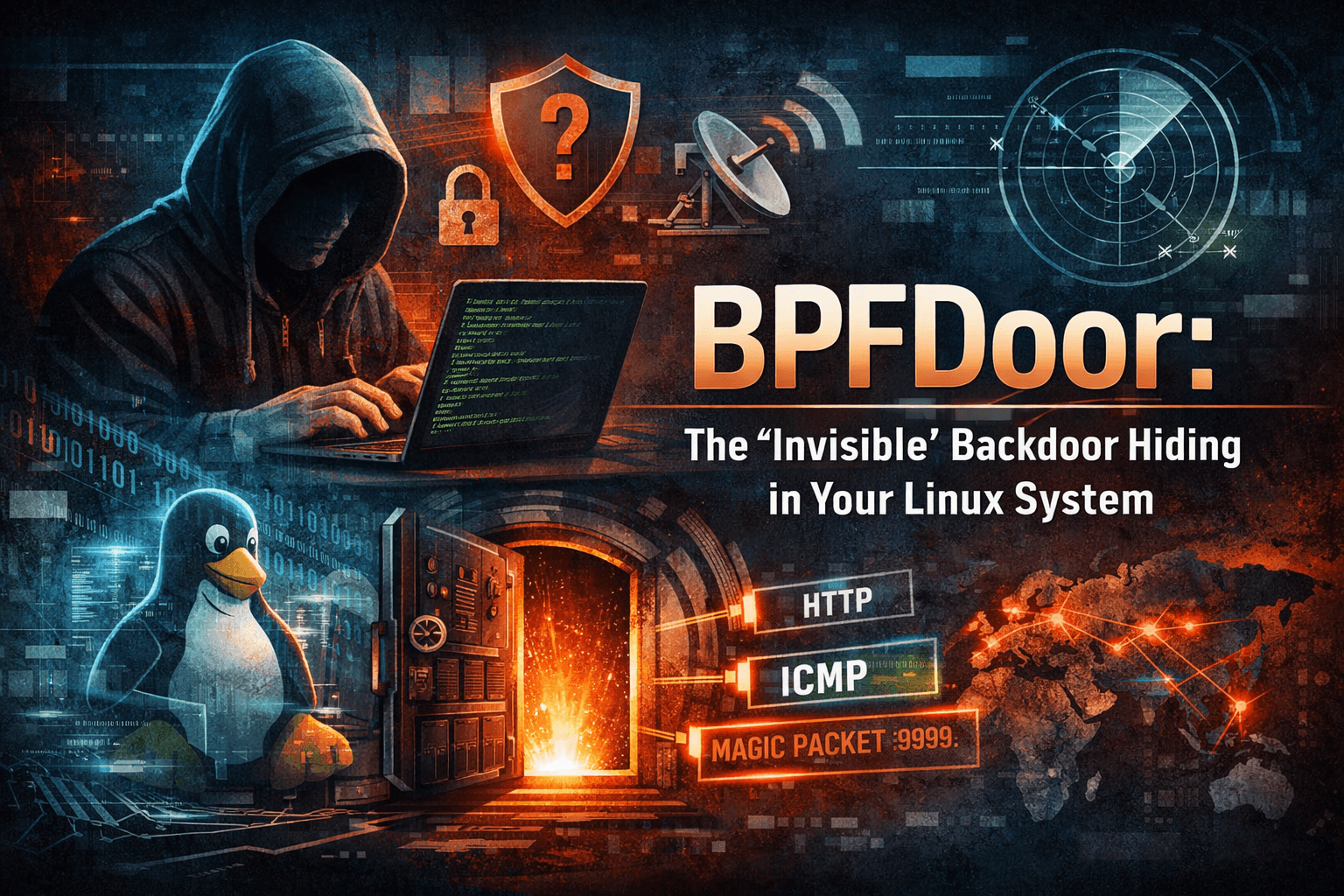
Invisible malware in the Linux kernel: Are you sure your system is clean?
Overview
In the modern world of cybersecurity, most defense mechanisms are built on a familiar assumption: every threat will leave a trace — a suspicious connection, an open port, or at least an unusual behavior in the system. The APT Red Menshen group is covertly deploying seven entirely new BPFDoor variants to manipulate the core infrastructure of telecommunications providers. Based on an analysis of nearly 300 of the latest malware samples from Rapid7, this campaign has bypassed traditional EDR defenses by using Berkeley Packet Filters (BPFs) at the Kernel level, creating an invisible "trapdoor" architecture that activates only with a magic packet through stateless protocols.
Red Menshen - the APT group behind BPFDoor

Introduction
Red Menshen is a sophisticated cyber attack group (APT – Advanced Persistent Threat) known for using the BPFDoor backdoor in espionage campaigns spanning several years, specifically targeting telecommunications infrastructure and critical systems. Unlike many other noisy APT groups, Red Menshen operates with the philosophy: "Stay invisible, stay persistent." Simply put, this means causing no destruction, creating no noise, and quietly maintaining access over a long period.
Scope of operations
Red Menshen is noted for operating globally, with primary targets including telecom providers, internet infrastructure, enterprise Linux servers, and core network systems. The reason the hackers target telecom is simply to access call metadata, monitor user traffic, and serve strategic espionage goals.
Prominent attack techniques
Implant into router firmware Use custom backdoor Living-off-the-land Supply chain attack (possible)
Detailed techniques

