No login required, no clicks needed: n8n vulnerability allows hackers to take over the server in an instant
Overview
The Pillar research team discovered an extremely critical vulnerability in n8n that allows:
Remote Code Execution (RCE)
No login required (unauthenticated)
No user interaction needed (zero-click)
Just accessing a public form can initiate an attack.
If you use:
n8n Cloud → is safe
Self-host → needs immediate update with the patch
Vulnerability CVE-2026-27493
1. Exploitation conditions
A multi-step form
A step that re-displays user data (e.g.,
Thank you, {{Name}})The form is public on the internet
=> This is a very common configuration (contact forms, sign-up forms…)
2. How the attack works (simplified)
The system processes the form twice (double evaluation):
- Step 1: The server takes user input (e.g., Name) and inserts it into HTML
Thank you, {{Name}}
- Step 2: The server scans the HTML again to find {{ }} and executes it like code. If an attacker enters:
{{ malicious_code }}
=> It will be executed in step 2, leading to RCE.
3. Real-world attack scenario
Attacker opens the public form /form/contact-us
Enters payload into the Name field
Submits form
Server:
Injects payload into HTML
Execute payload
Result:
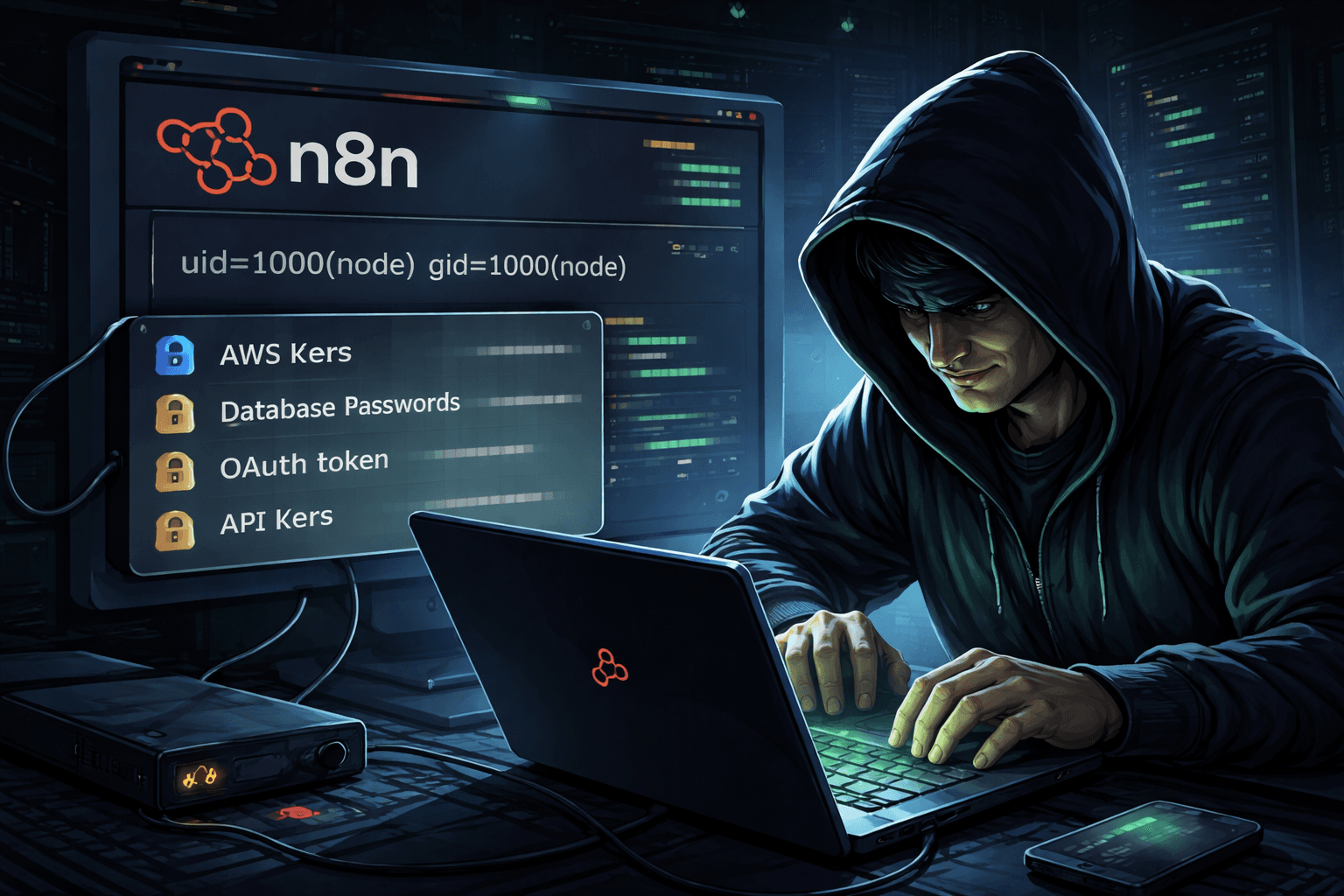
uid=1000(node) gid=1000(node)
➡️ The server has been compromised.
Vulnerability CVE-2026-27577
This is a sandbox escape in the expression processing engine.
1. Cause
AST filter missed SpreadElement
Allows access to dangerous variables like process
2. Sample Payload:
={{ ((g) => g.getBuiltinModule('child_process').execSync('id').toString())({...process}) }}
Result:
Access Node.js runtime
Run system command

3. The core danger point
n8n stores all credentials:
AWS keys
Database passwords
OAuth tokens
API keys
👉 Just need RCE → gain access to the entire system
Form public = perfect entry point
No login required
No permissions needed
No interaction with other users necessary
Affected to cloud multi-tenant
It can affect other tenants
Risk of spreading throughout the entire system
In-depth analysis (security perspective)
1. Nature of the vulnerability: Expression Injection
This is similar:
SQL Injection
SSTI (Server-Side Template Injection)
However, it's more dangerous because:
Go straight to RCE
No need to bypass many steps
2. Double Evaluation = design flaw
The mistake lies in:
User input → render → Re-parse as code
👉 This is an extremely dangerous anti-pattern in secure coding.
3. Sandbox is not an absolute layer of protection
The sandbox is bypassed at the compile stage, not at runtime.
=> If dangerous data gets through the compile stage, runtime can't save it.
4. Why doesn't TypeScript detect it?
AST missing case SpreadElement
Type system thinks it's fully covered
5. Complete exploit chain
Public Form -> Expression Injection (CVE-2026-27493) -> Sandbox Escape (CVE-2026-27577) -> RCE -> Dump credentials -> Lateral movement / Cloud compromise
6. Severity level
| Criteria | Evaluate |
|---|---|
| Attack vector | Internet |
| Auth | No need |
| User interaction | No |
| Impact | All systems |
| CVSS | ~9.5 (Critical) |
Conclusion
This is one of the most dangerous vulnerabilities because:
No auth needed No click needed
Exploitation is extremely easy (just need a browser)
Affects the entire downstream system
If n8n is deployed and not patched, consider it compromised
Recommendation
FPT Threat Intelligence provides the following recommendations for N8N users:
Update immediately
Check all forms: Do they display input again?
If exploitation is suspected: Rotate all credentials
Check variable: N8N_ENCRYPTION_KEY
Apply patches immediately