PDF reader software or backdoor? Tropic Trooper's new campaign raises security concerns
Overview
A seemingly harmless PDF file. A familiar programming tool. But when Tropic Trooper is involved, everything can become a gateway for a sophisticated espionage campaign. This is what Zscaler ThreatLabz announced on March 12, 2026, regarding a new cyberattack campaign by the notorious APT group Tropic Trooper—a Chinese-speaking group that has been active since at least 2011. This campaign primarily targets Chinese-speaking users in Taiwan and has also spread to targets in South Korea and Japan.

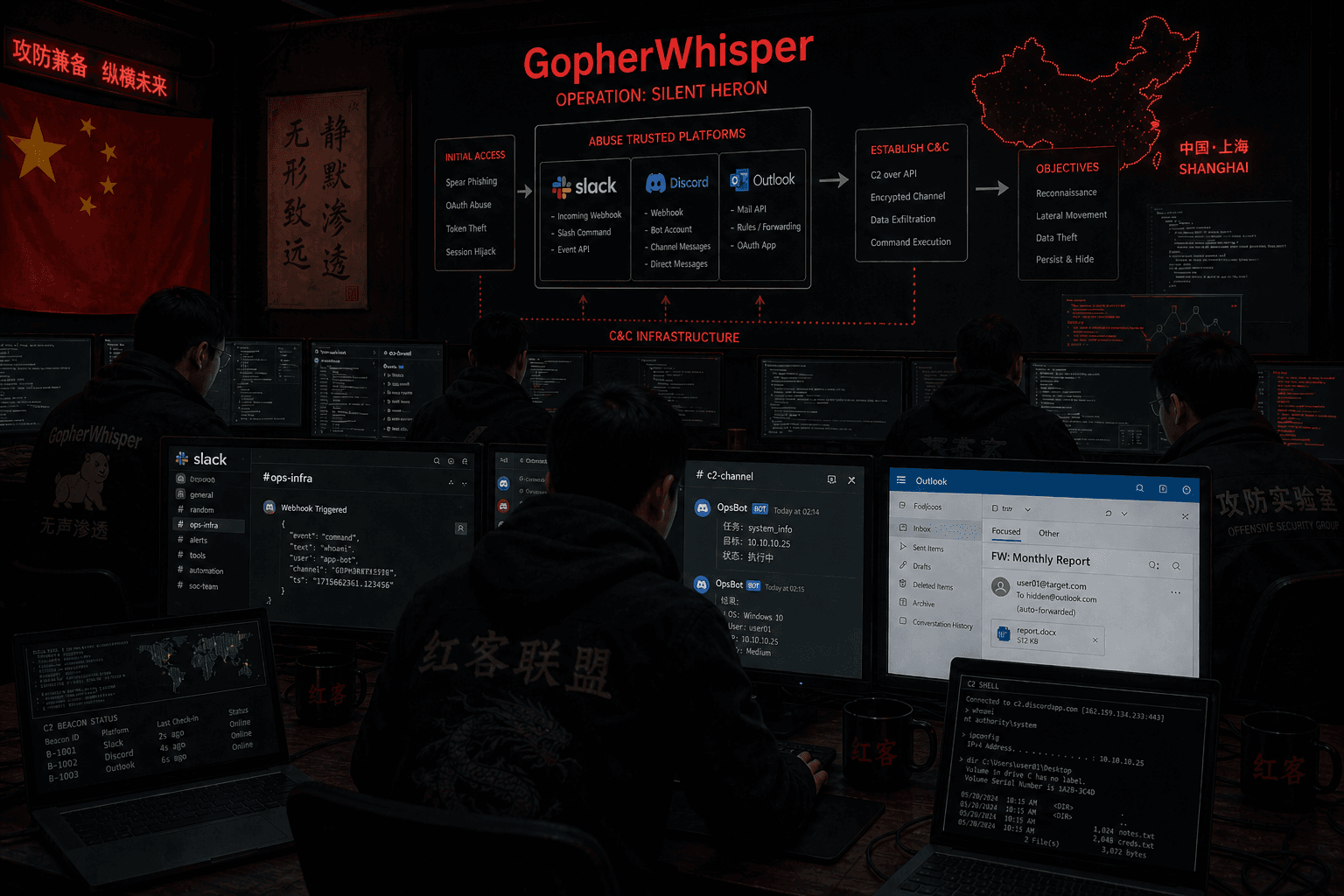
