Crypto-Stealing Malware Spreads on AppStore and Google Play
Just a SOC Analyst ^^
Cybersecurity experts have recently discovered a data-stealing trojan named SparkCat, which has been active on the AppStore and Google Play since at least March 2024. This is the first malware using optical recognition to appear on the AppStore. SparkCat utilizes machine learning to scan image libraries and steal screenshots containing cryptocurrency wallet recovery phrases. It can also find and extract other sensitive data in images, such as passwords.
Method of Spread
This malware is spreading through both infected legitimate apps and decoys, such as messaging apps, AI assistants, food delivery apps, and cryptocurrency-related applications. Some of these apps are currently available on official platforms like Google Play and AppStore. Data from Kaspersky also shows that software versions infected with malware are being distributed through unofficial sources. On Google Play, these apps have been downloaded over 242,000 times.
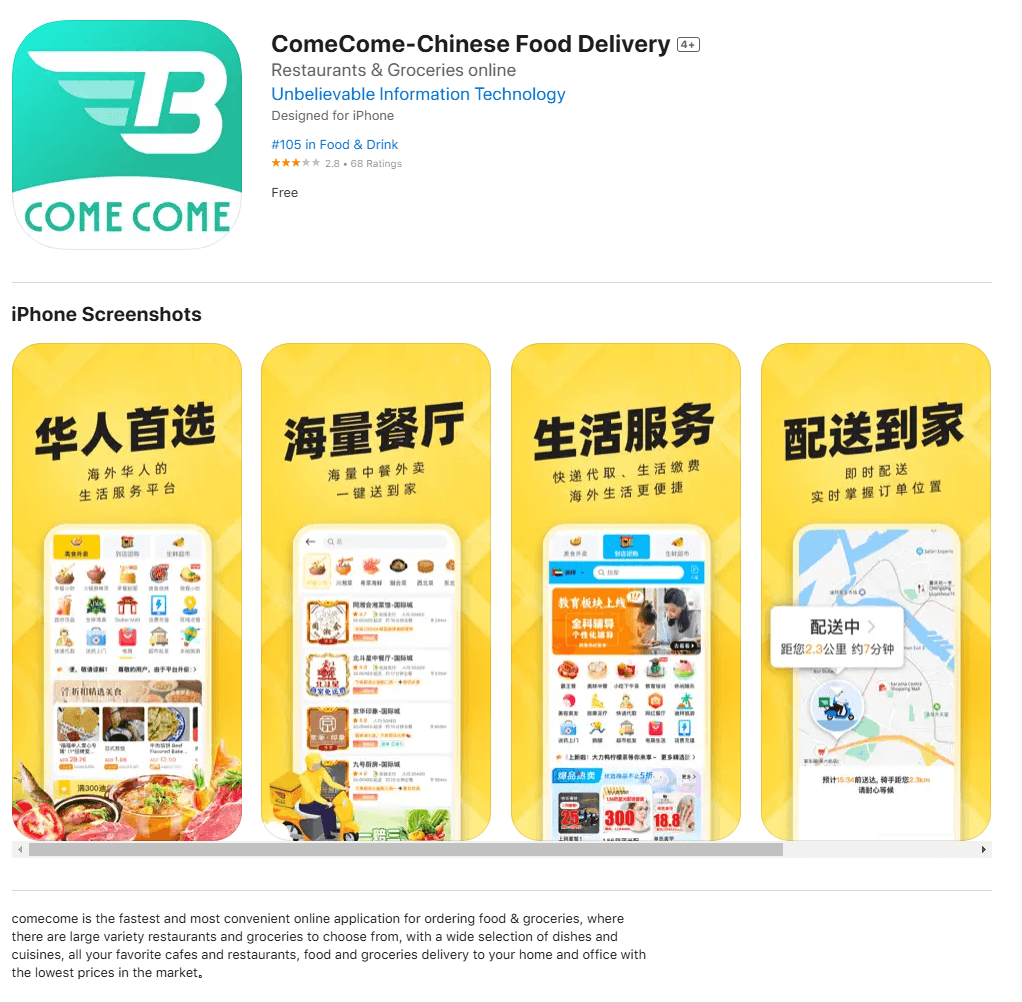
Figure 1. The ComeCome food delivery app for iOS infected with malware
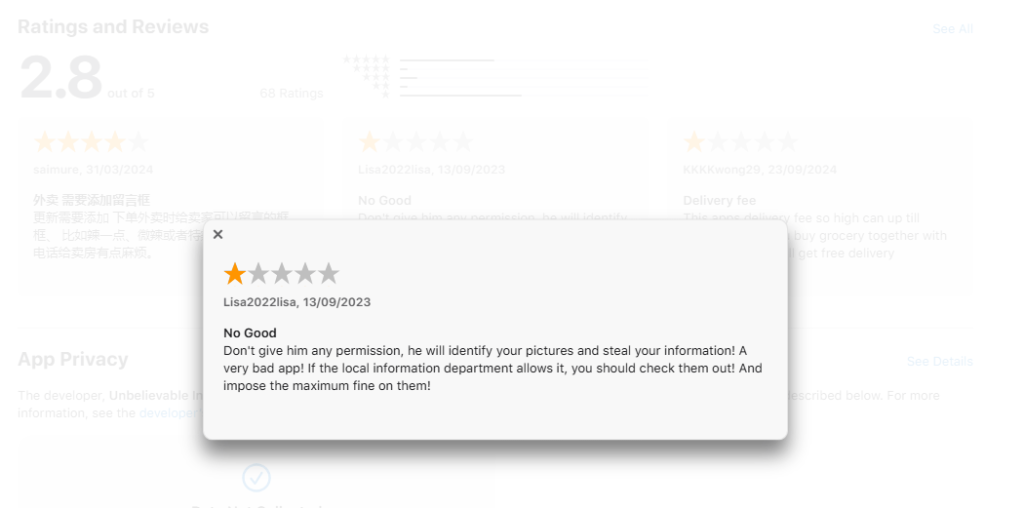
Figure 2. Negative user feedback about ComeCome
Attackers' Targets
