Serious vulnerability ignores authentication in Pan - OS software

Introduction
According to the latest report from February 2025 by Palo Alto Networks, an attack campaign targets the PAL-OS firewall by exploiting the CVE-2025-0108 vulnerability, allowing attackers to bypass authentication.
This is a critical security issue that affects the PAN-OS web management interface, enabling unauthenticated attackers on the network to bypass authentication and execute some suspicious PHP scripts, potentially impacting the integrity and security of the system.
Overview of the Vulnerability
CVE ID: CVE-2025-0108
Severity Level: 8.8 (High)
Description: The vulnerability allows an unauthenticated attacker with network access to the web management interface to bypass authentication and execute some PHP scripts.
Affected Versions
PAN-OS 11.2: All versions before 11.2.4-h4.
PAN-OS 11.1: All versions before 11.1.6-h1.
PAN-OS 10.2: All versions before 10.2.13-h3.
PAN-OS 10.1: All versions before 10.1.14-h9.
Attack Stages
The way attackers exploit this vulnerability primarily involves three main steps that have been recorded:
Network Access: The attacker must have network-level access to the PAN management interface, which is typically available when the interface is exposed externally.
Create Malicious Requests: Using tools like Curl or custom scripts, the attacker sends requests that bypass proper authentication tokens.
Create Malicious PHP Scripts: With authentication barriers bypassed, the attacker executes sensitive PHP scripts to extract configuration data or change firewall settings.
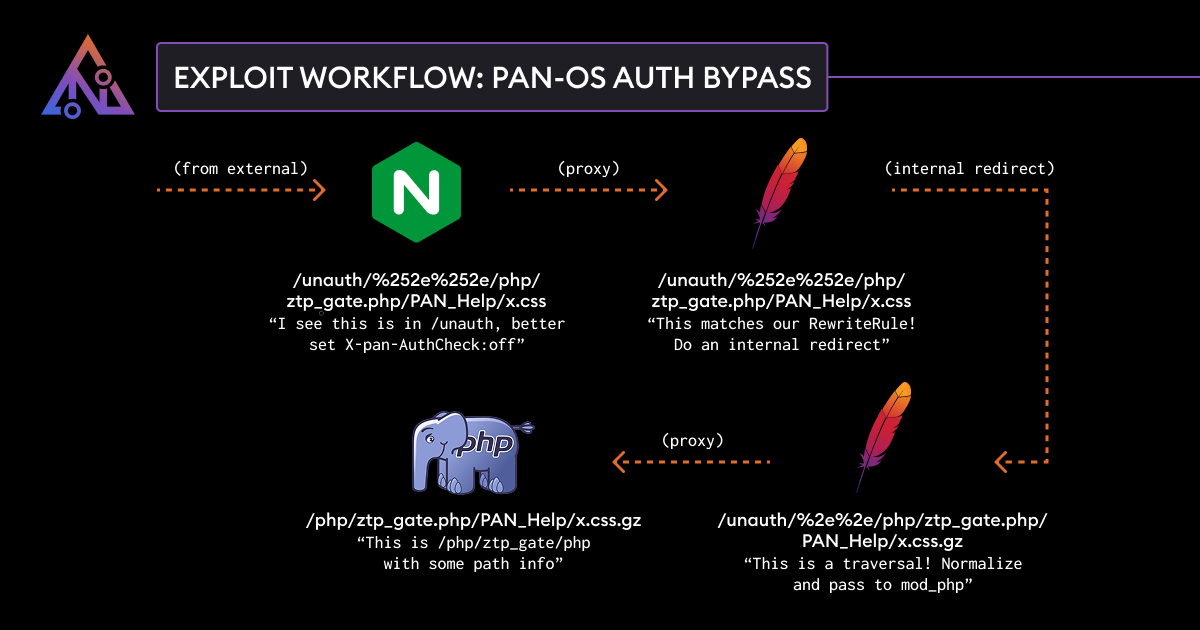
The root cause of CVE-2025-0108 lies in the inconsistent handling of web requests by the management interface components of PAN-OS, including Nginx, Apache, and the embedded PHP application.

