Zhong Stealer: A Threat to Fintech and Crypto via Zendesk Platform
Just a SOC Analyst ^^
A newly identified malware, named Zhong Stealer, has emerged as a significant threat to the fintech and cryptocurrency sectors. Attackers exploit chat support platforms like Zendesk, posing as customers to trick support staff into downloading the malware.
Zhong Stealer's Attack Method
The attack pattern of this malware can be described through the following steps:
First, the attacker creates a support ticket from a new account.
These tickets often include messages written in Chinese.
Attached to this ticket are ZIP files containing screenshots or additional details.
The attacker requests the support staff to open it and acts frustrated when they refuse. The attacker uses social engineering techniques to manipulate the technical staff's psychology, pressuring them to open the malicious file.
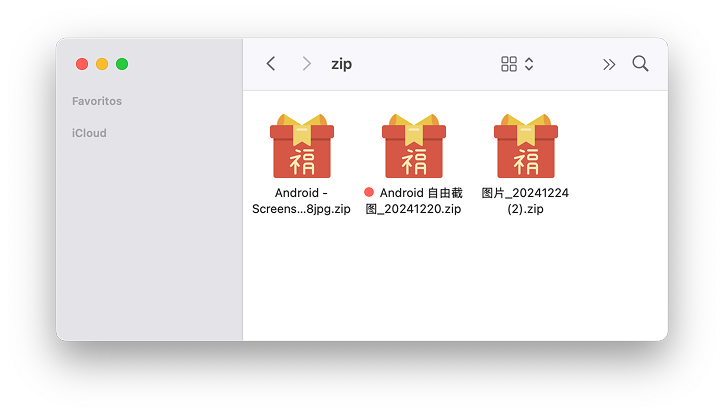
Figure 1. Suspicious ZIP files named in Simplified Chinese characters
Malware researchers have collected several suspicious ZIP file samples, all named in Simplified Chinese characters:
图片_20241224 (2).zip (Image_20241224 (2).zip)
Android 自由截图_20241220.zip (Android Free Screenshot_20241220.zip)
Android – Screenshots2024122288jpg.zip
After extracting the ZIP files, they all contain an EXE file inside:
图片_20241224.exe (Image_20241224.exe – Simplified Chinese)
圖片2024122288jpg.exe (Image2024122288jpg.exe – Traditional Chinese)
图片_20241220.exe (Image_20241220.exe – Simplified Chinese)

Figure 2. Suspicious EXE files named in Simplified and Traditional Chinese characters
Zhong Stealer Malware Analysis
Researchers used ANY.RUN to analyze Zhong Stealer. When this malware runs, it queries a C2 server based in Hong Kong, hosted by Alibaba Cloud.
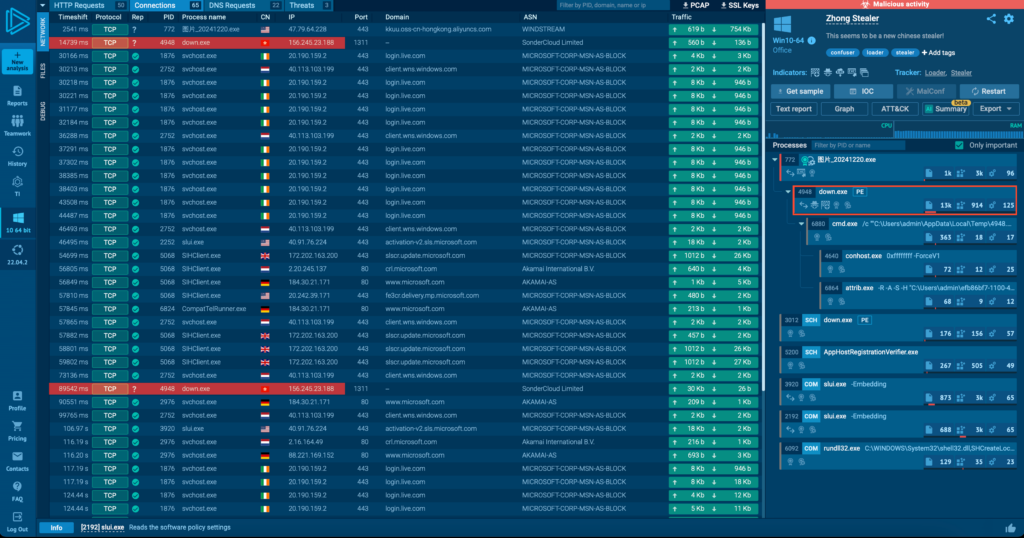
Figure 3. Initial connection behavior to the C2 server in Hong Kong
Stage 1: Initial Communications
The first action involves reading a TXT file, which contains links to itself and other malicious components that need to be downloaded.
