Are you installing a hacker's VSCode extension?
In an era where developers increasingly rely on extensions, a silent but extremely dangerous threat has emerged: the WhiteCobra hacker group has exploited Visual Studio Code extension repositories to distribute dozens of fake plugins. These extensions are expertly designed to steal crypto wallets and sensitive user data.
You might not realize that behind the "harmless" interface is a sophisticated supply chain attack targeting the Web3 community, blockchain developers, and anyone installing tools from the VSCode Marketplace or OpenVSX.
Do you think you're coding? WhiteCobra is recoding your wallet.
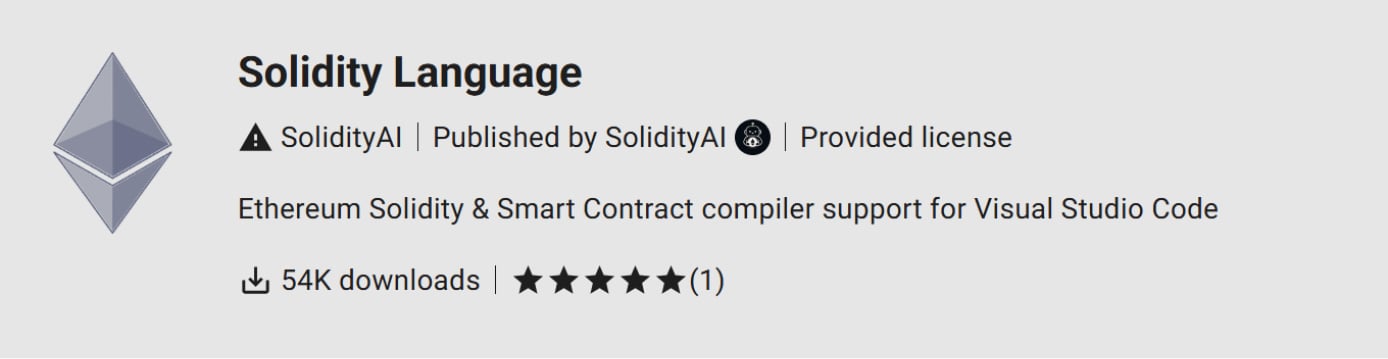
A developer shared on their personal page about how all the money in their digital wallet was drained after installing a seemingly legitimate extension called “contractshark.solidity-lang“.
.png)
The developer explained that the extension had all the signs of a legitimate product, with a professionally designed icon, detailed description, and 54,000 downloads on OpenVSX. In July, this hacker group also carried out a theft of $500,000 in cryptocurrency with similar extensions.
About WhiteCobra
WhiteCobra is known as a hacker organization behind the theft of cryptocurrency wallets through the distribution of fake extensions on Visual Studio Code and the OpenVSX Marketplace. The main goal of this group is to steal crypto wallets, login information, and sensitive data from developers, especially those working in the Web3 and blockchain fields.
WhiteCobra doesn't operate by "knocking on each computer's door," but instead sneaks into the software supply chain - specifically by exploiting developers' trust in VSCode extensions:
Releases fake extensions with names, descriptions, and icons identical to legitimate ones.
Embeds malicious code in the
extension.jsfile, connecting externally to download the payload.Installs malware like Lumma Stealer to steal browser data, cryptocurrency wallets, system information, etc.
Has its own "playbook": detailed instructions on spreading, optimizing downloads, and profit targets ($10K to $500K).
How WhiteCobra Attacks
According to the internal playbook that guides this group's execution flow, there are 5 attack stages:
Stage 1: Packaging - Create a malicious
.vsixextension.Stage 2: Deployment - Release on the marketplace.
Stage 3: Promotion - Market to attract users.
Stage 4: Inflation - Increase fake downloads (social proof).
Stage 5: Exfiltration - Steal data and transfer money immediately.
