Toddycat hacker group actively exploits ESET antivirus software to execute malicious code
Recently, FPT Threat Intelligence has detected an active exploitation campaign targeting ESET antivirus software. The hacker group ToddyCat has exploited the CVE-2024-11859 vulnerability to silently execute malware on compromised systems. This vulnerability allows attackers with administrative rights on the system to load and execute a malicious dynamic link library (DLL) using the "DLL search order hijacking" technique.
Overview
ToddyCat is an organized hacker group (APT) active since 2020, specializing in attacking government and military organizations in Europe and Asia. The group is known for using custom malware like the Samurai backdoor and Ninja trojan to carry out complex attacks.
In the initial phase, ToddyCat focused on exploiting vulnerabilities in Microsoft Exchange servers, including the ProxyLogon vulnerability, to infiltrate target systems. After gaining access, the group deploys backdoors like Samurai to maintain access and execute remote code.

Vulnerability Details
Vulnerability ID: CVE-2024-11859
CVSS Score: 6.8/10, medium severity
Scope of Impact:
ESET Endpoint Antivirus / ESET Endpoint Security: Affected versions from 7.0 to 10.1
ESET NOD32 Antivirus / ESET Internet Security / ESET Smart Security Premium: Affected versions from 13.0 to 17.0
ESET Server Security for Microsoft Windows Server: Affected versions from 7.0 to 10.1
ESET File Security for Microsoft Windows Server: Affected versions from 7.0 to 9.0
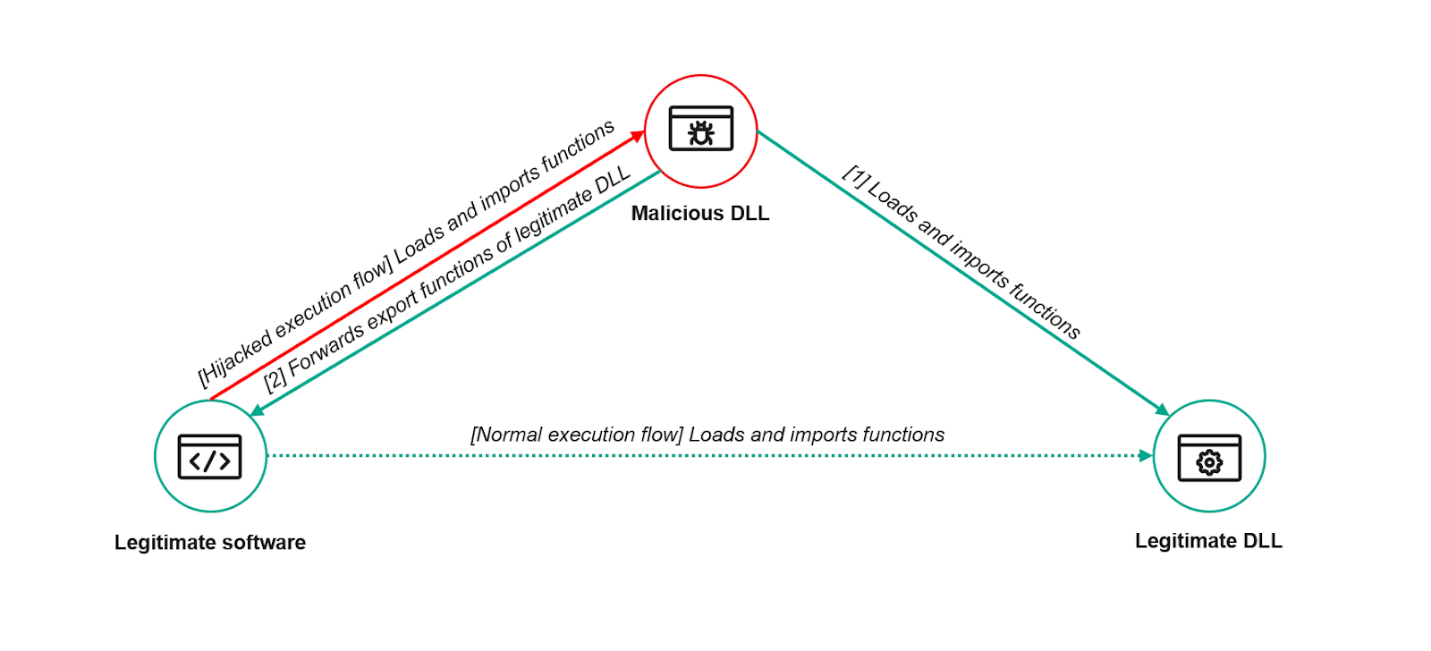
Attack Mechanism: The attacker can carry out an attack using the "DLL Search Order Hijacking" technique, which exploits how applications find and load dynamic link libraries (DLLs) on Windows.
