PDFSIDER: Safely Open Files by Confirming Their Source First
Overview
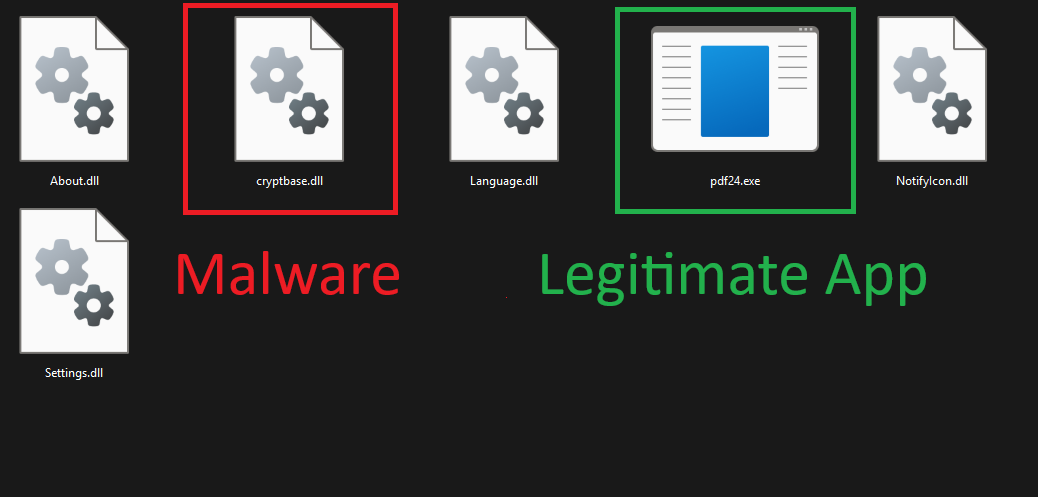
Recently, a highly sophisticated malware variant named PDFSIDER was discovered, spreading through DLL side-loading. It is designed to secretly deploy a backdoor with encrypted command-and-control (C2) capabilities. The malware uses a fake cryptbase.dll file to bypass endpoint detection mechanisms. This technique allows attackers to inject malicious code into the execution process of legitimate applications, making detection by signature or behavior much more difficult. It is classified as an Advanced Persistent Threat (APT) due to its sophisticated behavior and persistence in remote access through an encrypted backdoor.
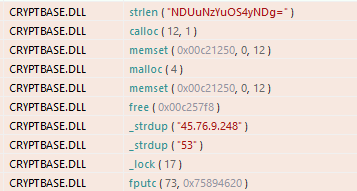
The analyzed DLL contains the entire Botan cryptography library embedded, configured to use AES-256-GCM authenticated encryption, which strongly indicates that the threat actors are using a secure and structured C2 protocol. Once loaded, the malware provides the attacker with a hidden interactive command shell and can exfiltrate command results through an encrypted channel.
Technical Details
The attack flow of PDFSIDER starts with spear-phishing using a ZIP file containing a fake PDF document file, which is exploited to load the malicious DLL (cryptbase.dll) through DLL side-loading, helping it bypass AV/EDR signatures. Upon execution, the malware runs in memory, initiating a hidden backdoor using cmd.exe /C with CREATE_NO_WINDOW, gathering system information (username, computer name, PID), creating a unique ID, and establishing AES-256/GCM encrypted C2 communication via Winsock (commonly using DNS port 53 on VPS). It also integrates strong anti-analysis mechanisms: checking for low RAM (GlobalMemoryStatusEx), detecting debuggers (IsDebuggerPresent), and sandbox/VM to avoid virtualization environments. Overall, this campaign combines high stealth, strong encryption, and analysis evasion, aligning more with APT than ransomware, but still relies on initial phishing—which can be blocked by advanced email filtering or user awareness—and the C2 infrastructure can be exposed if IOCs like IP 45.76.9.248 are monitored.

1 . Initial Infection and Delivery
PDFSIDER launches this campaign using spear-phishing emails that lead victims to an attached ZIP file. The ZIP file contains a legitimate EXE file named 'PDF24 App.' PDF24 Creator is software from Miron Geek Software GmbH used to create PDF files from any application and convert files to PDF format.
The infection chain begins when the victim opens the EXE file, which does not display an interface when running on the machine; however, it starts operating immediately upon execution.
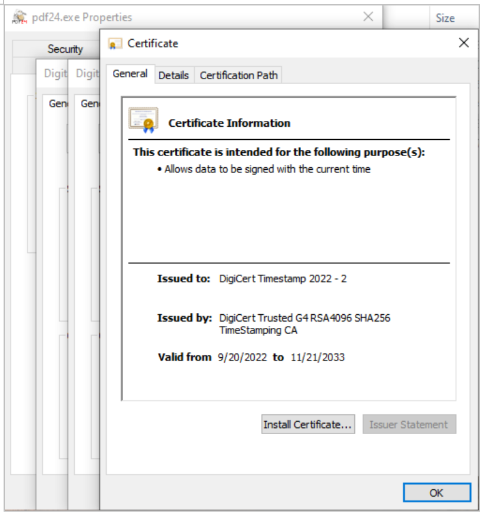
One of the code-signing certificates is still valid: [description of the legitimate certificate – this part usually includes an image in the original article].