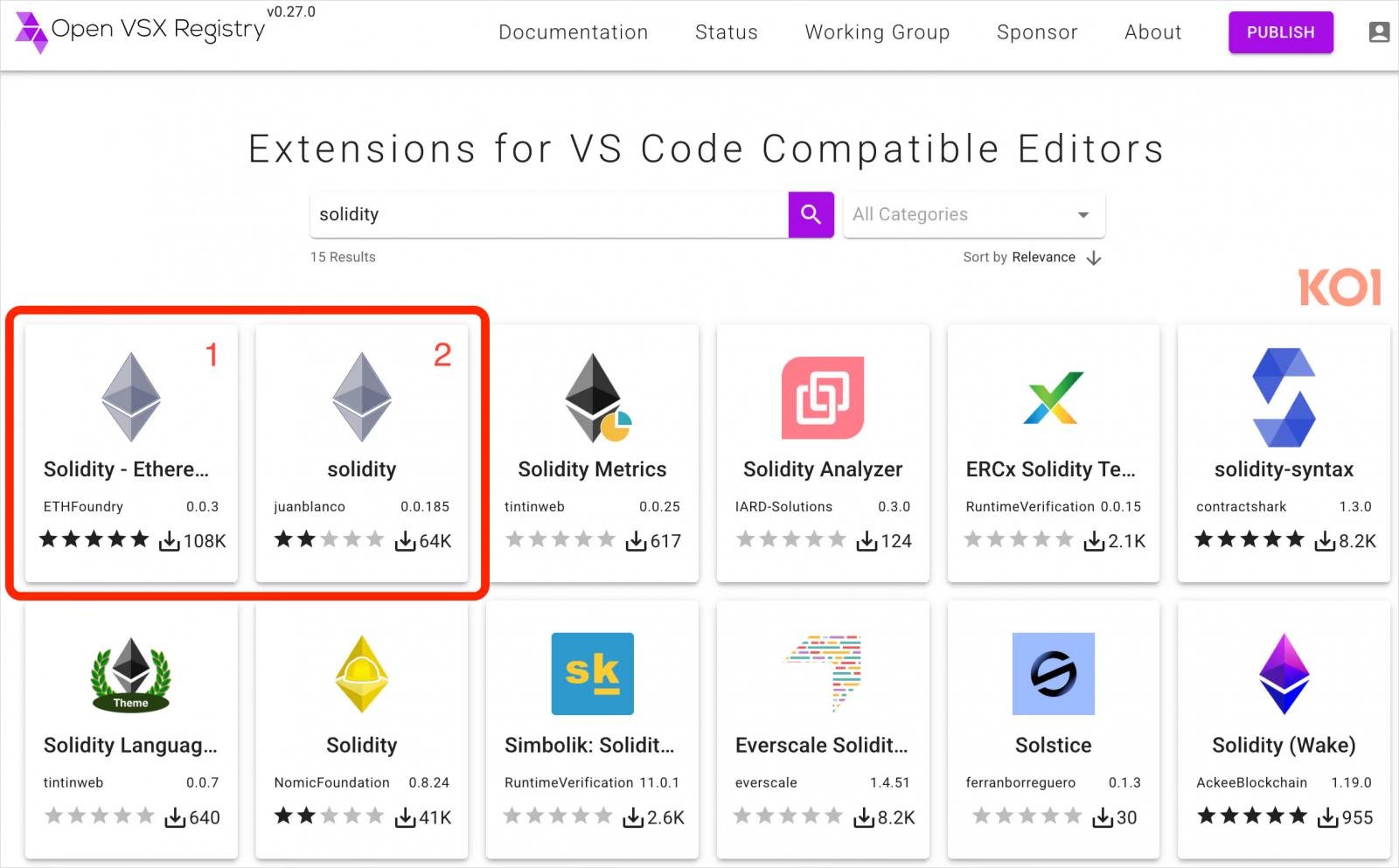
First, hackers will deploy and upload the extensions to marketplaces like OpenVSX (Cursor, Windsurf) and VSCode Marketplace. When uploading, they use the extension name, description, icon, and convincing details to gain the trust of developers.
