PLAYFULGHOST backdoor: A new cyber threat with multiple risks
Introduction
Recently, there have been reports about attackers using popular VPN applications as a backdoor to spread malware, one of which is PLAYFULGHOST. PLAYFULGHOST is a new malware family with capabilities including keylogging, taking screenshots, recording audio, accessing remote shells, and transferring and executing files.
Method of Spread
Google researchers analyzed a new malware family called PLAYFULGHOST, which supports many features including keylogging, taking screenshots, recording audio, remote shell access, and file transfer/execution.
The PLAYFULGHOST backdoor shares many functions with Gh0st RAT, whose source code was made public in 2008. However, the backdoor differs in its encryption method. According to a report by the Mandiant Defense Team from Google, this backdoor spreads through:
Phishing emails with subjects like "code of conduct" to trick users into downloading the malware.
Bundling malicious code with popular software like LetsVPN and distributing them through SEO poisoning (a method where attackers manipulate search engines, leading users to malicious or fake websites).
Method of Attack
In the case of phishing, the attack chain starts by tricking users into opening a suspicious RAR file disguised as an image file with a .jpg extension. When users open and execute the compressed file, it drops a Windows executable used to download and execute the PLAYFULGHOST payload from a remote server.
In the case of SEO poisoning, victims are tricked into downloading a fake software installer, like LetsVPN, which allows downloading components of the backdoor from a remote server.

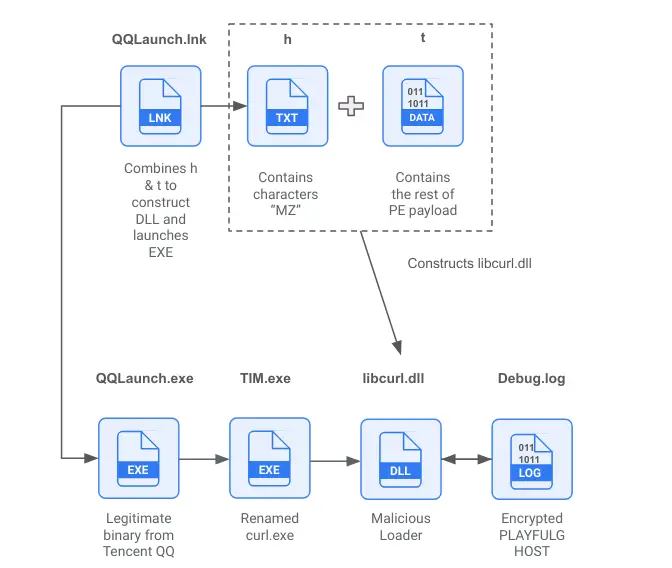
PLAYFULGHOST uses DLL search order hijacking and side-loading techniques to execute a malicious DLL. Researchers at Mandiant discovered a complex case where a Windows shortcut was renamed "curl.exe" to load the malware.
According to a public report by Google: “Mandiant observed a second, more sophisticated execution scenario which begins with a Windows LNK file named “QQLaunch.lnk”. This LNK file combines a text file named “h” which contains the characters “MZ” and a second file “t” which contains the rest of PE payload to construct a new malicious DLL named “libcurl.dll”. Then, the LNK file launches “QQLaunch.exe”, a legitimate binary from Tencent QQ, which launches another legitimate binary “TIM.exe” which is a renamed version of the program CURL. TIM.exe then loads a malicious launcher DLL “libcurl.dll” which will decrypt and load the PLAYFULGHOST payload from an encrypted file named “Debug.log”.“
Mandiant researchers have tracked malware families and tools related to PLAYFULGHOST, with the following information:
| Malware / Utility | Description | Use case |
| BOOSTWAVE | BOOSTWAVE is a shellcode that acts as in-memory dropper for an appended Portable Executable (PE) payload. | On one occasion, Mandiant observed a PLAYFULGHOST payload being embedded within BOOSTWAVE. |
| TERMINATOR | TERMINATOR is an open-source tool written in C++ that reproduces Spyboy technique to terminate all EDR/XDR/AVs processes by abusing the zam64.sys driver. | Mandiant observed the utility being deployed under the name 1.sys along with the download of PLAYFULGHOST components. |
| QAssist.sys | QAssist.sys is a rootkit embedded within PLAYFULGHOST capable of hiding registry, files, and processes specified by the threat actor. | While not observed being used, Mandiant assesses that the rootkit is intended to hide malicious activities on the system. |
| CHROMEUSERINFO.dll | CHROMEUSERINFO.dll is a DLL used by PLAYFULGHOST to retrieve Google Chrome user data including stored login credentials. | Mandiant observed an archive file containing CHROMEUSERINFO.dll along with other PLAYFULGHOST components. |
PLAYFULGHOST also has the ability to install Mimikatz, an open-source program used to extract passwords from computers. Additionally, it hides and maintains persistence through methods like registry keys, scheduled tasks, startup folders, and Windows services.
This backdoor can download additional payloads, block input like keyboard and mouse, delete event logs, clear the clipboard, erase browser data, and remove profiles for applications like Skype, Telegram, QQ...
Researchers at Google provide rules using Google Operations to detect PLAYFULGHOST activities.
Recommendation
To prevent the spread of malware in general, and specifically for PLAYFULGHOST, FPT Threat Intelligence recommends the following:
Do not open or follow instructions in emails from unknown senders or phishing emails.
Do not download software from unknown sources, cracked software, or from untrustworthy websites.
Increase user awareness, promote information security, and conduct phishing drills.







