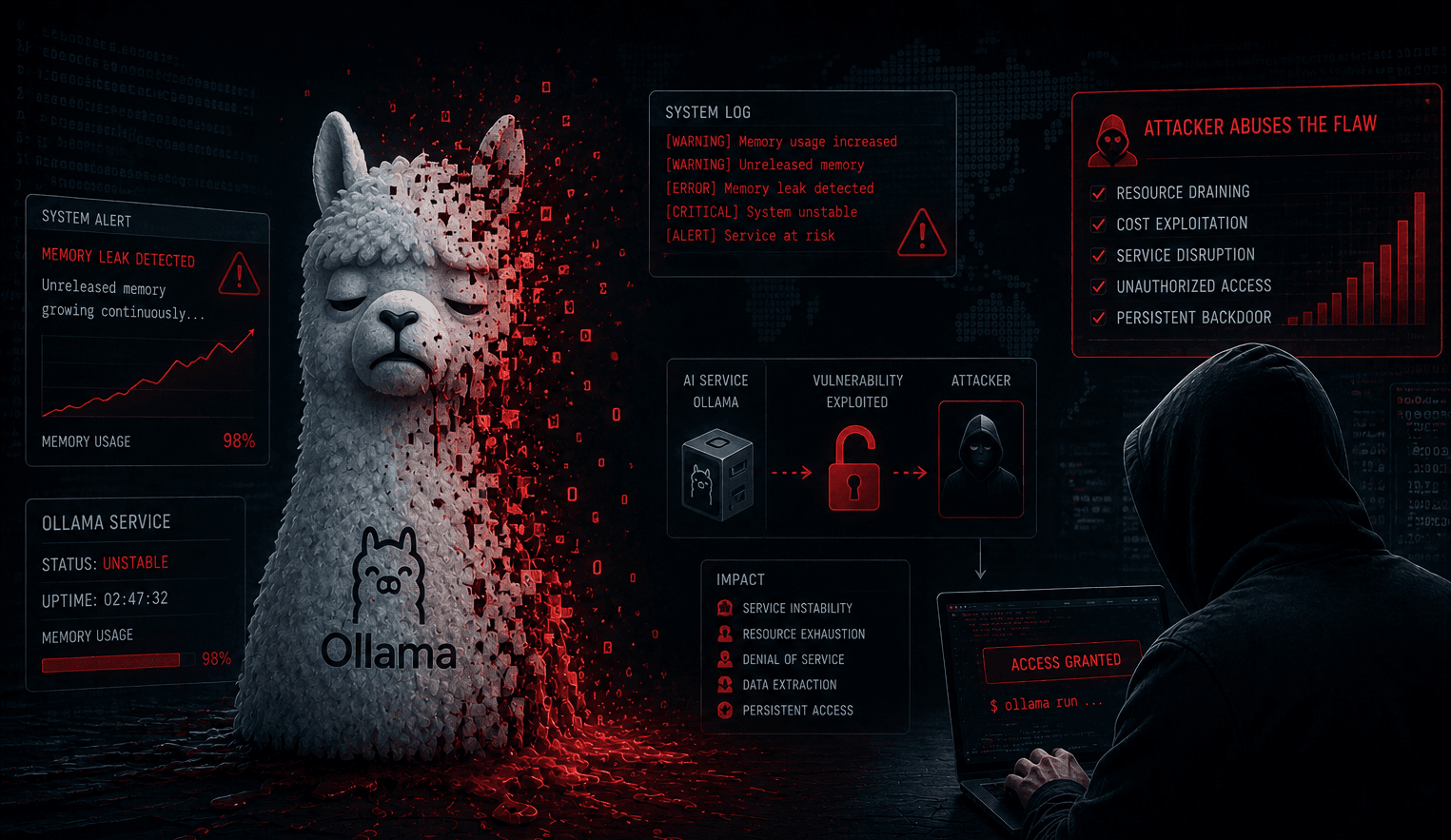
Crypto24 is a type of ransomware, specializing in encrypting victims' data and demanding a ransom for recovery. After infection, Crypto24 encrypts all files and appends the “.crypto24” extension to the file names.