Consequences: This can lead to remote code execution, allowing the attacker to run arbitrary code, steal sensitive data, or compromise the entire system.
Exploitation Conditions
The attacker already has administrative rights on the machine.
Can write files to the same directory where
ecls.exeis executed.A user or other software needs to execute
ecls.exe(which can be indirectly triggered by the attacker).
Campaign Details
- The first step for the hacker group is to create a malicious
.dllfile namedversion.dllwith functions that must be fully proxied for the malicious file to run stably without causing errors forecls.exe.
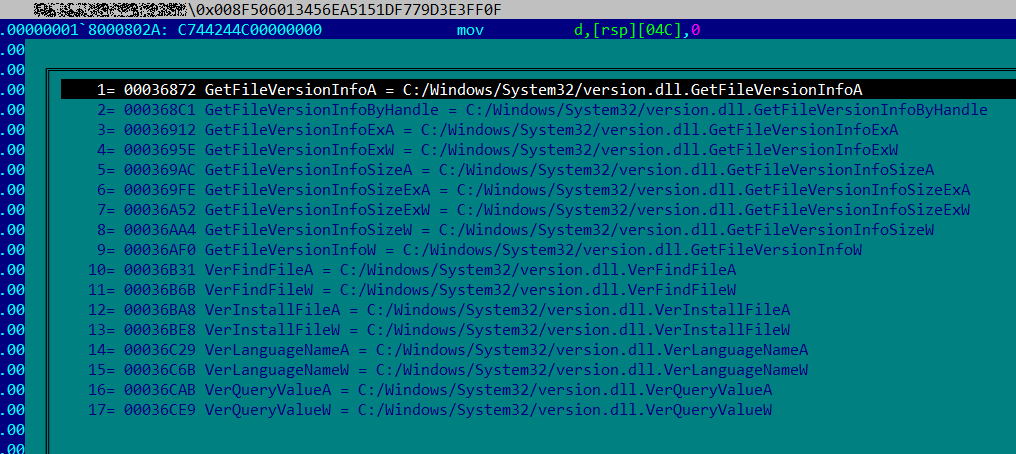
- This malicious DLL file will load all valid functions, but instead of executing them, it will redirect calls to these functions to the original DLL. In this way, an application loading the malicious library will continue to operate normally.
- The hacker group used a tool called "TCESB tool" to scan and disable AV processes, disable system callbacks, and clean up registry traces related to AV/EDR.
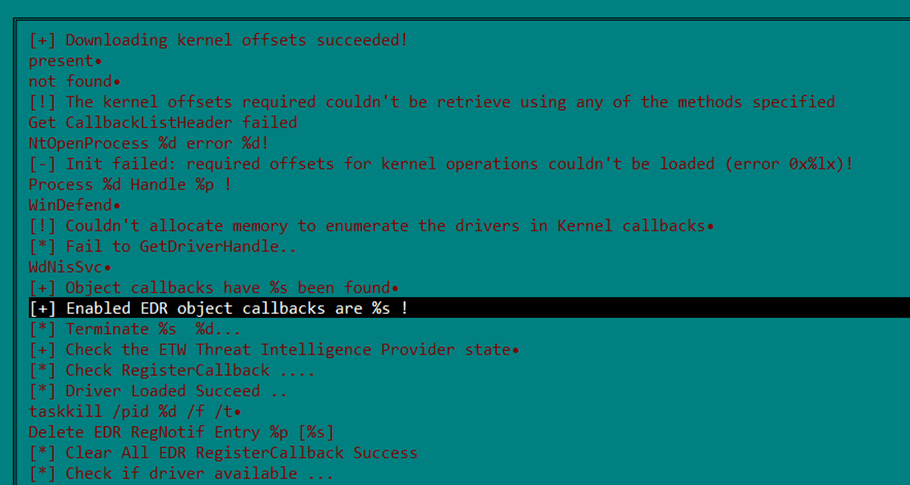
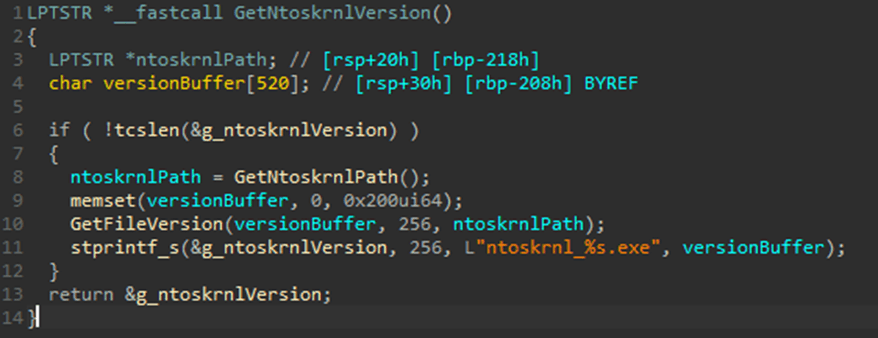
- After scanning and disabling AV processes, the TCESB malware will continue to check the versions of the Windows kernel using the
GetNtoskrnlVersion()function to disable the system's notification routines.
