When Booking Messages Become a Trap: The Rise of ClickFix Phishing
Cybersecurity researchers have warned about a phishing campaign targeting the hospitality industry, causing extremely large losses.

Overview
Recently, a campaign impersonating travel commerce platforms using the “ClickFix” model has resurfaced to distribute the PureRAT malware. This campaign has been active since early April 2025 and continues to operate vigorously through October of the same year with more sophisticated tactics. The attackers use compromised email accounts to send messages to many hotels across various countries, posing as booking services like Booking.com to lure victims.

As the end of the year approaches, many people around the world, including in Vietnam, are busy planning their year-end trips. This threat has more opportunities to grow stronger, quietly lurking behind seemingly harmless emails.
Initial Impact
Takeover of hotel admin accounts
Infection of systems with PureRAT malware
Loss of control over hotel operations
Initial financial damage
Risk of paving the way for further attacks
Campaign Details
Initially, the attackers will infiltrate by sending phishing emails to hotel email addresses (booking management, administration). The emails are often sent from compromised accounts or with a spoofed "From" address to make them appear as if they are from Booking.com. Naturally, these emails contain links leading to a traffic direction system (TDS) and then to a phishing site like: “booking-agreementstatementapril0225.com“.
\=> For example, the email subject lines will often be “New last-minute booking (REF + DATE)”, “New guest message in reference to your unit – Tracking code:{ID}”…
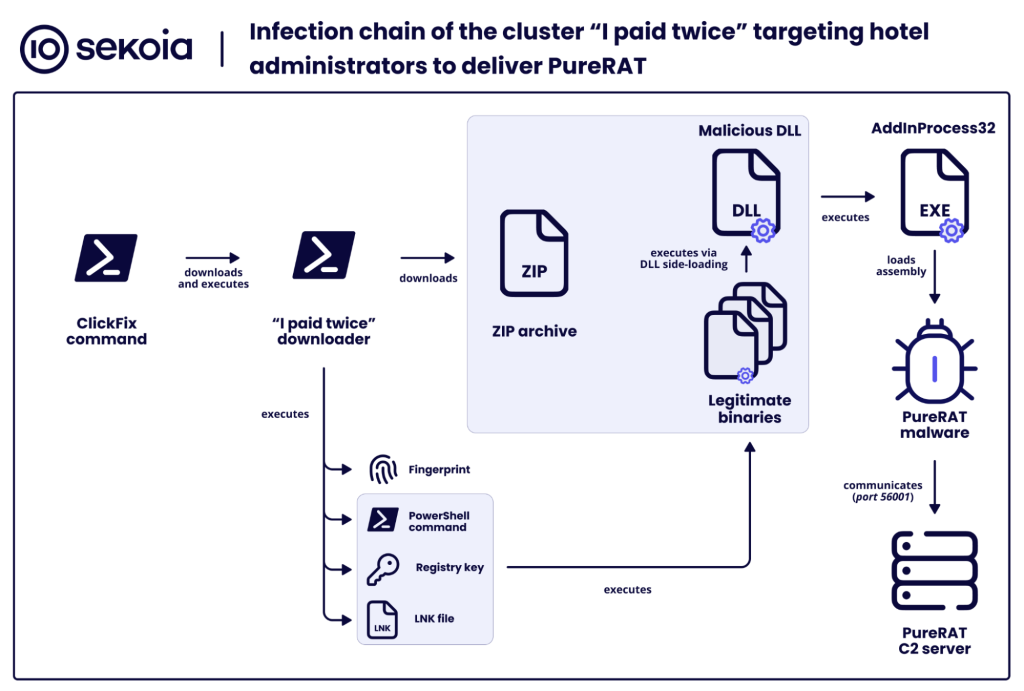
Moving to phase 2, the attacker begins using the “Clickfix” technique to download PURE-RAT onto the target system. When hotel staff or victims click on a link in an email like: https://{randomname}.com/[a-z0-9]{4}, it checks if the victim's machine is running in a sandbox environment. If it is, it exits immediately. After completing the check, the link redirects the browser through an HTTP intermediary, which helps deceive analysis tools and clean the URL. The target endpoint is the ClickFix page, which includes:
Branding from Booking.com or a fake admin extranet
A legitimate-looking interface with logos and CSS similar to the real site


What is ClickFix here? On this phishing page, victims are instructed to manually copy a PowerShell script under the pretense that the hotel's system has an error, requiring them to:
Verify through CAPTCHA (to create a "legitimate" feel)
Copy the PowerShell script (about 200–300 lines long)
Paste it into PowerShell and run it

These PowerShell commands typically collect some initial information from the victim and then send the data to the C2 server so the attacker knows how to execute the appropriate payload for each target.
hostname
OS version
Running AV / EDR
CPU / RAM
proxy configuration
The notable point here is that the PowerShell script also downloads a ZIP file that includes:
1 .exe file (legitimate or appears legitimate)
1 malicious .dll file**

Next, the DLL Side-Loading technique is executed to load the malicious .dll file, which then loads additional PureRAT code into memory (fileless). Once this malware is loaded onto the victim's machine, it can control the machine and gain access to the Booking.com account. From there, the attacker can log directly into the hotel's extranet without needing a password.
Remote desktop / HVNC
Keylogging
Access to webcam & microphone
Steal cookies & sessions
Extract browser information
Take screenshots
Install additional plugins (modular)
In the final stage, the attacker exploits the account and deceives customers. The attacker uses the compromised account to send phishing emails to customers who have booked rooms, using accurate information (obtained from the system) to increase customer trust. Naturally, banking information and payment details will be collected by the attacker on Booking.com phishing pages.

