The APT group Earth Kuma conducts attack campaigns targeting countries in Southeast Asia, including Vietnam
Information about the APT group Earth Kuma
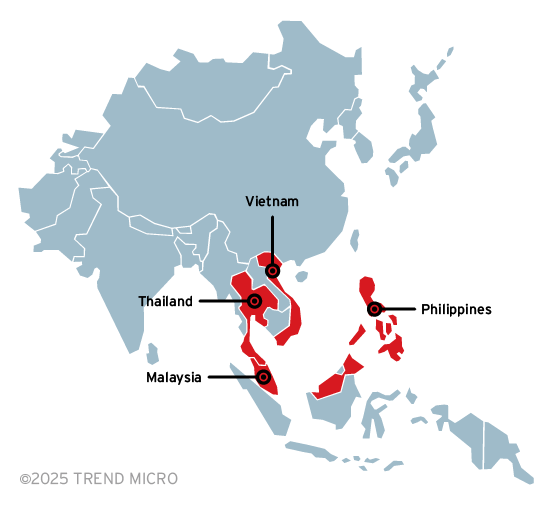
Since June 2024, security researchers from Trend Micro have discovered complex APT attack campaigns targeting Southeast Asian countries, including the Philippines, Malaysia, and Vietnam, and have named the group behind these campaigns Earth Kuma. This APT group mainly targets the government and energy sectors, aiming to steal data. According to tracked information, Earth Kuma has been engaging in data theft since November 2020. This APT group specializes in stealing data from public cloud services like OneDrive or Dropbox using custom tools such as TESDAT and SIMPOBOXSPY. They also create their own tools to hide activities, like KRNRAT and MORIYA.
Details about the attack behavior
The attack chain and malware used in the attack are summarized as follows:
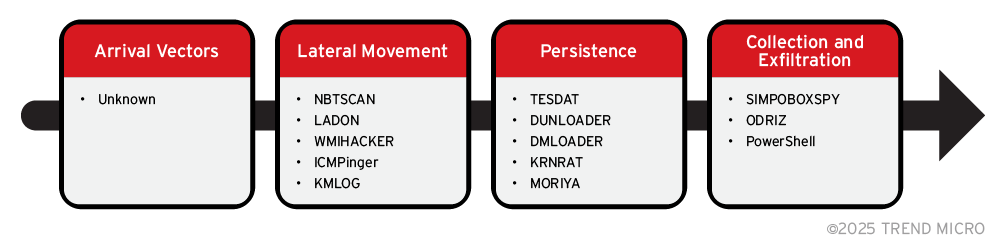
Currently, researchers are unsure of the initial intrusion method as they began investigating long after the victims had been attacked. To move between devices on the network, the attackers scan the system and set up malware including: NBTSCAN, LADON, FRPC, WMIHACKER, and ICMPinger. They also set up the KMLOG keylogger to steal the victim's login information.
The attackers use the ICMPinger tool to scan the network using the ICMP protocol to check if any devices are active on the network. They delete this tool once it has been used.
The Ladon tool is also used for scanning, including port scanning, service scanning, network devices, vulnerability detection, password cracking, etc. To avoid detection, this tool is wrapped in a loader compiled with PyInstaller.
To move laterally within the network, they use the WMIHACKER tool, which allows command execution on port 135 without needing SMB. In some cases, they execute commands through the SMB service (using net use) to check the system and set up malware.
To steal login information, they use a tool called KMLOG, a keylogger that saves user keystrokes in the file %Appdata%\Roaming\Microsoft\Windows\Libraries\infokey.zip. To hide this file, they add a fake ZIP file header (PK header) at the beginning. The content behind this header is the user's keystroke information.
To maintain presence, the group uses different loaders such as DUNLOADER, TESDAT, and DMLOADER. These loaders load payload files into memory, execute them, and then deploy malware to collect data on cloud services. In some cases, they also use KRNRAT and MORIYA.
