BlackLock Ransomware: "The Multi-Platform Phantom" Lurking in Your System

Nowadays, alongside online scams, ransomware variants are also emerging rapidly and are extremely dangerous. Of course, we must mention BlackLock—a ransomware-as-a-service (RaaS) group. This means they provide data-encrypting malware to affiliates for attacks, while the group behind it shares the ransom collected.
This group has been active since March 2024, initially under the name ElDorado (or Eldorado). Later, they rebranded to BlackLock at the end of 2024 to reposition themselves in the hacker community and expand their operations.
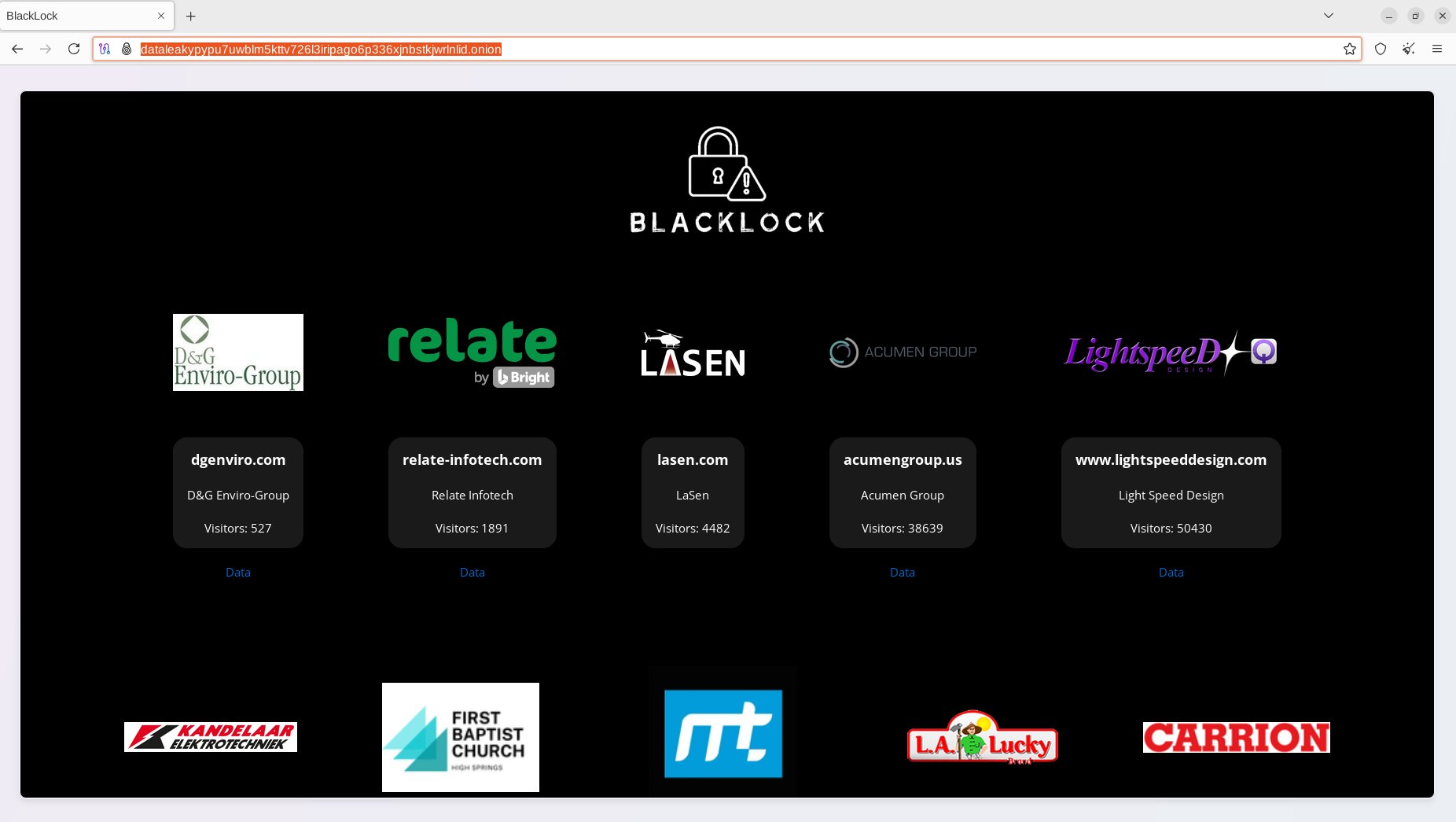
As of February 2025, there have been 46 victims across various sectors: economic, including electronics, academia, religious organizations, defense, healthcare, technology, IT/MSP providers, and government agencies. The affected organizations are based in Argentina, Aruba, Brazil, Canada, Congo, Croatia, Peru, France, Italy, Spain, the Netherlands, the United States, the United Kingdom, and the UAE.
