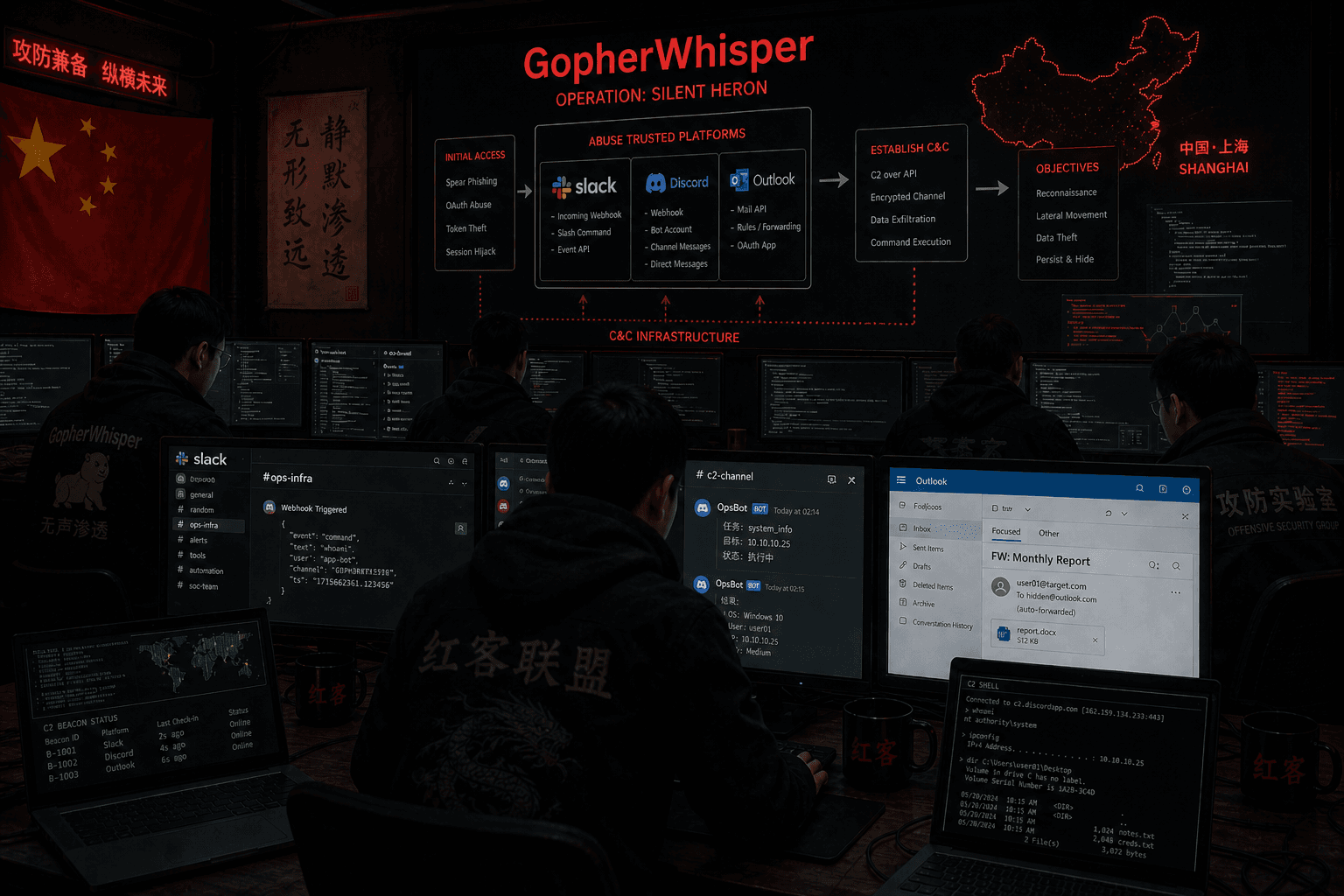
GopherWhisper: China-Aligned APT Weaponizes Slack, Discord, and Outlook as C2 Infrastructure
Executive Summary
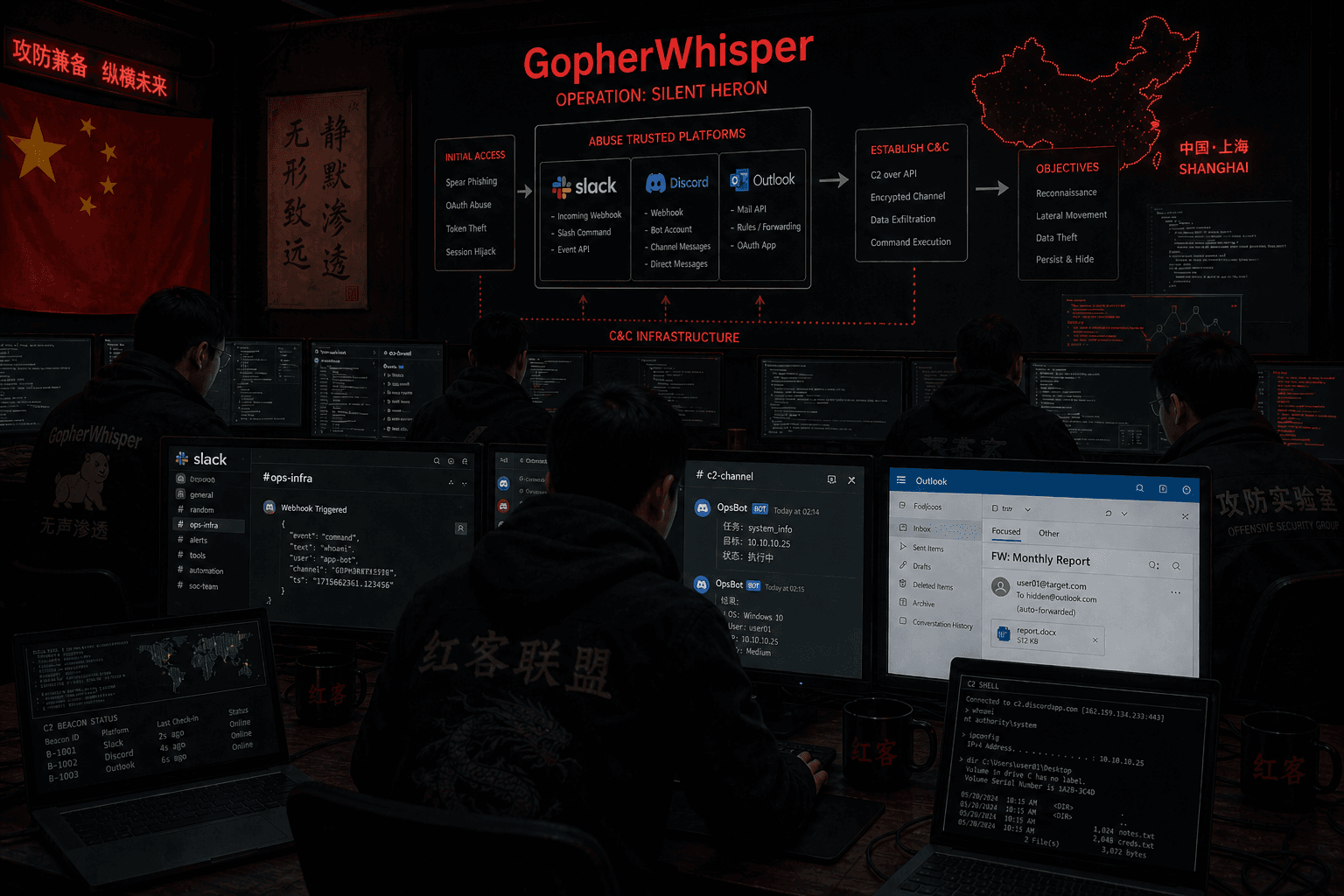
In January 2025, ESET Research uncovered a previously undocumented China-aligned APT group named GopherWhisper, actively targeting Mongolian government institutions. The group's defining characteristic is its use of legitimate SaaS platforms — Slack, Discord, Microsoft 365 Outlook, and file.io — as exclusive command-and-control (C2) infrastructure, blending malicious traffic into normal enterprise communication flows.
GopherWhisper's toolkit spans seven components, the majority written in Go: four backdoors (LaxGopher, RatGopher, BoxOfFriends, SSLORDoor), one injector (JabGopher), one exfiltration tool (CompactGopher), and one DLL loader (FriendDelivery). ESET confirmed at least 12 compromised systems within a single Mongolian government entity, with C2 traffic analysis suggesting dozens of additional, geographically unidentified victims.
Priority Action: Deploy detection rules for anomalous SaaS API connections (Slack, Discord, Graph API) originating from non-browser processes, and hunt for injected DLLs in svchost.exe instances with non-standard parent processes.