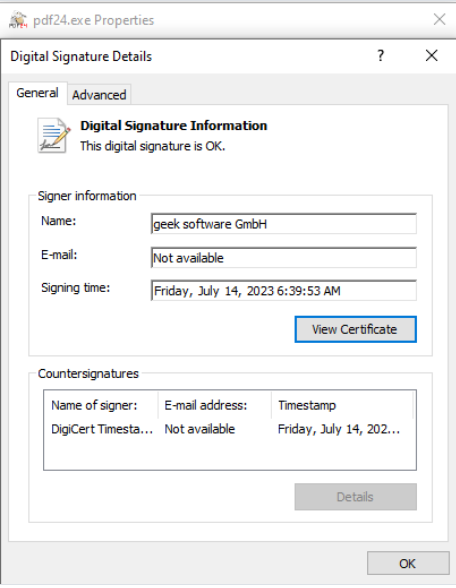
The EXE file carries a legitimate signature; however, the PDF24 software has a vulnerability that attackers exploit to load this malware and effectively bypass EDR.
Malware relies on DLL Side-Loading, a technique where a malicious DLL is placed next to a legitimate application so that it automatically loads the DLL.
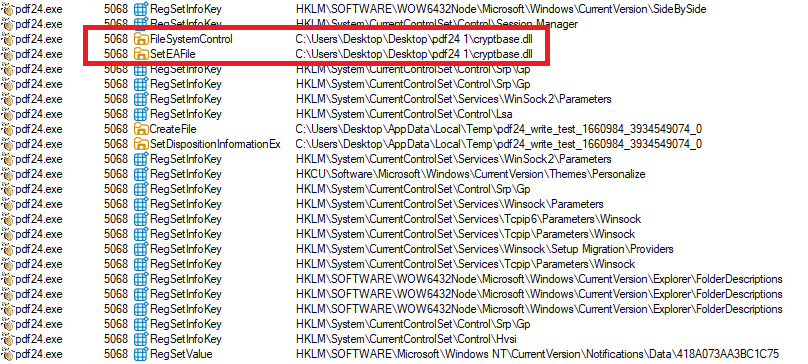
When the victim runs the legitimate program, PDF24.exe loads the attacker's DLL instead of the real system cryptbase.dll, thereby gaining code execution.
Once loaded, PDFSIDER initializes Winsock, sets up encrypted communication, gathers system information, and starts the backdoor loop.
2. In-Memory Execution
PDFSIDER operates mainly in memory, minimizing traces on the disk:
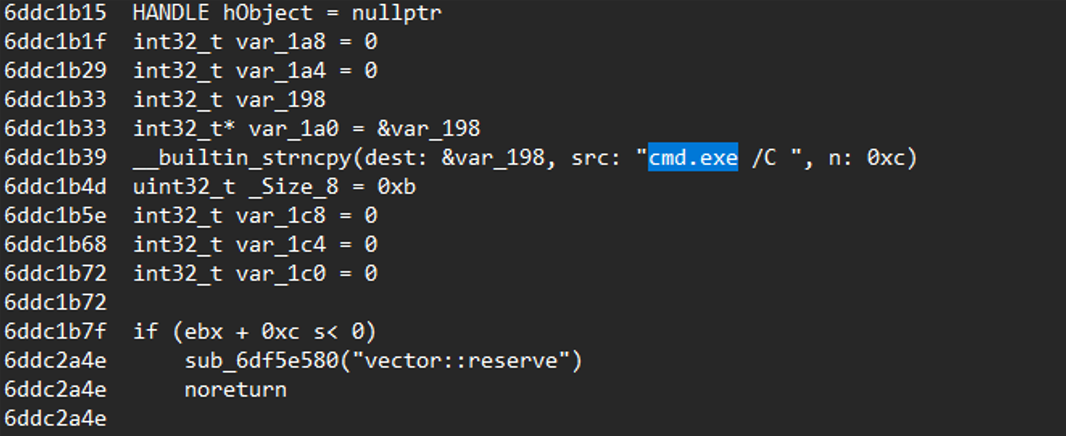
The malware provides full remote command execution capability as soon as it starts, performing various actions. It creates anonymous pipes and constructs command strings using cmd.exe /C <command provided by the attacker>.
This command is launched with the CREATE_NO_WINDOW flag, ensuring no console window appears.
