UAT-8302 — China-Nexus APT Targets Governments with a Shared Malware Arsenal
1. Campaign Summary
On May 5, 2026, Cisco Talos published a comprehensive analysis of UAT-8302 — a China-nexus advanced persistent threat group targeting government entities in South America (from at least late 2024) and Southeastern Europe (2025). The defining characteristic of this actor is not a unique malware family: UAT-8302 deploys a set of tools shared across multiple China-nexus APT clusters, reflecting a centralized tool-sharing model among groups operating under common tasking.
The most technically notable component is NetDraft — a .NET variant of the FINALDRAFT/SquidDoor backdoor that uses Microsoft Graph API and OneDrive as C2 infrastructure. UAT-8302 also deploys CloudSorcerer v3 (reading C2 from GitHub/GameSpot profiles), VSHELL via the SNOWLIGHT stager, and a newly identified Rust-based stager tracked as SNOWRUST. The operational objective is consistent across all targets: establish and maintain long-term persistent access, harvest credentials, and exfiltrate information from government environments.
Attribution: Cisco Talos — HIGH confidence. UAT-8302's tooling links directly to Jewelbug/REF7707/CL-STA-0049, LongNosedGoblin (ESET), Earth Estries, Earth Naga, UNC5174, and UAT-6382.
Regional relevance: Southeast Asia is an established target of multiple clusters within this same APT ecosystem — LongNosedGoblin has attacked government organizations in Southeast Asia and Japan using the same NetDraft/NosyDoor malware. Techniques abusing Microsoft Graph API and legitimate cloud services present a fundamental challenge for perimeter-based detection.
2. Event Timeline
| Date | Event |
|---|---|
| From March 2023 | CL-STA-0049/REF7707 (same ecosystem) attacks government, defense, telecom, aviation in Southeast Asia and South America |
| November 2024 | Elastic Security Labs discovers FINALDRAFT/PATHLOADER in REF7707 campaign targeting South American Foreign Ministry |
| February 2025 | Elastic publishes FINALDRAFT technical report; Unit 42 tracks same cluster as CL-STA-0049/Squidoor |
| Late 2024 | UAT-8302 begins targeting South American government entities |
| 2025 | UAT-8302 expands operations to Southeastern European government agencies |
| May 5, 2026 | Cisco Talos publishes comprehensive UAT-8302 report; first public disclosure of SNOWRUST (new Rust-based stager) |
| May 2026 | The Hacker News aggregates findings to broader security community |
3. Kill Chain / Attack Flow
Phase 1 — Initial Access (T1190, T1078) UAT-8302 exploits both zero-day and n-day vulnerabilities on edge devices and web servers (IIS), or leverages already-compromised valid credentials. Consistent with related clusters, certutil is used to download additional payloads via WinRM Remote Shell (WinrsHost.exe).