1. Background and Attribution
GopherWhisper was discovered in January 2025 when ESET researchers identified the LaxGopher backdoor on a Mongolian government system. Despite only being publicly disclosed in April 2026, the group is assessed to have been active since at least November 2023.
Attribution Basis — China Alignment:
Attribution to China is grounded in forensic metadata, not inference:
- Operational hours: The overwhelming majority of Slack and Discord C2 messages were sent during 08:00–17:00 UTC+8 (China Standard Time), consistent with standard government working hours.
- Slack metadata locale: The attacker-configured Slack workspace user had locale set to
zh-CN. - Operator machine fingerprint: Enumeration results returned to the Discord C2 channel revealed the operator was running a VMware-based virtual machine, with installation timestamps aligning to UTC+8.
- Novel toolset: No code overlap or TTP similarities with any previously known threat actor — warranting classification as a new group rather than a cluster of an existing one. Mongolia's geopolitical position — sandwiched between China and Russia — gives state-aligned espionage actors clear strategic interest in its government networks, despite the country's lower profile compared to Taiwanese or Southeast Asian targets.
2. Toolset — Technical Deep Dive
GopherWhisper implements a redundant multi-channel C2 strategy: each backdoor uses a different SaaS platform for command delivery. If one channel is blocked, operator access persists through the remaining ones.
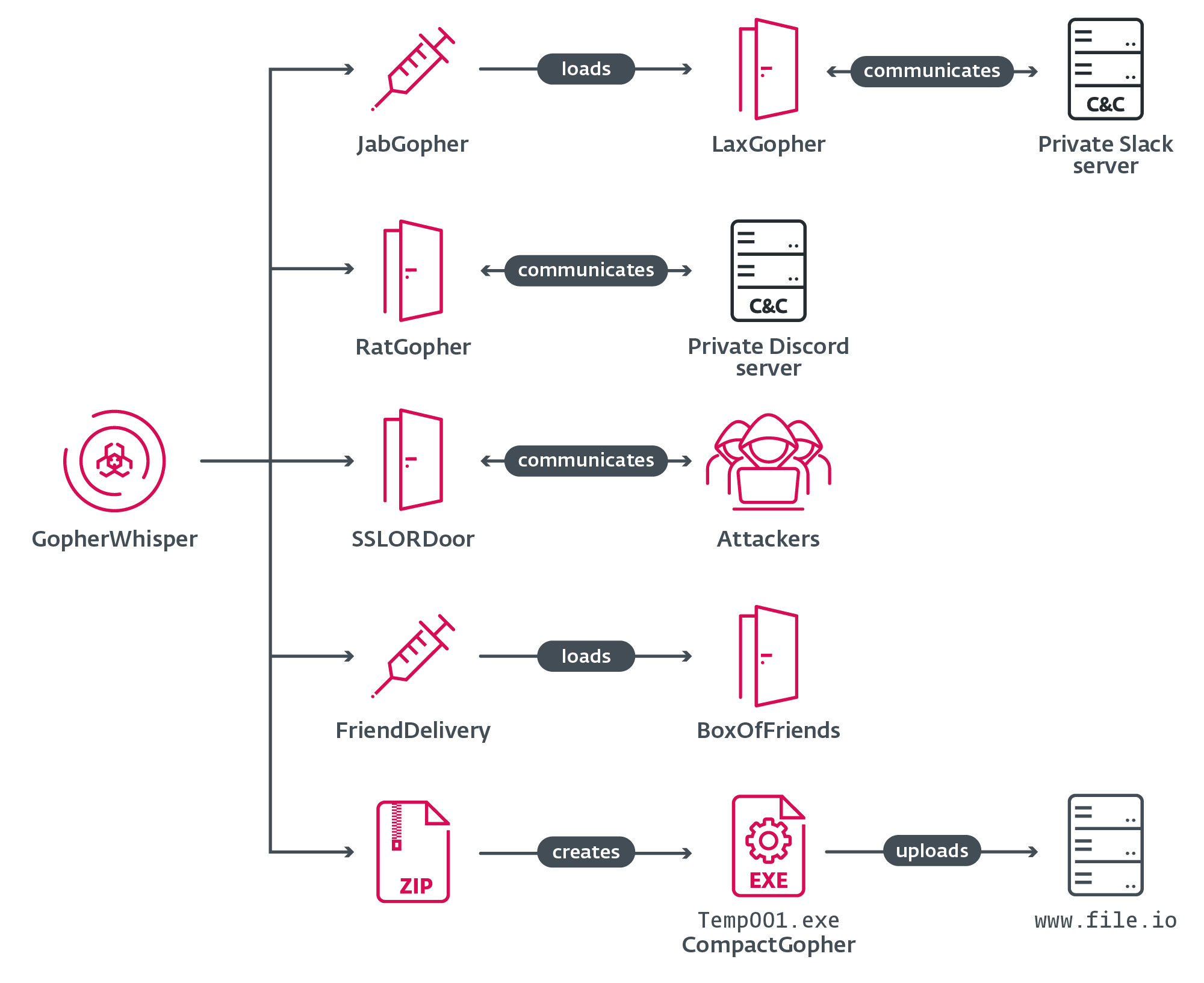 Figure 1: GopherWhisper toolset overview (Source: ESET Research)
Figure 1: GopherWhisper toolset overview (Source: ESET Research)
2.1. JabGopher — Injector
JabGopher initiates the execution chain by spawning a new svchost.exe process and injecting the LaxGopher payload into its memory space. Process injection into svchost.exe is a long-established evasion technique — the process runs on every Windows system by design and receives far less scrutiny than user-space processes.
