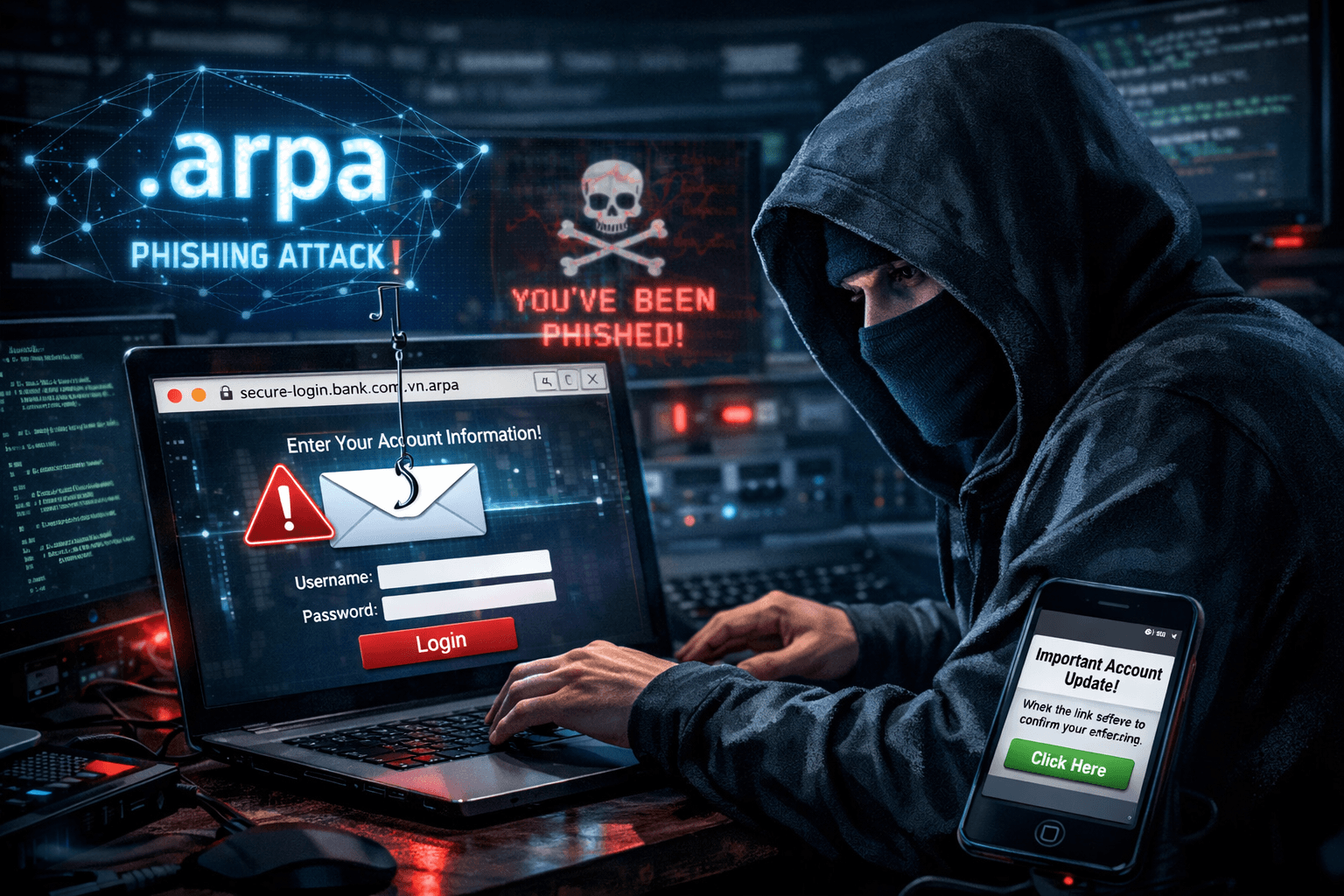
Misuse of TLD .arpa: Exploiting DNS Infrastructure to Spread Phishing
Overview
Current phishing email campaigns are very common, but the Infoblox research team has just discovered a completely new method, previously unreported, to bypass security controls. This technique exploits the .arpa TLD—a core part of the DNS infrastructure—combined with an IPv6 tunnel to host phishing content on domains theoretically not allowed to resolve to an IP address.
Technical Details
1. Why is .arpa dangerous?
The .arpa TLD has a special role in the DNS system: it is used to map IP addresses back to domain names—providing PTR records, not for hosting web content. This is the key point: because .arpa is part of the essential internet infrastructure, domains of this type are almost never blocked by security policies.
2. How do attackers create domains?
Attackers obtain an IPv6 range (through a free tunnel service like Hurricane Electric) and are authorized to manage the corresponding .arpa subdomain. Instead of creating a PTR record as usual, they create an A record for these reverse DNS domain names. Both Hurricane Electric and Cloudflare have been exploited to create these records—both have good reputations, allowing attackers to "borrow" credibility.