How has BPFDoor "evolved"?
Initially, BPFDoor was a fairly simple rootkit temporarily running in the /dev/shm directory, leaving no files on the disk and erasing traces after operation. This made it hard to detect, but its main weakness was that modern security systems could identify "strange" processes running from memory. After some upgrades, new variants changed their strategy: storing the malware directly on disk, masquerading as system processes (e.g., server management daemons) to make it appear legitimate and less suspicious. Simply put: shifting from "temporary concealment" to "long-term concealment and self-legitimization."
Command and Control (C2) architecture
The Red Menshen group uses two main methods to control BPFDoor: httpShell, which hides in web traffic, and icmpShell, which hides in ping (ICMP).

httpShell – Hidden in HTTP traffic
BPFDoor will monitor all network traffic, not at the application level but deep in the kernel. This means it sees packets before the firewall or antivirus.
In reality, the Internet has multiple layers (tunnels) such as GRE or GTP (in telecommunications networks). httpShell can "unwrap" these layers directly in the kernel to see the data inside. It's like opening an envelope, then opening another envelope inside, until the real content is revealed.
httpShell has another ability to evade firewalls and WAFs. Normally, firewalls/WAFs check the data position in a packet. BPFDoor uses a clever trick by adding padding (fake data) and forcing the identifier "9999" to always be at the 26th byte. As a result, even if the packet is altered by a proxy, the malware still finds the correct "signal" to exploit.
icmpShell – Control via ping

This variant, instead of using HTTP, will use ICMP (ping) to communicate and create a two-way control shell, which is often extremely dangerous because ICMP is usually not blocked.