LaxGopher is disguised as whisper.dll — the origin of the "Whisper" portion of the group's name.
2.2. LaxGopher — Slack-Based Backdoor
LaxGopher is a Go-based backdoor communicating with a private Slack workspace controlled by the attackers. Its operational loop:
- Connect to Slack API using a hardcoded token embedded in the binary
- Poll the configured Slack channel for operator commands
- Execute commands via
cmd.exe - Post execution results back to the same Slack channel
- Download additional payloads on operator instruction Observed LaxGopher commands focused on disk and file enumeration — consistent with post-access reconnaissance.
2.3. CompactGopher — Exfiltration Tool
Deployed by LaxGopher as a secondary payload, CompactGopher handles data staging and exfiltration:
- Filters files by extension:
.doc,.docx,.jpg,.xls,.xlsx,.txt,.pdf,.ppt,.pptx - Compresses targeted files into ZIP archives
- Encrypts archives with AES-CFB-128
- Automatically exfiltrates to file.io — a legitimate public file-sharing service Using file.io sidesteps blocklists targeting known C2 domains. Because file.io is a benign service, its traffic rarely triggers inspection.
2.4. RatGopher — Discord-Based Backdoor
RatGopher mirrors LaxGopher's functionality but routes C2 through a private Discord server:
- Connects via hardcoded Discord API token
- Receives commands from a configured Discord channel, executes, returns results
- Supports file upload/download via file.io Analysis of RatGopher's Discord channel also revealed Go source code, likely an early draft of the backdoor — the attackers were using the same Discord server for both development testing and live operations.
2.5. SSLORDoor — C++ Backdoor via Raw Socket
Unlike the Go-based backdoors, SSLORDoor is written in C++ and avoids SaaS platforms entirely. It uses OpenSSL BIO to communicate over raw sockets on port 443, camouflaging traffic within expected HTTPS flows without implementing full TLS termination in the conventional sense.
Capabilities: drive enumeration, file read/write/delete, command execution via C2 input.
2.6. FriendDelivery + BoxOfFriends — Email Draft C2
The most operationally sophisticated pair in the arsenal. FriendDelivery is a malicious DLL that loads and injects BoxOfFriends into memory. BoxOfFriends implements a dead drop C2 mechanism via Outlook:
- Uses Microsoft Graph API (Outlook mail REST API) with hardcoded credentials
- Does not send actual emails — instead creates and modifies draft messages in the mailbox
- Operator reads drafts to retrieve results; writes new drafts to issue commands The draft-based dead drop technique has been used by other APT groups (notably TURLA/Snake with Gmail drafts). GopherWhisper applies the same pattern to Outlook, well-suited to Microsoft 365 environments prevalent in government institutions.
The attacker's Outlook account is confirmed as barrantaya.1010@outlook[.]com, created on July 11, 2024 — exactly 11 days before the FriendDelivery DLL compilation timestamp of July 22, 2024.
3. C2 Traffic Analysis — A Critical Opsec Failure
One of the most significant intelligence gains in this investigation came from the attackers' own operational mistake. ESET extracted Slack and Discord API tokens from the analyzed binaries, gaining direct read access to the C2 channel history.
Root cause: GopherWhisper reused the same Slack and Discord servers for backdoor testing and live C2 operations — and never cleared the logs. This single opsec failure exposed thousands of internal communications.