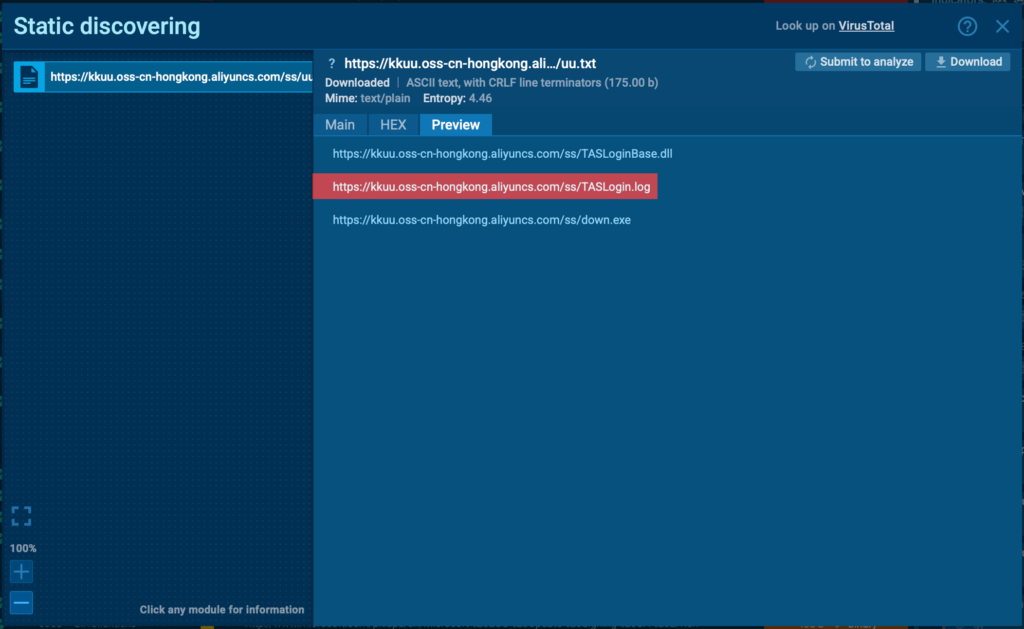
Figure 4. TXT file containing components of the malware to be downloaded
Stage 2: Downloader Execution
Next, a file named down.exe is downloaded. This file was previously signed with a valid certificate but has now been revoked from Morning Leap & Cazo Electronics Technology Co., indicating that the file may have been stolen. Notably, this file disguises itself as a BitDefender Security updater to avoid suspicion.