Phase 2 — Discovery & Reconnaissance (T1082, T1018, T1069) Immediately post-foothold, the group deploys the whatpc.ps1 recon script via a scheduled task, combined with specialized tools:
# whatpc.ps1 — run via SYSTEM-privileged scheduled task
schtasks /create /tn 'ReconLiteDebug' /tr 'powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File c:\windows\temp\whatpc.ps1' /sc ONCE /st 08:25 /ru SYSTEM /f
# Representative recon commands
whoami /groups
whoami /priv
net user /domain
net group Domain Admins /domain
nltest /domain_trusts
ipconfig /all
NETSTAT -ano
Network discovery:
# Ping sweep
for /l %i in (1,1,254) do @ping -n 1 -w 300 192.168.1.%i | find TTL= && echo 192.168.1.%i is alive > C:\Windows\Temp\alive_hosts.txt
# SMB scan
for /l %i in (1,1,254) do @net use \\192.168.1.%i\IPC$ >nul 2>&1 && echo %i open >> C:\Windows\Temp\portscan.txt
Phase 3 — Credential Access (T1003, T1552)
adconnectdump.py— credential extraction from Azure AD Connect / Entra IDSharpGetUserLoginIPRP— domain controller login information extraction (tool from Simplified Chinese repository)certutil -user -store My/CA/Root— certificate store enumerationMobaXterm SSH client credential extraction via MobaXtermDecryptor Phase 4 — Lateral Movement (T1021.002, T1047)
# WMI-based remote process creation
wmic /node:<IP> process call create "cmd.exe /c c:\programdata\e1.bat"
# Scheduled task-based lateral movement
schtasks /S <IP> /U <user> /P <pass> /create /tn 'Runbat' /tr 'c:\windows\temp\run.bat' /sc ONCE /st 5:12 /ru SYSTEM /f
Phase 5 — Persistence & Malware Deployment (T1053.005, T1574.002) Three malware families deployed concurrently via DLL sideloading:
NetDraft — .NET FINALDRAFT variant, C2 via Microsoft Graph API / OneDrive
CloudSorcerer v3 — C2 via GitHub/GameSpot dead drops → OneDrive/Dropbox backend
VSHELL — deployed via SNOWLIGHT/SNOWRUST stager, sideloaded through
wininet.dllPhase 6 — Collection & Exfiltration (T1560, T1041)Active Directory snapshots via AD Explorer (
ae.exe -snapshot)Event log collection and audit policy enumeration
Data exfiltration through established C2 channels (MS Graph API, Dropbox, OneDrive)
Full AD user/computer/group enumeration via PowerShell with complete attribute sets
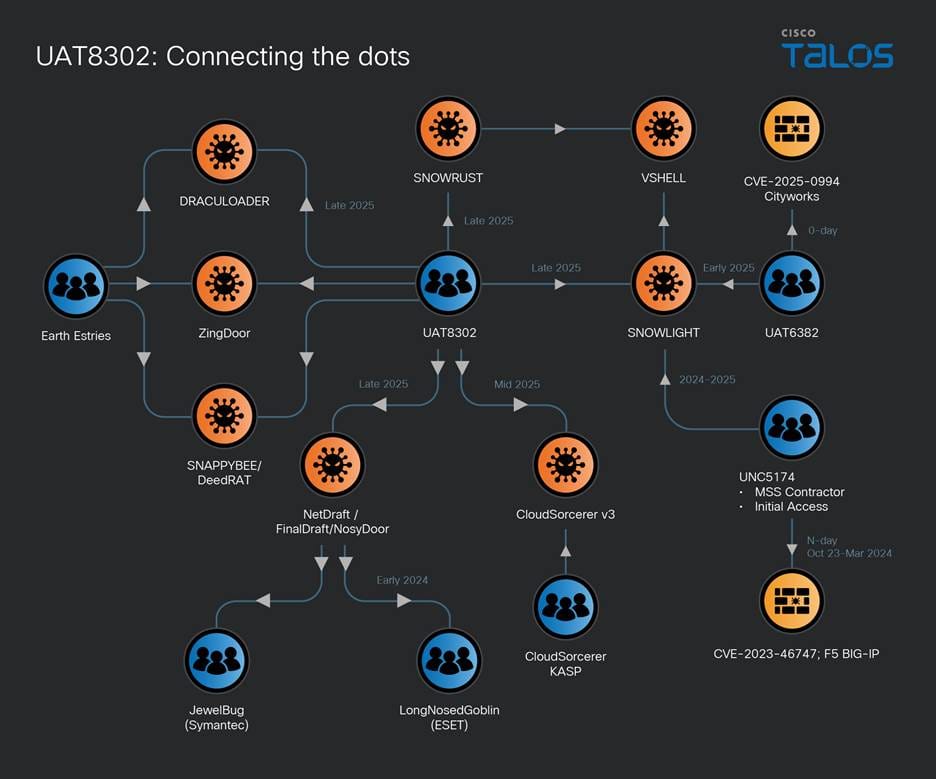
Figure 1. UAT-8302 interconnections with other China-nexus APT clusters (Cisco Talos).
4. Technical Analysis
4.1 NetDraft — .NET Variant of FINALDRAFT/SquidDoor
NetDraft (also tracked as NosyDoor by ESET) is a .NET port of the FINALDRAFT backdoor — a malware family developed and operated by the Jewelbug/REF7707/CL-STA-0049 cluster. This is the single most significant APT linkage in the campaign.
