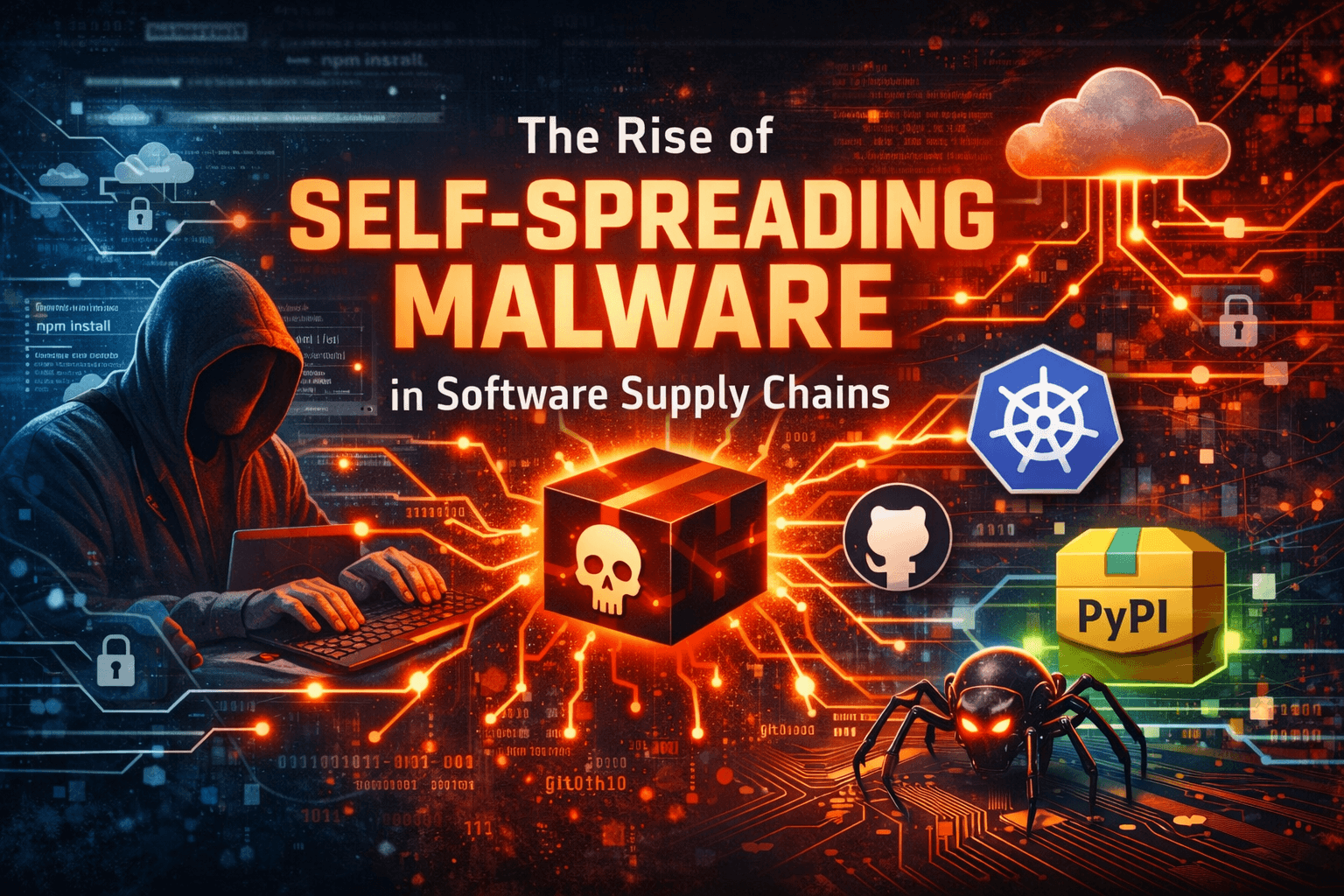
When open source becomes a weapon: The supply chain attack is spreading like a virus
Overview
From April 21 to 22, 2026, the supply chain attack campaign attributed to the TeamPCP group (or UNC6780) unexpectedly reactivated after a 26-day hiatus. This outbreak didn't stop at a single platform; it targeted three major ecosystems: npm, PyPI, and Docker Hub by compromising popular tools and libraries like Checkmarx KICS and Xinference, along with spreading the self-replicating malware CanisterSprawl.