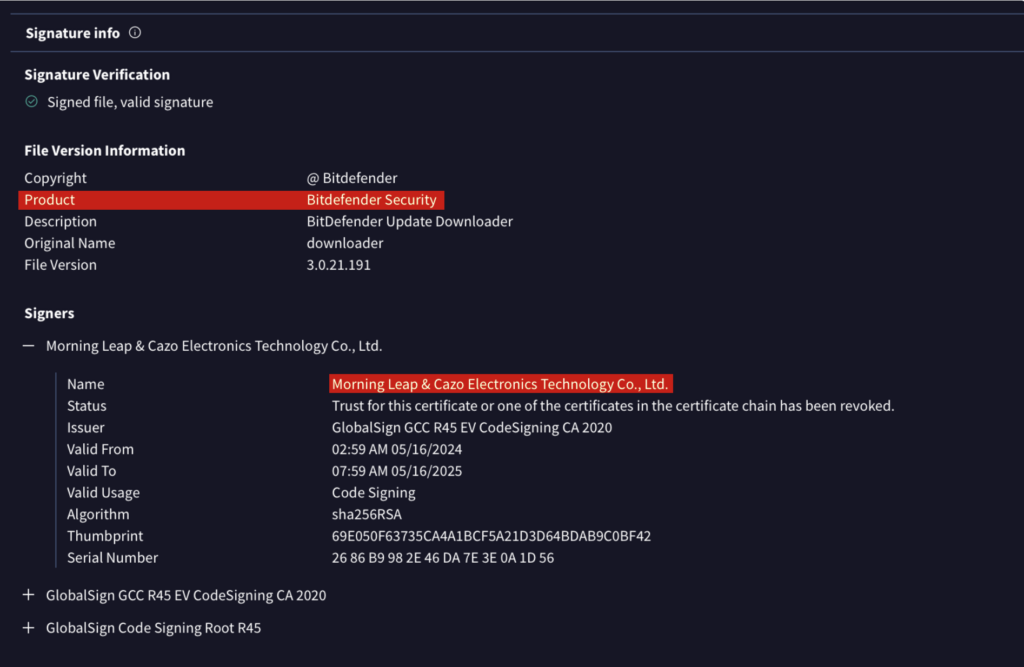
Figure 5. Fake BitDefender Signature
In this stage, Zhong downloads additional components:
TASLogin.log (log file)
TASLoginBase.dll (dynamic link library)
Stage 3: Persistence and Reconnaissance
After running, down.exe creates a BAT file with a name of four random digits in the user's TEMP directory (e.g., 4948.bat). This script sets up the environment by calling system utilities like Conhost.exe and Attrib.exe to grant execution rights for the next step.
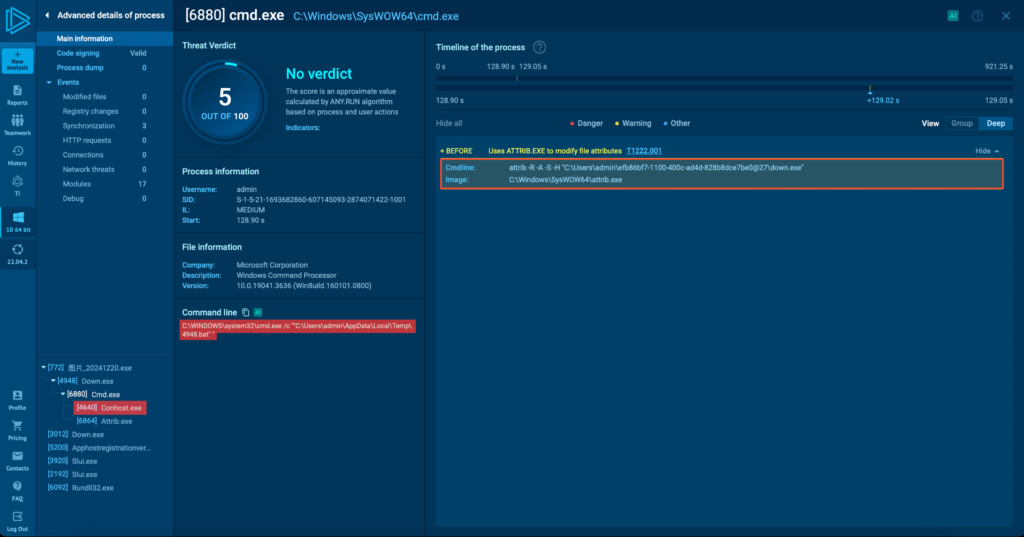
Figure 6. BAT file setting up the environment for the next steps
The attacker then queries the languages used by the system, a tactic commonly seen in ransomware. It is used to avoid targeting specific regions, reducing the risk of investigation by local authorities. It also schedules itself to run periodically through Task Scheduler, serving as a backup persistence method.
