BackConnect, the new weapon of the Black Basta and Cactus ransomware groups

Overview of BackConnect Malware, Black Basta Group, and Cactus
Recently, researchers from Zscaler, a cloud security company in the US, discovered a connection between two ransomware groups, Black Basta and Cactus. Both use the same sophisticated social engineering attack methods through Microsoft Teams and employ BackConnect, a proxy malware, to access corporate networks. Further research revealed that Zloader created a new proxy malware called BackConnect, containing code similar to Qbot (QakBot), allowing cybercriminals to connect remotely, hide activities, steal data, and escalate attacks within the victim's network undetected. All Zloader, Qbot, and BackConnect malware are believed to be linked to the activities of the Black Basta group. According to a recent report by Trend Micro, they also found that the Cactus group uses BackConnect to carry out attacks.
Attack Methods of Black Basta
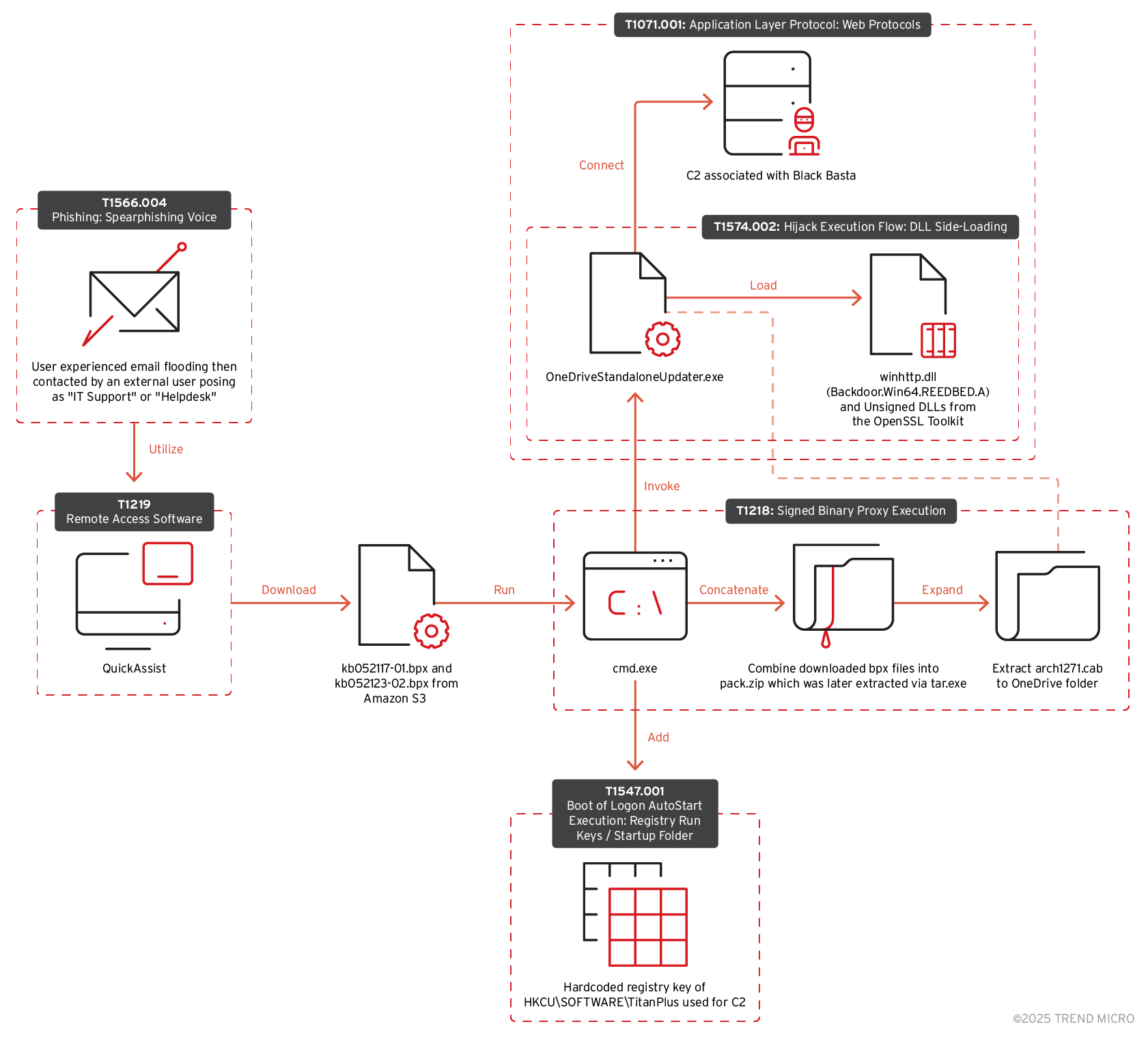
When researchers from Trend Micro investigated, they discovered a technique used by the DarkGate malware, where the victim's mailbox becomes flooded with emails. Then, an external attacker impersonates an IT support or helpdesk member and contacts the victim through Microsoft Teams. During the Teams communication, the victim is persuaded to allow the attacker access through Quick Assist. By using this feature, the victim permits the attacker to share control of the device. Microsoft has issued warnings about attackers impersonating IT staff to gain control through this feature. Now, this method is being used by Black Basta..
Then, the attacker downloads two malicious .bpx files from cloud repositories, and the .bpx file names will differ for each attack. After downloading, these two .bpx files are combined into a .zip file named "pack.zip," which can be extracted using Tar. After extracting "pack.zip," two .cab files are created in C:\Users\<user>\AppData\Local\Temp. Then, the .cab files are further extracted into the OneDrive folder using the command:
expand "C:\Users\<user>\AppData\Local\Temp\<filename>.cab" -F:* "C:\Users\<user>\AppData\Local\Microsoft\OneDrive"
After extracting into the OneDrive folder, the following files are created there:C:\Users\<user>\AppData\Local\Microsoft\OneDrive\winhttp.dll
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\libssl-3-x64.dll
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\vcruntime140.dll
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\libcrypto-3-x64.dll
OneDriveStandaloneUpdate.exe will then be run using the command
"C:\Users\<user>\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe" -Embedding
The file winhttp.dll is a loader used to decrypt the backdoor in the settingsbackup.dat file found in pack.zip. After the update, some configuration files have been modified:
C:\Users\<user>\AppData\Local\Temp\.ses
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\StandaloneUpdater\PreSignInSettingsConfig.json
C:\Users\<user>\AppData\Local\Microsoft\OneDrive\StandaloneUpdater\Update.xml
When OneDriveStandaloneUpdater.exe is run, it connects to IP 38.180.25[.]3. This IP is considered malicious.