This dangerous variant also uses the "PID mutation" technique. This means each time the malware runs, it has a different PID (Process ID). BPFDoor exploits this by attaching logic to the PID, causing its "signature" to change with each run. As a result, the firewall cannot write a fixed rule to block it.
Another point is the extremely clever way this variant operates. Typically, malware requires a fixed C2 server (IP/domain), but BPFDoor does not. When an attacker sends a packet, the malware doesn't need to know the IP in advance; instead, it just reads the source IP of the packet and then makes a reverse connection. Simply put, the attacker can control it from anywhere without needing a fixed infrastructure.
In cases where the malware cannot connect, it turns the infected machine into a relay, sending ICMP to another machine on the internal network. This is even more dangerous as it allows the variant to penetrate deeper into the system like a secret router.
What makes BPFDoor dangerous?
Operates in the kernel, almost "invisible" to antivirus. No need for a fixed C2, making it impossible to block by IP/domain. Uses a legitimate protocol, but inside is a secret control channel.
HTTP → normal
ICMP → normal
NTP → normal
Constant changes with a non-fixed signature make it very difficult to detect using rules.
Expert assessment & conclusion
The logical shift of the BPF filter from initializing SOCK_RAW sockets to SOCK_DGRAM provides a clear view of Red Menshen's objectives. The group is actively streamlining the process of dissecting virtual packets, leaving the task of unraveling complex telecommunications layers (like IPsec and GRE node setups) to the target server's kernel. Typically, telecommunications control servers maintain a heavy multi-layered network array; this adjustment allows BPFDoor to eliminate bulky decoding libraries, reducing the infection footprint and the risk of crashing the core processes of the national network system.
Additionally, the malware's precise identification of the disguise process in the format of HPE Insight Management (cmathreshd) with the specific command -p 5 -s OK for deployment into the Bare-Metal hardware of HPE ProLiant demonstrates that this APT campaign has a deep understanding of the infrastructure architecture that the victim—especially the 4G/5G core clusters of Ericsson—is operating.
The variant's direct trace of hidden system files into the directory /var/run/user/0 instead of using the chmod script allows the attacker to avoid modifying execution permissions recorded in the auditd log file. This is a highly sophisticated technique that undermines the logic of detecting malicious files in current host-monitoring EDR platforms in Vietnam.
Recommendation
Immediate (0-24h)
Conduct a network infrastructure scan for ICMP packet connections with Sequence Number = 1234 and an invalid ICMP Code 1. These are beaconing heartbeats revealing the variant's blind spot.
Check the process list on Linux servers, focusing on direct execution of root mask processes like zabbix_agentd, dockerd, or cmathreshd without practical mapping to /bin or software installation directories. Administrators are encouraged to immediately run the script rapid7_bpfdoor_check.sh to capture filter logic pinned to AF_PACKET packets.
Short-term (1-7 days)
Immediately block and review connections to the following DNS endpoints: ntpussl.instanthq.com, ntpupdate.ddnsgeek.com, ntpd.casacam.net, ntpupdate.ygto.com.
Change the rule detection model to depend on payload, applying structural identification indicators. Update the Suricata rule to match byte-level from BPF backdoor like: udp[8:2] == 0x3182 or (icmp[8:2] == 0x1051 and icmp[icmptype] == icmp-echo)
Long-term
Add monitoring rules to the auditd system module to closely track all socket creation operations under the AF_PACKET label, specifically targeting the setsockopt command used to attach BPF filter strings to the kernel.
Restructure the privilege mechanism for running services as root on physical telecom core clusters. Deeply implement the File Integrity Monitoring (FIM) system to immediately patch the spread paths in temporary /run directories.
MITRE ATT&CK Mapping
| Tactic | Technique ID | Technique Name | How BPFDoor uses |
|---|---|---|---|
| Execution | T1059 | Command and Scripting Interpreter | Provide remote shell via HTTP / ICMP |
| Persistence | T1036 | Masquerading | Masquerading legitimate system processes |
| Persistence | T1543 | Create or Modify System Process | Services can be created to maintain persistence |
| Defense Evasion | T1014 | Rootkit | Use BPF in the kernel to hide activity |
| Defense Evasion | T1620 | Reflective Code Loading | Run fileless from /dev/shm |
| Defense Evasion | T1027 | Obfuscated/Compressed Files and Information | Magic packet is encoded, marker fixed |
| Defense Evasion | T1070 | Indicator Removal on Host | Delete file/process traces |
| Command & Control | T1071 | Application Layer Protocol | Communicate via HTTP (httpShell) |
| Command & Control | T1095 | Non-Application Layer Protocol | Tunnel via ICMP (icmpShell) |
| Command & Control | T1094 | Custom C2 Protocol | Magic packet + Hidden IP (HIP) |
| Command & Control | T1090 | Proxy | Relay traffic through infected host |
| Command & Control | T1001 | Data Obfuscation | Padding + hides data in the packet |
| Discovery | T1046 | Network Service Discovery | Passively sniff traffic via BPF |
| Lateral Movement | T1021 | Remote Services | Pivot sang host khác qua tunnel |
| Collection | T1040 | Network Sniffing | Capture packets directly at the kernel level |
IOCs
BPFDoor Controller
6227cb77cb4ab1d066eebf14e825dbc0a0a7f1e9 64171d46c8290c5cd88e0fbce9e23dcecbe20865 65e4d507b1de3a1e4820e4c81808fdfd7e238e10 9bb8977cd5fc7be484286be8124154ab8a608d96
BPFDoor Malware
02aebc3762e766be0ac24ef57a135398344a8f7e 04aa241c574f0a7ec93ba5d27807d8e78467f21e 16f94f0df6003f1566b2108f55e247f60a316185 1db21dbf41de5de3686195b839e74dc56d542974 28765121730d419e8656fb8d618b2068408fe5ae 291af8adf6fa078692d0bf5e0d9d00c376bb3fff 316ac8215095a24429632849407311b18a16e0cf 351febd645c66a3c9a79253d0aefcce8ff77054c 3771319be1c8883610c65977811e93b0bdaddf6f 4181bc848a1cd32911a83e02feac9b8abbd69ae2 43b4dbc71ada99a7b8a8d6d0490ba5526a34f9a0 4b1ea5e7b28eb110d8741b76d34f7dbae6f13b79 4c89beab00e3119cf516d6f98d364a5d99232181 5ddcbe4b591293f7b34fc0ef65db6248bcc67eb6 64171d46c8290c5cd88e0fbce9e23dcecbe20865 7ab39d7aad49abb0f626383ed776fe20a3b4c8f3 88075bbc34655d1fa2a750f3bbdee38214974009 8b5844fcbf6af23bc0b410fc180e7e6bdd4f35c7 8ebe1a71af1061d9e943bdff46c5ed954d8c9348 937f6068df4e091cf92d50afb3c6b7cad1de6230 9bdea37835cdb7f0b291891386af28184ac85f79 a6b66b8b7eae2969fd7237888d30766baa1b2274 be47b0c2fb328a338874f6efbe8305ddb74f6a48 c38fc109e31c9d67a1efc6cb767f826b7e46fb19 c54e214810ca7042d013845076b0360bdd7132b2 c83651d7706efa8c115f2a0edb07f863f4e79ce5 d53b7d0030a095a3ffa4b67d13de82d08adda248 d61bf187c4cd3f9953b567b3ad320b9ecde1c347 d9037e0de902e6f7b6c5f1b3269ba482f5e67c8a dc94eaa39e11f2ca7739d2cfded9eec1967f33ee dd8db29e90c6b52ee3d2723cc168cf33ee0bb521 e17ddb6515f2d399552245191f98458b68fece7b ef03b84048193a158ecf1f7033ab0cc8869dd2a5 f61589b1f86d8692964a6bd3e96ddadbe22994eb fb488cdfd2e475f0d5cbecfe11e9bab2241f9d50
Reference
New Whitepaper: Stealthy BPFDoor Variants are a Needle That Looks Like Hay
China-Linked Red Menshen Uses Stealthy BPFDoor Implants to Spy via Telecom Networks
Chinese Hackers Caught Deep Within Telecom Backbone Infrastructure - SecurityWeek
BPFDoors Hidden Controller Used Against Asia, Middle East Targets | Trend Micro (US)