The malware then extracts all information from your system, creates a unique ID from the system, and sends the output back to the attacker.
2.2 Encrypted C2 Data Handling
The malware uses the encryption library Botan 3.0.0, integrating key components like AES-256/GCM, GHASH, and checks for GCM tag errors.
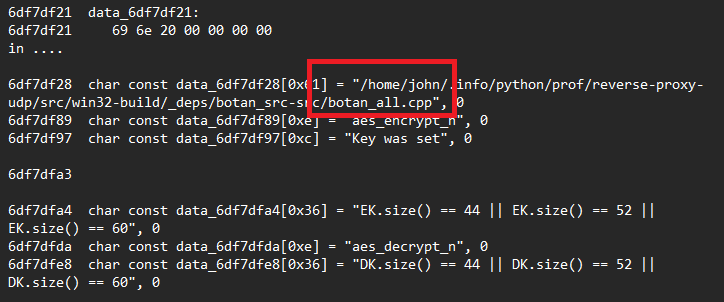
This strongly indicates that all data in/out is decrypted in memory, ensuring it is never written to disk. The data is also authenticated using AEAD (Authenticated Encryption with Associated Data) in GCM mode, providing a high level of security. This type of encryption implementation is typical for remote shell malware in targeted attacks, where the integrity and security of communication are crucial.
3. Anti-VM Technology
PDFSIDER has a multi-stage environment check routine to detect sandboxes, virtual machines (VMs), and analysis labs. The malware uses the GlobalMemoryStatusEx function to assess the total system RAM, and systems with low RAM (often associated with sandboxes or virtual environments) will cause the malware to exit early.
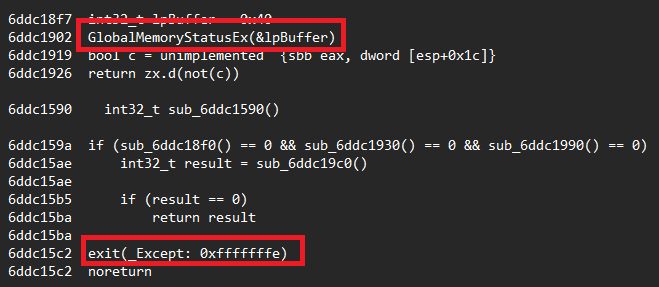
Additionally, it checks for the presence of a debugger, further ensuring that the malware avoids executing in controlled or monitored environments.
During the investigation, we discovered that the hacker rented a VPS from a company and set up a C&C server to send encrypted data through DNS port 53 at a specified location, used to exfiltrate compromised data.
PDFSIDER is a powerful and stealthy backdoor, designed for long-term secret access, flexible remote command execution, and encrypted communication—more aligned with espionage tradecraft rather than malware for financial gain.
4. Decoy
The threat actor can use various types of decoys to lure victims into opening malicious documents. In a recent event of the same campaign, the actor even used fake documents as if they were prepared by the Intelligence Bureau of the Joint Staff Department of the Central Military Commission of China (中央军委联合参谋部情报局).
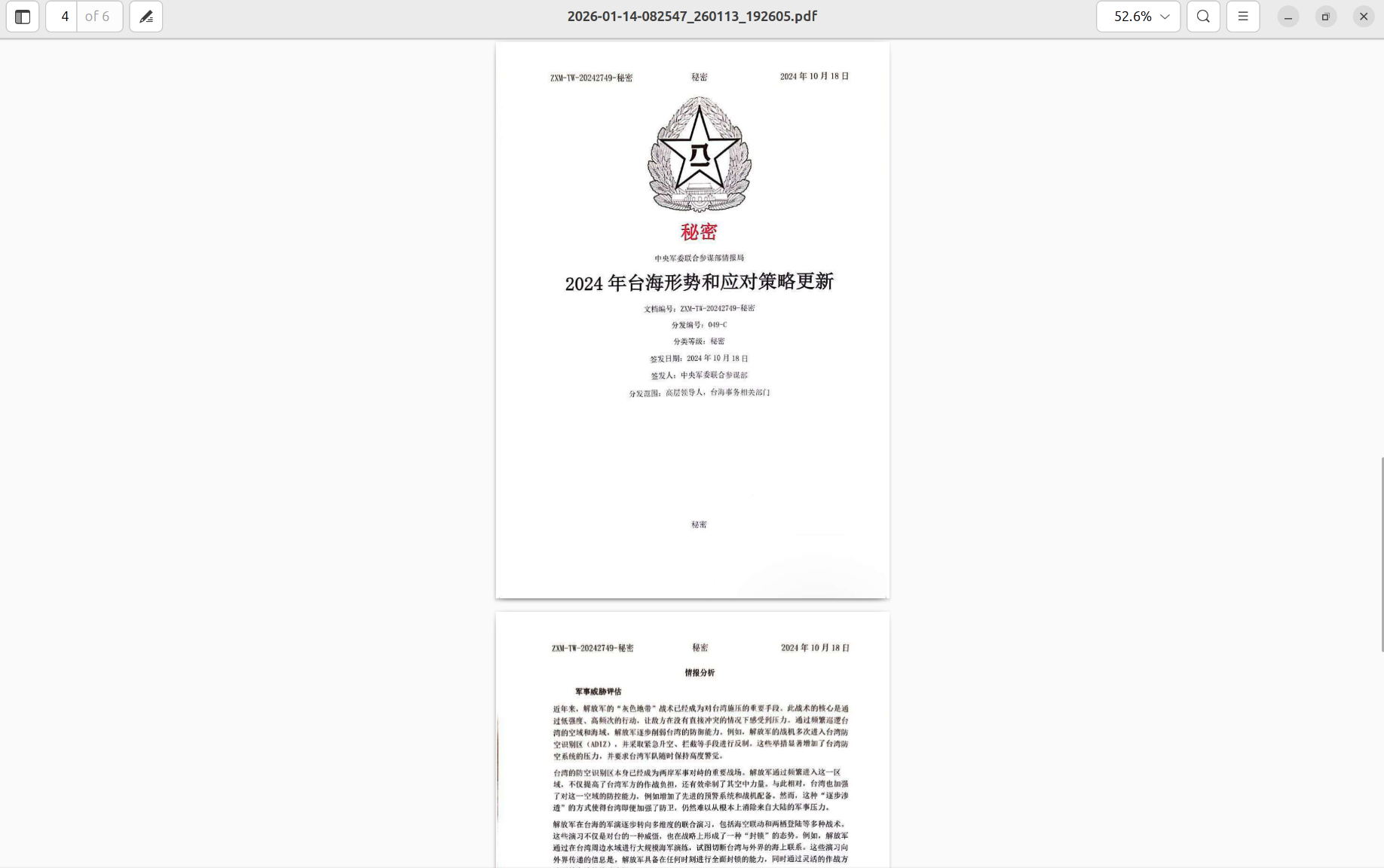
Notably, most artifacts of the PDFSIDER campaign evade popular AV/EDR solutions. Currently, Resecurity assesses PDFSIDER as tradecraft used in targeted attacks rather than widespread distribution.
IOCs
File
| File name | MD5 Hash | Status |
