FireScam Android spyware - poses a significant threat globally

Overview
Recently, there has been a reported attack campaign involving the FireScam Android malware disguised as Telegram Premium to steal data and control devices. Attackers use a fake app called "Telegram Premium" to steal information from victims' phones, with the ability to monitor, surveil, and collect sensitive data about the victims.
Key Findings
- FireScam is essentially Android malware disguised as a "Telegram Premium" app to steal data and control users' devices. This software is distributed through phishing websites hosted by GitHub.io and impersonates RuStore, a popular app store in Russia.

The malware uses a multi-stage infection process, starting with a dropper APK and performing extensive surveillance activities once installed. By exploiting the widespread use of popular apps and legitimate services like Firebase, FireScam illustrates the advanced tactics used by modern malware to evade detection, steal data, and maintain continuous control over compromised devices. It then steals sensitive information and sends the data to Firebase C2.

Attack Flow
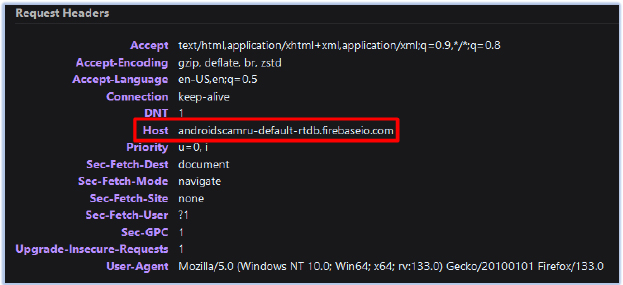
- An APK is downloaded from this phishing website, which then installs the FireScam malware disguised as the "Telegram Premium" app. The filtered data is temporarily stored in the Firebase Realtime Database at the URL "https[:]//androidscamru-default-rtdb[.]firebaseio[.]com" and is then deleted after it has the capability to filter and store important content in a separate private location.
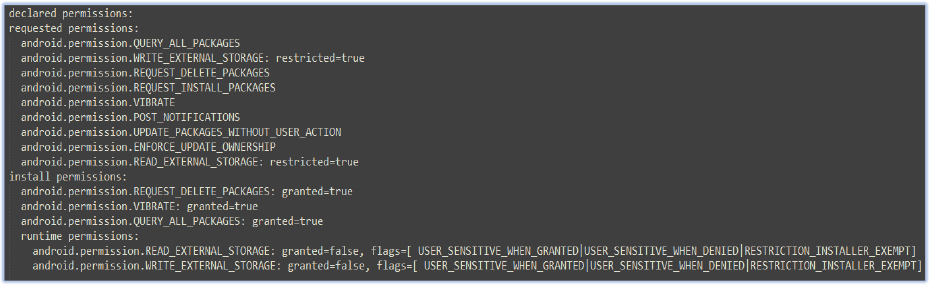
After installing this fake software, FireScam will request access permissions to the victim's phone. Additionally, there is a recorded .apk file: GetAppsRu.apk, which aims to encrypt strings in the APK and modify the app's control flow to make analysis more difficult. Some requests executed include:
Access contacts
Call logs
SMS messages
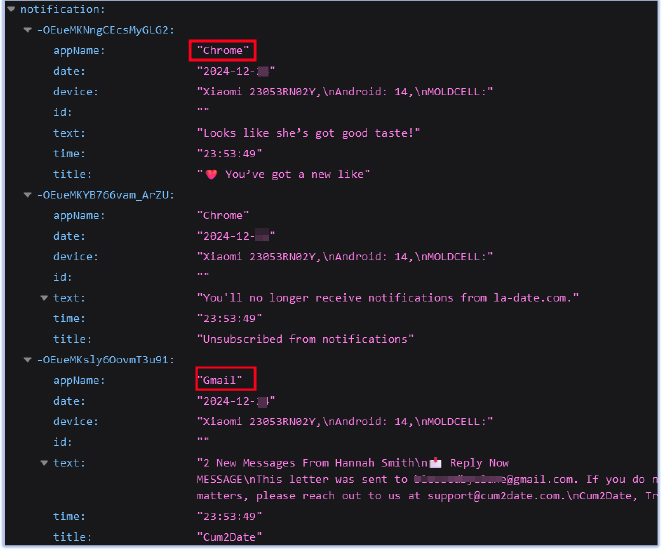
Monitor notifications
Overlay other apps
Once 'Telegram Premium' is granted the necessary permissions, it will steal sensitive information from the victim's phone.
Steal users' Telegram login information
Monitor online activities
Access and steal sensitive data, including financial information
Record device status changes like screen on/off events
Track e-commerce transactions, collecting sensitive financial data
Monitor messaging apps and filter captured messages
Track screen activity, uploading important events to the C2 server
It can listen to Firebase Cloud Messaging push notifications to trigger remote commands.