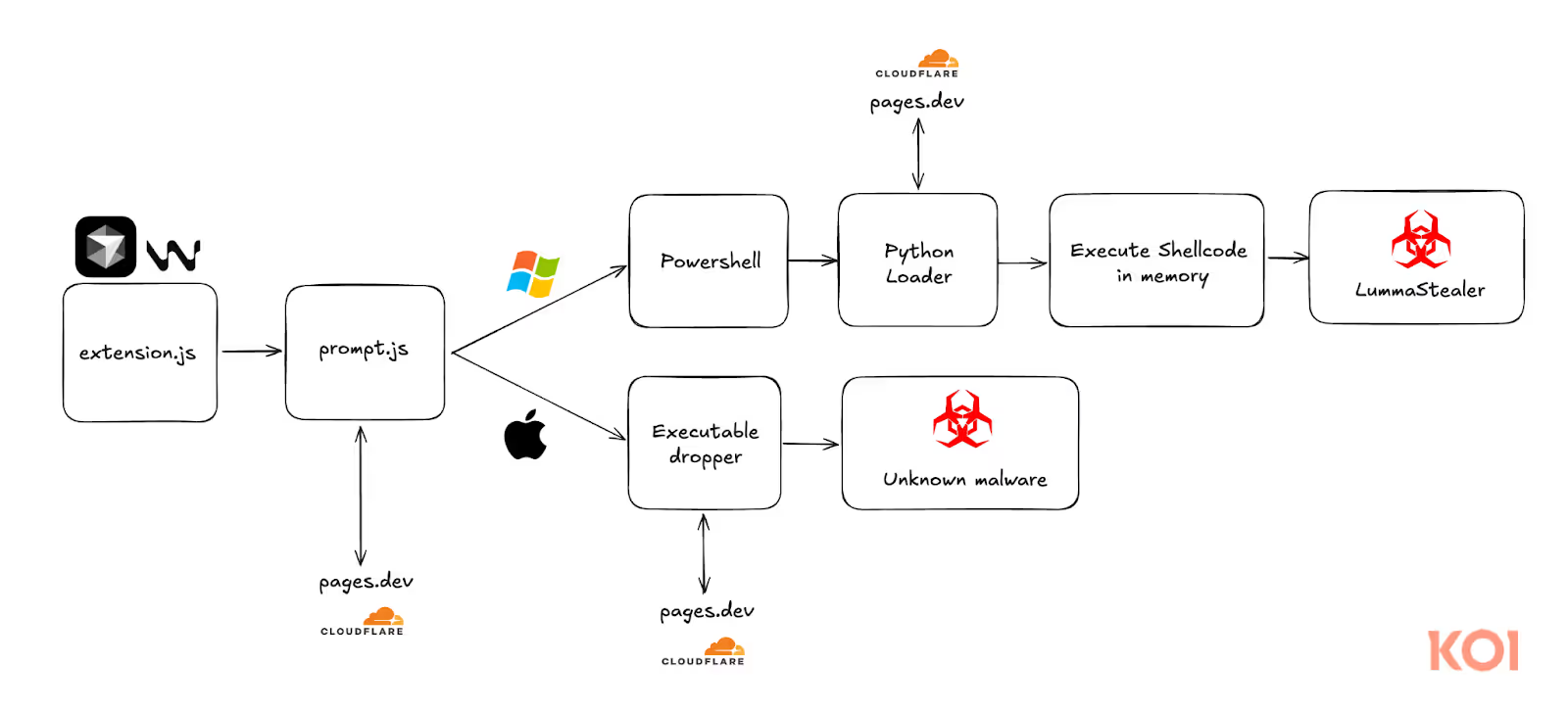
The actual malware is pushed to a secondary script: prompt.js. This is where the dangerous execution logic resides, called from extension.js through the ShowPrompt() function.

The ShowPrompt() function will be executed, and this is also a starting point for loading the base64 encoded malware from an external source or embedding it internally. To bypass reviewers, hackers will use indirect eval() and obfuscate the string with characters like $, &, and reverse() to make it harder to detect.

The malware will be downloaded through a script with a malicious domain:
- g83u.pages.dev


A payload file will then be downloaded and executed to load additional Python embed (of Python 3.12.8) if it's not already present. Additionally, this payload will hide itself and automatically clean up, then quickly terminate to avoid suspicion.