The malware primarily targets users in the UAE and countries in Europe and Asia. SparkCat scans image libraries for keywords in multiple languages, including Chinese, Japanese, Korean, English, Czech, French, Italian, Polish, and Portuguese. However, experts believe victims may also come from other countries.
Figure 3. A fake messaging app on the AppStore related to SparkCat malware
How SparkCat Malware Works
After installation, the malware requests access to view photos in the user's phone library. It then analyzes text in the images using an optical character recognition (OCR) module. If the malware detects relevant keywords, it sends the images to the attacker. The main goal of the hackers is to find recovery phrases for cryptocurrency wallets. With this information, they can fully control the victim's wallet and steal funds. Besides stealing recovery phrases, the malware can extract other personal information from screenshots, such as messages and passwords.
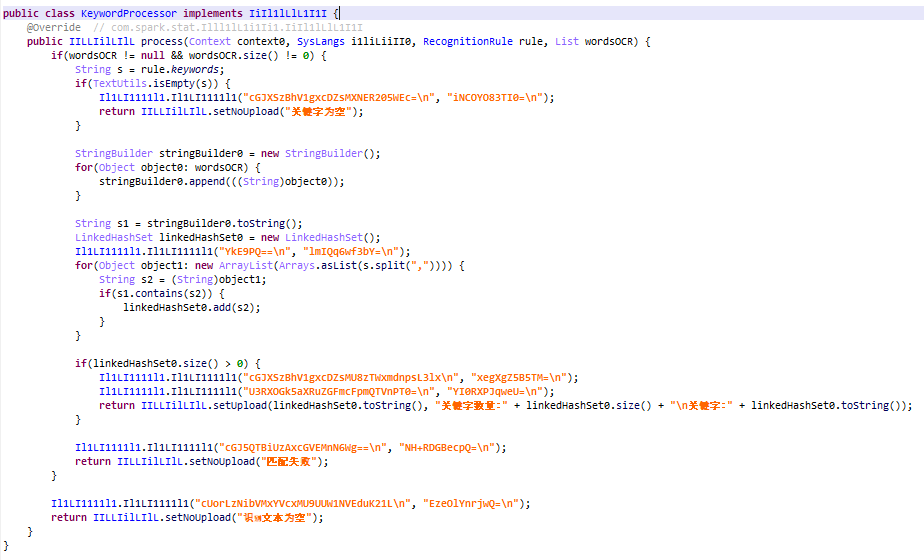
Figure 4. Searching for keywords after extracting text from images
Despite being rigorously screened by official app stores, infected apps still find their way into Google Play and the App Store. What makes this Trojan particularly dangerous is that there are no signs indicating hidden malware within the app. The permissions requested by the app seem necessary for its core functionality and appear harmless at first glance. This case has challenged the notion that iOS is unaffected by threats posed by malicious apps.