The most dangerous aspect of this outbreak is the cascading compromise effect. The attackers didn't stop at inserting malware into the Checkmarx KICS security tool; they also exploited the auto-update feature of CI/CD systems like Dependabot to passively spread to downstream applications, notably the Bitwarden CLI. Any organization using these libraries and conducting CI/CD processes during April 21-22 is at risk of having cloud credentials (AWS, GCP), environment tokens, and source code siphoned. An urgent review of dependency update history and blocking connections to the campaign's command and control servers should be prioritized now.
Hacker profile
The supply chain attack campaign mentioned is not a one-off or opportunistic activity. According to assessments from cybersecurity intelligence units, particularly the Google Threat Intelligence Group (GTIG), the group behind it is internally identified as UNC6780, also known as TeamPCP.

Origin and operational model
TeamPCP has a background in self-propagating malware campaigns within the open-source ecosystem. A notable example is the Shai-Hulud worm event on npm in late 2025. Its presence in infected packages (e.g., Bitwarden CLI) indicates a high likelihood of being a deliberate continuation rather than random reuse.
Unlike traditional APT groups, TeamPCP doesn't just stop at infiltration; they also build an ecosystem to monetize stolen data, including controlled data leaks, selling access rights (access broker), and extorting businesses.
The group is believed to be linked to or share infrastructure with networks such as Vect, ShinyHunters, and CipherForce.
Technical expertise and operational tactics
TeamPCP employs a strategy known as "Ruthless Tool Reuse." The main components include:
SANDCLOCK: A tool specialized in stealing internal credentials
CanisterWorm: A worm capable of self-propagating within the package ecosystem (npm, PyPI)
A key distinction of the group is the use of Internet Computer Protocol (ICP) and deployment as a canister (decentralized container). The result is the absence of traditional C2 servers to dismantle, making it difficult to locate and disconnect the control infrastructure.
Additionally, they have the capability to collect a wide range of credentials, with over 40 different types, including: .env (environment variables), .npmrc (npm tokens), Terraform state/config, SSH private keys, Cloud credentials (AWS, GCP, Azure), and Kubernetes secrets..
MITRE ATT&CK attack chain
T1195.002 – Supply Chain Compromise (Software Dependencies)
T1059.006 – Python Execution
T1059.007 – JavaScript/Node.js Execution
T1552.001 – Credentials in Files
T1552.004 – Private Keys
T1528 – Steal Application Access Token
T1082 – System Information Discovery
T1119 – Automated Collection
T1041 – Exfiltration over C2 Channel
T1567 – Exfiltration over Web Services
Campaign Execution Process
Unlike typical data leaks, TeamPCP deployed a three-pronged attack matrix with independent yet synergistic vectors for cross-infection. This execution process is divided into separate cyberspaces with an extremely sophisticated attack structure.

Python ecosystem attack vector: The infection process through the Xinference library (with over 680,000 downloads) is divided into a series of closed steps to bypass EDR systems:
Initial infiltration: The attacker successfully steals the publish token of the Xinference package administrator on PyPI.
Injection: The malware, encoded in multi-layered Base64, is directly embedded into the core file __init__.py of versions 2.6.0, 2.6.1, and 2.6.2.
Hidden execution (Stage 1): When users import the library, Python activates the payload. The payload downloads a malicious "collector," initiating a detached subprocess. This prevents the original application from freezing, misleading security engineers into thinking the installation is proceeding normally.
Data Extraction (Stage 2): The subprocess begins a frantic scan of the local system: from .env files, .npmrc, Kubernetes/Docker configurations, API keys... It particularly focuses on scanning the AWS metadata service (accessing IP 169.254.169.254) to extract IAM access commands and IMDSv2 tokens. Everything is compressed into the file love.tar.gz.
Exfiltration: The malware cleans up traces, deletes temporary files, and uses cURL with a spoofed HTTP header X-QT-SR: 14 to push love.tar.gz to the launchpad whereisitat.lucyatemysuperbox[.]space.
Automatic propagation vector (CanisterSprawl worm via npm): This is the initial vector aimed at thoroughly sweeping the common attack surface.
Wide distribution: Create 16 fake library packages under publishers like @automagik or pgserve.