Booking management accounts are also traded on cybercrime forums: selling usernames/passwords, cookies, logs, etc. Their price depends on their value (number of bookings, Genius partner level, region, etc.).
Recommendations
Recommendations for Hotels
Enable MFA (mandatory):
- Only use app-based MFA (Authenticator, Duo) → avoid SMS as it can be easily hijacked.
Do not reuse passwords between Booking, email, and PMS.
Block suspicious logins by:
Checking the Devices / Sessions section → log out of all suspicious sessions.
Monitoring emails for unusual login notifications.
Prohibit staff from clicking on payment links / ClickFix sent via Booking chat.
Establish a customer verification process:
- If a customer reports “payment made but not received by the system”, check directly on the Booking Partner page, not through a link.
Train to recognize TDS redirects:
Strange URLs before reaching a “Booking-like” page.
Use domain camouflage techniques (IDN homograph).
Recommendations for Users
Do not make payments through links outside the app.
Check the domain:
Real Booking:
*.booking.com.
Do not upload passports or ID cards through strange links.
If in doubt, you should:
Change your Booking password.
Review payment history.
Report immediately to the hotel and Booking.
Conclusion
This campaign is proof that cybercriminals are becoming more professional and targeting industries that seem "ordinary," like tourism and hospitality. By infiltrating hotel systems, using real data to deceive customers, and deploying sophisticated malware techniques, they exploit the entire booking chain from hotels to customers.
It is evident that booking data is an attractive target not only now but also in the future because it involves many transactions, multiple parties, and valuable customer data. Protecting customer data alone is not enough; organizations need to safeguard the entire supply chain: hotels, partners, and booking systems. Early detection and response to unusual signs are crucial in the field of cybersecurity today.
IOC
Url
hxxps[://]headkickscountry[.]com/lz1y hxxps[://]activatecapagm[.]com/j8r3 hxxps[://]homelycareinc[.]com/po7r hxxps[://]byliljedahl[.]com/8anf hxxps[://]byliljedahl[.]com/8anf hxxps[://]jamerimprovementsllc[.]com/ao9o hxxps[://]seedsuccesspath[.]com/6m8a hxxps[://]zenavuurwerkofficial[.]com/62is hxxps[://]brownsugarcheesecakebar[.]com/ajm4 hxxps[://]hareandhosta[.]com/95xh hxxps[://]zenavuurwerkofficial[.]com/62is hxxps[://]customvanityco[.]com/izsb hxxps[://]byliljedahl[.]com/lv6qhxxps[://]ctrlcapaserc[.]com/bomla hxxps[://]bknqsercise[.]com/bomla hxxps[://]bkngssercise[.]com/bomla hxxps[://]bkngpropadm[.]com/bomla hxxps[://]cquopymaiqna[.]com/bomla hxxps[://]emprotel[.]net[.]bo/updserc[.]zip hxxps[://]cabinetifc[.]com/upseisser[.]zipDomain
whooamisercisea[.]com whooamisercise[.]com aidaqosmaioa[.]com bqknsieasrs[.]com update-infos616[.]com mccplogma[.]com mccp-logistics[.]com cquopymaiqna[.]comThe indicators listed below are available in CSV format with additional metadata in the SEKOIA-IO/Community GitHub repository. contmasqueis[.]com update-info1676[.]com admin-extranet-reservationsinfos[.]com eiscoaqscm[.]com comsquery[.]com caspqisoals[.]com ctrlcapaserc[.]com admin-extranet-reservationsexp[.]com admin-extranetmngrxz-captcha[.]com admin-extranetrservq-cstmrq[.]com admin-extranetadmns-captcha[.]com extranet-admin-reservationssept[.]com bkngssercise[.]com admin-extranetmnxz-captcha[.]com bknqsercise[.]com admin-extranetadm-captcha[.]com bookreservfadrwer-customer[.]com bookingadmin-updateofmay2705[.]com breserve-custommessagehelp[.]com confvisitor-doc[.]com confirminfo-hotel20may05[.]com guestinfo-aboutstay1205[.]com confsvisitor-missing-items[.]com guesting-servicesid91202[.]com booking-agreementstatementapril0429[.]com booking-agreementaprilreviews042025[.]com booking-viewdocdetails-0975031[.]com booking-agreementstatementapril0225[.]com api-notification-centeriones[.]com booking-visitorviewdetails-64464043[.]com booking-reservationsdetail-id0025911[.]com booking-refguestitem-09064111[.]com reserv-captchaapril04152025[.]com booking-reviewsguestpriv-10101960546[.]com booking-aprilreviewstir-9650233[.]com booking-confviewdocum-0079495902[.]com booking-confview-doc-00097503843[.]com booking-reservationinfosid0251358[.]comPayload & C2
hxxps[://]ctrlcapaserc[.]com/loggqibkng hxxps[://]bqknsieasrs[.]com/loggqibkng 703355e8e93f30df19f7f7b8800bd623f1aee1f020c43a4a1e11e121c53b5dd1 5301f5a3fb8649edb0a5768661d197f872d40cfe7b8252d482827ea27077c1ec 64838e0a3e2711b62c4f0d2db5a26396ac7964e31500dbb8e8b1049495b5d1f3 sqwqwasresbkng[.]com 85.208.84[.]94:56001 77.83.207[.]106:56001






