A new wave of malware on npm: Installing a package can lead to data loss
Overview
In recent years, software supply chain attacks have become one of the most serious threats to the modern software development ecosystem. Instead of directly attacking the target system, attackers focus on the dependencies that developers use daily. When a dependency is compromised with malicious code, its impact can spread to thousands of different software projects.
A prime example of this trend is the PhantomRaven campaign, targeting the npm ecosystem—the most popular package management system for Node.js. In this campaign, the attacker distributed dozens of malicious packages through various npm accounts to steal sensitive information from developers' environments. These packages were designed to resemble legitimate libraries or packages that developers might inadvertently install while searching for dependencies for their projects.
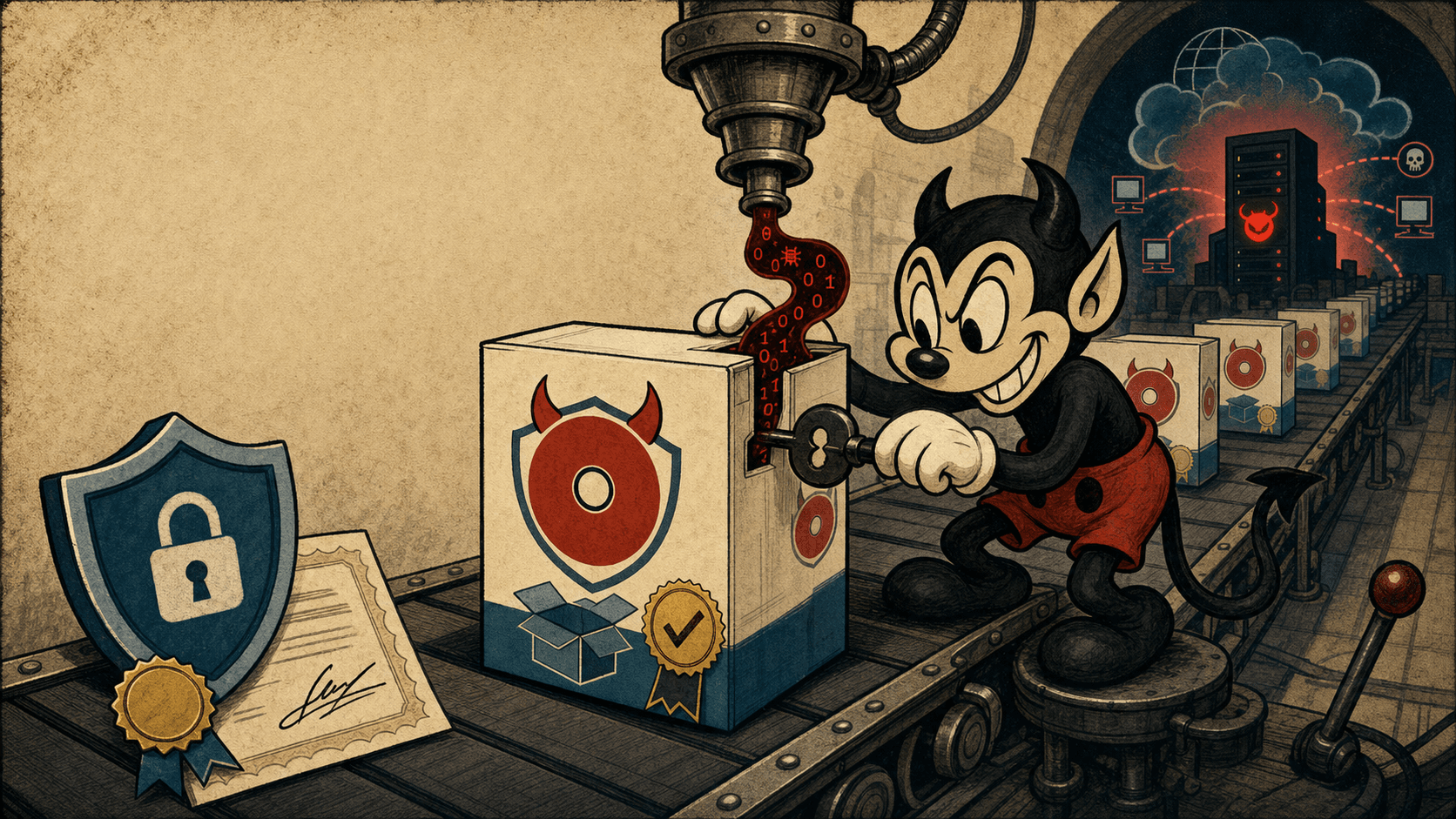
A notable aspect of PhantomRaven is the use of Remote Dynamic Dependencies (RDD) techniques. Instead of directly containing malicious code in the npm package, these packages act merely as a "loader," then download the payload from an external server during installation.
In the following sections, the article will delve into the workflow analysis of the PhantomRaven campaign, the root causes of the exploited vulnerabilities, the exploitation techniques used, and the mapping of attack behaviors with the MITRE ATT&CK framework to clarify the entire picture of this campaign.