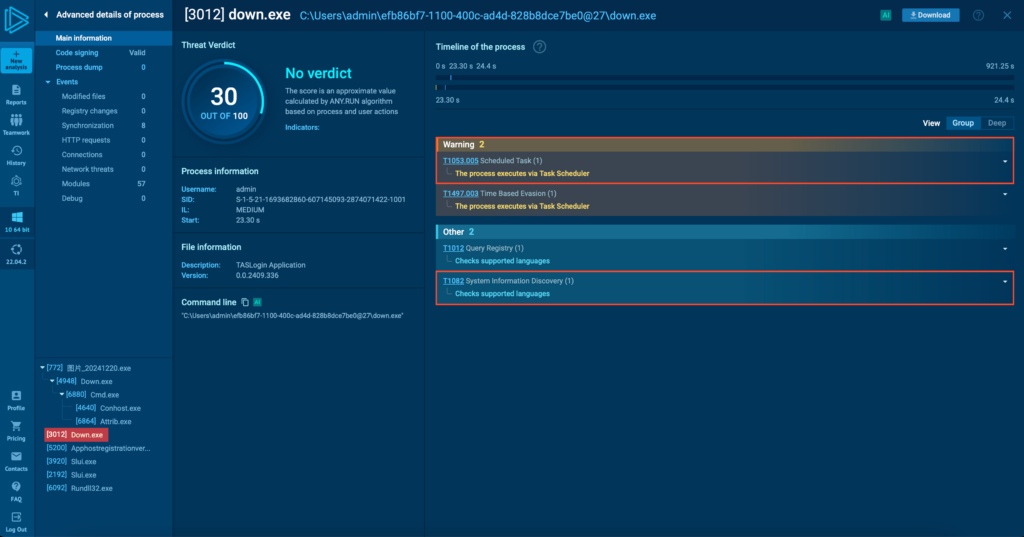
Figure 7. Zhong self-scheduling through Task Scheduler and checking system language
Next, Zhong disables trace logs (part 1 in the figure below) and initiates system reconnaissance processes. This includes reading registry keys to gather information such as hostnames, GUIDs, proxies, software policies, and supported languages (parts 2 and 3). It also evaluates Internet Explorer/Edge security settings (part 4).
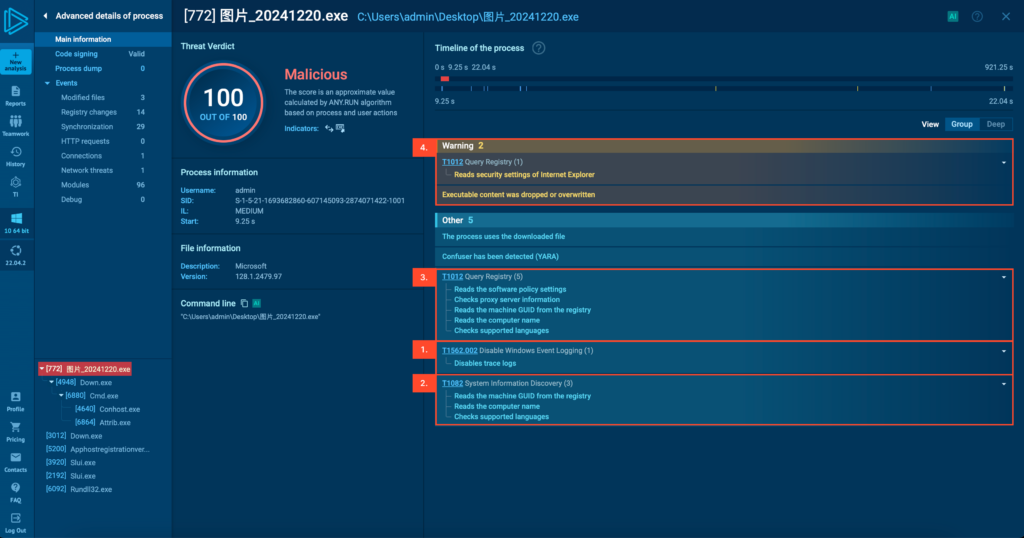
Figure 8. Zhong stealer's preparation, reconnaissance, and evasion steps in practice
Stage 4: Credential Theft and Data Exfiltration
From this stage, the malware begins its main actions. Zhong establishes persistence on the system by adding a registry key (part 1 in the figure below) at:
HKEY_CURRENT_USER\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Next, it collects browser credentials and extension data (part 2) before connecting to its C2 server on port 1131 (part 3) to exfiltrate the stolen information.