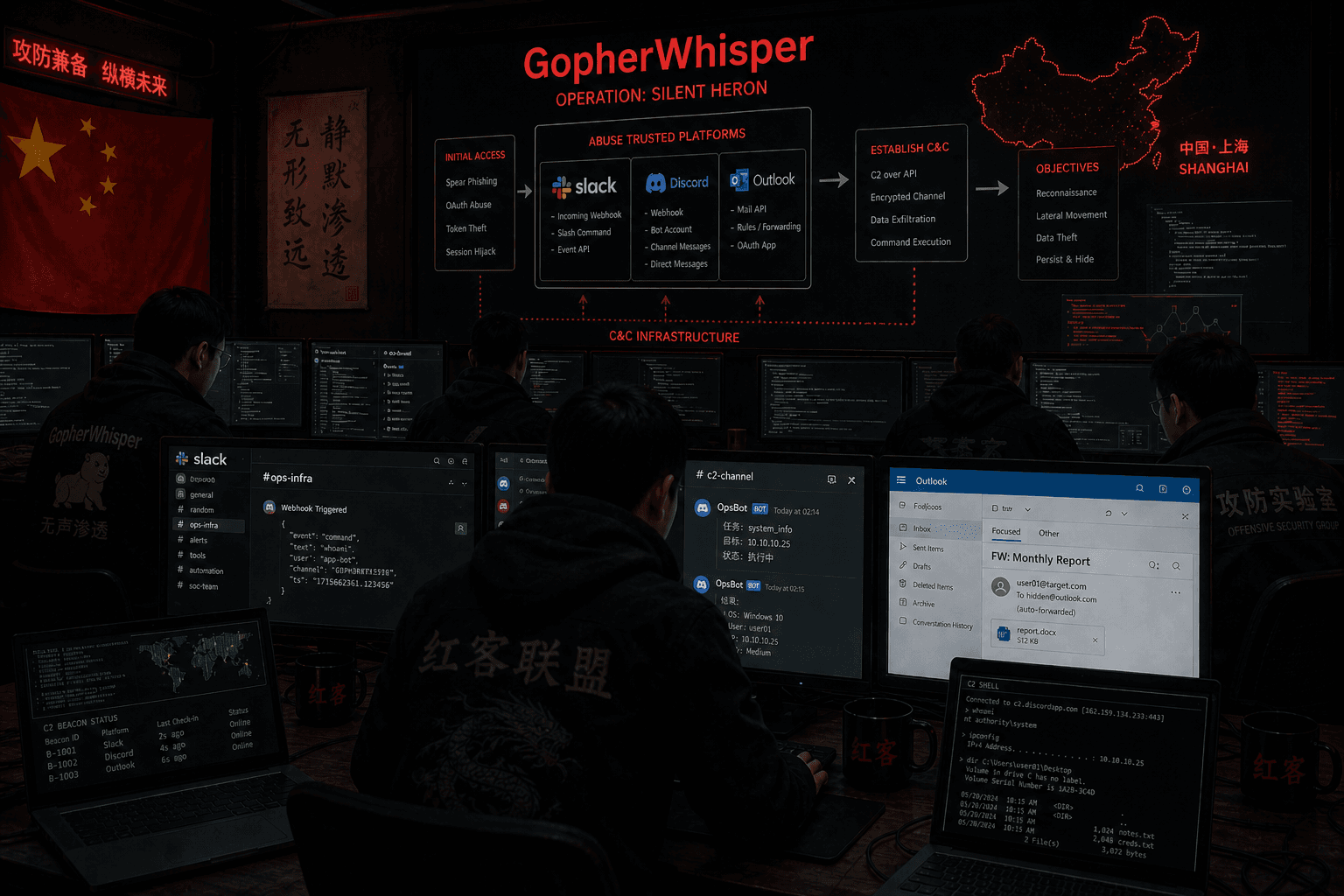
The standout difference lies in the change of tool strategy: instead of relying on familiar frameworks like Cobalt Strike or Mythic Merlin, the group has shifted to using AdaptixC2—an open-source platform, combined with a custom control mechanism through GitHub. This shift helps blend C2 traffic with legitimate activity, making detection significantly more difficult. Notably, the final stage of the attack chain leverages Visual Studio Code tunnels to establish interactive remote access, turning familiar development tools into an almost “invisible” backdoor channel within the enterprise environment.
