Hackers Distribute Malicious Microsoft Teams to Gain Remote Access
Security researchers at Blackpoint have recently warned about a new malware distribution campaign, where hackers use sponsored Google ads or SEO - Search Engine Optimization tricks to lure users into downloading a fake installation version of Microsoft Teams.
Detailed Information
The goal of this fake Microsoft Teams distribution campaign is to spread the Oyster backdoor (also known as Broomstick). By modifying the original installer from the publisher, hackers have successfully trojanized Microsoft Teams, turning it into a tool to widely distribute the backdoor, with the number of infected victims increasing exponentially.

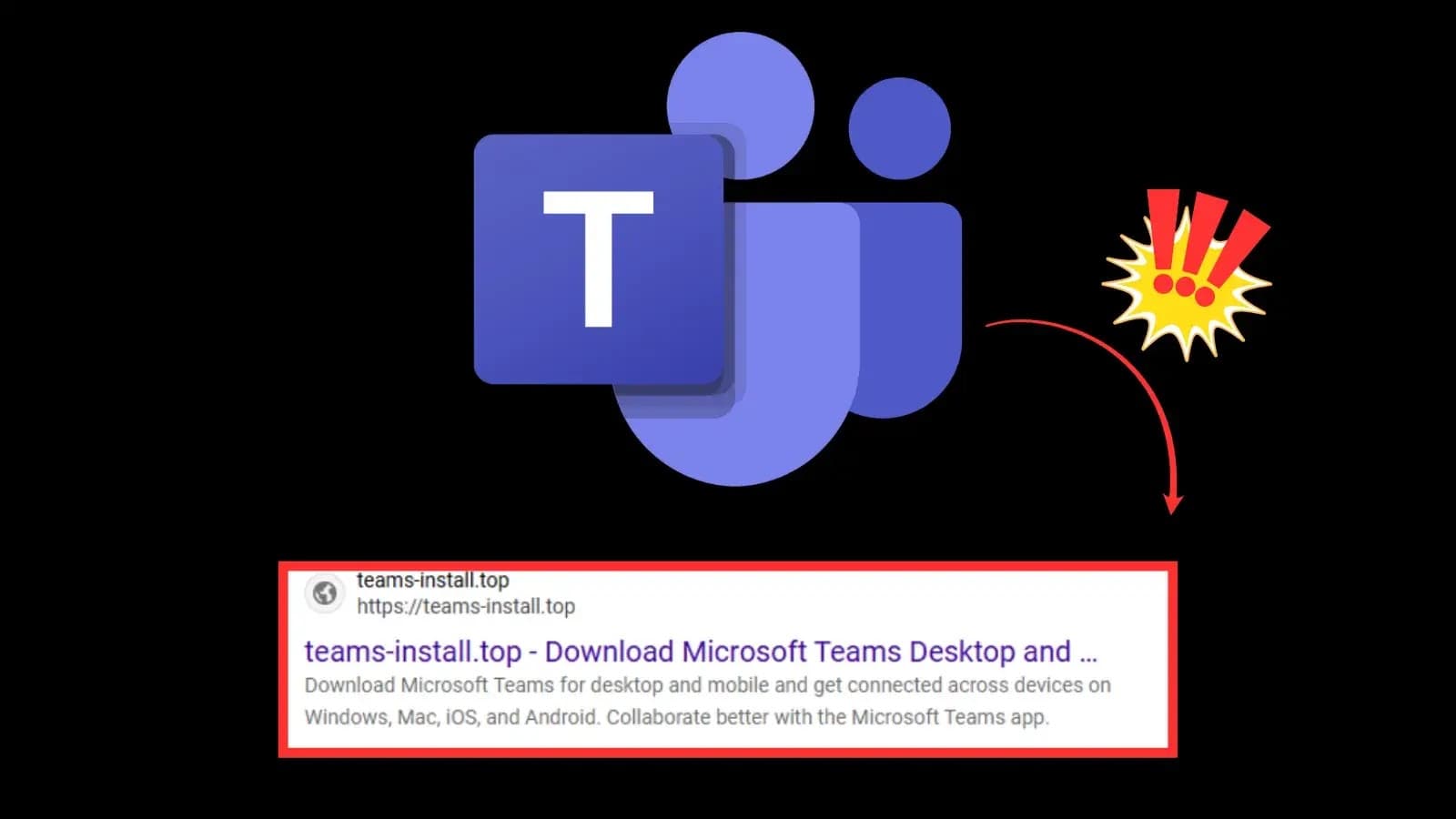
The tactic used by hackers to spread the malware is very simple. By exploiting sponsored Google ads or SEO - Search Engine Optimization tricks, whenever a user searches for terms related to downloading Microsoft Teams software like "teams download," "download teams," etc., a fake download page appears at the top of the search results. This lures users to access and download from it. According to the report, one of the fake websites recorded is teams-install[.]top.