DUNLOADER is a loader that allows loading payloads from a file named pdata.txt or from its own BIN file, then decodes them using XOR. This is a DLL file and is always executed by rundll32.exe by checking if the parent process name contains the string und. This loader has an export function named Start.
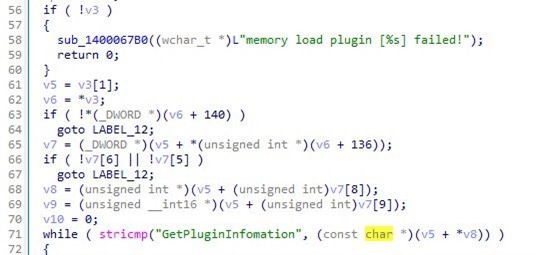
A newer loader named TESDAT always loads a payload file with the extension .dat. Instead of using standard APIs, it uses an API called SwitchToFiber. There are two different types of TESDAT loaders, which can be either an EXE or a DLL file with an export function called Init.
DMLOADER is a recent loader that loads embedded payloads and decodes them as a PE buffer in memory. This loader has export functions named Domain, Startprotect, or MThread.
The names of these loaders are placed in directories commonly accessed by victims rather than those typically used by other attackers, aiming to blend the loaders with other legitimate user files.
After setting up the loader, this attack group installs a rootkit on the victim's machine. The first type of rootkit encountered by researchers is MORIYA, which operates by intercepting TCP streams. It attempts to monitor for packets from C2 servers by checking the first 6 magic bytes. If they match, it tries to inject malicious payloads into the body of the returned packet.
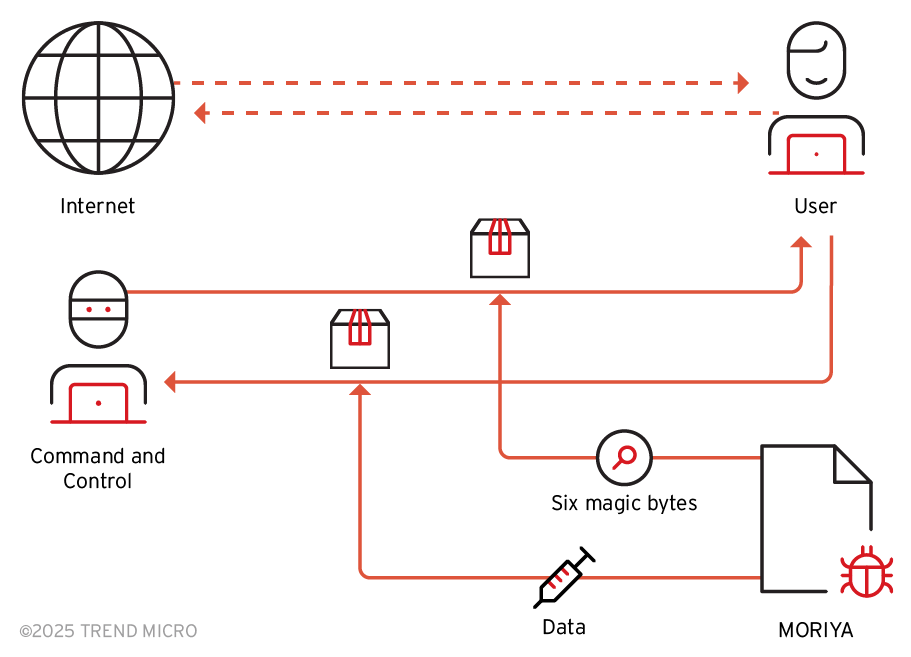
This rootkit can also inject shellcode, loading a payload from \\SystemRoot\\system32\\drivers\\{driver_name}.dat. This payload will be AES decrypted and injected into the svhost.exe process. The shellcode can be called using the NtCreateThreadEx API.