These lines are the proxy_set_header configuration in Nginx, used to set or override HTTP headers when Nginx acts as a reverse proxy.
These settings can be used in some attack vectors, such as:
Bypass authentication on firewalls or WAF systems.
Conceal the origin of the request to avoid detection.
Attack the proxy system by sending spoofed requests.
According to the latest report, a configuration segment using directives in Nginx to control the $panAuthCheck variable may be related to the authentication mechanism of the Palo Alto Networks (PAN-OS) system or another security system.

If the attacker accesses
/php/logout.php, the$panAuthCheckvariable is also disabled.This can affect how the system handles logout, which could be a security issue if the logout process is interfered with or bypassed.
Next, the attackers will use the configuration for Apache HTTP Server itself to carry out the next steps in the exploitation process, including

Disable DirectorySlash:
"DirectorySlash off"DirectorySlash is a feature that automatically adds a
/to the end of a URL if it's missing, then performs a redirect.The issue is that Apache uses the hostname from user input to redirect, which can accidentally lead to an Open Redirect vulnerability or Host Header Injection. If an attacker controls the Host header, they can create a redirect to a malicious page.
Example: http://victim.com/admin → http://victim.com/admin/ (Apache automatically adds
/)
Access configuration:
Require all granted- This can allow attackers to gain access to resources
After that, the attackers will send a PHP script to execute

Bypass authentication using
X-PAN-AuthCheck: offExploit Path Traversal or Direct Access
Fake
REMOTE_HOSTto impersonate localhost
The next step allows attackers to easily carry out some exploits they desire by using "Curl." Attackers can exploit Path Traversal vulnerabilities or bypass authentication.

%252e%252e: This helps the attacker "traverse" (move up) to the parent directory bypassing authentication.Access the file
ztp_gate.php- this could be a Zero-Touch Provisioning (ZTP) auto-configuration script of Palo Alto Networks PAN-OS.- If authentication is not required, an attacker can send a request to obtain sensitive information or change the configuration.
After exploiting, attackers can easily carry out actions.

Access other important files:
GET /unauth/%252e%252e/etc/passwd HTTP/1.1GET /unauth/%252e%252e/php/config.php HTTP/1.1
Send a request to change the configuration
If
ztp_gate.phphas an API or a data submission form, an attacker can use:curl -X POST -d "new_config=<malicious_config>"https://target.com/unauth/%252e%252e/php/ztp_gate.phpFrom there, gain control of the device.
Remote Code Execution (RCE) Attack
curl -X GET "https://target.com/unauth/%252e%252e/php/ztp_gate.php?cmd=id"From there, malicious code can be executed on the PAN-OS system.
Recommendation
CVE-2025-0108 is a critical authentication bypass vulnerability affecting Palo Alto Networks' PAN-OS, which can be exploited by an unauthenticated attacker to access specific PHP scripts. To protect the system, recommended measures include:
1.Upgrade to the patched version of PAN-OS:
PAN-OS 11.2 → update to 11.2.4-h4 or later
PAN-OS 11.1 → update to 11.1.6-h1 or later
PAN-OS 10.2 → update to 10.2.13-h3 or later
PAN-OS 10.1 → update to 10.1.14-h9 or later
2. Restrict access to the web management interface
Only allow access from trusted IP addresses (internal subnets or VPN).
Disable access from the internet to the web management interface to minimize the risk of attacks.
3. Apply additional protective measures
If you can't update immediately, configure a firewall rule to block unauthorized access.
Enable multi-factor authentication (MFA) if possible to enhance security.
Conclusion
CVE-2025-0108 is a critical security vulnerability in Palo Alto Networks' PAN-OS software, allowing an unauthenticated attacker to gain unauthorized access to the web management interface and execute certain PHP scripts. Although this execution does not allow remote code execution, it can negatively impact the integrity and security of the system.
This vulnerability has been reported to be actively exploited in the wild, especially when combined with other vulnerabilities like CVE-2024-9474 and CVE-2025-0111. Therefore, implementing protective measures is extremely important to ensure the safety of your system.