Example domain used in phishing email:
d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa
<10-random-characters>.5.2.1.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa
To make these domains harder to detect and block, attackers add a randomly generated subdomain at the front, making each FQDN unique.
3. Phishing email content
Phishing emails in this campaign are very simple—typically just an image containing a hidden hyperlink. The image often promises "free gifts" for completing a survey, requiring a credit card to "pay for shipping." Other scams include service disruption notifications or exceeding cloud storage limits.

4. Traffic Distribution System (TDS)
After the victim clicks on the image, they are redirected through one or more TDS. This system analyzes the victim's traffic and only forwards them to the actual phishing page if certain criteria are met—specifically, a mobile device combined with a residential IP increases the likelihood of reaching the malicious landing page.

One notable point: the hyperlinks in phishing emails only work for a few days. After that, all requests display a standard unsubscribe page or return an error, regardless of the type of traffic—making it very difficult to recreate phishing during investigations.
Additional Tactic: Hijacked CNAME & Subdomain Shadowing
In addition to the .arpa technique, these campaigns also exploit subdomains of well-known legitimate domains. Over 100 cases have been identified where attackers used hijacked CNAMEs from government agencies, universities, telecommunications companies, media organizations, and retailers.
Two notable examples: The domain publicnoticessites[.]com once provided public notice content for over 120 local newspaper websites. When this domain expired, attackers acquired it and gained access to all CNAMEs referencing it, with 8 CNAMEs used in phishing emails. Similarly with hobsonsms[.]com—this domain provided account services for at least three different universities through the same subdomain. Controlling one subdomain allowed attackers to compromise all three.
IOCs (Indicators of Compromise)
⚠️ Important note: The indicators below are related to legitimate services that have been abused. Carefully consider before blocking them entirely.
IPv6 Reverse DNS Domains (with DGA subdomain)
| Domain Pattern | Description |
|---|---|
<10 random characters>.5.2.1.6.3.0.0.0.7.4.0.1.0.0.2[.]ip6[.]arpa |
IPv6 reverse DNS + DGA subdomain |
<10 random characters>.1.9.5.0.9.1.0.0.0.7.4.0.1.0.0.2[.]ip6[.]arpa |
IPv6 reverse DNS + DGA subdomain |
<10 random characters>.d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2[.]ip6[.]arpa |
IPv6 reverse DNS + DGA subdomain |
Malicious Phishing Domains
| Domain | Type |
|---|---|
actinismoleil[.]sbs |
Phishing domain |
cablecomparison[.]shop |
Phishing domain |
cheapperfume[.]shop |
Phishing domain |
drumsticks[.]store |
Phishing domain |
fightingckmelic[.]makeup |
Phishing domain |
TDS (Traffic Distribution System) Domains
| Domain | Type |
|---|---|
dulcetoj[.]com |
TDS domain |
golandof[.]com |
TDS domain |
politeche[.]com |
TDS domain |
taktwo[.]com |
TDS domain |
toindom[.]com |
TDS domain |
Domains Hijacked CNAME
| Domain | Type |
|---|---|
publicnoticessites[.]com |
Hijacked CNAME (120+ local newspapers) |
hobsonsms[.]com |
Hijacked CNAME (3 universities) |
hyfnrsx1[.]com |
Hijacked CNAME (global F&B company) |
Recommendations
FPT Threat Intelligence provides the following recommendations:
Monitor DNS queries to domains like *.ip6.arpa that resolve to an A record (unusual—not a PTR). This is the clearest sign of this technique.
Alert when an A record appears in the reverse DNS namespace (in-addr.arpa or ip6.arpa).
Track traffic from mobile devices to strange .arpa domains.
Check passive DNS for CNAMEs pointing to expired domains within your internal infrastructure.
Inspect subdomains of domains your organization owns to detect dangling CNAMEs.
Security measures based on domain reputation, registration information, and policy blocklists are ineffective against these .arpa domains because they have a clean reputation, no registration information, and are often not blocked by policy. Additional layers to detect unusual DNS behavior are necessary.
Implement Protective DNS / DNS Firewall with the ability to detect anomalous A records in the reverse namespace.
Regularly check and remove dangling CNAMEs from your organization's DNS.