All the information collected will be sent to the attacker's control server through Firebase, a legitimate service, helping FireScam hide and avoid detection.
YARA Rules
rule FireScam_Malware_Indicators {
meta:
description = “Detects FireScam malware based on file hashes, URLs, and network indicators”
author = “Cyfirma Research”
last_modified = “2024-12-25”
strings:
// MD5 Hashes
$md5_1 = “5d21c52e6ea7769be45f10e82b973b1e” ascii
$md5_2 = “cae5a13c0b06de52d8379f4c61aece9c” ascii
// SHA256 Hashes
$sha256_1 = “b041ff57c477947dacd73036bf0dee7a0d6221275368af8b6dbbd5c1ab4e981b” ascii
$sha256_2 = “12305b2cacde34898f02bed0b12f580aff46531aa4ef28ae29b1bf164259e7d1” ascii
// URLs
$url_1 = “https://androidscamru-default-rtdb.firebaseio.com” ascii
$url_2 = “https://s-usc1b-nss-2100.firebaseio.com/.ws?ns=androidscamru-default-rtdb&v=5&ls=” ascii
$url_3 = “https://rustore-apk.github.io/telegram_premium/” ascii
condition:
// Match on either hash or URL indicators
($md5_1 or $md5_2 or $sha256_1 or $sha256_2) or
($url_1 or $url_2 or $url_3)
}
List of Recorded IOCs
- Hash Code
5d21c52e6ea7769be45f10e82b973b1e
b041ff57c477947dacd73036bf0dee7a0d6221275368af8b6dbbd5c1ab4e981b
cae5a13c0b06de52d8379f4c61aece9c
12305b2cacde34898f02bed0b12f580aff46531aa4ef28ae29b1bf164259e7d1
- Malicious URL
https://s-usc1b-nss-2100[.]firebaseio[.]com/.ws?ns=androidscamru-default-rtdb&v=5&ls=*
https[:]//androidscamru-default-rtdb[.]firebaseio[.]com
https[:]//rustore-apk[.]github[.]io/telegram_premium
- Malicious Domain
- s-usc1b-nss-2100[.]firebaseio[.]com
Recommendation
Only download apps from official sources like the Google Play Store
Avoid installing apps from unknown sources or through untrusted links
Carefully check the permissions that apps request before installing
Use reliable security software to scan and detect threats
Conclusion
FireScam's analysis reveals a complex and diverse threat targeting Android devices. Disguised as a fake Telegram Premium app, this malware uses advanced evasion techniques—abusing legitimate services like Firebase and leveraging phishing sites for distribution. Its ability to monitor various device activities, intercept sensitive information, and exfiltrate data to remote servers highlights its potential impact on user privacy and security.
As threats like FireScam continue to evolve, it is crucial for organizations to implement strong cybersecurity measures and proactive defense strategies. Users should be cautious when opening files from untrusted sources or clicking on unfamiliar links, especially those advertising suspicious software or content.