Another type of rootkit encountered is called KRNRAT, which has full backdoor capabilities including process manipulation, file hiding, shellcode execution, traffic obfuscation, and connection to C2 servers. Finally, after execution, this rootkit will load an additional payload and inject it into the svhost.exe process. This shellcode operates similarly to MORIYA.
After connecting to the C2 server, it will download the payload for the next step. The final payload downloaded from the C2 server is called SManager.
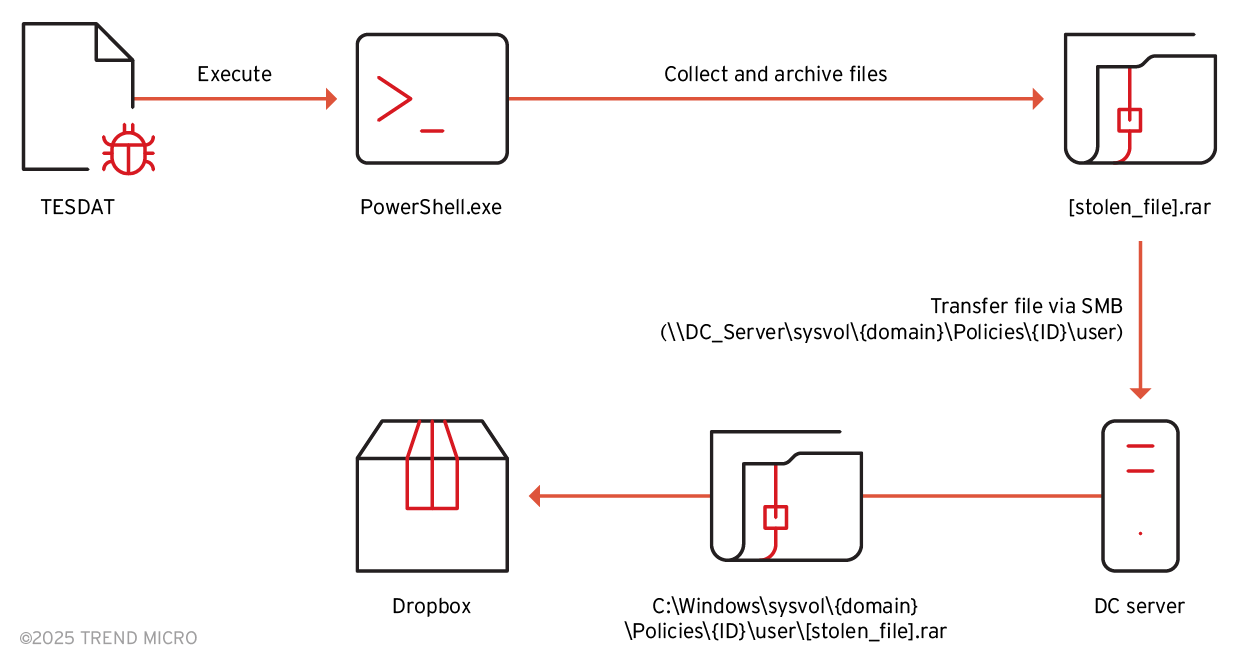
At the data collection and extraction stage, two tools are used to extract information from the victim to the attacker's cloud services like Dropbox or OneDrive. Before retrieving files from the victim's machine, several commands are executed by the TESDAT loader to collect documents with extensions .pdf, .doc, .xls, .xlsx, .ppt, and .pptx. These documents are first placed in a tmp folder and then compressed using WinRAR with password protection.
The SIMPOBOXSPY tool is used to collect and upload the compressed files to Dropbox with a predefined token.
The other tool, ODRIZ, is used to upload the collected files to OneDrive with a refresh token.