Key intelligence recovered:
- Thousands of Slack and Discord C2 messages with full command history
- Operator machine metadata (VMware environment, installation timestamps)
- GitHub repositories used as development references
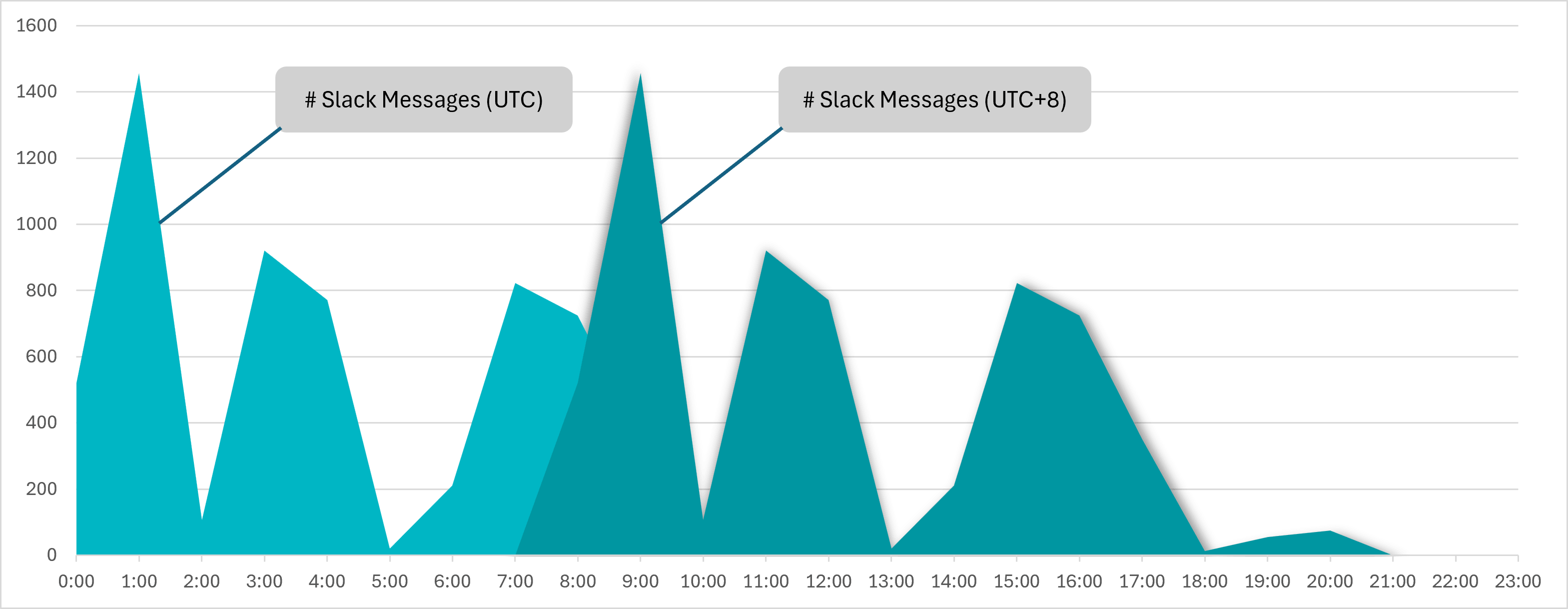 Figure 2: Slack message distribution by hour — clear 08:00–17:00 UTC+8 working hour pattern (Source: ESET Research)
Figure 2: Slack message distribution by hour — clear 08:00–17:00 UTC+8 working hour pattern (Source: ESET Research)
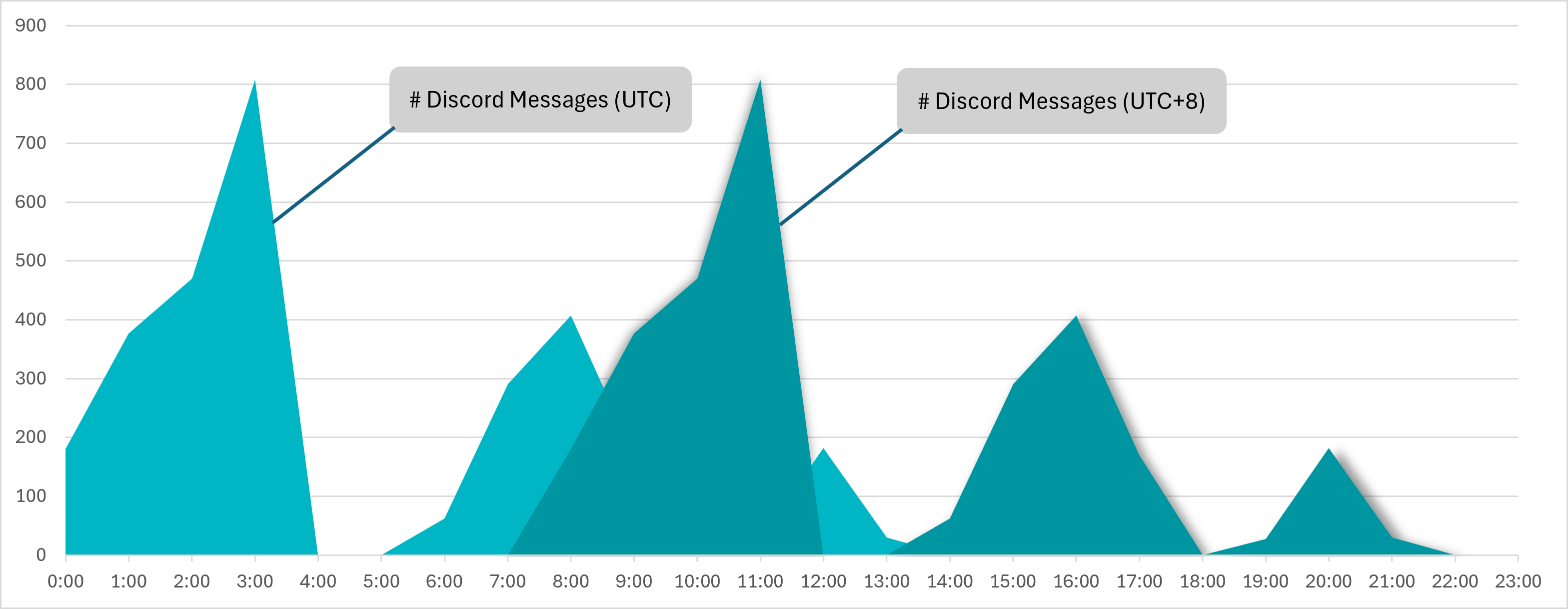 Figure 3: Discord message distribution mirrors the same working hour pattern (Source: ESET Research)
Figure 3: Discord message distribution mirrors the same working hour pattern (Source: ESET Research)
GitHub repositories referenced in C2 messages:
| Repository | Purpose |
|---|---|
github.com/kardianos/service |
Service daemon management for Go |
github.com/NHAS/stab |
Process injection (local and remote) for Go |
github.com/kirinlabs/utils |
Encryption and compression utilities for Go |
github.com/wumansgy/goEncrypt |
Encryption method implementations in Go |
These repositories indicate active toolset development, with a clear focus on injection, persistence, and cryptographic capabilities — suggesting future iterations of the toolkit may be more sophisticated.
4. Kill Chain and MITRE ATT&CK Mapping
Attack Flow
[Phase] [Technique] [Tool]
──────────────────────────────────────────────────────────────────────
Initial Access Unknown (initial vector not confirmed) —