A particularly dangerous aspect of BlackLock is that the attackers use the GO programming language to deploy ransomware variants, allowing them to target Windows, Linux, and VMware ESXi systems.

In a reported case, when the malware is executed, it steals a lot of sensitive information from the victim as well as server system information, including configuration files and login credentials.

Main Impact
Loss of data access
- Data is fully encrypted by BlackLock, preventing victims from accessing systems or important internal documents (accounting, production, customers, etc.).
Financial damage
- Organizations may face ransom demands ranging from thousands to millions of USD.
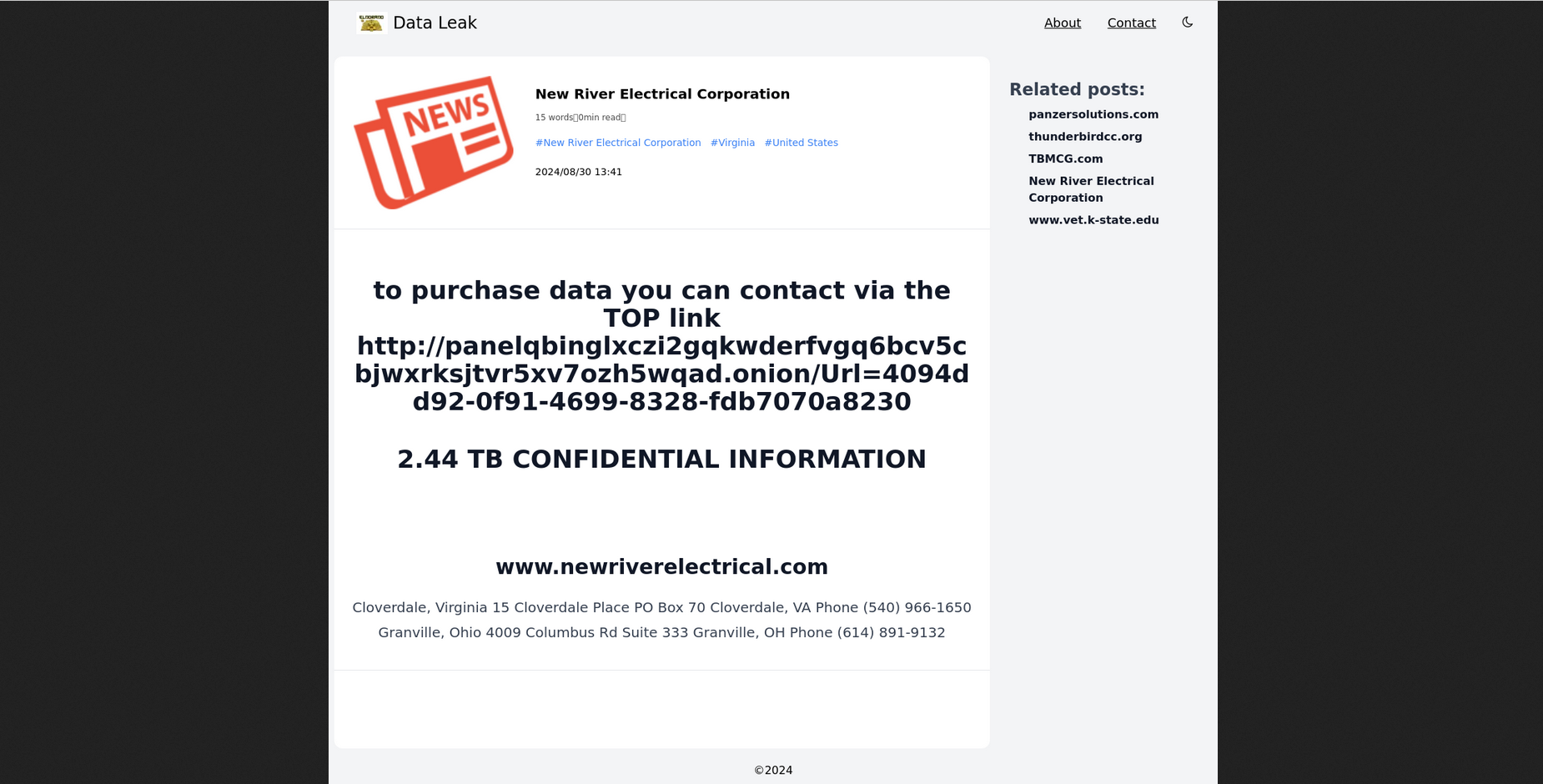
Leakage of sensitive information
- Leaked data may include: customer information, contracts, internal source code, government documents.