Event timeline

Originating in late August 2025, a malware sample using Azure Functions as its control infrastructure was created (based on the metadata of the LNK file). Just a few days later, on August 28, 2025, an ISO file named Servicenow-BNM-Verify.iso was uploaded to the VirusTotal platform from Malaysia, indicating the initial distribution signs of the campaign.
By September 5, 2025, another sample with the same imphash—a crucial technical indicator linking the payloads—was uploaded from Singapore, reinforcing the theory of an expanding campaign in the region. After the "silent preparation" phase, the campaign officially emerged on March 12, 2026, when Zscaler ThreatLabz discovered a ZIP file containing military-themed lure documents designed to distribute malware related to Tropic Trooper.
In March 2026, ThreatLabz completed the analysis and confidently attributed the campaign to Tropic Trooper. By April 2026, the information spread widely when The Hacker News published details of the incident, leading to the extensive sharing of attack indicators (IOCs) within the cybersecurity community.
Who is Tropic Trooper?
Introduction
Before delving deeper into the analysis process, let's explore a bit about the hacker group behind this: Tropic Trooper. Tropic Trooper (also known as APT23, Earth Centaur, Pirate Panda) is a Chinese-speaking APT group active since at least 2011. This group is known for cyber espionage campaigns targeting government, military, technology, and telecommunications sectors in the Asia-Pacific region.

Targets of attack
Primary targets: Government, Defense, Telecommunications, High Technology. Main regions: Taiwan (primary focus), Japan, South Korea, Southeast Asia (expanding trend including Vietnam).
Key Stages
In the early stages, Tropic Trooper primarily targeted high-strategic-value objectives, especially Taiwan, which is considered the focal point of most of the group's campaigns. Additionally, countries like Japan and South Korea frequently appeared on the target list. From around 2017 onward, Tropic Trooper began to show significant technical upgrades. The group expanded its operations to other areas in Asia and adopted new techniques to enhance resilience and evasion capabilities.
Entering the 2020–2024 phase, Tropic Trooper began changing its approach. Instead of relying entirely on custom malware, the group increasingly utilized tools available within the operating system—a strategy often referred to as "living-off-the-land." By the 2025–2026 phase, Tropic Trooper had reached a completely different level. Recent campaigns show the group not only using legitimate tools but also directly leveraging cloud infrastructure and the developer ecosystem to conceal activities.
Attack chain

The attack chain of Tropic Trooper is designed in several distinct stages, with the ongoing goal of deceiving users, silently executing payloads, and maintaining long-term control without detection.
Phase 1 — Initial Access: Trojanized Software
Everything begins with a ZIP file containing military-themed documents in Chinese, accompanied by a cleverly disguised executable file. This file is actually a trojanized version of SumatraPDF, retaining legitimate indicators like certificates or PDB paths to bypass surface checks, but internally, it has been embedded with a malicious loader.
When users open the file, they believe they are simply reading a normal document—while the attack process has already commenced.

Phase 2 — Execution: TOSHIS Loader
After execution, the TOSHIS loader is activated in a more sophisticated manner than previous variants: instead of modifying the entry point, it hijacks the execution flow at the _security_init_cookie function, reducing the likelihood of detection.
The loader performs several consecutive steps:
Create encrypted strings in memory (C2, file paths, key)
Resolve APIs through hash instead of direct import
Download a decoy PDF file from the server and open it to distract the user
Simultaneously download the second-stage payload (shellcode) from the same source
Decrypt the payload using AES and execute it directly in memory (fileless)

Phase 3 — Command & Control via GitHub
The second-stage payload is an AdaptixC2 beacon, customized to use GitHub as the control channel.
Instead of communicating with a traditional C2 server, the malware:
Sends beacons through GitHub Issues
Retrieves commands by reading open issues
Executes commands after decryption
Uploads results back to the repository
Especially, the beacons are deleted just seconds later, making it nearly impossible to reconstruct the communication content during an investigation. The entire traffic appears as legitimate API calls to GitHub, posing a significant challenge for detection.