Execution DLL Side-Loading JabGopher → whisper.dll
Persistence [NEEDS VERIFICATION] —
Defense Evasion Process Injection into svchost.exe JabGopher
SaaS C2 (blends with legitimate traffic) LaxGopher/RatGopher/BoxOfFriends
C2 Slack API (private workspace) LaxGopher
Discord API (private server) RatGopher
Outlook Draft via Microsoft Graph API BoxOfFriends
Raw Socket port 443 (OpenSSL BIO) SSLORDoor
Collection File filter by extension, ZIP + AES CompactGopher
Exfiltration Upload to file.io CompactGopher
MITRE ATT&CK Mapping
| Technique ID | Name | Associated Tool |
|---|---|---|
| T1055 | Process Injection | JabGopher |
| T1574.002 | DLL Side-Loading | JabGopher (whisper.dll) |
| T1071.001 | Application Layer Protocol: Web Protocols | LaxGopher, RatGopher, BoxOfFriends |
| T1102 | Web Service (Legitimate External Services) | Slack, Discord, Outlook, file.io |
| T1567.002 | Exfiltration to Cloud Storage | CompactGopher → file.io |
| T1560.001 | Archive Collected Data: Archive via Utility | CompactGopher (ZIP + AES-CFB-128) |
| T1027 | Obfuscated Files or Information | CompactGopher (encryption) |
| T1105 | Ingress Tool Transfer | LaxGopher (payload download) |
| T1087 | Account Discovery | LaxGopher/RatGopher (enumeration) |
| T1078 | Valid Accounts | BoxOfFriends (hardcoded Outlook credentials) |
5. Indicators of Compromise (IOC)
Note: Full IOC lists (hashes, IPs, domains) are published in the ESET white paper and GitHub repository. The following indicators have been publicly confirmed.