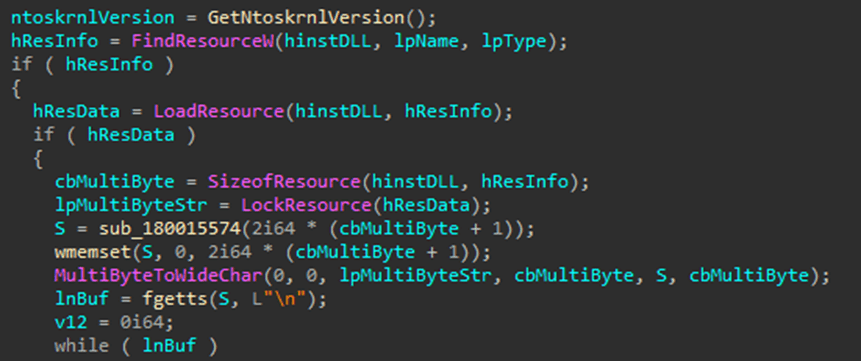
- The next step the hacker group will take is to load embedded resources (
FindResourceW,LoadResource) that contain shellcode, malicious scripts, or encrypted machine code. Additionally, the functionsub_186015574is used by the attackers to obfuscate the analysis process and conceal their actions.
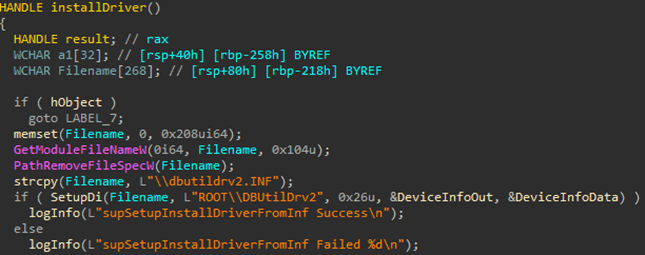
A special attack code using a kernel-mode driver is also used by the attackers to:
Install unauthorized drivers into the Kernel
Bypass UAC/Driver Signature
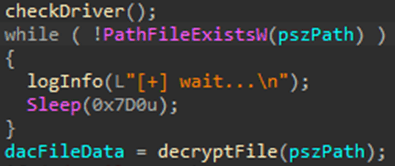
After scanning and infiltrating, the hacker group will begin launching their malicious payloads. A piece of code used in TCESB is related to the "polling" behavior (waiting for a file to appear).
The malware will wait for the payload to be downloaded from the C2 server
The loader waits for the encrypted file to appear to decrypt and execute it
After the user starts the affected ESET application, the malicious payload will be executed, causing several impacts on the victim's machine:
Install backdoor, RAT
Take full control of the system
Disable security programs (specifically ESET)
Hide processes, encrypt, or delete data
IOC
File Hash:
D38E3830C8BA3A00794EF3077942AD96
008F506013456EA5151DF779D3E3FF0F
8795271F02B30980EBD9950FCC141304
B87944DCC444E4C6CE9BB9FB8A9C0DEF
DE39EE41D03C97E37849AF90E408ABBE
DACB62578B3EA191EA37486D15F4F83C
Recommendation
Update the software immediately
ESET Mail Security for Microsoft Exchange Server: \>= 11.1.10009.0ESET Security for Microsoft SharePoint Server: \>= 11.1.15003.0
Restrict directory write permissions
Set the ESET installation directory permissions to SYSTEM and Administrators only.
Check directories such as:
C:\Program Files\ESET\,C:\ProgramData\ESET\,C:\Windows\Temp\
Conclusion
CVE-2024-11859 is an important reminder to keep security software updated and monitor system behavior. Although the vulnerability requires administrative privileges to exploit, in an enterprise environment where users might be tricked into granting permissions or face insider threats, the risk is very serious.
Organizations using ESET products should immediately check and apply patches, along with implementing appropriate monitoring and system control measures to ensure complete safety.