Phase 4 — Persistence
After establishing the control channel, the malware creates scheduled tasks to maintain access. The tasks are named to resemble system services (e.g., "MSDNSvc," "MicrosoftUDN") to blend in with legitimate processes. This allows the payload to automatically rerun periodically with elevated privileges, ensuring the attacker retains control even if the system restarts.
Phase 5 — Post-Exploitation: Remote Access via VS Code
When identifying a valuable target, the attacker deploys Visual Studio Code and sets up a tunnel for remote access.
Notably:
The tunnel uses legitimate Microsoft infrastructure
The HTTPS traffic appears completely normal
Provides a full interactive shell for the attacker
This turns VS Code into a "legitimate" backdoor, almost indistinguishable if relying solely on network traffic.
IOC
File Hashes
Tropic Trooper Campaign
ZIP (lure + trojanized SumatraPDF)
- SHA-256:
a4f2131eb497afe5f78d8d6e534df2b8d75c5b9b565c3ec17a323afe5355da26
- SHA-256:
Trojanized SumatraPDF (.exe)
- SHA-256:
47c7ce0e3816647b23bb180725c7233e505f61c35e7776d47fd448009e887857
- SHA-256:
Encrypted shellcode / Beacon (4d.dat)
- SHA-256:
aeec65bac035789073b567753284b64ce0b95bbae62cf79e1479714238af0eb7
- SHA-256:
AdaptixC2 Beacon DLL (decrypted)
- SHA-256:
7a95ce0b5f201d9880a6844a1db69aac7d1a0bf1c88f85989264caf6c82c6001
- SHA-256:
Azure Functions Malware (Related Activity)
ISO:
0ba328aeb0867def650694c5a43fdd47d719c6b3c55a845903646ccdbf3ec239LNK:
9e312214b44230c1cb5b6ec591245fd433c7030cb269a9b31f0ff4de621ff517Malicious DLL:
b03a2c0d282cbbddfcf6e7dda0b4b55494f4a5c0b17c30cd586f5480efca2c17Legit binary (sideload victim):
b778d76671b95df29e15a0af4d604917bfba085f7b04e0ce5d6d0615017e79dbShellcode:
550c27fd8dc810df2056f1ec4a749a94ab4befc8843ba913c5f1197ef381a0a5Final DLL:
c0fc5ec77d0aa03516048349dddb3aa74f92cfe20d4bca46205f40ab0e728645Related sample (Singapore)
SHA-256:
28e85fd3546c8ad6fb2aef37b4372cc4775ea8435687b4e6879e96da5009d60aImphash:
B74596632C4C9B3A853E51964E96FC32
Network Indicators
Infrastructure
- Staging IP:
158.247.193[.]100
Command & Control
GitHub C2 (AdaptixC2)
api.github.com/repos/cvaS23uchsahs/rss/issues
Cobalt Strike C2
47.76.236[.]58:4430stg.lsmartv[.]com:8443
Cloud-based C2
Azure Functions
Host:
logsapi.azurewebsites[.]netEndpoint:
/api/logs
Tooling / Staging
bashupload[.]app/6e1lhcbashupload[.]app/zgel2a.bin
Living-off-the-land tooling
Visual Studio Code tunnel download
code.visualstudio.com/...cli-win32-x64
Host-Based Indicators
Persistence (Scheduled Tasks)
\MSDNSvc\MicrosoftUDN
Suspicious File Paths
C:\Users\Public\Documents\dsn.exeC:\Users\Public\Documents\MicrosoftCompilers.exeC:\Users\Public\Documents\2.library-ms
Artifacts
Cobalt Strike Watermark:
520EntryShell AES Key:
afkngaikfaf
MITRE ATT&CK Matrix
Tactic | ID | Technique |
Initial Access | T1190 | Exploit public-facing application |
T1566.001 | Spear Phishing Attachment | |
Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
T1059.003 | Command and Scripting Interpreter: Windows Command Shell | |
T1569.002 | System Services: Service Execution | |
Persistence | T1543.003 | Create or Modify System Process: Windows Service |
T1574.002 | Hijack Execution Flow: DLL Side-Loading | |
T1505.003 | Server Software Component: Web Shell | |
Defense Evasion | T1140 | Deobfuscate/Decode Files or Information |
T1070.001 | Indicator Removal on Host: Clear Windows Event Logs | |
T1027.002 | Obfuscated Files or Information: Software Packing | |
T1218.011 | Signed Binary Proxy Execution: Rundll32 | |
T1036.005 | Masquerading: Match Legitimate Name or Location | |
Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
T1552.002 | OS Credential Dumping: Credentials in Registry | |
Lateral Movement | T1021.002 | Remote Services: SMB/Windows Admin Shares |
Discovery | T1087.002 | Account Discovery: Domain Account |