Network Indicators
# Slack API C2 endpoint (LaxGopher)
api.slack.com
# Discord API C2 endpoint (RatGopher)
discord.com/api/
# Microsoft Graph API C2 endpoint (BoxOfFriends)
graph.microsoft.com
# Exfiltration destination
file.io
# Attacker-controlled Outlook account
barrantaya.1010@outlook[.]com
Host-Based Indicators
# Side-loaded DLL filename
whisper.dll
# Injection target process
svchost.exe (new instance with non-standard parent process)
# File types targeted by CompactGopher
*.doc, *.docx, *.jpg, *.xls, *.xlsx, *.txt, *.pdf, *.ppt, *.pptx
Full IOC Repository
# ESET GitHub
https://github.com/eset/malware-ioc/tree/master/gopherwhisper
# ESET White Paper
https://web-assets.esetstatic.com/wls/en/papers/white-papers/gopherwhisper-burrow-full-malware.pdf
6. Detection Rules
KQL — Microsoft Sentinel (svchost SaaS API Connection)
// Detect svchost.exe connecting to Slack/Discord/Graph API
DeviceNetworkEvents
| where InitiatingProcessFileName == "svchost.exe"
| where RemoteUrl has_any (
"slack.com/api",
"discord.com/api",
"graph.microsoft.com",
"file.io"
)
| where InitiatingProcessParentFileName !in ("services.exe", "wininit.exe")
| project Timestamp, DeviceName, RemoteUrl, RemoteIP,
InitiatingProcessFileName, InitiatingProcessParentFileName,
InitiatingProcessCommandLine
| order by Timestamp desc
KQL — Suspicious DLL Side-Loading
// Detect whisper.dll load or non-system DLLs loaded into svchost
DeviceImageLoadEvents
| where FileName =~ "whisper.dll"
or (InitiatingProcessFileName == "svchost.exe"
and FolderPath !startswith "C:\\Windows\\System32"
and FolderPath !startswith "C:\\Windows\\SysWOW64")
| project Timestamp, DeviceName, FileName, FolderPath,
SHA256, InitiatingProcessFileName
Sigma — Non-Standard svchost.exe Parent Process
title: svchost.exe Spawned with Non-Standard Parent Process
id: gw-001-svchost-injection
status: experimental
description: |
Detects svchost.exe created by a non-standard parent process,
consistent with JabGopher injection technique used by GopherWhisper APT.
author: SOC Team
date: 2026-05-04
references:
- https://www.welivesecurity.com/en/eset-research/gopherwhisper-burrow-full-malware/
logsource:
category: process_creation
product: windows
detection:
selection:
Image|endswith: '\svchost.exe'
filter_legitimate:
ParentImage|endswith:
- '\services.exe'
- '\wininit.exe'
- '\MsMpEng.exe'
condition: selection and not filter_legitimate
falsepositives:
- Some legitimate software may spawn svchost directly — manual verification required
level: high
tags:
- attack.defense_evasion
- attack.t1055
- attack.t1574.002
Sigma — SaaS C2 from Non-Standard Processes
title: Suspicious SaaS API Connections from Non-Client Processes
id: gw-002-saas-c2
status: experimental
description: |
Detects connections to Slack/Discord/Graph API from processes
other than known legitimate clients — consistent with GopherWhisper C2 behavior.
author: SOC Team
date: 2026-05-04
references:
- https://www.welivesecurity.com/en/eset-research/gopherwhisper-burrow-full-malware/
logsource:
category: network_connection
product: windows
detection:
selection:
DestinationHostname|contains:
- 'slack.com'
- 'discord.com'
- 'graph.microsoft.com'
- 'file.io'
filter_legitimate_processes:
Image|contains:
- '\Slack\app-'
- '\Discord\app-'
- '\Microsoft\Teams'
- '\msedge.exe'
- '\chrome.exe'
- '\firefox.exe'
- '\outlook.exe'
condition: selection and not filter_legitimate_processes
falsepositives:
- Enterprise applications with legitimate Slack/Discord API integration — whitelist as needed
level: medium
tags:
- attack.command_and_control
- attack.t1102
- attack.t1071.001
7. Expert Assessment
The SaaS C2 Bet — Where It Works and Where It Breaks
GopherWhisper's core assumption is correct: most enterprise firewalls do not deep-inspect HTTPS traffic to tier-1 SaaS providers. Traffic to api.slack.com or graph.microsoft.com is indistinguishable from a business employee using Slack or Outlook — at the network perimeter level.