C2 via Microsoft Graph API:
FINALDRAFT/NetDraft uses Microsoft Outlook as a C2 channel by interacting with the Outlook draft email folder through the Microsoft Graph API. The operator sends commands by writing to email drafts; the bot reads the draft, executes the command, and writes results back to a new draft. This traffic is indistinguishable from legitimate HTTPS traffic to graph.microsoft.com.
NetDraft → OAuth token → Microsoft Graph API → Outlook Drafts folder
← Read commands from draft ←
→ Write command output to new draft →
NetDraft uses OneDrive (rather than Outlook) for the same purpose in some variants, storing OAuth tokens in registry paths determined by the current privilege level.
Infection chain:
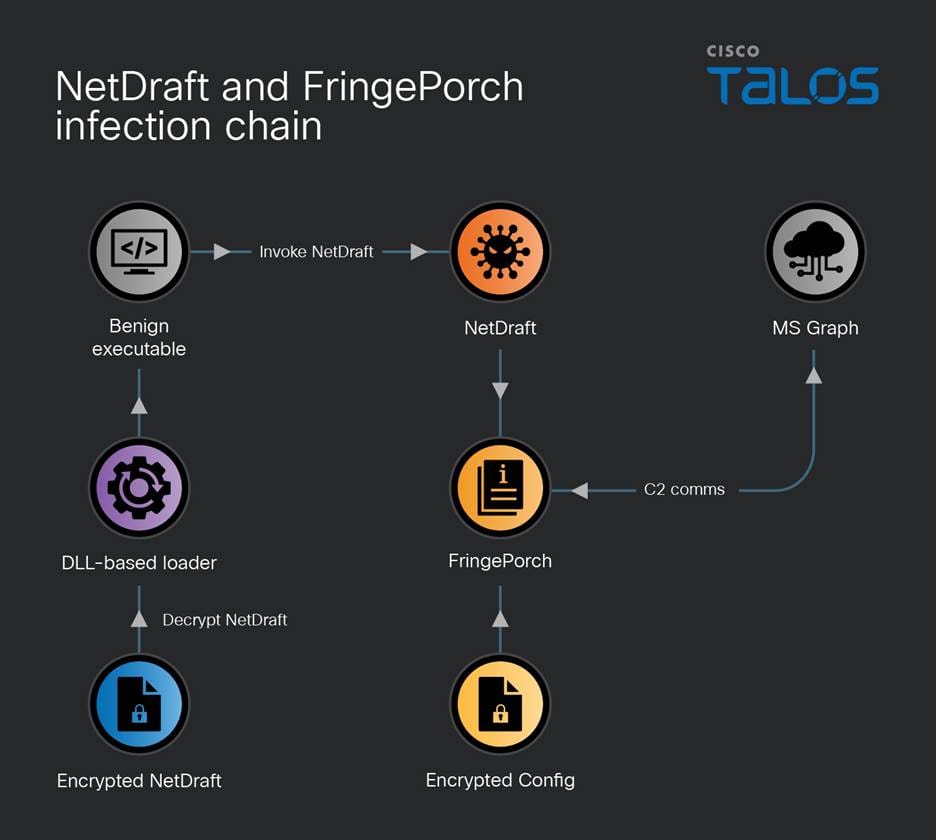
Figure 2. NetDraft and FringePorch infection chain (Cisco Talos).
Benign executable sideloads a malicious DLL loader
DLL loader decodes NetDraft from an accompanying data file
NetDraft executes within the context of the legitimate process
Embedded library FringePorch (compressed via Fody/Costura framework) is decompressed and instrumented at runtime NetDraft + FringePorch capabilities:
Execute arbitrary commands on the endpoint
Execute .NET assemblies sent by the C2 within NetDraft's process context
File upload/download to and from C2
File management (rename, enumerate, set write timestamps)
Execute .NET plugins via
Plugin.RunBecause NetDraft lacks a built-in persistence mechanism, the C2 immediately issues a scheduled task creation command upon establishing a connection:
schtasks /create /ru system /tn Microsoft\Windows\Maps\{a086ff1e-d6dc-45f7-b3e4-6udknw82sa} /sc hourly /mo 2 /tr 'C:\ProgramData\Microsoft\Microsoft\Appunion.exe' /F
APT linkage: The same NetDraft/NosyDoor was used by LongNosedGoblin to target Southeast Asian and Japanese government organizations; Erudite Mogwai/LuckyStrike Agent deployed it against Russian IT organizations in 2024.
