A vulnerability in Update Health Tools allows hackers to execute arbitrary code on Windows operating systems
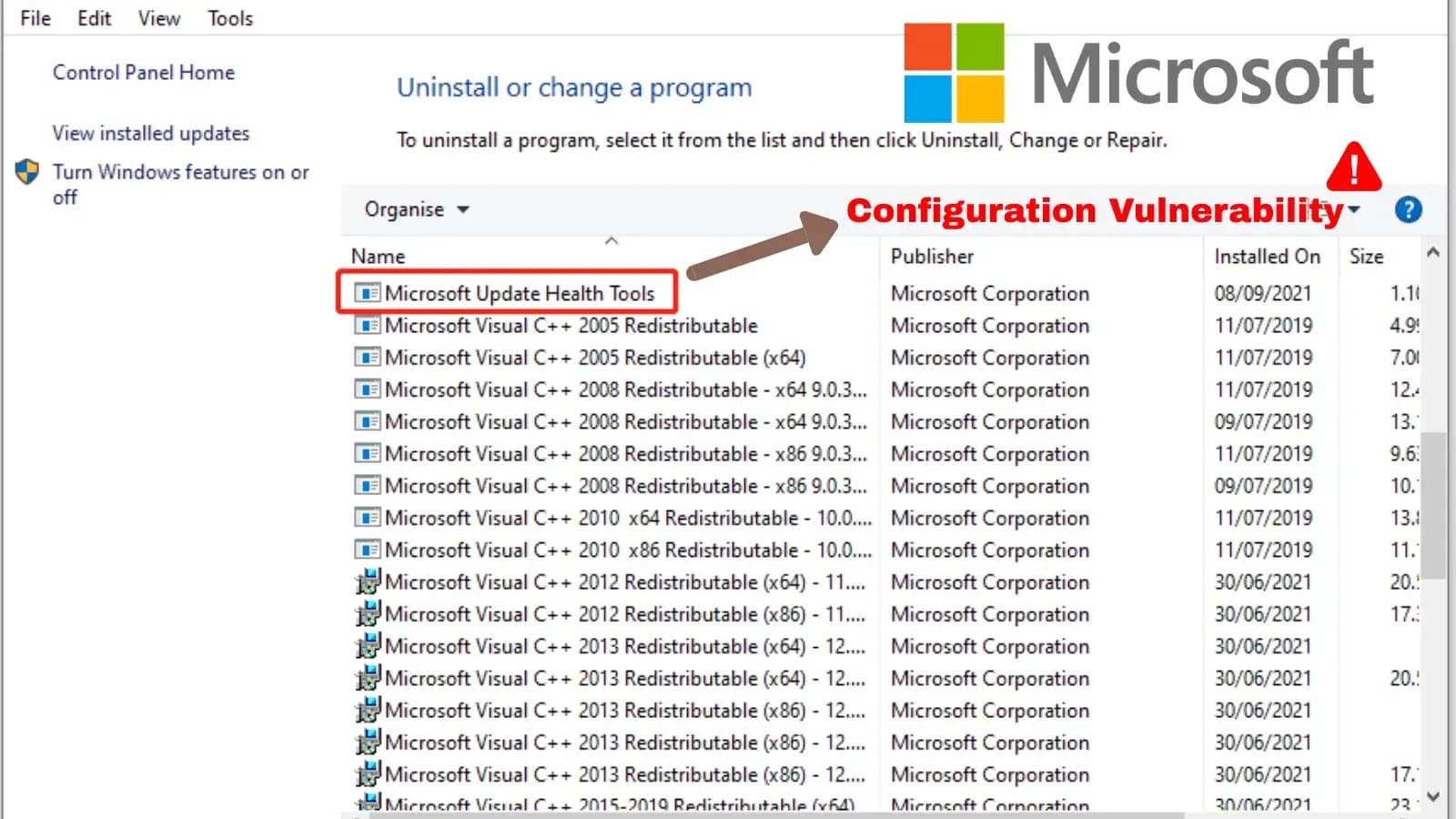
Recently, Microsoft recommended that users urgently install patch KB4023057 to fix a vulnerability in the Microsoft Update Health Tools application. According to cybersecurity experts at Eye Security, this vulnerability allows hackers to remotely execute arbitrary malicious code on affected systems, highlighting the severity of this issue.
