Darcula PhaaS v3, the new phishing platform for cybercriminals

Overview of the platform
Darcula-suite is a major leap in the cybercrime world, removing barriers that allow attackers to target any brand with complex phishing campaigns. This is a Chinese PhaaS (Phishing-as-a-Service) platform developed by a Telegram user of the same name. It is very easy to use, so even a cybercriminal without technical knowledge can easily and quickly clone a brand's website and carry out phishing attacks. Since March 2024, Netcraft, a cybersecurity company specializing in phishing detection, has discovered and blocked over 90,000 domains, nearly 31,000 IP addresses, and more than 20,000 fraudulent websites related to Darcula.
Functions of Darcula-suite
In mid-February, a new version is expected to be released, making phishing even more dangerous. In this version, Darcula will use Puppeteer, allowing the creation of advanced phishing kits targeting any brand with just a click.
The platform will operate as follows:
First, copy and add the URL of the website you want to spoof into Darcula.
The platform will use automated tools like Puppeteer to extract HTML and other necessary content.
Select HTML parts to replace and insert into the phishing content.
Choose a template from the available phishing templates, such as: requesting payment information, requesting sensitive information (username, password…), etc.
Edit to fit and make it resemble the target brand's website interface.
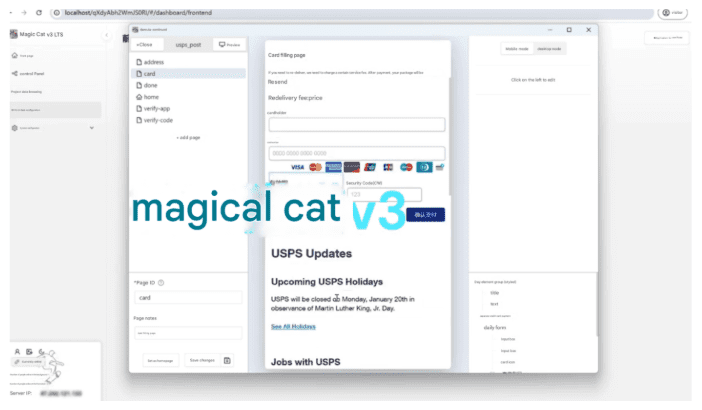
Activate the creation of separate pages for the initial bait page, enter address, card information, and two-factor authentication.
Export the phishing tool as a package named “.cat-page”.
Upload the package to the admin page of Darcula.
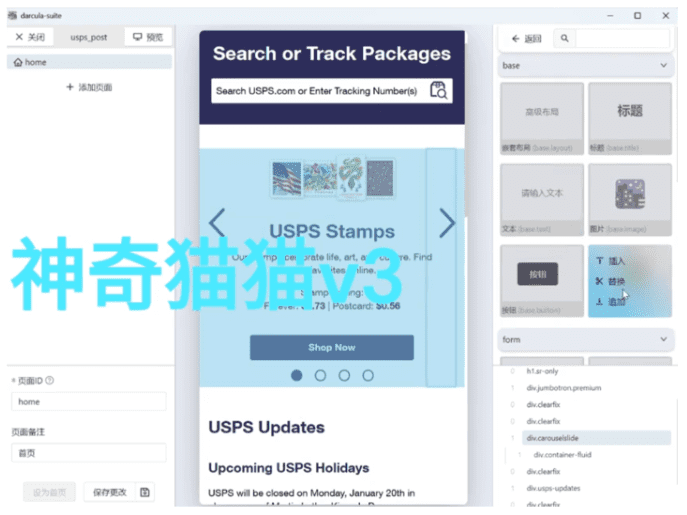
Using the Darcula-suite is very easy for carrying out a phishing campaign. The platform also provides dashboards to help scammers manage their campaigns.
The previous version of Darcula and its Telegram channels resemble criminal organizations using cat names and images. This trend continues with the creation of phishing tools targeting ".cat-page". The ".cat-page" package is uploaded to the platform where attackers manage and monitor active campaigns, and find and manage extracted data such as credit cards, login information, etc.
To set up the admin management page, the scammer runs a script that will execute Docker images from Darcula's Docker registry.
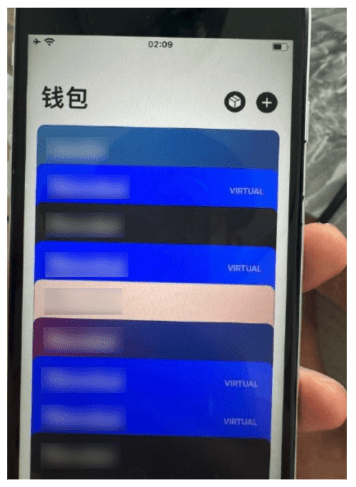
Once the card information is retrieved from the phishing campaign, the Darcula-suite allows users to create images of the victim's card that can be used to scan and add to a digital wallet. These cards are often added to smartphones and sold by Darcula criminals. This information has been verified by scammers publicly showing phones with up to 20 stolen cards added to each device in chat channels related to Darcula.
In the previous version of Darcula, Darcula v2, there were many features that made it easier for less technically skilled criminals to access. Additionally, it included complex measures to avoid detection, such as:
Each setup of Darcula can be hidden behind a unique subdirectory.
IP blocking to restrict access from cybersecurity companies.
User-agent blocking to prevent automated data scraping, such as by Google crawlers.
The client-side website is built using React, meaning it requires JavaScript to load, which needs to be monitored with a headless browser.
Cybercriminals are encouraged by Darcula to hide the real server through CDN providers like Cloudflare.
With the Darcula v2 version, it was already terrifying with pre-built brand templates, including over 200 brand templates from more than 100 countries. The third version, called Darcula-suite, launched in mid-February, introduces a new approach that allows phishing attacks to target any brand worldwide.
Prevent phishing
With the increase in criminals testing this platform since early February and the growing number of tools and platforms facilitating phishing, users need to be knowledgeable to prevent it. FPT Threat Intelligence offers the following recommendations:
Be cautious of messages and emails sent from untrustworthy or unidentifiable senders.
Carefully check links and websites, as these often contain spelling or syntax errors that make them look similar to legitimate website URLs.
Users should remain calm and cautious when receiving messages or emails with urgent content that demands immediate action.
Use phishing detection and prevention applications like Netcraft.