4.2 CloudSorcerer v3
CloudSorcerer v3 is the latest iteration of the backdoor Kaspersky disclosed in 2024 — used in attacks against Russian government entities. UAT-8302 deploying this version confirms it is being actively maintained and shared or updated centrally within the ecosystem.
Deployment mechanism (DLL sideloading):
Yandex.exe -r -p:test.ini -s:12
VMtools.exe -r -p:VM.ini -s:12
Both executables sideload mspdb60.dll, which decrypts the .ini file to extract and execute CloudSorcerer v3 shellcode.
Process-name branching logic:
| Process | Action |
|---|---|
dpapimig.exe |
Collect system info, inject into explorer.exe, receive commands via named pipe |
spoolsv.exe |
Contact GitHub to obtain C2 info, receive and execute commands from C2 |
| Any other process | Inject into dpapimig.exe, spoolsv.exe to initiate the malicious chain |
C2 information retrieval: CloudSorcerer v3 reads an encoded blob from a GitHub repository or a GameSpot profile controlled by the threat actor. The decoded blob contains either:
A direct C2 URL / IP under UAT-8302 control, or
An access token to a legitimate cloud service (OneDrive or Dropbox) used as C2 backend
4.3 VSHELL via SNOWLIGHT and SNOWRUST
Infection chain:
Benign executable sideloads malicious
wininet.dllDLL reads a BIN file and injects shellcode into
explorer.exeShellcode is the SNOWLIGHT stager: downloads VSHELL payload, decodes with single-byte XOR key
0x99, executes Talos confirmed the same stager (single-byte XOR0x99) was used by UAT-6382 to deliver VSHELL via CVE-2025-0994 (Cityworks zero-day) in early 2025, and by UNC5174 and UNC6586 — confirming SNOWLIGHT as shared infrastructure.
SNOWRUST is a newly identified Rust-based stager — first tracked by Talos in this campaign — performing the same staging function as SNOWLIGHT but implemented in Rust.
4.4 Scanning & Lateral Movement Toolset
UAT-8302 employs a collection of largely open-source tools, with several originating from or written for Chinese-language developer communities:
| Tool | Function | Notes |
|---|---|---|
gogo |
Network scanner (GoLang) | Open-source, written in Simplified Chinese |
QScan |
Port scanner | Chinese-language repository |
naabu |
Port discovery | ProjectDiscovery |
dddd |
Automated recon | Chinese-language origin |
httpx |
Web service discovery | ProjectDiscovery |
nbtscan |
NetBIOS scanner | Standard tool |
SharpGetUserLoginIPRP |
DC login info extraction | Chinese-language repository |
adconnectdump.py |
Azure AD Connect credential dump | Python-based |
MobaXtermDecryptor |
SSH credential extraction | Targets MobaXterm sessions |
AD Explorer (ae.exe) |
Active Directory snapshot | Sysinternals |
| Impacket | Auth/credential attacks | Standard red-team framework |
4.5 The Tool-Sharing Ecosystem — What It Tells Us
This is the analytically most significant aspect of the Talos report. UAT-8302 does not operate in isolation — it draws from a shared tooling pool distributed across the China-nexus APT ecosystem:
| Malware/Tool | Other Clusters Using It |
|---|---|
| NetDraft/NosyDoor | Jewelbug/REF7707, LongNosedGoblin, Erudite Mogwai |
| CloudSorcerer v3 | Russian government attacks 2024 (Kaspersky) |
| SNAPPYBEE/DeedRAT + ZingDoor | Earth Estries (Trend Micro) |
| Draculoader | Earth Estries, Earth Naga |
| SNOWLIGHT + VSHELL | UAT-6382 (CVE-2025-0994), UNC5174, UNC6586 |

5. IOC & Artifacts
File Artifacts
# Malware components (representative filenames)
Appunion.exe - NetDraft loader (benign-looking name)
mspdb60.dll - CloudSorcerer malicious loader DLL
