Why is a ransomware from 2020 still taking down hundreds of businesses in 2025?
Makop Ransomware is back, an old vulnerability but new tactics have caused unpredictable consequences for businesses..

Overview
Makop ransomware is emerging as one of the most dangerous threats targeting businesses operating Windows systems via Remote Desktop Protocol (RDP). Exploiting weakly secured RDP ports or leaking login information, the Makop attack group quietly infiltrates the internal network, escalates privileges, and installs malware that encrypts all of the victim's data in just a few minutes. What's worrying is that Makop doesn't use overly complicated techniques, instead they just take advantage of the administrator's subjectivity in protecting RDP.
Makop is also known for its rapid customization: each campaign creates new malware variants, attaching different extensions, anti-analysis techniques and separate ransom payment instruction records. Thanks to that, this ransomware can bypass many traditional defense layers and make it difficult for businesses to trace the source of the attack.
What is Makop ransomware?
Makop ransomware first appeared in late 2020 and was quickly identified as a family of ransomware operating strongly under the Ransomware-as-a-Service (RaaS) model. Unlike famous malware lines such as REvil or LockBit, Makop operates more silently, mainly relying on a network of small-scale affiliates, attacking small and medium-sized targets instead of large businesses.
In its early stages, Makop used relatively simple encryption techniques, accompanied by file extensions such as .makop, .lokd, or .espino, but variations quickly increased. From 2021 to 2023, the Makop development team continuously releases new versions with the ability to:
Customize the extension name according to the campaign.
Hybrid encryption combines AES + RSA.
Insert ransom note in HTML or TXT format.
Added difficult analysis techniques such as obfuscation and packer.
Automatically delete shadow copies to prevent data recovery.
From 2023–2024, Makop has strongly shifted to attack campaigns against businesses using Windows Server infrastructure, causing a series of intrusion reports worldwide. The continuous appearance of variants such as ACCESS, LOCKED, CARTOP shows that the Makop operating team is still actively developing and refining the malware.
To date, Makop is considered one of the most persistent ransomware lines in the RDP brute-force attack segment, targeting unprotected or misconfigured environments.
Techniques used by Makop Ransomware
RDP (Remote Desktop Protocol) attack.
Privilege Escalation.
BYOVD – Bring Your Own Vulnerable Driver.
Use AV Killer/Security Disabler.
Lateral Movement – Move through other machines.
Use a loader like GuLoader.
Shadow Copy – Prevents data recovery.
Strong data encryption (AES + RSA).
Commonly exploited Makop vulnerabilities
CVE-2016-0099: LPE Windows Kernel, CVSS 7,8
CVE-2017-0213: Windows Update Medic, CVSS 7,8
CVE-2018-8639: Win32k Elevation, CVSS 7,8
CVE-2019-1388: Service Control Manager, CVSS 7,0
CVE-2020-0787: BITS Service, CVSS 7,8
CVE-2020-0796: SMBGhost, CVSS 10 (RCE/Privilege Escalation)
CVE-2020-1066: Windows Installer, CVSS 7,8
CVE-2021-41379: Desktop Window Manager, CVSS 7,8
CVE-2022-24521: Win32k Subsystem, CVSS 7,8
CVE-2025-7771: ThrottleStop.sys Driver, CVSS 8,4 (BYOVD)
Attack mechanism and exploitation process
.webp)
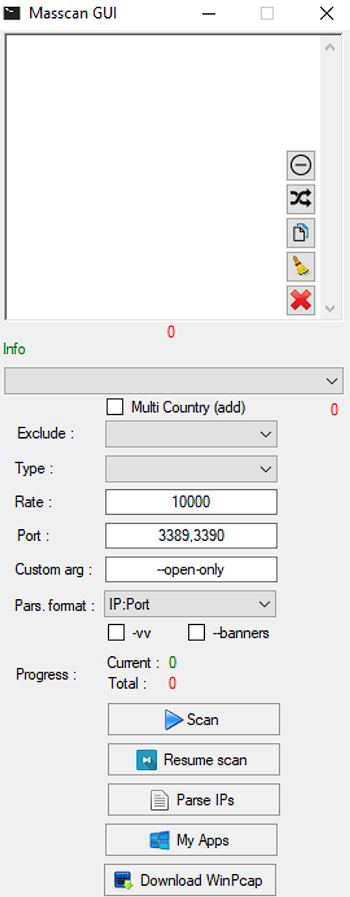
Unlike many common malware, Makop has a methodical and detailed attack flow with the first stage being system reconnaissance. The goal of this stage is to detect hosts with open RDP, collect usernames, and network information. Here the attacker will perform RDP brute-force or log in with a credential leak.