The cause of the campaign
Lack of control over dependencies from external URLs: This means npm allows dependencies to be defined using remote URLs, resulting in malicious code potentially being loaded at runtime and not being checked by the registry scanner.
Lack of package verification: A notable aspect of the npm ecosystem is that it contains millions of packages, and anyone can publish a package. This inadvertently allows attackers to distribute fake packages.
Reliance on AI-suggested libraries: Some packages are designed using the technique of typosquatting. This means attackers register packages with names that AI might "hallucinate," leading developers to trust the AI and install the package.
Attack Flow

As mentioned above, in the initial stage, the attacker uploads numerous malicious packages to the npm registry through various accounts. These packages are often named using the technique of slopsquatting, meaning they use names similar to popular libraries or those that might be suggested by AI.
For example, they might impersonate libraries related to Babel plugins, GraphQL tooling, ESLint configuration, or developer utilities. This increases the likelihood of developers accidentally installing malicious packages when searching for dependencies for their projects.
Next comes the process of installing the malicious package. Here, developers trustingly install the package using the command: npm install .
In the PhantomRaven campaign, these packages contain a special technique called Remote Dynamic Dependencies (RDD). Instead of declaring dependencies from the npm registry, the package specifies dependencies pointing to an external URL controlled by the attacker.

As soon as npm install is executed, it will carry out a series of actions, starting with reading the package.json, detecting dependencies pointing to a URL, automatically downloading the package from the attacker's server, and then installing that dependency into the local environment. Thus, the malicious payload does not exist in the npm registry but is directly downloaded from the attacker's server during installation.
After the dependency is downloaded, the malware is executed through npm lifecycle scripts, typically: preinstall, install, or postinstall. These scripts run automatically during the package installation without user interaction. The payload in PhantomRaven is nearly identical across attacks, with research showing that 257 out of 259 lines of malware code are the same across the campaign's waves. This indicates that the attacker focuses more on altering the distribution infrastructure rather than the payload itself.

After execution, the malware begins collecting information from the developer's environment. The first target for the attacker is the "developer configuration." Here, the malware reads two important files: ~/.gitconfig and ~/.npmrc. These are considered to store the developer's email, npm authentication token, and git credentials. The malware also checks environment variables to find tokens or secrets.
Another key target of PhantomRaven is the tokens used in DevOps pipelines. The malware searches for credentials related to GitHub Actions, GitLab CI, Jenkins, and CircleCI. In other words, once these are compromised, the attacker can access repositories, modify build pipelines, and most dangerously, inject malicious code into released software.

In addition to credentials, the malware also gathers system information to identify the victim: IP address, hostname, operating system, and the version of Node.js the victim is using. This information helps the attacker categorize the victim and adjust the payload in a way that suits their objectives.

Any attack campaign will have a C2 server system where the attacker receives commands and sends information. After obtaining the necessary information, they will establish methods such as HTTP GET request, HTTP POST request, and WebSocket connection to connect to the C2 server.