Chuỗi kỹ thuật
Initially, like many other cybercriminal groups, BlackLock ransomware conducts reconnaissance on the target system with the specific aim of gathering information about the victim before launching an attack. As mentioned earlier, BlackLock does not limit itself to a specific industry but targets multiple sectors (infrastructure, IT, healthcare, education, agencies). Here, they may use public services like Shodan.io, WHOIS & DNS Enumeration, or in some cases, Google Dorking to find basic information: public IP, VPN gateway, business email, exposed systems (VDI, RDP, Web server, email server, etc.).
After that, the malware moves to the initial intrusion stage, with the main goal of gaining initial access to the target system. According to analysis by Resecurity, the attackers use four main techniques, including:
Brute-force or credential stuffing attacks: If a password list is leaked, it can be used to log into VPN, RDP, or email.
Phishing emails: Sending emails containing malware or links to PDF/Office documents with malicious macros.
Exploiting unpatched vulnerabilities:
Web servers (Apache, nginx, WordPress, etc.)
VPN/Firewall appliances (Fortinet, SonicWall, etc.)
Indirect malware installation through third-party software (supply chain): The group may exploit MSPs or software with extensive system privileges.
After that, the attacker will maintain access to the target system. Here, they will create new user accounts like blog and dataleak, and perform privilege escalation between users. A dangerous point is how the attacker uses chown, chmod, and chgrp to change permissions of the hidden .ssh directory, allowing for unauthorized SSH access.

Not only do they stop at creating accounts, but right after gaining access, they erase their tracks to evade analysts and antivirus systems.

Next, the attackers will perform privilege escalation in the target system, with the main goal of upgrading from a regular user to root or admin rights. Here, they will look for sensitive information from configuration files like /etc/shadow and .bash_history.

After gaining elevated privileges, the attacker will continue with internal reconnaissance to understand the entire network system for more advanced attack steps. They will mainly gather information from Active Directory:
net group "domain admins" /domain.net user /domain,dsquery, BloodHound.
In addition, they read important internal documents, such as IT documents, file server structure, backup server, and cloud access credentials, as well as map out servers containing important data to prioritize encryption later.
Next, the attacker will begin moving between machines in the internal network with the aim of controlling the entire network from one machine. During analysis, researchers observed several tools and techniques used by this group:
RDP / WinRM / SMB (Windows).
SSH (Linux).
Pass-the-Hash / Token Impersonation.
Remote PowerShell.
Copy and execute payload on another machine.
Use PsExec or WMI to trigger ransomware remotely.