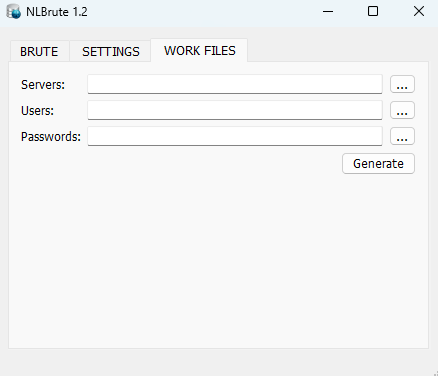
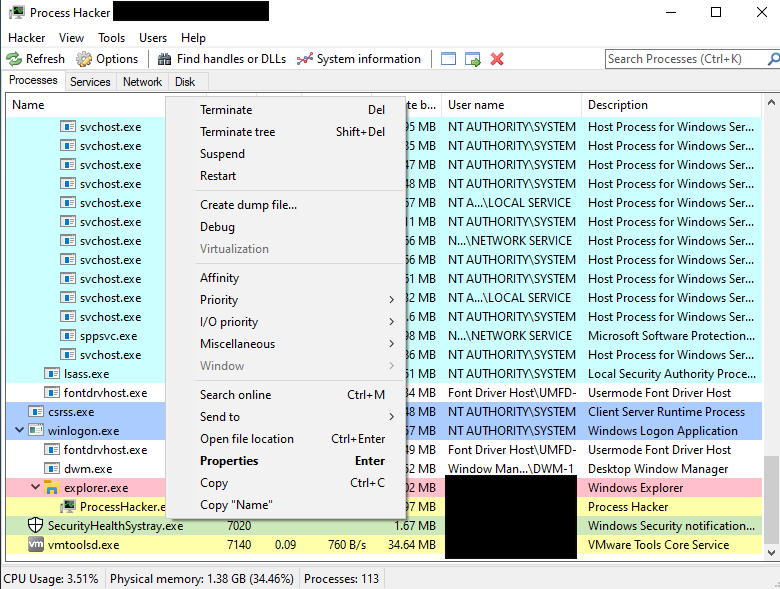
Once inside the system, they use network scanning tools such as: Advanced IP Scanner or NetScan to identify high-value servers, internal shares and network resources that need to be taken over.
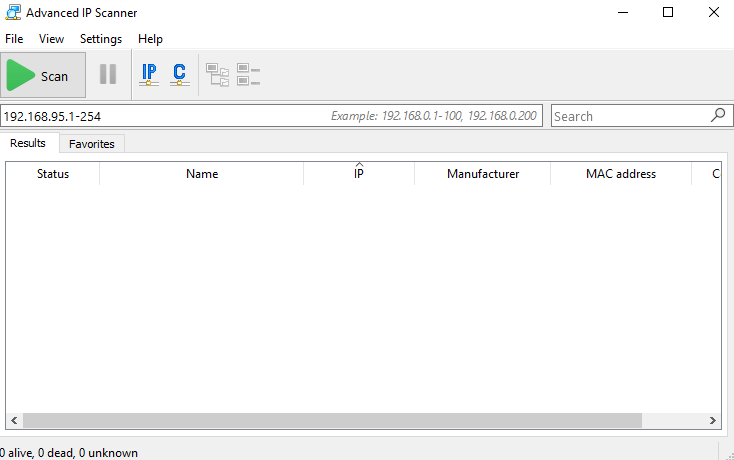
From here we will map goals to carry out the next stages.
