XWorm Backdoor Returns with a New Variant and Sophisticated Phishing Campaign
New versions of the backdoor XWorm are being widely distributed in phishing campaigns after the original developer XCoder abandoned the project last year.
The latest variants — XWorm 6.0, 6.4, and 6.5 — are currently being exploited by multiple threat actor groups. These versions support extended plugins, allowing for a range of malicious activities such as data theft, remote system control, file encryption, or conducting DDoS attacks.
The final version developed by XCoder was XWorm 5.6, which had a RCE (Remote Code Execution) vulnerability that has now been patched in the new updates.
1. From a Versatile RAT to a Hacker's "All-in-One Tool"
First discovered in 2022, XWorm quickly gained fame in the cyberattack community due to its flexible modular architecture and high scalability.
Initially, it was used for:
Collecting sensitive data (passwords, cryptocurrency wallets, financial information)
Keylogging
Stealing clipboard data
Downloading and executing additional malware
Additionally, XWorm can perform DDoS attacks and create remote access backdoors.
When XCoder deleted his Telegram account—where he used to share updates—many threat actors released cracked versions of XWorm. One attack group even exploited XWorm itself to install backdoors to steal data from less experienced hackers, leading to over 18,000 infections worldwide, concentrated in Russia, the US, India, Ukraine, and Turkey.
2. New Distribution Method: From .LNK to PowerShell Loader
Since June, researchers at Trellix have noted a significant increase in XWorm samples on VirusTotal, indicating its growing popularity.
New variants are being promoted on hacker forums by the account “XCoderTools”, offering lifetime licenses for $500 USD. Although the true identity of the account is unknown, the person claims to have fixed the RCE vulnerability and added many new features.
A typical phishing campaign starts with a .lnk (shortcut) file containing a Base64-encoded PowerShell command. When the victim opens the file:
PowerShell downloads the file
Discord.exe(a .NET file masquerading as the Discord app).Discord.exethen drops two malicious files,main.exeandsystem32.exe.system32.exeis the XWorm payload that executes last.
The goal of this chain is to deeply embed itself in the system, deceive users with a legitimate file name (system32.exe), and bypass antivirus monitoring.
3. Technical Analysis
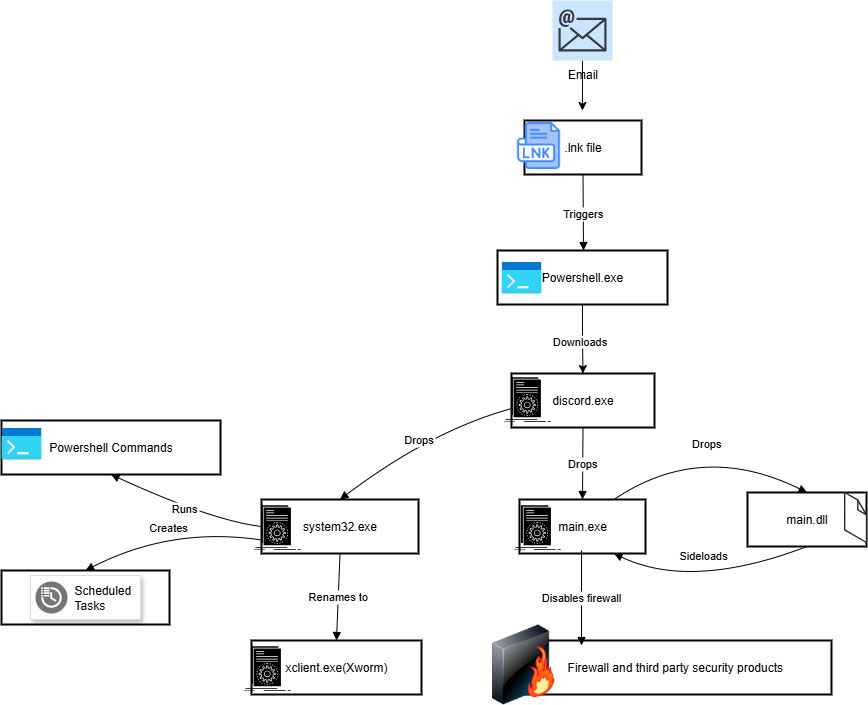
.lnk File
Contains a Base64-encoded PowerShell script that downloads and runs Discord.exe from the address hxxp://85[.]203[.]4[.]232:5000/Discord.exe.
Discord.exe
Is a .NET file with a legitimate Discord icon, using strong packing techniques to avoid detection. After running, it creates:
main.exesystem32.exe
The name “system32.exe” is deliberately chosen to disguise itself as a real system process.