Additionally, the attacker adds to the registry to store the IP address of BackConnect:
reg add "HKCU\SOFTWARE\TitanPlus" /v 1 /t REG_SZ /d "38.180.25.3A443;45.8.157.199A443;5.181.3.164A443" /f
The IPs 38.180.25[.]3, 45.8.157[.]199, and 5.181.3[.]164 added to the registry are considered malicious, associated with C&C servers and Black Basta.
Attack Methods of Cactus

With the Cactus malware group, the attack methods are similar to the Black Basta group. After a successful infection, the malware uses several techniques to spread:
Server Message Block (SMB) and Windows Remote Management (WinRM): Uses SMB through shared folders and WinRM to execute commands and scripts remotely, allowing it to move across the entire network.
Attacks ESXi servers by setting up a SystemBC proxy malware named socks.out, creating a root SSH session.
Uses WinSCP software to transfer files from a domain named pumpkinrab[.]com (208[.]115[.]200[.]146)
Recommendations
FPT Threat Intelligence recommends users:
If you notice your mailbox is flooded with strange emails, report it to your company's IT team for support.
Be cautious of messages from unknown people, especially from unfamiliar accounts claiming to be IT staff or helpdesk, trying to convince you to share Quick Assist.
Update the list of IOCs below to prevent attack behaviors early.
IOC
| SHA256 | Filename | Detection |
| b79c8b7fabb650bcae274b71ee741f4d2d14a626345283a268c902f43edb64fd | winhttp.dll | Backdoor.Win64.REEDBED.A |
| 60bca9f0134b9499751f6a5b754a9a9eff0b44d545387fffc151b5070bd3a26a | wscapi.dll | |
| 623a43b826f95dc109f7b46303c6566298522b824e86a928834f12ac7887e952 | run2.bat |
5.181.159[.]48
45.128.149[.]32
207.90.238[.]46
45.8.157[.]158
195.123.233[.]19
178.236.247[.]173
195.123.241[.]24
20.187.1[.]254
5.78.41[.]255
38.180.192[.]243
207.90.238[.]52
89.185.80[.]251
91.90.195[.]91
45.8.157[.]162
20.82.136[.]218
45.8.157[.]146
5.181.3[.]164
195.123.233[.]148
45.8.157[.]199
89.185.80[.]86
195.211.96[.]135
38.180.25[.]3
38.180.135[.]232
185.190.251[.]16
pumpkinrab[.]com
hxxps://sfu11[.]s3[.]us-east-2[.]amazonaws[.]com/js/kb052117-01[.]bpx
hxxps://sfu11[.]s3[.]us-east-2[.]amazonaws[.]com/js/kb052123-02[.]bpx
hxxps[://]filters14[.]s3[.]us-east-2[.]amazonaws[.]com/