When users execute the MSTeamsSetup.exe file downloaded from the fake website, the Oyster backdoor is immediately deployed on the victim's system. The Oyster backdoor is a multistage malware with a modular structure designed to maintain long-term remote access to the compromised system. The deployment process of this malware can be divided into the following main parts:
The malware drops a DLL file named
CaptureService.dllinto a random folder within the %APPDATA%\Roaming path. The %APPDATA% folder is hidden on Windows, so any folders within it are hidden from the user's view, making it harder to detect unusual activity for those without in-depth knowledge of computers and operating systems.It creates a Scheduled Task named
CaptureServiceto automatically trigger the DLL, ensuring long-term presence on the infected system. Additionally, this automated task is configured to frequently use therundll32.exeprocess, so the malicious DLL is continuously called, allowing hackers to access the victim's system at will as the connection to the Oyster backdoor remains open.It connects to the hacker's C2 server. Through the backdoor, hackers can easily collect sensitive data such as information about the victim's system, documents stored on the system, or even deploy additional malware on the system, causing severe security damage.
Remediation & Recommendations
Security researchers recommend that users should:
Download legitimate software: Only download and install software from the publisher's official website. Use bookmarks to directly access legitimate websites instead of indirect access through search results or ads.
Use security software: Utilize reputable security software to immediately alert and block unsigned installers or those with untrustworthy digital signatures.
Increase awareness: Enhance personal awareness of cyber threats, understand the risks of SEO poisoning and malvertising to minimize the chance of falling victim to dangerous malware campaigns.
Use security services: Employ 24/7 security monitoring services to easily detect early signs such as unusual Scheduled Tasks, strange folders created in the %APPDATA% directory, or suspicious connections to hacker C2 servers through network traffic monitoring.
IOCs
| MSTeamsSetup.exe | 9dc86863e3188912c3816e8ba21eda939107b8823f1afc190c466a7d5ca708d1 |
| MSTeamsSetup.exe | ac5065a351313cc522ab6004b98578a2704d2f636fc2ca78764ab239f4f594a3 |
| CaptureService.dll | d47f28bf33f5f6ee348f465aabbfff606a0feddb1fb4bd375b282ba1b818ce9a |
| CaptureService.dll | d46bd618ffe30edea56561462b50eb23feb4b253316e16008d99abb4b3d48a02 |
| Ads.dll | 90b633cacfa185dd912a945f370e14191644ecff1300dbce72e2477171753396 |
| CaptureService | Malicious Scheduled Task |
| team[.]frywow[.]com | Malvertising Domain |
| teams-install[.]icu | Malvertising Domain |
| teams-install[.]top | Malvertising Domain |
| nickbush24[.]com | Oyster C2 |
| techwisenetwork[.]com | Oyster C2 |
| maddeehot[.]online | Oyster C2 |
| server-na-qc2[.]farsafe[.]net | Oyster C2 |
| 45.66.248[.]112 | Oyster C2 |
| 54.39.83[.]187 | Oyster C2 |
| 185.28.119.228 | Oyster C2 |
| 4th State Oy | Malicious Cert Signer |
| NRM NETWORK RISK MANAGEMENT INC. | Malicious Cert Signer |