The weak point lies in process-to-network correlation. A svchost.exe instance connecting to api.slack.com — without a Slack client binary in the chain — is a clear behavioral anomaly for any SOC with adequate endpoint telemetry coverage. The problem is that most organizations have not built correlation rules linking process identity to destination. GopherWhisper exploits precisely this gap.
The "C3" (Civilian Command and Control) pattern — co-opting legitimate cloud infrastructure rather than operating dedicated servers — reduces infrastructure cost and dramatically increases the attacker's longevity before detection. Takedowns require coordination with commercial providers rather than simple server shutdown.
Comparing GopherWhisper to Known China-Aligned Groups
SaaS abuse is not novel. Evasive Panda leveraged cloud services for C2 in Operation CloudScout (2024), and email draft dead-drops have been documented across multiple APT families for years. What stands out about GopherWhisper for a newly identified group is the breadth of the toolkit: seven distinct tools, three independent C2 channels, and a clear Go-first development philosophy.
Go (Golang) is increasingly the language of choice for threat actors across sophistication tiers. The reasons are practical: single self-contained binaries, straightforward cross-compilation, and more complex reverse engineering compared to conventional C/C++ code. The GitHub repositories found in GopherWhisper's Slack channel suggest the group is actively building out injection and persistence capabilities — the current toolkit may represent an early-stage iteration.
Relevance to Southeast Asia
No confirmed GopherWhisper activity targeting Southeast Asian organizations has been reported. However, multiple China-aligned APT groups follow an expansion pattern — establishing operational capability against an initial target set before broadening scope. Government institutions, energy infrastructure, and telecommunications operators across Southeast Asia, including Vietnam, represent high-value espionage targets for China-state-aligned groups.
The more pressing unknown is the "dozens of other victims" referenced in ESET's C2 traffic analysis — with no geographic information currently available. Those victims could be anywhere.
8. Recommendations
Immediate (0–24h)
- Alert/block
svchost.execonnections toapi.slack.com,discord.com/api,graph.microsoft.comwhere parent process is notservices.exeorwininit.exe. - Hunt for
whisper.dllacross managed endpoints:Get-ChildItem -Path C:\ -Filter "whisper.dll" -Recurse -ErrorAction SilentlyContinue - Add
barrantaya.1010@outlook[.]comto email threat watchlist; addfile.ioto monitoring (evaluate full block based on business use).
Short-term (1–7 days)
- Deploy Sigma rules
gw-001andgw-002into SIEM. - Audit all Azure AD/Entra ID applications with Microsoft Graph API permissions — ensure only registered, legitimate applications hold mail read/write scopes.
- Ingest full IOC set from ESET GitHub:
https://github.com/eset/malware-ioc/tree/master/gopherwhisper - Review endpoint EDR telemetry for DLL loads into
svchost.exefrom non-system paths.
Long-term
- Evaluate TLS/SSL inspection for SaaS-bound endpoint traffic — with appropriate privacy and performance considerations.
- Build process-to-network baseline profiles for SaaS platforms in use; alert on deviation rather than blanket blocking.
- Incorporate SaaS C2 detection patterns into threat hunting runbooks — this attack vector will grow in frequency as perimeter defenses mature.
References
- ESET Research — "GopherWhisper: A burrow full of malware" (Apr 23, 2026) — https://www.welivesecurity.com/en/eset-research/gopherwhisper-burrow-full-malware/
- BleepingComputer — "New GopherWhisper APT group abuses Outlook, Slack, Discord for comms" — https://www.bleepingcomputer.com/news/security/new-gopherwhisper-apt-group-abuses-outlook-slack-discord-for-comms/
- The Hacker News — "China-Linked GopherWhisper Infects 12 Mongolian Government Systems" — https://thehackernews.com/2026/04/china-linked-gopherwhisper-infects-12.html
- ESET White Paper — https://web-assets.esetstatic.com/wls/en/papers/white-papers/gopherwhisper-burrow-full-malware.pdf
- ESET IOC Repository — https://github.com/eset/malware-ioc/tree/master/gopherwhisper