Critical Security Flaws in Foxit PDF Reader Enable Code Execution Risks

Just a SOC Analyst ^^
In the Foxit PDF Reader and Editor tool, security researchers have discovered a long list of security vulnerabilities, with the most serious of them potentially leading to arbitrary code execution.
General Summary
Foxit PDF Reader is a free multilingual PDF tool that can create, view, edit, digitally sign, and print PDF files. Successfully exploiting the most serious vulnerability among these could allow arbitrary code execution in the case of a user who has successfully logged into the system.
Depending on the privileges associated with the user, an attacker could then install malicious programs; view, change, or delete data; or create new accounts with full user rights. Users with accounts granted fewer privileges on the system would be less affected than administrative users.
Impact Level
Affected Versions
2024.2.3.25184 and earlier versions for Windows.
2024.2.3.25184 and all previous 2024.x versions for Windows.
2023.3.0.23028 and all previous 2023.x versions for Windows.
13.1.3.22478 and all previous 13.x versions for Windows.
12.1.7.15526 and all previous 12.x versions for Windows.
11.2.10.53951 and earlier versions for Windows.
2024.2.3.64402 and all previous 2024.x versions for macOS.
2023.3.0.63083 and all previous 2023.x versions for macOS.
13.1.2.62201 and all previous 13.x versions for macOS.
12.1.5.55449 and all previous 12.x versions for macOS.
11.1.9.0524 and earlier versions for macOS.
2024.2.2.64388 and earlier versions for macOS.
Risk Level
For Government Agencies
Central Government Agencies: High Risk
Local Government Agencies: Medium Risk
Businesses
Large and Medium-sized Enterprises: High Risk
Small Enterprises: Medium Risk
Individual Users
- Low Risk
Technical Details
Below are descriptions of three serious security vulnerabilities found in Foxit PDF Reader:
Use-After-Free Vulnerability: The application can be attacked through a Use-After-Free vulnerability and crash when processing certain objects like checkboxes, Annotation objects, or AcroForms, which attackers can use to execute remote code or extract data. This occurs when the application uses an invalid pointer or a freed object without proper validation, errors in synchronizing reply note objects when processing annotations with JavaScript, or errors in updating font cache after deleting a page. These vulnerabilities are assigned CVE-2024-28888 and CVE-2024-7725.
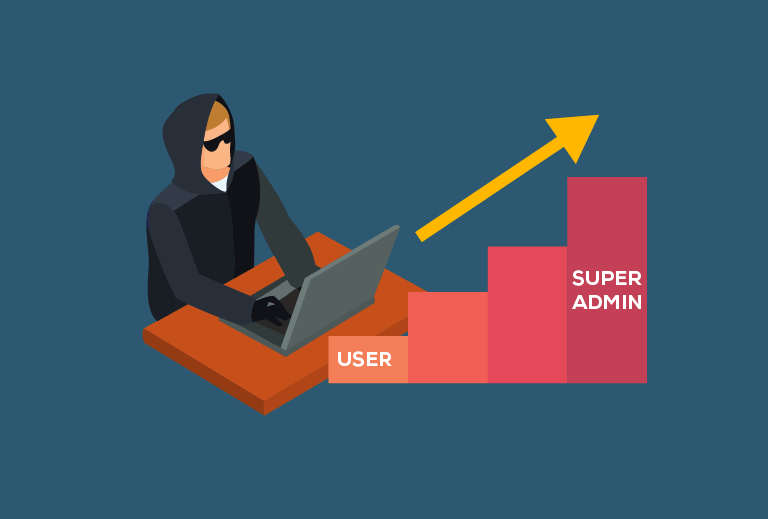
Privilege Escalation Vulnerability: The application can be exploited for privilege escalation during updates or plugin installations. Attackers can exploit this vulnerability to delete arbitrary files or execute arbitrary code to perform privilege escalation attacks. This occurs due to incorrect permission assignments on resources used by the update service, incomplete signature validation, weak randomness for temporary directory names during plugin installation, or improper DLL loading. The related CVE is CVE-2024-38393.
- Out-of-Bounds Read/Write Vulnerability: The application may encounter out-of-bounds read/write errors and crash when parsing PDF files or processing Annotation objects, providing an opportunity for hackers to execute remote code. This error occurs when the application reads or writes data beyond the limits of an object or buffer. This error does not yet have a CVE.
Additionally, information on less severe vulnerabilities is as follows:
Side-Loading Vulnerability: The application can be exploited by this vulnerability during updates. Attackers can replace the update file with a malicious file to run a malicious payload. This occurs when the application does not verify the integrity of the updater when running the update service. The related CVE is CVE-2024-41605.
Null Pointer Dereference Vulnerability: The application may encounter issues due to this vulnerability when scrolling through PDF files containing unusual StructTreeRoot entries in the dictionary. Attackers can exploit this to perform a Denial of Service attack. This error is due to using a null pointer without valid verification. This vulnerability does not yet have a CVE.
Privilege Escalation Vulnerability: The application may encounter issues when exploited for privilege escalation during deactivation or uninstallation, especially when the application is reinstalled without prior uninstallation. Attackers can exploit this to perform malicious actions. This error occurs due to incorrect permissions set for the
/usr/local/share/foxitdirectory, allowing low-privileged attackers to modify script files in the directory. This vulnerability does not yet have a CVE.
Recommendations
FPT Threat Intelligence recommends organizations and individuals take several measures to prevent these vulnerabilities:
Update Patches: Update the Foxit PDF Reader software patches as recommended by the company.
Apply the Principle of Least Privilege: All software should run under the rights of a non-administrative user to minimize the impact of a successful attack.
Use Intrusion Detection Tools: Deploy monitoring and alert systems for unusual activities.
Employee and User Awareness Training: Inform and educate users about threats from hypertext links in emails or attachments, especially from untrusted sources. Remind users not to access untrusted websites or follow links from unknown sources.






