LNK Stomping: A Technique to Bypass Windows Security
In the context of increasingly sophisticated cyberattacks, a new technique is emerging that is causing significant concern for organizations using the Windows operating system: LNK Stomping. This method exploits vulnerabilities in how Windows handles shortcut files (LNK), allowing hackers to bypass core security measures like Mark of the Web (MoTW), Smart App Control (SAC), and SmartScreen. The result? Malicious files can be executed without triggering any alerts, leading to risks of data theft, malware spreading, or remote system control.
Overview
The vulnerability CVE-2024-38217 was officially announced by Microsoft last year and was patched in the September 2024 security update (Patch Tuesday). According to the Cybersecurity and Infrastructure Security Agency (CISA), this vulnerability has been actively exploited for at least the past 6 years, with the first malware samples detected on VirusTotal since 2018. As a business, we cannot take this lightly, especially as email attacks with LNK file attachments are increasing, targeting employees to infiltrate internal networks.
This article will clearly explain, step-by-step, LNK Stomping, how it works, and most importantly, specific protective measures for businesses.
Some information about the vulnerability:
Mark of the Web (MoTW) is a basic security feature of Windows, acting as a "warning label" for files downloaded from the internet. When you download a file, Windows adds metadata (via NTFS Alternate Data Stream – ADS Zone.Identifier) so that SmartScreen and SAC can check and block it if it's suspected to be harmful. For example, when you open an EXE file from the web, you will see a warning dialog: "This file might harm your computer."
However, CVE-2024-38217 (rated CVSS severity 5.4 – Medium but widely exploited) allows hackers to "remove" the MoTW label by exploiting the path normalization process of Windows Explorer. The result: Malicious files run smoothly, just like trusted internal files.
Impact on Businesses:
Financial Risk: According to IBM's report, the average cost of a ransomware attack (often starting from a malicious file) will reach $4.88 million in 2024.
Loss of Sensitive Data: Hackers can steal customer information and trade secrets through payloads hidden in LNK files.
Operational Disruption: Attacks like these often spread through internal networks, affecting hundreds of computers.
Regulatory Compliance: Violating GDPR, HIPAA, or Vietnam's Cybersecurity Law can lead to heavy fines if data is exposed.
CISA added CVE-2024-38217 to the Known Exploited Vulnerabilities (KEV) catalog on September 10, 2024, requiring U.S. federal agencies to patch it urgently—a clear signal for global businesses to take immediate action.
How LNK Stomping Works:
Imagine an LNK file as a "shortcut" on the desktop that points to another program. The complex binary structure of an LNK includes the LinkTarget IDList, which contains Shell Item IDs describing the target file's location in the Windows system.
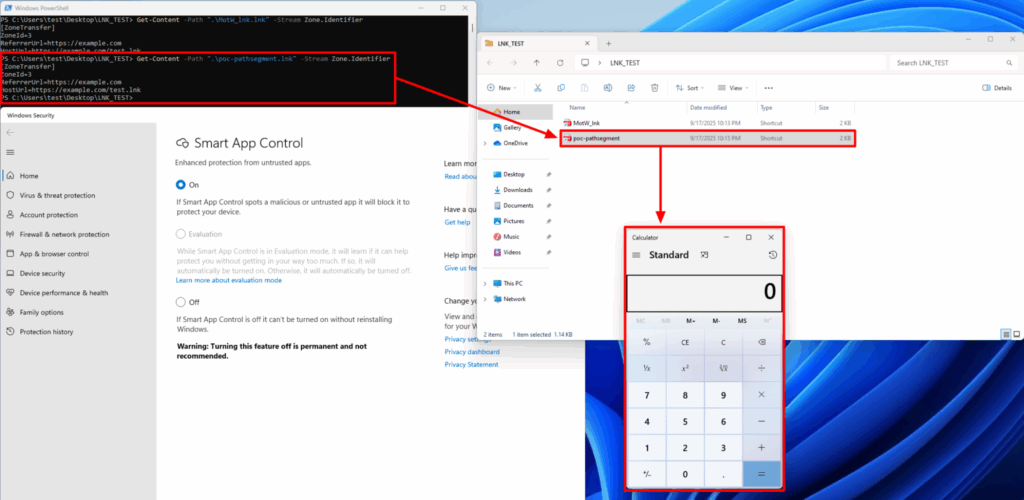
PathSegment Type (Path Segment Attack): Hackers cram the entire file path (e.g., C:\Users\Victim\malware.exe) into a single IDList element instead of breaking it down by directory. When a user clicks, Windows Explorer detects a "structure error" and automatically "fixes" it by overwriting the LNK file, unintentionally removing the ADS Zone.Identifier (MoTW).
Dot Type (Dot/Character Attack): Add a dot (.) or space at the end of the executable path, like "powershell.exe." instead of "powershell.exe". This triggers the normalization process, removing the MoTW before security checks.
Relative Type (Relative Path Attack): Use a single file name (like "malware.exe") without specifying the full path. Windows tries to "normalize" it, again removing security metadata.
Typical Attack Process:
The hacker sends an email with an LNK file disguised as an invoice or document (often compressed in RAR/ISO to avoid email scanning).
An employee clicks the file—Explorer.exe activates and removes the MoTW.
The payload runs through legitimate Windows tools (like PowerShell), appearing to operate normally.
Result: Malware is downloaded and spreads without triggering alarms.
This technique "hides" within legitimate system behavior, making it difficult for signature-based antivirus to detect. The first samples on VirusTotal from 2018 show that hackers experimented at least 6 years before making it public.
Exploitation in Practice
LNK Stomping is not "new"; it was disclosed by Elastic Security Labs in August 2024, but evidence shows exploitation since 2018. Joe Desimone (Elastic) discovered numerous samples on VirusTotal, with the oldest sample from over 6 years ago.
After Microsoft's policy to block Office macros in 2022, hackers shifted to using LNK, ISO, and RAR files—leading to a 300% increase in attacks via compressed files, according to a Splunk report. No specific threat actor group has been attributed, but CISA has confirmed active exploitation, often combined with infostealer malware.