Activation via install hook: Exploit npm's postinstall feature. As soon as the developer downloads, a hidden bash command automatically triggers a process to scan memory and shell history.
Wide Harvesting: Apply a filter with over 40 regular expression (Regex) formats to scan for all types of private keys, security certificates, and cloud tokens.
Ecosystem Transfer: Uniquely, if the worm detects a PyPI publish token on the host, CanisterSprawl immediately morphs, using that token to infect Python library packages, transforming from an npm worm into a PyPI worm.
Peak of Blind Automation (Checkmarx - Bitwarden Service Chain): This is a classic cascading process (domino effect) exploiting the "vulnerability" of open code trust (Trusted Automation):
Tool Trap: The attacker took control of the official checkmarx/kics image repository on Docker Hub at 12:35 UTC on April 22. KICS, an infrastructure as code (IaC) scanner, inherently has access to read all sensitive files. The malware was injected, but KICS continued to function normally. However, it was turned into a double agent: collecting sensitive configuration certificates it scanned and sending unauthorized telemetry to audit.checkmarx[.]cx.
Passive Infection Cascade (The Cascade Effect): At that moment, Bitwarden's automated CI/CD update system (like Dependabot or equivalent) detected a "new update" for KICS (the malicious version) and naively pulled it into the internal build environment.
Chain Reaction: Bitwarden's pipeline used the compromised Docker KICS to build the package. As a result, the build of the Bitwarden CLI tool (version 2026.4.0) was infected. This malicious version was then directly pushed to npm with the payload titled "Shai-Hulud: The Third Coming," secretly extracting GitHub tokens from thousands of developers using Bitwarden CLI to the hacker's public repository. This is the deepest nightmare of the automated supply chain economy!
IOCs
Hash
971670c10eff28339a085ca50a600e35
3ee893ae46530b92e0d26435fb979d82 9b3257e45b27a6bbe4e240e41a3a306f
484067fd6232f7cdd7b664b33857fc2c
fe17e2ea4012d07d90ecb7793c1b0593a6138d25a393192263e751660ec3cd0
Network Indicators
hxxps://whereisitat.lucyatemysuperbox[.]space
hxxps://audit.checkmarx[.]cx/v1/telemetry
Expert opinion
This outbreak highlighted a concerning aspect of the risks in the "trusted automation" era. Bitwarden's infection due to the automated Dependabot process pulling a Docker Image with a backdoor in the KICS security tool demonstrates a sophisticated loop attack strategy. Hackers understand that directly stealing data can sometimes be more labor-intensive than controlling components already within the target's CI/CD chain. By inserting a backdoor into the "gatekeeper" like Checkmarx KICS, the malware easily bypasses all static code analysis (SAST) checks.
For organizations and businesses using CI/CD flows, this event serves as a wake-up call about the misuse of automated updates without parallel software version control. A third-party library updating to the latest version without going through sandbox security testing can turn an entire enterprise application against itself in just a 30-minute dwell time. Resources from machine learning frameworks like Xinference also highlight a new trend: supply chain hackers have begun targeting repositories at the forefront of the AI wave to access massive infrastructure on AWS or GCP.
Recommendations and Actions
Immediate Measures (0-24 hours): All systems running Xinference must be downgraded using the command pip install xinference==2.5.0 -y. System administrators using Bitwarden CLI, Checkmarx KICS, or platforms dependent on CanisterSprawl since April 21 must immediately isolate the execution environment to prevent spread. Configure the host file to block the C2 domains listed above. Most importantly, any credentials (including Cloud Tokens, SSH Keys, AWS IAM roles) that were loaded into environment variables during the malicious scan period must be considered compromised and must be revoked and rotated immediately.
Short-term Actions (1-7 days): Trace all network flows to IP 169.254.169.254 (AWS Metadata service) to detect malicious requests attempting to extract IMDSv2 tokens outside the default flow. Freeze automatic update flows (Dependabot, Renovate) on sensitive pipelines until the SOC team establishes pre-flight check procedures.
Long-term Improvements: Companies should establish a local private artifact registry for npm packages, PyPI, and Docker container images. Release authorization workflows must pass through an independent policy server to verify signatures before synchronization.
Refer to
New npm supply-chain attack self-spreads to steal auth tokens