wininet.dll - VSHELL malicious loader DLL
test.ini / VM.ini - Encrypted CloudSorcerer shellcode container
*.bin - VSHELL/SNOWLIGHT payload
# Recon scripts
whatpc.ps1 - System reconnaissance PowerShell script
ping_scan.bat - Ping sweep batch file
run_scan.bat - Network scan orchestrator
nbtscan.exe - NetBIOS scanner
# Credential tools
adconnectdump.py - Azure AD Connect credential extractor
ae.exe - AD Explorer snapshot tool
S.exe - SharpGetUserLoginIPRP
C2 Infrastructure Patterns
# CloudSorcerer v3 C2 resolution chain
GitHub repository - Read encoded blob containing C2 info
GameSpot profile - Alternate dead-drop for C2 info
OneDrive / Dropbox - Cloud-based C2 backend (access token from blob)
# NetDraft C2
Microsoft Graph API - graph.microsoft.com over HTTPS (indistinguishable from legitimate traffic)
OneDrive - File-based C2 communication channel
Scheduled Task Artifacts
# NetDraft persistence
Task name: Microsoft\Windows\Maps\{a086ff1e-d6dc-45f7-b3e4-6udknw82sa}
Command: C:\ProgramData\Microsoft\Microsoft\Appunion.exe
Schedule: Hourly, every 2 hours
Run as: SYSTEM
# Reconnaissance task
Task name: ReconLiteDebug / RunWhatPC
Command: powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File c:\windows\temp\whatpc.ps1
Run as: SYSTEM
6. MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Initial Access | Exploit Public-Facing Application | T1190 | IIS web shell, edge device exploitation |
| Initial Access | Valid Accounts | T1078 | Pre-compromised valid credentials |
| Execution | Windows Management Instrumentation | T1047 | WMI remote process creation |
| Execution | Scheduled Task/Job | T1053.005 | Lateral movement + malware execution |
| Persistence | Scheduled Task/Job: Scheduled Task | T1053.005 | NetDraft hourly persistence task |
| Privilege Escalation | Hijack Execution Flow: DLL Side-Loading | T1574.002 | NetDraft, CloudSorcerer, VSHELL |
| Defense Evasion | Masquerading | T1036 | Benign-looking executable filenames |
| Defense Evasion | Obfuscated Files or Information | T1027 | Encrypted shellcode in .ini/.bin files |
| Credential Access | OS Credential Dumping | T1003 | Impacket, adconnectdump.py |
| Credential Access | Credentials from Password Stores | T1555 | MobaXtermDecryptor |
| Discovery | Account Discovery: Domain Account | T1087.002 | LDAP queries, PowerShell AD cmdlets |
| Discovery | Network Service Discovery | T1046 | gogo, naabu, httpx, QScan, dddd |
| Discovery | System Information Discovery | T1082 | whatpc.ps1, systeminfo |
| Lateral Movement | Remote Services: SMB/WMI | T1021.002 | WMI + schtasks lateral movement |
| Collection | Archive Collected Data | T1560 | 7zip compression of AD snapshot |
| Collection | Data from Local System | T1005 | Event logs, AD snapshot, credentials |
| C2 | Application Layer Protocol: Web Protocols | T1071.001 | HTTPS to MS Graph API |
| C2 | Web Service: Dead Drop Resolver | T1102.001 | GitHub/GameSpot → C2 resolution |
| C2 | Web Service: Bidirectional Communication | T1102.002 | OneDrive/Dropbox/Outlook drafts |
| Exfiltration | Exfiltration Over C2 Channel | T1041 | Via MS Graph API / cloud service |
7. Expert Assessment
UAT-8302 is the clearest current demonstration of the contractor ecosystem model in Chinese state-sponsored APT operations: rather than each group maintaining its own isolated toolset, clusters draw from a shared development pool — likely maintained by a centralized development team or distributed through a structured sharing arrangement among groups operating under common state tasking.