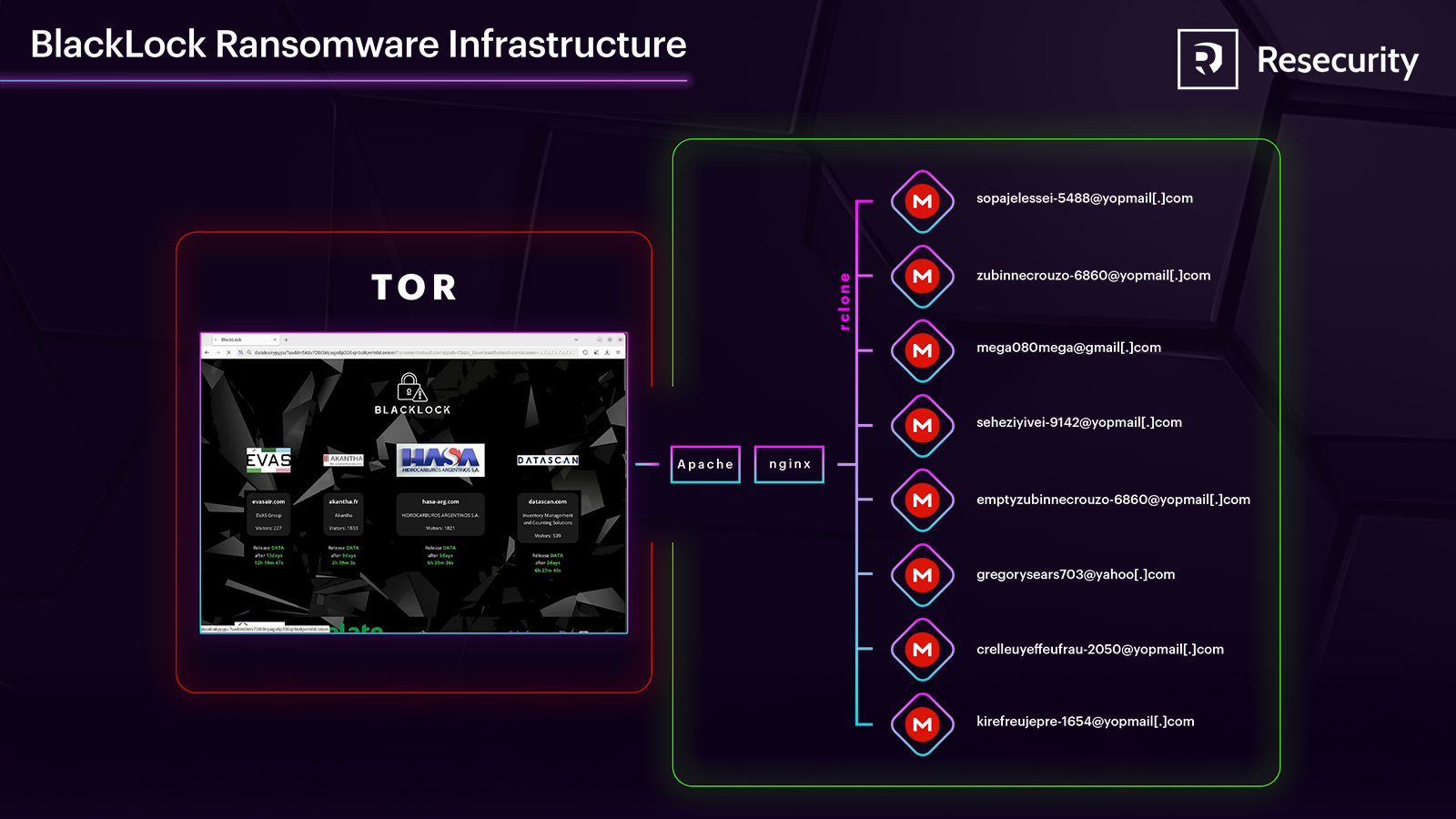
A notable point is the process of gathering information and filtering data. Here, they use rclone to upload data to MEGA.