In the next stage, the attacker will execute the pre-loaded payload or use a loader like GuLoader to download. payload. payload. These payloads can be executed via scheduled tasks, new services, or by remote execution tools (PsExec-like).

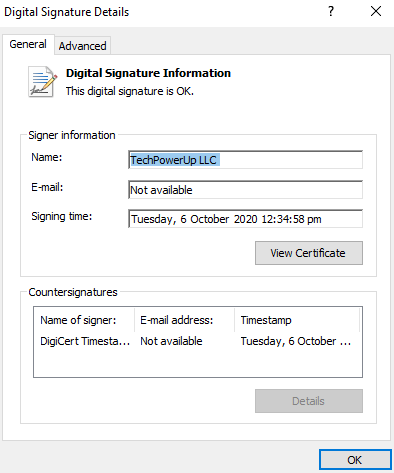
The attacker then continues to create a hidden local account, create an auto-start service, and add Run keys to the registry to maintain access. Makop uses a series of LPE vulnerabilities, or they will exploit known Windows vulnerabilities (old CVEs). A special point at this stage is that the attacker will install a driver with a valid signature but with vulnerabilities to execute code in the kernel, turning off AV/EDR.
To easily install additional Backdoors, attackers will disable the security system.
Next, the Makop malware will move to the avoidance and sabotage phase, where the malicious code is placed in a disguised folder (such as desktop, music folder) or named like a legitimate process such as: taskmgr.exe, mc_osn.exe to avoid detection.
Finally, once he has full control over the system and removes the security software, Makop will delete Volume Shadow Copies / system restore points to prevent restore. The attacker's aim would be to encrypt data and leave a ransom note.
Main impact of malicious code
Risk of paralysis of entire operations because the server system is encrypted.
Loss of important data without offline backup.
Data leak occurs if the attack group chooses the “double extortion” model.
Huge financial losses due to operational disruptions, loss of customers, and compliance fines.
Mapping tóm tắt sang MITRE ATT&CK
Initial Access: T1078 (Valid Accounts), T1110 (Brute Force)
Execution: T1059 (Command and Scripting Interpreter), T1106
Persistence: T1547 / T1543 (Registry Run Keys; Services)
Privilege Escalation: T1068 (Exploitation for Privilege Escalation), BYOVD (kernel exploitation patterns)
Defense Evasion: T1562 (Impair Defenses), T1222 (File and Directory Permissions Modification)
Discovery: T1046 (Network Scanning)
Lateral Movement: T1021 (Remote Services), T1077 (Windows Admin Shares)
Collection / Exfiltration: T1560, T1041 (optional)
Impact: T1486 (Data Encrypted for Impact), T1490 (Inhibit System Recovery)
Conclude
Makop ransomware is not a technically sophisticated line of malware, but its simplicity, durability, and focus on exploiting businesses' most common weaknesses make it a dangerous and difficult threat to eliminate. Most Makop attacks originate from vulnerabilities that organizations can completely prevent, especially opening RDP to the Internet, using weak passwords, lack of monitoring mechanisms, and insecure backups.
In the context of ransomware groups increasingly tending to industrialize their operating models, Makop is a clear demonstration of how even a small error in configuration can lead to serious consequences - from operational disruption, loss of important data, to heavy financial losses. This highlights that effective defense does not necessarily require complex technology, but rather lies in maintaining information security discipline, reinforcing basic configurations and applying sound security processes.
The fight against ransomware is a long-term journey, and success will only come when organizations view information security as a core part of operations, not just a post-incident response. With a multi-layered defense strategy and proper awareness, Makop will only be an "easy to resolve" threat, instead of becoming a disaster for the entire system.
Recommended
Enhanced RDP security (highest priority)
Turn off RDP if not needed.
If you must use RDP:
Switch default port 3389 → custom port.
Enable Network Level Authentication (NLA).
Only allow RDP through VPN, do not open directly to the Internet.
Limit IP access allowed (Dynamic Firewall Rules).
Turn on brute-force protection.