The C2 technique via Microsoft Graph API and Outlook drafts is among the stealthiest approaches documented in 2025–2026. No perimeter device can distinguish NetDraft's graph.microsoft.com:443 traffic from a legitimate user's Outlook session — same endpoint, same certificate, same port. Detection is only viable at the endpoint level (anomalous process making Graph API calls) or at the identity layer (unexpected OAuth token issuance, unauthorized OAuth app consent).
One observation worth highlighting: the same malware family (FINALDRAFT/NetDraft/NosyDoor/Squidoor) was independently discovered by three separate research teams (Elastic, ESET, Unit 42) and given different names before Talos synthesized the picture. This reflects the operational breadth of these clusters — enough simultaneous activity across different geographic regions that multiple TI teams encounter it in parallel.
The tool-sharing model also has a practical implication for defenders: a detection rule for one cluster now has value against multiple clusters. A behavioral YARA or Sigma rule for NetDraft's Graph API communication pattern catches not just UAT-8302, but also whatever cluster Talos hasn't identified yet that's using the same code.
8. Recommendations
Immediate (0–24h)
Hunt for known artifacts in the environment — specifically scheduled tasks matching the Microsoft\Windows\Maps\{GUID} naming pattern running from C:\ProgramData, and recon files (whatpc.ps1, ping_scan.bat) in C:\Windows\Temp:
// KQL — Sentinel: Suspicious scheduled task creation
DeviceProcessEvents
| where ProcessCommandLine has_any ("schtasks", "/create")
and ProcessCommandLine has_any ("ProgramData", "AppData")
and ProcessCommandLine has "SYSTEM"
| where InitiatingProcessFileName !in~ ("msiexec.exe", "setup.exe")
// KQL — Sentinel: Anomalous OAuth app consent (NetDraft pattern)
CloudAppEvents
| where ActionType == "Add service principal credentials"
or ActionType == "Consent to application"
| where RawEventData has "graph.microsoft.com"
Short-term (1–7 days)
Audit all OAuth applications registered in your Azure AD / Entra ID tenant — specifically any app holding Mail.ReadWrite, Files.ReadWrite, or Sites.ReadWrite.All permissions that IT did not explicitly approve. Review for DLL sideloading: non-Microsoft, non-vendor executables loading DLLs from the same directory. Monitor outbound HTTPS to graph.microsoft.com from processes that are not legitimate Office applications.
Long-term
Implement Conditional Access policy restricting OAuth user consent: end-users should not be able to self-consent third-party applications to Microsoft Graph access. Enable Microsoft Defender for Cloud Apps to monitor Graph API usage anomalies. For TI teams: maintain a tracking list covering the full ecosystem (Jewelbug, REF7707, LongNosedGoblin, Earth Estries, UAT-6382, UNC5174, UNC6586) — because they share tooling, an indicator from one cluster's campaign may surface in an intrusion by a different cluster entirely.
9. References
Cisco Talos — UAT-8302 and its box full of malware (May 5, 2026): https://blog.talosintelligence.com/uat-8302/
The Hacker News — China-Linked UAT-8302 Targets Governments Using Shared APT Malware Across Regions (May 2026): https://thehackernews.com/2026/05/china-linked-uat-8302-targets.html
Elastic Security Labs — You've Got Malware: FINALDRAFT Hides in Your Drafts (February 2025): https://www.elastic.co/security-labs/finaldraft
The Hacker News — FINALDRAFT Malware Exploits Microsoft Graph API for Espionage on Windows and Linux (February 2025): https://thehackernews.com/2025/02/finaldraft-malware-exploits-microsoft.html
Unit 42 / Palo Alto Networks — Squidoor: Suspected Chinese Threat Actor's Backdoor Targets Global Organizations (March 2025): https://unit42.paloaltonetworks.com/advanced-backdoor-squidoor/
ESET — LongNosedGoblin Tries to Sniff Out Governmental Affairs in Southeast Asia and Japan: https://www.welivesecurity.com/en/eset-research/longnosedgoblin-tries-sniff-out-governmental-affairs-southeast-asia-japan/
Kaspersky — CloudSorcerer: New APT Cloud Actor (2024): https://securelist.com/cloudsorcerer-new-apt-cloud-actor/113056/
MITRE ATT&CK — Web Service: Dead Drop Resolver (T1102.001): https://attack.mitre.org/techniques/T1102/001/