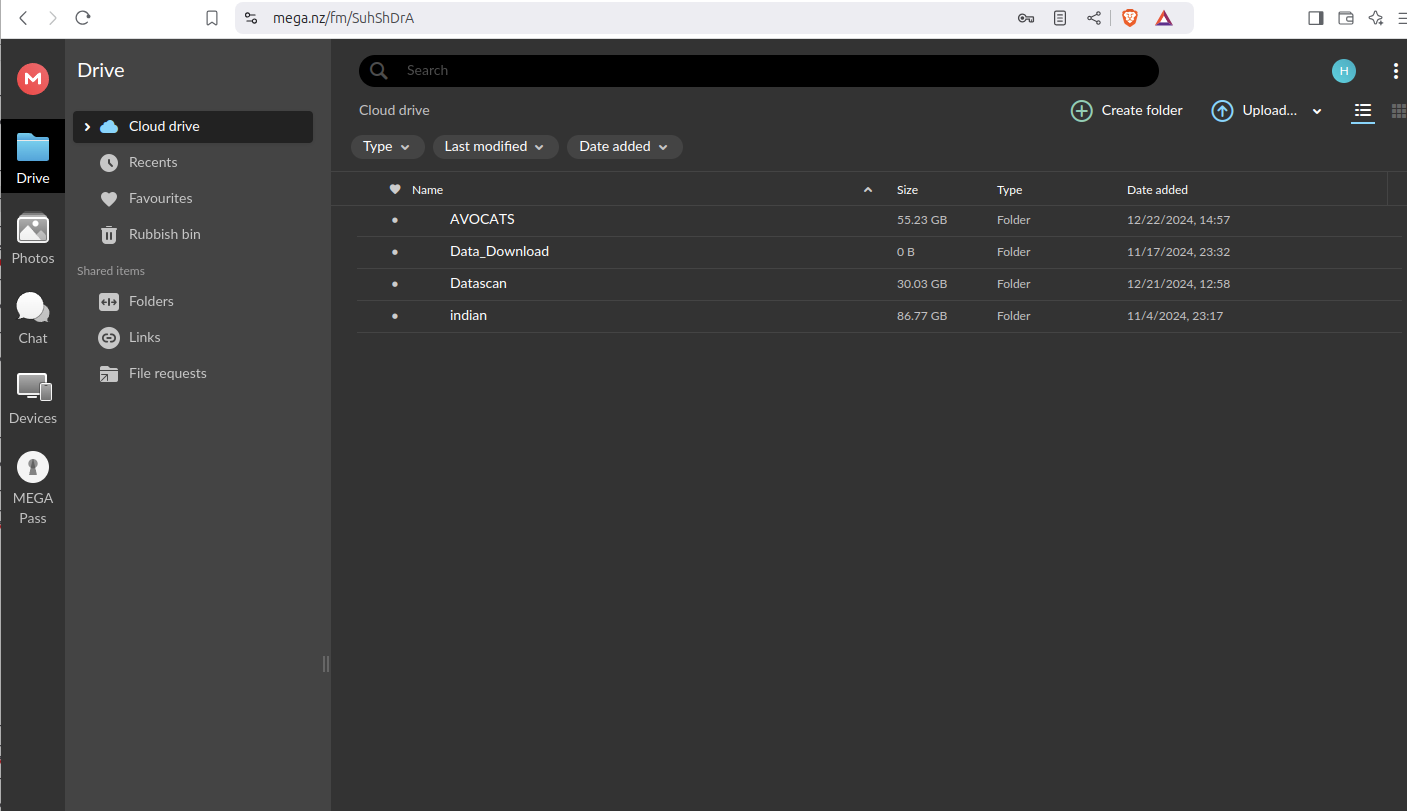
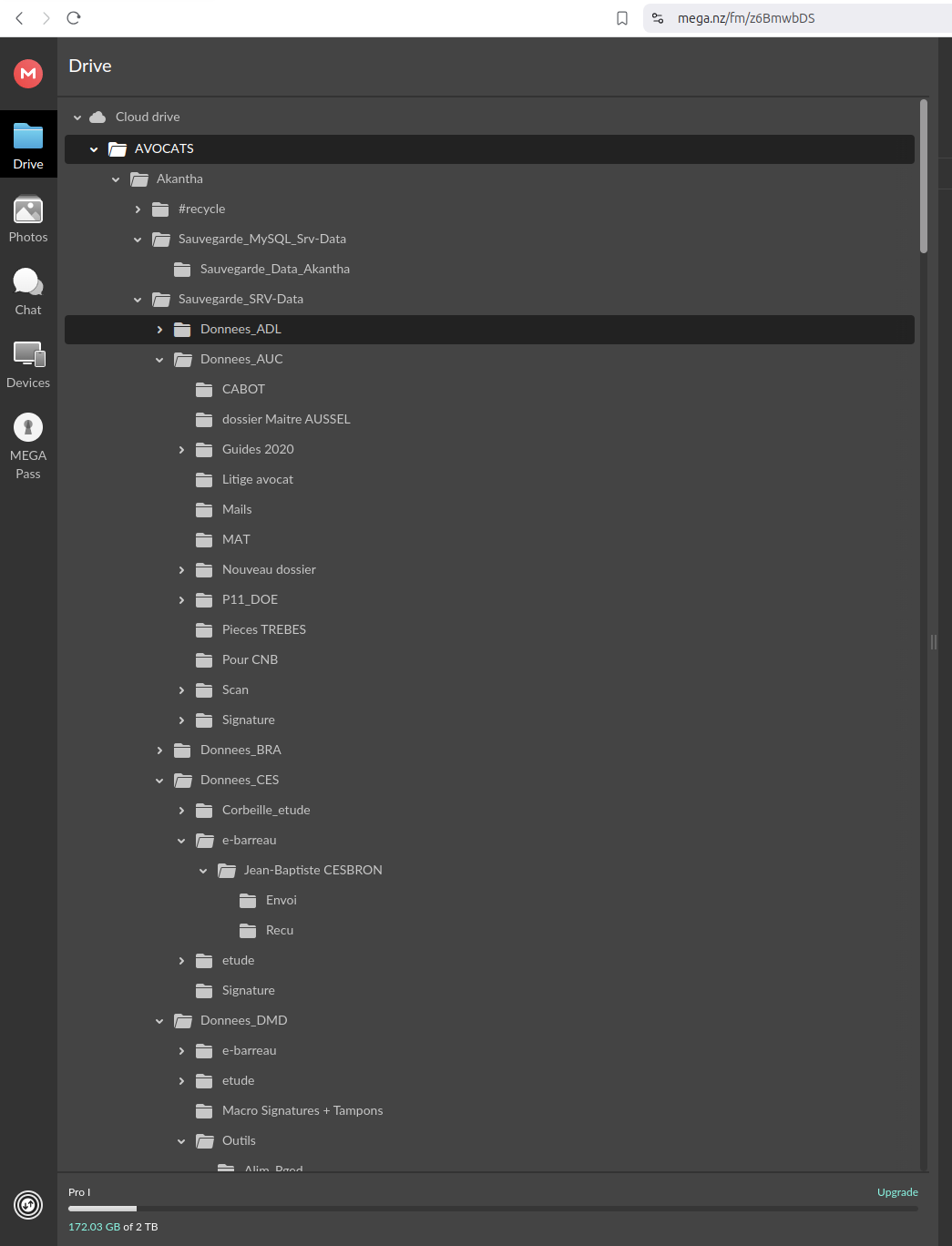
The attackers will create an anonymous MEGA account, using an @yopmail email.
sopajelessei-5488@yopmail.commega080mega@gmail.com
The main purpose is to hide activities through TOR or VPN, avoiding traffic detection. Additionally, they will install the MEGA client directly on the victim's machine, allowing data to be uploaded directly without needing to transfer it through an intermediary server.
Finally, after completing the data collection process, they will erase traces by deleting logs and removing tools like rclone and the MEGA client after use.

However, a weakness of this group is their OPSEC mistakes:
Not encrypting all logs
Exposed
bash_historyLeaving behind certificates, passwords, MEGA logs
Conclusion
The BlackLock ransomware campaign clearly demonstrates the increasing sophistication, organization, and danger of today's cybercriminal groups. This campaign is not a random attack. The group carries out every step in the kill chain, from reconnaissance, infiltration, escalation, data collection to encryption, and erasing traces.
The use of tools like rclone, the MEGA client, and leaving behind configuration files like .bash_history shows a high level of customization and flexibility in the attack.
Recommendations
- Enhance Initial Access Security
Disable RDP if not needed.
Limit IP access to VPN/RDP using a firewall.
Enable multi-factor authentication (MFA) for all remote access.
- Update Operating Systems
Patch vulnerabilities regularly (at least monthly).
Monitor CVEs related to VPN, firewall, and email servers.
- Protect Data and Back Up Regularly
Perform regular backups (daily/weekly).
Limit access to shared folders.
Monitor for large data download activities.
- Conduct Cybersecurity Awareness Training
Organize regular training sessions.
Simulate internal phishing attacks to test responses.
Regularly update IOC (Indicators of Compromise).
IOC
- Malicious IP
185.147.124.54
218.92.0.252
45.144.225.49
185.225.73.252
62.204.41.67
- Malicious Domain
api.anotherdomain[.]xyz