Using multiple data transmission methods allows the malware to maintain a connection even if one protocol is blocked and bypass network monitoring mechanisms. After receiving the stolen data, the attacker can access private repositories, steal source code, modify CI/CD pipelines, and insert backdoors into software builds. This transforms PhantomRaven from an attack on individual developers into a large-scale software supply chain attack.
Mapping MITRE ATT&CK
| Tactic | Technique | Description |
|---|---|---|
| Initial Access | T1195 – Supply Chain Compromise | Distribute malicious packages on npm. |
| Execution | T1059 – Command and Script Interpreter | JavaScript script runs when installing the dependency. |
| Discovery | T1082 – System Information Discovery | Collect system information |
| Credential Access | T1552 – Unsecured Credentials | Retrieve tokens from config files |
| Collection | T1005 – Data from Local System | Collect developer data |
| Exfiltration | T1041 – Exfiltration Over C2 Channel | Send data to the attacker's server. |
| Command and Control | T1071 – Application Layer Protocol | Using HTTP/WebSocket |
Conclusion
The PhantomRaven campaign demonstrates the evolution of supply chain attacks in the open-source ecosystem. By combining slopsquatting, Remote Dynamic Dependencies, and data harvesting scripts, attackers can stealthily steal developer data during the package installation process.
In the context of npm containing millions of dependencies, just one malicious package can compromise the entire software development chain.
Therefore, controlling dependencies, monitoring installation behavior, and protecting DevOps tokens are crucial factors in mitigating risks from similar campaigns.
Recommendations
Check and verify packages before installation.
Number of downloads: Popular packages typically have a large and stable download count.
Source repository: Check if the package is linked to a valid GitHub or GitLab repository.
Update history: Reliable packages typically have a clear commit history and active maintainers.
Reputable maintainer: Avoid installing packages published by newly created accounts or those with little information.
Avoid using dependencies from external URLs.
Only use dependencies from the official npm registry
Do not use dependencies from unverified URLs
Check the
package.jsonfile of newly installed packages
Protect tokens and credentials
Do not store tokens directly in configuration files
Use a secret manager or environment vault
Set token expiration
Regularly rotate tokens
Monitor network behavior during installation
In many cases, malware will connect to the attacker's server as soon as the package is installed. Therefore, you should:
Monitor network traffic during npm install
Detect connections to unfamiliar domains
Block requests to domains not on the whitelist.
Enhance security awareness for developers
Organizations should train developers on:
Risks from supply chain attacks
How to identify malicious packages
How to protect tokens and secrets.
IOCs
Malicious Domain
URL / Phishing
https://airtable.com/appz4nCLxGPcHqdBW/shr9uFgyeZIubJlPV/tbl1eP2Yz0wiJb546/viwB5oWwcsH08FjVm
https://airtable.com/appremzEfrzMpskzA/shrWcQ3t3TCDXLzti/tblSZUfjjtIthEsRo/viwTONuWd3KMfQU0
MD5
AC89EE798372724756025B6EF400BDDD
328BE455C1BD821A4F04194B8C905C6D
AF24E5FCEBA310E0953FA34AE40B75E5
685017977342F93705E4A99B256D0B18
SHA1
1C0BB37868D0208128EB99D0D2DD994DCC45F46F
58EC6F2D933DAE3D4685CF5B318D13E564308FBC
C1AF38C04ED6D848904D99CBC322ABE6014B04F0
AF387331734F4575F6ED7FE3F919E70F6781A8B5
SHA256
6F78E06CB72FD69F93F8E7A38F8F0B9A146F99DDA0C9C8729886C522D0CE18C9
BFAEA094A6908594813CC0D8F257A602143D041A2CAFEAF1E18F19AE0642E489
53638DD5FD06CABBB6CDA83908BF5205A6AFBAFF500135607B0ACBFB18321F57
C227036E15FDC1AE368034AB737EC330C9B3CC029470C4C72B5324B4D9303A1F
IP C2 Server
54.173.15.59
100.26.42.247
13.219.250.107
54.227.45.171