Recommendation
To be cautious of complex campaigns like those of the APT Earth Kuma group, FPT Threat Intelligence provides the following recommendations:
Update the IOCs of this attack campaign to detect and prevent attacks
Do not open unnecessary service ports like SMB
Implement policies for installing drivers, only install drivers that are verified as safe
Have strict monitoring measures and conduct user awareness training
IOC
| sha256 | 004adec667373bdf6146e05b9a1c6e0c63941afd38e30c2461eaecb707352466 | TESDAT |
| sha256 | 0a50587785bf821d224885cbfc65c5fd251b3e43cda90c3f49435bb3323d2a8b | TESDAT |
| sha256 | 10898b74b612b1e95826521c5ccf36f7a238f5d181993c3c78c2098fcfdc1f3f | TESDAT |
| sha256 | 131bacdddd51f0d5d869b63912606719cd8f7a8f5b5f4237cbdb5c2e22e2cba2 | WMIHACKER |
| sha256 | 1ab42121bb45028a17a3438b65a3634adb7d673a4e1291efeabf227a4e016cfb | SIMPOBOXSPY |
| sha256 | 1c350d09c1cd545d54c38cd03aba3fd4eb0e8d97a3ba6c3744cc33ed92cb9a48 | DUNLOADER |
| sha256 | 1e48967e24d4ae2ac2697ef09c0f2702285825831bd516cb3be8859496fd296f | DUNLOADER |
| sha256 | 1f3f384e29eab247ec99d97dfe6a4b67110888e4ad313b75fa9d0beceef87e93 | KRNRAT |
| sha256 | 1f5f6cc1cbf578412ea5279dbdb432eda251309695513a74de66063ab02789f1 | TESDAT |
| sha256 | 2c9b8e4852181d51ff72dc6dec78bef014db8af83d30c05c3e9c5eb060278730 | KRNRAT |
| sha256 | 2e87615142170a7510e26f94790bfb81df4d499a9f530d0bd8fe0fb1575b17f8 | TESDAT |
| sha256 | 34366323262346e10d8780bad9d30c6d4d747e4ec543243be76f33b7c028ea36 | TESDAT |
| sha256 | 37a397a2482b37d19d58588c0a897a08111b74d122c21542f1bf852ae83e1db0 | DMLOADER |
| sha256 | 383aa73fe72caf268ce0874ebbcd13fc4c9e1e5c6200cdd66862de7257942cea | TESDAT |
| sha256 | 398234b692a80a424939e98a2d96a705ce3fd9d61950420b5f2af45890abc48e | TESDAT |
| sha256 | 4198b4ec5bb0c72112e9cf835686c33b9a97037acfb7727e494046a73106e938 | MORIYA |
| sha256 | 45e1138f2b8e822cbd4573cb53104b402ae26dcddb42c70534cf024a8bc6db66 | DUNLOADER |
| sha256 | 49ab6e2b5e378c74d196aecac4e84c969c800051167c1e33d204531fabd17990 | KMLOG |
| sha256 | 4ae186ee19d0d3e246dc37ac722a27d5297d2577de59b8583c97897480290bc1 | TESDAT |
| sha256 | 54e14b7742801970c578fad2ec2a193334ca8a17b60ee18dd6ec0fbfc8ce900b | SIMPOBOXSPY |
| sha256 | 612a5fcb7620deef45a021140b6c06ab9c0473dce5b7e4a54960e330a00c90f3 | DUNLOADER |
| sha256 | 6190b13df521306bfa7ee973b864ba304ee0971865a66afbe0b4661c986099f4 | KMLOG |
| sha256 | 66edb72f6f7c8cad23c6659a81fa023f57c1a86c7d7b7022f1453b177f2b3670 | NBTSCAN |
| sha256 | 6bbbb227d679ea00f0663c2e261d5649417d08285f9acc1fd80e806ddea08403 | TESDAT |