| About.dll | e0e674ec74d323e0588973aae901b5d2 | Clean |
| Cryptbase.dll | 298cbfc6a5f6fa041581233278af9394 | Malicious |
| Language.dll | 80e4a29270b828c1f97d9cde9475fcbd | Clean |
| NotifyIcon.dll | 96ff508f9be007062b1770691f489e62 | Clean |
| Pdf24.exe | a32dc85eee2e1a579199050cd1941e1d | Clean |
| Settings.dll | 9f9dd5a432b4dde2160c7a7170e0d069 | Clean |
C2 IPs: 45.76.9.248
Recommendations
Based on the analysis of the PDFSIDER malware, a sophisticated APT threat using spear-phishing, DLL side-loading to evade AV/EDR, and similar threats targeting Vietnamese businesses like Mustang Panda or Operation Hanoi Thief, FPT Threat Intelligence provides the following necessary and practical recommendations for protection:
Enhance cybersecurity awareness training for employees: Organize free or short-term training sessions (via online platforms like AIS eLearning) on how to recognize spear-phishing emails and avoid opening strange attachments (such as ZIP files containing EXE disguised as PDF24). Encourage the use of email scanning tools like VirusTotal before opening, which can reduce initial infection risks by 80%.
Update and implement basic security tools: Use free or low-cost antivirus software like Kaspersky Free or Microsoft Defender, combined with simple EDR (such as CrowdStrike Falcon Insight for SMEs). Enable behavior monitoring to detect DLL side-loading and in-memory execution, and patch legitimate software vulnerabilities like PDF24 Creator as soon as updates are available.
Apply the principle of least privilege and multi-factor authentication (MFA): Limit access to system files and use MFA for business emails (via affordable Google Workspace or Microsoft 365). Regularly check admin rights to prevent exploitation of vulnerabilities like those in APT campaigns from China targeting Vietnam.
Monitor networks and back up data: Use SIEM traffic monitoring from Firewalls and DNS to track unusual traffic (e.g., C2 connections via DNS port 53), and perform weekly data backups (off-site or cloud like Google Drive). To counter ransomware related to PDFSIDER, apply the 3-2-1 rule (3 copies, 2 media, 1 offline).
References
PDFSIDER Malware - Exploitation of DLL Side-Loading for AV and EDR Evasion
https://www.bleepingcomputer.com/news/security/Researchers Uncover PDFSIDER Malware Built for Long-Term, Covert System Access