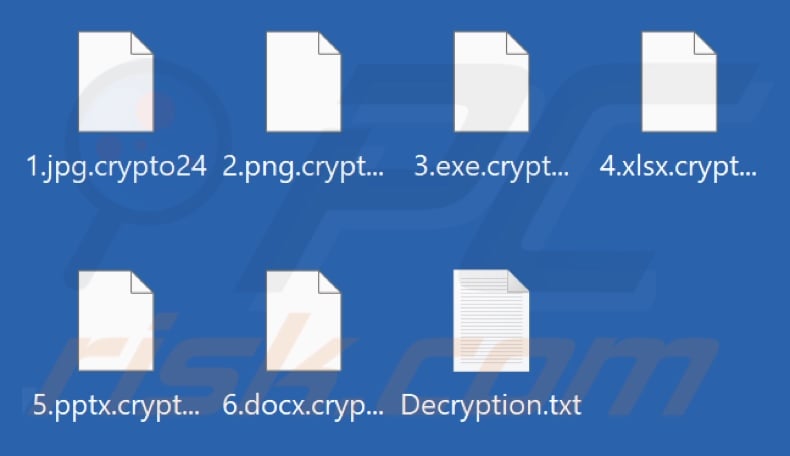
Figure 2. Files encrypted by Crypto24 ransomware
Simultaneously, the malware creates a ransom note file named Decryption.txt:
Users are informed that their data has been encrypted and stolen.
To retrieve the data, victims must purchase a “decryption key” from the attacking group.
The attackers warn that:
Renaming or modifying locked files may render them unrecoverable.
If the ransom is not paid, the data will be publicly leaked on leak sites like .onion controlled by the group.
IOCs
According to data collected from sources monitoring leak sites on the Dark Web, the crypto24 ransomware group has operated a .onion site titled Public Data Storage. This site was last accessed at 02:31 AM on 15/04/2025 and is currently inactive. It may have been used to store or publish stolen data from victims as part of a ransom pressure strategy.

Figure 3. Information about Crypto24 ransomware IOCs
Victims of the Crypto24 Group
The first victims of the Crypto24 ransomware group were discovered on 08/04/2025, and the attacks indicate that the group is intensifying its malicious campaign globally, targeting organizations in various sectors: technology, finance, legal services, and enterprise data. Below is a list of 07 organizations confirmed as victims of this group (updated as of 15/04/2025):
CMC Corporation (Vietnam)
Date Discovered: 12/04/2025
Impact Level: 2 TB of data stolen from MariaDB, MongoDB, RARS-DB,... at the data center
ModulusGroup, Ludi-SFM (Indonesia)
- Casino customer data, ERP databases, system project source code.
Taxplan (Canada)
- Documents and databases related to tax and tax management software.
Mochtar Karuwin Komar (Indonesia) – Law Office
- Legal records, financial information, contracts, client consultation data.
Technoforte Software Pvt Ltd (India)
- Main project source code for Palms (including mobile version).
International Business Service (India)
- ID card images, personnel data, payment records of about 3,000 employees.
Iris Neofinanciera (Colombia)
- Entire Google Drive files, chat data, 5-year personnel documents, SQL databases, and customer personal information.

Figure 4. Countries with victims of this malware (according to Ransomware.live)
Recommendations
FPT Threat Intelligence recommends organizations and individuals take several measures to prevent this particularly dangerous attack campaign:
Network Monitoring and Intrusion Detection: Deploy network monitoring systems (NIDS/NDR) to detect anomalies, unusual encrypted traffic, and suspicious behaviors related to ransomware.
Secure Data Backup: Ensure offline backups are available to recover data in case of encryption.
System Updates: Always update the latest security patches to protect systems from exploitable vulnerabilities.
Access Management: Limit user access rights, apply network segmentation to prevent lateral movement by attackers.
Account Security: Use strong, unique passwords and enable multi-factor authentication (MFA) to protect login information.
Data Encryption: Implement encryption for sensitive data to protect against theft or leakage.
Reduce Attack Surface: Disable unnecessary functions to reduce the risk of exploitation.
Enhance Security Awareness: Train employees on security risks and attack methods commonly used by cybercriminals.
Monitor Dark Web and Leak Sites: Use threat intelligence services to detect early information leaks about the organization on .onion sites or hacker forums.
Regularly Check System Logs: Analyze access logs, authentication logs, and unusual behaviors on servers to detect early privilege escalation or lateral movement in the network.
Conduct Regular Penetration Testing: Perform regular penetration testing (Pentest) to identify and fix vulnerabilities that ransomware could exploit.
Incident Response Plan (IR Plan): Develop and rehearse scenarios for responding to ransomware attacks, ensuring relevant teams know how to isolate, recover, and report incidents promptly.