Set up Account Lockout Policy.
Use a firewall with Geo-blocking (unnecessary country blocking).
Account security – identity management
Use strong passwords + MFA.
Disable or rename the default Administrator account.
Apply the Least Privilege model.
Protect Endpoints & Servers
Fully updated operating system and software.
Install new generation EDR/Antivirus.
Block deletion of shadow copies.
Personnel training – Security Awareness
Periodic training on:
Identify phishing emails.
It's safe to use RDP remotely.
Do not download crack files or strange tools.
Report the problem immediately.
IOC
Makop ransomware
8ccb30606e3229ff88b3b67a5f4b2b087cab290ce7eedfcb24d1d3954b01d5f9
f43b86ff363f19f26cc7d80aa64fa0894a264a736ae0abd013d98e344637e4d8
0e3c6b3366640989979ae059b768586ff1d8ba4c4b96b49b40609cdaa871363c
Hash
10ea5ac09ec72101c6f8656f3f08f6f9495f8b43849f27928efd6485cee04913
6752d24da3565761c94ab10d3010e1be702221783f9b509209f97a8e32003767
aac0c5ad612fb9a0ac3b4bbfd71b8931fc762f8e11fdf3ffb33ef22076f9c4bc
0a4a0f0df5eea57f16a76bff6489dd95a7089afba8e9e5c8bcadc46870af33fb
a903f4d8f126a830b8f12e05c035b86e4dfd65cb1fd64d0d0b503035b49d0cb7
6cf6dd6119abcb2751c2692fb93a623b5b4bd290cb3dc217fa9fe09dd721fcdd
7470ae5b55ca282695d2f7c4896344622c94292a915aa63e55000beeb2c1350e
ca08299002fa6181d249115907ee29356e698d72ff06afdca05431c1ed38db35
fb1dd40577af7ac4d8c32506e78e39841ff6d05ee643c18270ef26eac798df3f
0745633619afd654735ea99f32721e3865d8132917f30e292e3f9273977dc021
5b9407df404506219bd672a33440783c5c214eefa7feb9923c6f9fded8183610
c7e471218b00cdec4f7845a80f1c5b069ee97bf270f878ea45b2dd53aad14798
0d468fa92767ca1abe881155224d94879b575860e403636d3dbb550e9b9a6a7a
5994db4362ded8bf15f81f134e14b9ed581cd2e073709b5fae6b2363bae455e9
f181b8ae88f6c657c3ec3d1d5e8420fbf340c543b3d9292947ae035e3591b664
43c3b5dbc18ebbc55c127d197255446d5f3e074fdac37f3e901b718acbe7c833
20c730c7033b5bdc0a6510825e90449ba8f87942d2d7f61fa1ba5f100e98c141
1ef6c1a4dfdc39b63bfe650ca81ab89510de6c0d3d7c608ac5be80033e559326
feb09cc39b1520d228e9e9274500b8c229016d6fc8018a2bf19aa9d3601492c5
bd1f381e5a3db22e88776b7873d4d2835e9a1ec620571d2b1da0c58f81c84a56
5b7b280b53ff3cf95ead4fd4a435cd28294c5fce6a924ec52e500a109deb868b
16f83f056177c4ec24c7e99d01ca9d9d6713bd0497eeedb777a3ffefa99c97f0
5caacdc577c27110f639d4d7c0241607c1bc53ee6f5dbd337793d05cc57e703f
41a328c3bb66e94d73e861699a5ebc4a5c0c7fcee2129e5ecd98c7bde1f95e8e
bd2c2cf0631d881ed382817afcce2b093f4e412ffb170a719e2762f250abfea4
eaa9dc1c9dc8620549fee54d81399488292349d2c8767b58b7d0396564fb43e7
37d2a1626dc205d60f0bec8746ab256569267e4ef2f8f84dff4d9d792aa3af30