Detailed Information
Microsoft Update Health Tools is a Microsoft tool designed to help ensure the Windows update process runs smoothly and reliably. This tool automatically fixes certain issues that may occur during the operating system update process, making it easier for users to receive the latest updates without encountering software or installation problems.
The main features of Microsoft Update Health Tools include:
Fixing Windows update errors: If Windows has trouble downloading or installing an update, this tool helps resolve those issues.
Checking and repairing system errors: It scans for faulty parts of the system that may prevent updates from being downloaded and installed.
Maintaining system stability: Helps maintain the stability of Windows Update and improves performance when downloading or installing updates.
Typically, this tool is installed and runs automatically in the background without user intervention, usually appearing in the list of Windows applications during a major update, such as Windows 10 or Windows 11 updates.
However, according to a recent report by security researchers at Eye Security, this tool, designed to protect Windows systems, has a dangerous vulnerability. This flaw allows hackers to exploit and execute remote code through unused Azure blob storage. Accounts from these storage locations share a common path format: payloadrod0 to payloadprod15.blob.core.windows[.]net. A quick statistic shows that 10 out of 15 blobs receive thousands of repeated requests from nearly 10,000 Azure tenants worldwide with the structure:
GET /<hash>/enrolled.json
GET /<hash>/Devices/<hash>.json
Notably, all these requests use the same user agent named UHSMAILBOX, created by the uhssvc.exe service or Update Health Service located at C:\Program Files\Microsoft Update Health Tools. Through technical measures, security experts have studied how this tool works, assuming that Microsoft engineers created this tool to have an easy service to check which updates need to be installed and decided to use Azure blob storage along with some JSON configuration files as the final choice. Here are the conclusions:
With each new update, it checks if the current device is Entra joined/registered. If not, it stops the update process as this tool is for enterprises.
The service checks if this Entra tenant is registered in the update management system by downloading a file from
/<tenant_hash>/enrolled.jsonand checking if the Enrolled field in the JSON is set to true.If the tenant is registered, it continues the self-enrollment process. This includes downloading another JSON from
/<tenant_hash>/Devices/<device_id_hash>.jsonwhich contains a single field with the policy ID assigned to this computer.Then, Update Health Tools will start polling to:
/<tenant_hash>/Policies/<policy_id>/<cpu>_<osbuild>.jsonThe tool will look at the EnterpriseActionType field to determine the action to take.
The analysis process also led researchers to discover a vulnerability that could be exploited for code execution: ExecuteTool. This action allows the execution of Microsoft-signed binaries. Although it seems safe, attackers could exploit this mechanism.

Immediately, a JSON payload file was created by researchers for testing purposes. This malicious payload points to legitimate Windows executables like explorer.exe or calc.exe and uses ExecuteTool as a stepping stone to bypass any security measures due to its legitimacy. The content of this JSON file is as follows:
{
"RequestId": "00000000-0000-0000-0000-000000000001",
"EnterpriseActionType": "ExecuteTool",
"EnterpriseExecutableClientPath": "..\\..\\Windows\\explorer.exe",
"EnterpriseExecutableClientParameters": "/root,C:\\Windows\\system32\\calc.exe",
"EnterpriseExecutableClientPayload": []
}
The test results confirmed the hypothesis that through ExecuteTool, an attacker could exploit it to execute a command or another valid executable on the target system to achieve full remote code execution capability.

Although a newer version of the Update Health Tool has been released by Microsoft, with a standard web service like devicelistenerprod.microsoft.com deployed, backward compatibility options can still be altered, putting the system at risk.
Mitigation & Recommendations
Administrators and users need to take the following actions to address the dangerous vulnerabilities present in the Update Health Tool:
Update to the latest patch: Users and administrators need to apply the latest KB4023057 patch for this tool to promptly address existing vulnerabilities and avoid risks related to information security issues.
Disable connections to old Azure blob storage: If the system is using Update Health Tool version 1.1, this action can be skipped. However, if version 1.0 is in use, disabling connections to old Azure blob storage should be done immediately. Users and administrators must ensure the registry key
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\UpdateHealthTools\UHS.ENABLEBLOBDSSCHECKis not set to1.Monitor DNS traffic and network traffic: Implement monitoring rules in the EDR/SIEM system to alert and detect early connections to old Azure blob storage or connections to unfamiliar servers with unusual behavior.