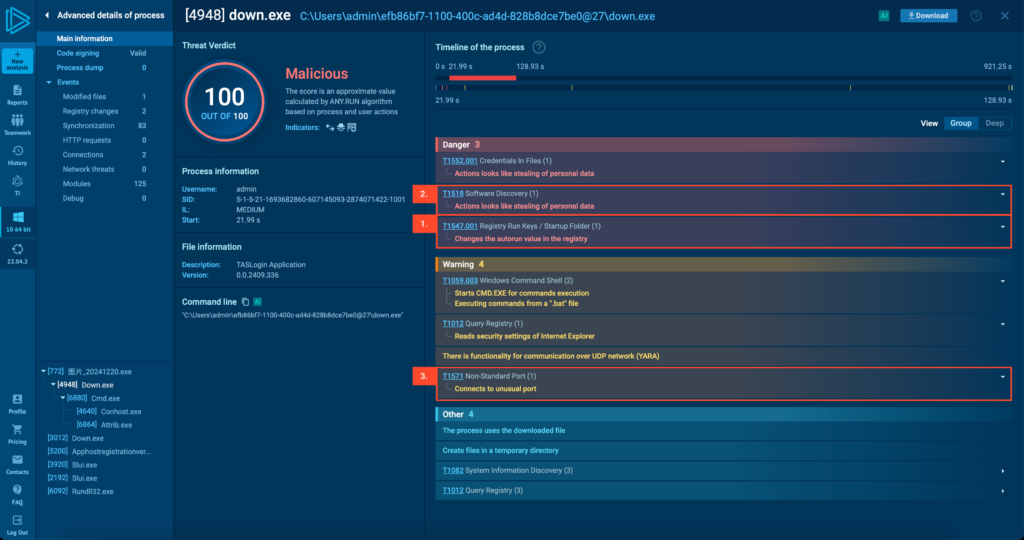
Figure 9. Steps of persistence, stealing information, and communicating with the C2 server of the malware
The Zhong Stealer campaign highlights the increasing sophistication of cyber threats targeting fintech and cryptocurrency companies. The malware's ability to steal login credentials and sensitive data poses a serious risk to organizations handling financial transactions and digital assets.
IOCs Related to Zhong Stealer Malware
File hash
| 778b6521dd2b07d7db0eaeaab9a2f86b | MD5 |
| ce120e922ed4156dbd07de8335c5a632974ec527 | SHA1 |
| 02244934046333f45bc22abe6185e6ddda033342836062afb681a583aa7d827f | SHA256 |
| 1abffe97aafe9916b366da57458a78338598cab9742c2d9e03e4ad0ba11f29bf | SHA256 |
| 4eaebd93e23be3427d4c1349d64bef4b5fc455c93aebb9b5b752981e9266488e | SHA256 |
| dd44dabff536a1aa9b845dd891ad483162d4f28913344c93e5d59f648a186098 | SHA256 |
| e46779869c6797b294cb097f47027a5c52466fd11112b6ccd52c569578d4b8cd | SHA256 |
URL
| hxxps://kkuu.oss-cn-hongkong.aliyuncs[.]com/ss/TASLogin.log |
| hxxps://kkuu.oss-cn-hongkong.aliyuncs[.]com/ss/TASLoginBase.dll |
| hxxps://kkuu.oss-cn-hongkong.aliyuncs[.]com/ss/down.exe |
| hxxps://kkuu.oss-cn-hongkong.aliyuncs[.]com/ss/uu.txt |
zhongmaziil992@outlook.com |
Hostname
kkuu.oss-cn-hongkong.aliyuncs[.]com |
IP
| 156.245.23.188 |
| 47.79.64.228 |
Recommendations
FPT Threat Intelligence recommends organizations and individuals take several measures to prevent this malware:
Education and Awareness: Train employees to recognize phishing tactics and avoid opening suspicious attachments.
Limit Opening ZIP Files from Unverified Sources: Prevent opening ZIP files from untrusted sources and apply a "zero-trust" security policy to prevent unauthorized access.
Monitor Outbound Network Traffic: Monitor network traffic to detect suspicious C2 connections, especially those using non-standard ports like 1131, a key indicator of Zhong Stealer activity.
Analyze Executable Files in a Safe Environment: Use malware analysis tools to examine the behavior of unidentified executable files.
Use Advanced Behavioral Analysis: Apply advanced behavioral analysis methods to proactively prevent new threats.