1845fe8545b6708e64250b8807f26d095f1875cc1f6159b24c2d0589feb74f0c
ffa28db79daca3b93a283ce2a6ff24791956a768cb5fc791c075b638416b51f4
a332f863da1709b27b62f3a3f2a06dca48c7dabe6b8db76ec7bb81ce3786e527
3cc5ee93a9ba1fc57389705283b760c8bd61f35e9398bbfa3210e2becf6d4b05
61c0810a23580cf492a6ba4f7654566108331e7a4134c968c2d6a05261b2d8a1
8c57b97b04d7eabbae651c3400a5e6b897aea1ae8964507389340c44b99c523a
a8bf7da7e2f62296985e1aadbac8373f5ac813ac158047f5b5579a3f900fd85b
3fa65f17518d10af9ed316fbd0395bf39b3b75a63a5374ff071cbba4b642e4a3
6e95adda5f24fdf805ad10ae70069484def3d47419db5503f2c44b130eedf591
e97bdf7fafb1cb2a2bf0a4e14f51e18a34f3ff2f6f7b99731e93070d50801bef
76f88afe7a18e3583bfcc4aed3b3a0ca8a9c18c62ee5f4d746f8da735c47a5e3
3902165d0645afdb4b7d95f5cc55d65ecee17d3b77a31d51170e0beae3fd296a
b044c6dbd55747c3592ac527215c3dbf71f92aa4bd8eee5e29ddad571b9335b4
4c6cf8dda0c55fafab37569d2e11621c42e17f37a290b13087215190f7518d73
10c0dd2878bd0ab9732cd593febf61d94bb2b798bf0aa1c8fa45ddf8c7092cbc
17fb52476016677db5a93505c4a1c356984bc1f6a4456870f920ac90a7846180
51fd557a7325dd58cfcabebbbc33ef452d93f812c189360d4f2bf87c6df0a59c
c7d994eb2042633172bd8866c9f163be531444ce3126d5f340edd25cbdb473d4
f47e3555461472f23ab4766e4d5b6f6fd260e335a6abc31b860e569a720a5446
dd748db20e3909596ab18ce3f0b1264e2cfe9f67dfb4bce7d4f9c085ec1fce0a
92c65b58c4925534c2ce78e54b0e11ecaf45ed8cf0344ebff46cdfc4f2fe0d84
3da3b704547f6f4a1497107e78856d434a408306b92ba7c6e270c7c9790aa576
a1a6005cc3eb66063ae33f769fc2d335487b2ed7f92c161e49ad013ffed11ec8
8b9c7d2554fe315199fae656448dc193accbec162d4afff3f204ce2346507a8a
be2b45b7df8e7dea6fb6e72d776f41c50686c2c9cfbaf4d456bcc268f10ab083
722fff8f38197d1449df500ae31a95bb34a6ddaba56834b13eaaff2b0f9f1c8b
26d5748ffe6bd95e3fee6ce184d388a1a681006dc23a0f08d53c083c593c193b
4b036cc9930bb42454172f888b8fde1087797fc0c9d31ab546748bd2496bd3e5
f20721945a0a4150470e63bc81c9316cbb5802a60615ae4393283273a62cf8a2
de903a297afc249bb7d68fef6c885a4c945d740a487fe3e9144a8499a7094131
37ff328175acd45ef27d3d339c3127a7612ad713fccd9c9aae01656dfbf13056
8f7569e82bd339f3e24431884687b095f678971f20053787d93359672bb9f687
5cdabf41672241798bcca94a7fdb25974ba5ab2289ebadc982149b3014677ae3
b5c2474397fb38a4dd9edab78b6e5178832074ba5bab9bac3f0cad7bc0660cf2
5ff803269d6491dd3f0267f6f07b8869e3f08d62cf2110b552bba2cc3d75d26a
c8afb68260b9036d8e65811927c379112274a2526cc161c7f1502457a501a0d3
01f34180bb635022681723eef73c19adf330d7a32a2e6639c27b1ee5777312be
c8e8cca4ee3c4f4ce4f2076ed93cca058fa1ff88d5ffe49d8d293b27ad25ef68
8315327f22eff069457c02ddda1ea32a31964e1b8ab688709bcb96c6ccbb6212