List of IOCs Related to SparkCat
Hashes of Infected Android Apps
| 0ff6a5a204c60ae5e2c919ac39898d4f | MD5 |
| 21bf5e05e53c0904b577b9d00588e0e7 | MD5 |
| a4a6d233c677deb862d284e1453eeafb | MD5 |
| 66b819e02776cb0b0f668d8f4f9a71fd | MD5 |
| f28f4fd4a72f7aab8430f8bc91e8acba | MD5 |
| 51cb671292eeea2cb2a9cc35f2913aa3 | MD5 |
| 00ed27c35b2c53d853fafe71e63339ed | MD5 |
| 7ac98ca66ed2f131049a41f4447702cd | MD5 |
| 6a49749e64eb735be32544eab5a6452d | MD5 |
| 10c9dcabf0a7ed8b8404cd6b56012ae4 | MD5 |
| 24db4778e905f12f011d13c7fb6cebde | MD5 |
| 4ee16c54b6c4299a5dfbc8cf91913ea3 | MD5 |
| a8cd933b1cb4a6cae3f486303b8ab20a | MD5 |
| ee714946a8af117338b08550febcd0a9 | MD5 |
| 0b4ae281936676451407959ec1745d93 | MD5 |
| f99252b23f42b9b054b7233930532fcd | MD5 |
| 21bf5e05e53c0904b577b9d00588e0e7 | MD5 |
| eea5800f12dd841b73e92d15e48b2b71 | MD5 |
iOS Framework
| 35fce37ae2b84a69ceb7bbd51163ca8a | MD5 |
| cd6b80de848893722fa11133cbacd052 | MD5 |
| 6a9c0474cc5e0b8a9b1e3baed5a26893 | MD5 |
| bbcbf5f3119648466c1300c3c51a1c77 | MD5 |
| fe175909ac6f3c1cce3bc8161808d8b7 | MD5 |
| 31ebf99e55617a6ca5ab8e77dfd75456 | MD5 |
| 02646d3192e3826dd3a71be43d8d2a9e | MD5 |
| 1e14de6de709e4bf0e954100f8b4796b | MD5 |
| 54ac7ae8ace37904dcd61f74a7ff0d42 | MD5 |
| caf92da1d0ff6f8251991d38a840fb4a | MD5 |
| db128221836b9c0175a249c7f567f620 | MD5 |
Trojan Configuration in GitLab
| hxxps://gitlab[.]com/group6815923/ai/-/raw/main/rel.json |
| hxxps://gitlab[.]com/group6815923/kz/-/raw/main/rel.json |
C2 Server
| api.firebaseo[.]com |
| api.aliyung[.]com |
| api.aliyung[.]org |
| uploads.99ai[.]world |
| socket.99ai[.]world |
| api.googleapps[.]top |
Photo Storage
hxxps://dmbucket102.s3.ap-northeast-1.amazonaws[.]com |
Recommendations
FPT Threat Intelligence recommends several measures for organizations and individuals to prevent this malware:
If you have installed an infected app, remove it immediately and avoid reinstalling until a patch is available.
Avoid storing screenshots containing sensitive information, such as cryptocurrency wallet recovery phrases, in your photo library. Store passwords, secure documents, and important data in dedicated security applications.
Use robust security solutions on all your devices to protect against malware threats.
User training and awareness: Organize cybersecurity training sessions to help identify phishing, scams, and social engineering attacks.
Check app permissions on your phone: Only install apps from official sources like Google Play or App Store and review permissions before granting them.
Regularly update your operating system and applications: Always use the latest versions to reduce the risk of exploitation by security vulnerabilities.