Next, a highly dangerous malware will be downloaded and executed: LummaStealer - a software that steals information (crypto wallets, cookies, passwords, browser extensions, messaging apps, VPN/VNC applications...).

After analyzing and reading logs from Process Monitor (Procmon), experts noted that the process generated from the shellcode was executed in memory as mentioned above.
.png)
.avif)
From the logs, the attacker's intention at this stage is to collect sensitive information about accounts and connections from the system, including:
Telegram login accounts
FTP login information and file-sharing services
VPN configuration for anonymity/lateral movement
Access tokens for cloud systems like AWS, Azure
Finally, after completing the collection of “seed phrases” (wallet recovery phrases), account information, and other sensitive data, the extension sends it to the command and control (C2) server. The attacker uses the backdoor ScreenConnect on port 8041 to maintain long-term control.


Conclusion
The WhiteCobra campaign is clear evidence of one of the most dangerous threats today: software supply chain attacks. By exploiting extension distribution platforms like VSCode Marketplace or OpenVSX, this group has successfully:
Disguised malicious extensions as legitimate development tools
Infiltrated developers' systems quietly and subtly
Stolen digital assets (crypto) directly from the work environment
The concerning part is that the techniques used are not complicated, yet they are extremely effective because they target trust—a factor that the developer community always places in open-source tools.
Recommendations
Control extensions in VS Code
Only install extensions from official sources, prioritizing Microsoft's marketplace, and do not trust unclear sources like OpenVSX.
Disable or limit extension installation rights for unnecessary users, especially in corporate environments.
Use a whitelist of extensions for internal developers.
Enhance user awareness training
Warn technical staff and developers about attackers' “Inflation + Promotion” tactics:
Faking extension download numbers to build trust
Advertising on social media with bots
Do not download extensions just because they have many downloads if the source code is not verified.
Protect sensitive information
Do not store seed phrases, API tokens, or SSH keys in plaintext in the VS Code directory or user profile.
Use a secret manager (like HashiCorp Vault, AWS Secrets Manager) instead of manually using
.env,secrets.json.Set appropriate permissions for directories containing sensitive information.
IOC
Domain
File Hash
1a728a7b7f68a71474a6a04f92960b18aae45ae5d00ea9a1d88174f8bd4ffa10
89848e8a1c8840a0561fcae2948b5941ed55a53474298007d7272f391b28c1b9
fa078483566de02cb64d970d06aa82470beee4c665cfee6915968cb0adb2c6c4
39459ad404c9f0ad361d82b9f96d60f13a9281d3746ada4ef8675dd80fcb9a7e
e8ce84a6e84d4bb0ee50dcde0a72dab9f2e6a2c2f80eeab4df243d5eaaa57a6f
99b976ff0908b03d277bc96d0010b0f1aef8ae1529b753c645c57b7399760a51
22350ef4cdee6af4cbe7809f98256dbfd882dab08ea51ab14880d5da9ce9c06d
118b10295fea2613f72bc89074db9ab82a57c44ab7f62bddb3a86a4ed87f379f
Extension
OpenVSX:
ChainDevTools.solidity-prokilocode-ai.kilo-codenomic-fdn.hardhat-solidityoxc-vscode.oxcjuan-blanco.soliditykineticsquid.solidity-ethereum-vscETHFoundry.solidityethereumJuanFBlanco.solidity-ai-ethereumEthereum.solidity-ethereumjuan-blanco.solidityNomicFdn.hardhat-solidityjuan-blanco.vscode-soliditynomic-foundation.hardhat-soliditynomic-fdn.solidity-hardhatCrypto-Extensions.solidityCrypto-Extensions.SnowShsoNo
VSCode Marketplace:
JuanFBlanco.awswhhETHFoundry.etherfoundrysEllisonBrett.givingblankiesMarcusLockwood.wgbkVitalikButerin-EthFoundation.blan-coShowSnowcrypto.SnowShoNoCrypto-Extensions.SnowShsoNoRojo.rojo-roblox-vscode