| sha256 | 6ef3a27fdca386fe093c12146cd854d9ae6b42ca637950ca46bfd364ceab5b53 | DUNLOADER |
| sha256 | 73afc6af6fdfcaf9832aa2975489271bad7c8ea58679f1a2ddd8f60b44cc4a13 | TESDAT |
| sha256 | 75cc8474abb1d9a06cd8086fede98958653d013fb7ff89bbc32458b022a8fc94 | DUNLOADER |
| sha256 | 823a0862d10f41524362ba8e8976ddfd4524c74075bd7f3beffa794afb54f196 | MORIYA |
| sha256 | 8414136128f73fa7e29032df7b8115bc89832c57e2602d81de1e520cc2d7958d | ICMPINGER |
| sha256 | 85e78a1b0a78e5d921c89241aaadd505d66dc4df29ca7d8a81098f42487ba350 | TESDAT |
| sha256 | 876c822f333e812041af24ae80935a830ca5016f9aaf2e8319ebb6cab1f9d7d0 | SIMPOBOXSPY |
| sha256 | 8c703148567cb66fe27bc07d18de58aa36aa84a49f1ce7545e9ec56378857d3d | TESDAT |
| sha256 | 8ca1ffbd3cd22b9bead766ebd2a0f7b2d195b03d533bacf0cb8e1b1887af5636 | KMLOG |
| sha256 | 8e6583cca6dd4a78bdc0387c7f30334ab038e5c77848f708fe578e60dd8d9e00 | DUNLOADER |
| sha256 | 96b407856889c920a49f921d925118a130b904e99f9fe43a87342c680ffb9f27 | ODRIZ |
| sha256 | a359a06fbc6b5cf5adf7f53c35145b28f3c8a70f6998631090021825aea08e22 | TESDAT |
| sha256 | aa925a5a8a7d5b36a66431f4968bd1003d1bbb6cb3ff6d03d9e3e0143c48382b | DUNLOADER |
| sha256 | aef3407310de48e13575c3d98b660ab7ddafb7efe3f4909682907ac286062392 | TESDAT |
| sha256 | b26e8e0be066ee0b86f8fb2b0a703717ebbf34c8a33ef9a6f8f164ad012f1746 | LADON |
| sha256 | c0326a0cd6137514ee14b6ac3be7461e8cf6c6adec74d087fd30cb06b91ecda2 | TESDAT |
| sha256 | c6f73268eba553c7991f876a166440f5b4d519dea6b13bc90583fde1e89e81ed | FRPC |
| sha256 | d3d2355b1ffb3f6f4ba493000e135dfd1b28156672e17f0b34dfc90cc3add352 | TESDAT |
| sha256 | e143c15eaa0b3faccc93ce3693960323dbaa683ac9ce30382e876690278dfefa | DUNLOADER |
| sha256 | ec9220cf8208a3105022b47861d4e200672846ef484c1ea481c5cfd617cb18dc | MORIYA |
| sha256 | f3916c414db0f660d488c9d3aaa8355f3eb036ca27a9c606fe7e5e1a9bd42b38 | LADON |
| sha256 | f52d9355b9efb6a1fcb32b890c5c373274df21ce38050d49416f469be95dc783 | DUNLOADER |
| sha256 | f9892636093266a01ed6f0486c00189d2eeb532a3086660490f4efeb6d026487 | FRPC |
| domain | www[.]dfsg3gfsga[.]space | C&C |
| domain | www[.]igtsadlb2ra[.]pw | C&C |
| domain | www[.]ihyvcs5t[.]pw | C&C |
| domain | www[.]vidsec[.]cc | C&C |
| ipv4 | 103[.]238[.]214[.]88 | C&C |
| ipv4 | 149[.]28[.]147[.]63 | C&C |
| ipv4 | 166[.]88[.]194[.]53 | C&C |
| ipv4 | 185[.]239[.]225[.]106 | C&C |
| ipv4 | 38[.]147[.]191[.]103 | C&C |
| ipv4 | 38[.]60[.]199[.]225 | C&C |
| ipv4 | 45[.]77[.]250[.]21 | C&C |
Reference
Earth Kurma APT Campaign Targets Southeast Asian Government, Telecom Sectors
Earth Kurma APT is actively targeting government and telecommunications orgs in Southeast Asia