T1482 | Domain Trust Discovery | |
T1083 | File and Directory Discovery | |
Collection | T1005 | Data from Local System |
Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
T1095 | Non-Application Layer Protocol | |
T1090.001 | Proxy: Internal Proxy | |
Exfiltration | T1567.002 | Exfiltration to Cloud Storage |
T1020 | Automated Exfiltration | |
T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | |
T1203 | Exploitation for Client Execution | |
T1564.001 | Hide Artifacts: Hidden Files and Directories | |
T1518.001 | Software Discovery | |
T1082 | System Information Discovery | |
T1016 | System Network Configuration Discovery | |
T1049 | System Network Connections Discovery | |
T1033 | System Owner/User Discovery | |
T1204.002 | User Execution: Malicious File | |
T1078.003 | Valid Accounts: Local Accounts |
Expert opinion
This campaign shows Tropic Trooper actively reducing detection capabilities by switching from Cobalt Strike to AdaptixC2 combined with GitHub as C2. Using GitHub Issues makes blocking nearly impossible, forcing the blue team to focus on detecting abnormal behavior instead of network signatures. The quick beacon removal mechanism and lack of session key storage increase forensic difficulty, while leveraging Visual Studio Code tunnels turns legitimate tools into "invisible" remote access channels. Simultaneously, the trend of using Azure Functions as C2 indicates a strong shift towards a cloud-based model by the attacker. Overall, this is a typical "blend in" strategy: utilizing legitimate infrastructure and tools to conceal activities, making detection increasingly reliant on behavioral analysis rather than traditional technical indicators.
Recommendation
Immediate (0–24h) - Quick response
Within the first 24 hours, the goal is to determine if the system shows signs of compromise:
Scan all IOCs (hash, IP, domain) on endpoints, EDR, and SIEM for quick detection of compromise indicators.
Check persistence by reviewing scheduled tasks, especially those with deceptive names like \MSDNSvc or \MicrosoftUDN.
Behavioral process analysis:
Identify unusual processes spawning Visual Studio Code (code.exe).
Monitor processes calling the GitHub API, especially if originating from directories like C:\Users\Public\Documents.
Block known malicious infrastructure:
- Block IP staging 158.247.193[.]100 on the firewall/proxy.
Quick triage endpoint:
Find executable files in public/writable directories
Prioritize files of unknown origin or those masquerading as legitimate software
Short-term (1–7 days) — Threat Hunting & Hardening
Behavioral threat hunting
Trojanized software
Find processes related to SumatraPDF or other popular software.
Verify if the digital signature (code signing) is valid.
VS Code tunnel abuse
Query processes with command lines containing code tunnel or tunnel login.
Identify the execution source (user, host, parent process).
Scheduled task disguise
Detect tasks with names similar to Microsoft/Windows
Prioritize tasks created recently or by frequent users
Network anomaly
Monitor requests to the GitHub API (api.github.com) from processes that are not browsers or IDEs.
Detect unusual user-agents (e.g., curl) from unfamiliar processes.
Check cloud and API traffic
Review outbound traffic to:
*.azurewebsites.net
Endpoints related to Azure Functions
Prioritize:
Request POST
Payload encrypted or unusual in size/frequency
Long-term — Sustainable Defense
Execution Control
Implement application allowlisting for writable directories
Prevent execution from:
C:\Users\Public\
%TEMP%, %APPDATA%
Control developer tools
Limit the use of Visual Studio Code tunnels:
Allow only on designated developer machines
Monitor login/initialization tunnel behavior
Refer
Tropic Trooper Uses Trojanized SumatraPDF and GitHub to Deploy AdaptixC2
Tropic Trooper: AdaptixC2 + Custom Beacon | ThreatLabz