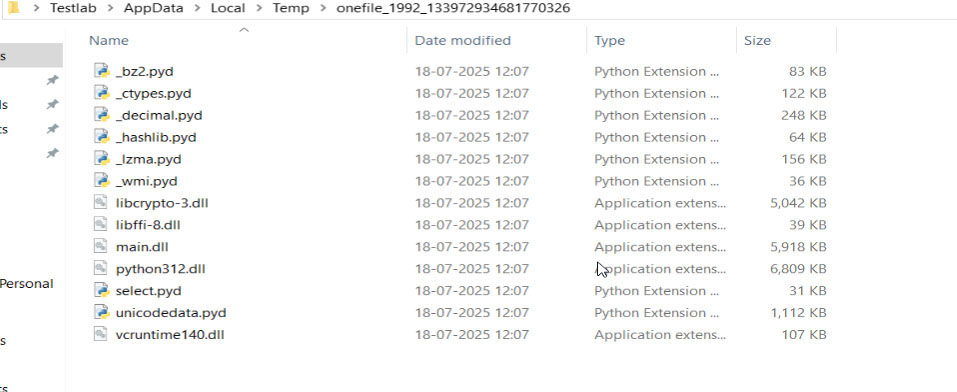
main.exe
Contains several .pyd modules (Python Dynamic Module) and main.dll, compiled with Nuitka, making it difficult to reverse engineer.
Main functions:
Disable Windows Firewall
Check and disable security tools
Write registry key at:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\WindowsFirewall\DisableFirewall
main.dll
There is only one export function run_code, along with two TLS callbacks to execute code before the entry point, increasing the ability to evade sandbox detection.
system32.exe (XWorm Payload)
Check for virtual environments (VMware, VirtualBox). If detected, the process will self-destruct (failfast).
If in a real environment, it copies itself as Xclient.exe, adding to the antivirus exclusion list via PowerShell:
Add-MpPreference -ExclusionPath Add-MpPreference -ExclusionProcessCreate Scheduled Task "XClient" to run every minute.
Write auto-start Registry key:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\XClient
Encryption & Data Hiding Mechanism
XWorm uses the Rijndael algorithm (the predecessor of AES) combined with Base64 to encrypt C2 data (IP, domain, port) and internal strings.
This combination secures communication and makes reverse engineering difficult.
Anti-Analysis Mechanism
Creates a mutex “1JJyHGXN8Jb9yEZG” to prevent multiple parallel runs.
Checks for virtualization signs and stops immediately if a sandbox is detected.
Collects system information (machine name, manufacturer, model) to send back to C2.
Backdoor Commands
From C2, an attacker can:
Shut down/restart the system
Upload/download files
Open malicious URLs
Trigger DDoS
Execute commands in hidden
cmd.exe
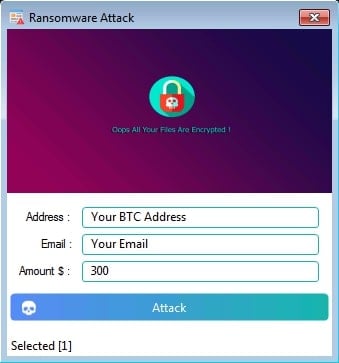
4. Ransomware Module and Extension Plugins
According to Trellix, XWorm currently has over 35 plugins, including:
Ransomware.dll: encrypts files, changes wallpaper, displays ransom note.
Data is locked in the
%USERPROFILE%andDocumentsfolders.Added extension:
.ENCContact information (BTC, email) is saved in an HTML file on the Desktop.

Stealer Modules: steals login information from over 35 applications, including browsers, cryptocurrency wallets, FTP, email, and messaging apps.
RemoteDesktop.dll: allows remote control of the victim's machine.
FileManager.dll, Shell.dll, Informations.dll, Webcam.dll: manage files, execute hidden commands, gather information, and record video from the webcam.
Some code segments in the ransomware module show a high level of similarity with the NoCry malware (2021), using the same AES-CBC 4096 byte algorithm and analysis environment checking mechanism.
5. Conclusion and Recommendations
XWorm has shifted from familiar spreading methods to more sophisticated disguise techniques, combining social engineering and technical attacks for maximum effectiveness.
The infection chain no longer relies on .bat, .vbs, or .hta — it directly drops executable files disguised as legitimate software.
This indicates that XWorm has entered a new phase of development, becoming a versatile attack platform, functioning as a RAT, ransomware, and stealer.
FPT Threat Intelligence provides the following recommendations:
Implement multi-layered defense.
Use EDR to detect abnormal behavior, such as creating Scheduled Tasks, modifying the Registry, or running encoded PowerShell.
Add email/web protection layers to block malware at the distribution stage.
Monitor network traffic to detect unusual connections to C2 servers.
Update the IOC list for XWorm.
XWorm clearly demonstrates how "underground open-source" malware can quickly mutate when in the hands of various attackers — turning an old attack tool into a polymorphic, unpredictable, and continuously evolving threat.
6. IOC
| MD5 | Filenames |
| c2f66498298c1af28da64eb5392a4a6e | .lnk file |
| 4e98e45377fbf1390676ca36dbef0b85 | Discord.exe |
| cb3241ff094bb1292dc7841148a7431e | main.exe |
| 7c1129af104acf9cc4c0793077e9c5df | main.dll |
| 72eb8c4ffd6d5f721ed3ee121264b53f | System32.exe |
C2 server:
- 85[.]203[.]4[.]232






